OSDP
Safetrust has been named the 2025 winner of the Access Control Software, Hardware, Devices & Peripherals – Wired category at the SIA New Products and Solutions (NPS) Awards for its IoT Neural Sensor. Safetrust was honoured during an award ceremony at the Bridge Stage on the ISC West show floor. Presented in partnership with ISC West, the NPS Awards are the Security Industry Association (SIA) flagship program, recognising the year’s most innovative security products, services, an...
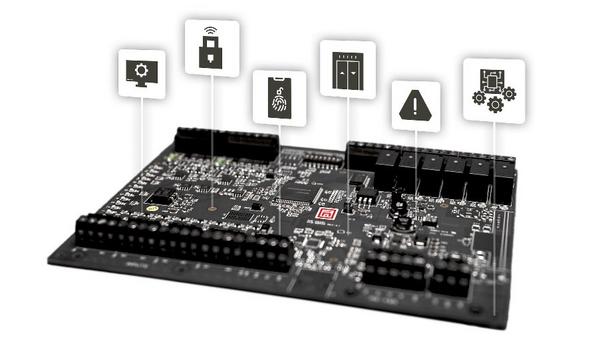
Mercury Security, the pioneer in open architecture access control hardware, is launching a new addition to its industry-defining controller platform—the Mercury embedded application environment, an open platform that enables technology partners and OEMs to develop and deploy custom applications directly on Mercury MP Controllers. “We have a lot of exciting things happening at Mercury,” said Steve Lucas, vice president of sales at Mercury Security. “We are excited to...
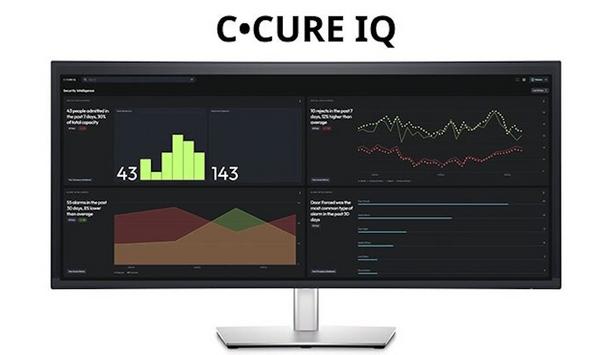
Johnson Controls, the pioneer for smart, healthy and sustainable buildings, announced a series of upgrades to their access control and video surveillance (ACVS) solutions. These product enhancements will integrate with existing security architectures to improve management of mission-critical security and protection for people, buildings and assets. They will transform customers’ security posture, unlocking new levels of operational agility and cost-effectiveness. Advanced access control...
Mercury Security, the pioneer in open architecture access control hardware, returns to ISC West to highlight a new addition to their industry-defining controller platform—the Mercury embedded application environment, an open platform that enables technology partners and OEMs to develop and deploy custom applications directly on Mercury MP Controllers. “We have a lot of exciting things happening at Mercury, and a dedicated booth at ISC West is the perfect place to showcase them,...
Verkada, a pioneer in cloud-based physical security solutions, announced a new integration with SimonsVoss SmartIntego wireless locks at its VerkadaOne London conference. An extension of its flagship conference in the United States, VerkadaOne London convened more than 400 IT and physical security pioneers to connect and learn about new solutions from Verkada that are empowering physical security pioneers to be more proactive and efficient than ever. Partnership with SimonsVoss "I'm proud to...
Johnson Controls, the pioneer for smart, safe, healthy and sustainable buildings, is excited to reveal new products and solutions across its industry-pioneering security portfolio at Booth 18033 at ISC West in Las Vegas, March 31-April 4. The company will highlight how its breadth of offerings and products enhance safety, improve automation and advance real-time situational awareness for customers. Integrated solutions “As security threats grow more complex, organisations need inte...
News
Verkada, a pioneer in cloud-based physical security, announced a wide range of updates to its Command platform that will make it even easier for its customers around the world to keep their people and places safe. To strengthen and enhance the entry experience, Verkada has deepened the integration of Verkada Guest and Verkada Access Control. Now, its customers can grant guests temporary, customisable visitor access credentials. Verkada's roll call reports Each credential is unique, time-bound, and exactly matched to the visitor's needs The moment a visitor checks in with Verkada Guest, organisations can provision a temporary access badge with custom permissions, or they can send a door unlock link that enables a visitor to open authorised doors directly from their phones. Each credential is unique, time-bound, and exactly matched to the visitor's needs. Guests are also now fully integrated with Verkada's roll call reports. Verkada customers can manage all occupants – both employees and guests – in emergency situations from a single tool. Improvements to access control solution Verkada also announced several step-change improvements to its access control solution for large-scale deployments, including support for third-party OSDP door readers and two new APIs that automate access control operations: programmatic updates to door schedules and the ability to update the doors, schedule, or groups components of an access level from third-party software, eliminating the need to make these changes manually in Command. Verkada's platform controls access "Today, Verkada's platform controls access for more than 3.7 million users and checks in more than 1.5 million visitors every month," said Brandon Davito, Senior Vice President of Product and Operations at Verkada. "We know that security starts at the door, so we've made significant investments in our platform that will both strengthen and simplify the entry experience for our customers – especially for organisations managing access in enterprise environments." Range of additional product and platform updates Verkada also announced a range of additional product and platform updates, including: Broadened video search tools. With History Player Search, Verkada customers can now access a comprehensive overview of all sightings of an individual with a single click – another way to streamline and optimise investigations. Verkada also reimagined the search interface in Command to give security teams an even more granular list of search attributes – from makes and models of vehicles to bumper stickers and even vehicle body damage – to surface people and vehicles of interest in even less time. Continued commitment to interoperability. Verkada's Command Connector is now officially recognised as an Open Network Video Interface Forum (ONVIF) Profile S conformant client. In addition, Command Connector can now also ingest feeds from RTSP-compatible cameras that are not ONVIF Profile S conformant, bringing the number of compatible video security camera models to more than one thousand. This will ensure that even more organisations can bring legacy, non-Verkada cameras into its cloud platform in minutes as they migrate to Verkada's Command platform. Even more flexible security deployments. Verkada's new WiFi Gateway will enable customers to deploy a range of Verkada devices anywhere with power and Wi-Fi, making installation simple in hard-to-wire locations like parking lots, fence lines, and school grounds. Enhanced privacy features. Building on Verkada's robust privacy features and permissions, its new Person of Interest Only Face Search limits the application of facial recognition technology to only images matching a pre-defined user list of Persons of Interest (POI). When enabled, all other facial recognition detections not in the POI list will not be stored. Streamlined management for organisations operating at scale. Verkada introduced new user and licence management tools to empower large, multi-site enterprises to more efficiently streamline and delegate operations. With the User Directories feature, organisations can now create regional boundaries for users and permissions that mirror their organisational structure, allowing local IT teams to manage their specific user base while central IT teams maintain oversight. Expanded line of next-generation Dome cameras. Verkada's 5MP CD43 and CD53 dome cameras include advanced image sensors with enhanced low-light viewing capability and expanded IR range for precise nighttime monitoring, as well as onboard storage of up to 365 days' retention and nearly 3x optical zoom capabilities for the CD53.
Matrix made a strong impact at the FSAI Project Heads, Architects & Consultants Conclave (PACC) 2025, held at ITC Grand Chola, Chennai, from February 6-9. This major event brought together 750+ industry pioneers, including Smart City CEOs, government officials, architects, and security experts, to discuss the future of security solutions. Latest security solutions PACC 2025 provided Matrix with a significant platform to showcase its latest security solutions PACC 2025 provided Matrix with a significant platform to showcase its latest security solutions designed to address modern challenges. The company showcased its Ruggedised Network Camera, which provides superior-quality images in high-vibration mobile environments. With an impressive 100,000-hour Mean Time Between Failures (MTBF), Matrix Network Cameras stand out for their reliability and durability, ensuring continuous operation with minimal maintenance. Evolving security landscape Matrix discussed the latest feature update-OSDP support in its Access Control solutions, which enhances encrypted communication for secure access control. At the event, another new feature was highlighted-WhatsApp Alerts in IP Video Surveillance solutions, for real-time notifications. The event also provided valuable insights into the evolving security landscape. Discussions revolved around the increasing demand for cyber-secure surveillance, seamless access control, and AI-driven security analytics. Importance of integrating security technology Matrix absorbed these insights, which will shape its future product roadmap, ensuring that its solutions Experts emphasised the importance of integrating security technology with existing infrastructure to create safer and more responsive security ecosystems. Matrix absorbed these insights, which will shape its future product roadmap, ensuring that its solutions remain relevant and industry-pioneering. A defining moment at the event was the speech by Dr. Vikram Singh, one of India’s most respected police officers, at the Bravery Awards Celebration on February 8, 2025. He commended key contributors in the security industry and acknowledged the importance of technology-driven safety measures. His words reinforced the critical role that enterprises like Matrix play in enhancing national security through innovation. Matrix’s participation in PACC 2025 Matrix’s participation in PACC 2025 is expected to fuel business growth and reinforce its industry standing. By demonstrating its technological expertise, the company has established itself as a preferred security partner for large-scale projects across smart cities, industrial complexes, and government initiatives. As security challenges escalate, Matrix’s solutions will play a pivotal role in strengthening national security infrastructure. The learnings from PACC 2025 will drive Matrix’s ongoing commitment to providing advanced, reliable, and easy-to-integrate security solutions for businesses and public spaces across the nation.
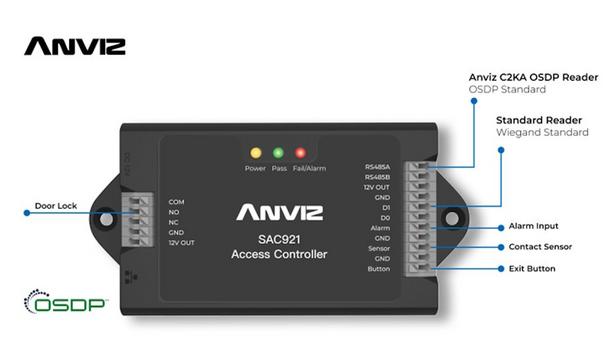
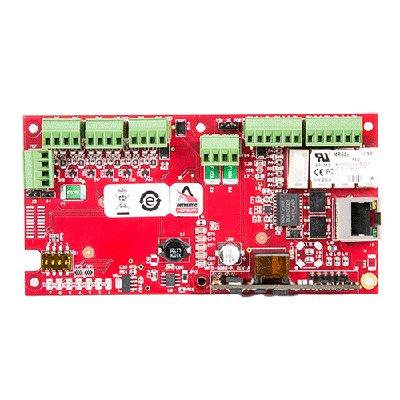
Anviz (a business unit of Xthings Group, Inc.) has officially launched an OSDP (Open Supervisory Device Protocol)-enabled access control solution. The goal is simple: improve the shortcomings of legacy access control systems while enabling bi-directional, secure data interactions between systems and components. While communication standards ensure interoperability among diverse technologies designed and manufactured by global companies – evolving standards like OSDP allow the application of technological advances and mitigation of external threats and vulnerabilities. Legacy control protocols no longer meet industry needs Data transmitted over Wiegand is not encrypted, creating security exposure and vulnerability Legacy Wiegand functionality limits device capability to being a point-to-point system where the reader transmits data directly to the access control panel but not to other devices. Data transmitted over Wiegand is not encrypted, creating security exposure and vulnerability. Anviz is fully committed to global security and privacy requirements, as exemplified by its adherence to GDPR compliance. The feature deployment of OSDP meets the customer’s goals of creating, enhancing, and maintaining secure and capable access control solutions. Once OSDP was released as an industry standard, Anviz mandated an internally driven and committed OSDP-focused feature enhancement goal. OSDP: A more secure, feature-rich access control protocol Since security is at the core of the OSDP access control protocol, modern OSDP-equipped access control systems and devices encrypt data and provide bi-directional communication, making them more secure--yet giving them greater application power and flexibility. OSDP key advantages Anviz OSDP-enabled devices can be deployed on legacy RS-485 networks Anviz OSDP-enabled devices can be deployed on legacy RS-485 networks, so site impact on infrastructure is reduced. When installed, the products offer data encryption for the highest data security, controller status monitoring at a glance, and visual feedback during user interaction. Anviz support for Wiegand and OSDP The SAC921 access controller supports legacy Wiegand readers and C2KA-OSDP readers. As shown, each door cassette on the SAC921 has connection points for legacy Wiegand and OSDP Anviz readers--for maximum installed or new site support. Anviz is constantly refining and updating its security systems--optimising components to maintain maximum flexibility while staying ahead of evolving threats. They strive to provide products to business end users that enable them to benefit from higher security and enhanced features – but with the advantages of long-term, regular technology updates Anviz offers.
Sielox, the established industry pioneer in layered access control and crisis event management solutions, is demonstrating its latest security innovations at ISC West 2025 at stand 11109. Sielox is showcasing its flagship Pinnacle Access Control Platform that features hundreds of user-selectable filters, enabling security teams to aggregate and manage access data and events with unprecedented insights and visibility. Future of access control Sielox is showcasing its vision Pinnacle's intuitive automated access control features and streamlined workflows"At ISC West we’re highlighting the future of access control with real intelligence. Pinnacle, and our broader portfolio of layered solutions, empower security teams with the proactive insights they need to identify and mitigate evolving threats,” said Karen Evans, President and CEO of Sielox. “We're not just reactive. Sielox delivers proactive data-driven intelligence." Sielox is showcasing this vision with live demonstrations of Pinnacle's intuitive automated access control features and streamlined workflows. Visitors will experience how this comprehensive access control ecosystem creates layered protection that adapts to evolving security challenges while remaining remarkably easy to implement and manage. Next-gen access control solutions Alongside Pinnacle, Sielox is highlighting a variety of powerful security solutions designed to make access control smarter and more efficient, including: Sielox AnyWare A web-based access control platform that lets users monitor and manage security in real time from anywhere. It supports up to 64 doors and 25,000 cardholders and allows authorised personnel to manage security events instantly from any device, anywhere. This plug-and-play system operates via LAN, WAN, WiFi or cellular networks with no monthly fees, configuring in minutes while providing enterprise-grade protection with a lower total cost of ownership. 2700 Controller An intelligent, secure, and fully distributed access controller supporting up to 34 doors with continuous operation even during communication interruptions. This true IP controller features OSDP compatibility, wireless lock integration, and 32GB of memory for redundant configuration—all secured by an embedded Linux OS with AES 256 encryption. CLASS (Crisis Lockdown Alert Status System) Demo An award-winning real-time emergency alert and response system designed to improve communication and safety during critical situations. The solution provides colour-coded status updates on any device, features two-way chat between occupants and responders, and integrates with cameras and access control systems to enable faster, more coordinated emergency responses and real-time lockdown. WaveLynx integration A strategic partnership that enhances Sielox's access control ecosystem with WaveLynx's advanced reader and credential technologies, including secure mobile credentials via Bluetooth. This integration delivers superior security and convenience across financial, commercial, government, and educational environments—giving users flexible credentialing options for migrating from prox credentials. Pinnacle’s UI/UX unveiled “ISC West attendees can get a preview of the Pinnacle new UI and UX,” said Evans, “We encourage attendees to join the end users and CSIs who have guided our development with feedback and direction of their own.”
Invixium, a pioneer in biometric access control, workforce, and visitor management, along with RTLS-connected worker solutions, is set to exhibit its latest Enterprise Series biometric solutions at ISC WEST. Making its entry into the North American market is Invixium’s effectively priced IXM ROSTO (face + card) and IXM TOUCH 3 (finger + card). These new products are purposely designed with relevant features for the Small-to-Medium Business (SMB) market. Invixium end-to-end solutions In addition, Invixium will also showcase its trusted portfolio of end-to-end solutions for heavy industries and critical infrastructure. “There’s never been a more exciting time to visit Invixium at ISC WEST,” said Shiraz Kapadia, CEO & President of Invixium. “We have achieved tremendous success in the industrial sector, and with the launch of the Enterprise Series, our goal is to deliver high-performance yet economical biometric solutions for the SMB market.” ROSTO features Enterprise Series solutions are sleek and versatile biometric devices designed for fast access control The Enterprise Series solutions, IXM ROSTO and IXM TOUCH 3, are sleek and versatile biometric devices designed for fast and secure access control, workforce, and visitor management. ROSTO features dual cameras for fast face recognition and a 5″ IPS LCD touchscreen for a clear and user-friendly interface. Equipped with a large 1:50K user capacity and Wiegand and OSDP connectivity to pioneering Access Control Panels, it also supports RFID, mobile, and QR code credentials, providing versatile authentication options. Invixium’s flagship solution TOUCH 3 is the newest member of the best-selling TOUCH series, offering advanced fingerprint authentication. It features a vibrant and responsive 3.5″ IPS LCD touchscreen, providing a clear and user-friendly interface for easy interaction. Equipped with an FBI-certified 500dpi optical fingerprint sensor, TOUCH 3 ensures precise and secure authentication. Attendees can also experience IXM TITAN 2nd Generation, now faster than ever, with an exceptional speed and high throughput of 28 faces per minute. Celebrated as Invixium’s flagship solution, TITAN is NDAA-compliant and specifically designed to withstand the toughest industrial and critical infrastructure environments. Invixium’s RTLS-connected worker solution Another highlight will be Triax, Invixium’s RTLS-connected worker solution Another highlight will be Triax, Invixium’s RTLS-connected worker solution. This innovative, easy-to-deploy solution features a patented and scalable mesh network, compact hardware, and actionable dashboards that identify and eliminate productivity pinch points. It enhances site safety, reduces muster times, tracks equipment usage, and triggers alerts for worker-generated injuries, delivering significant labour savings and maximising ROI. Invixium’s solutions at Stand 20103 Visitors will have the opportunity to experience live demos of Invixium’s solutions at Stand 20103. Thanks to strategic partnerships and seamless integrations with esteemed technology partners, their solutions will also be exhibited at Genetec – Stand 13062, Galaxy Control Systems – Stand 3077, and Honeywell – Stand 18059.
Iris ID, the pioneer in iris recognition technology for 25 years, enthusiastically debuts the all new IrisAccess® iA1000 concurrent iris and face recognition access control reader. Piggybacking off of key core technology and the success of the IrisAccess iCAM 7S Series, the iA1000 is the access control solution of the future. The iA1000 with two configurations, is equipped with capabilities to suit varied budgets as well as diverse access control needs. Key certifications of iA1000 The iA1000 meets key certifications, can be used in a variety of use cases and comes with the new iA-MS™ Depending on which configuration is chosen to secure operations, the iA1000 is equipped with a touchscreen LCD, Wi-Fi and PoE capabilities, OSDP and Wiegand protocols, and card reader that supports multiple card formats as well as mobile credentials. The iA1000 meets key certifications, can be used in a variety of use cases and comes with the new iA-MS™, a centralised web-based application for managing iA1000 devices. Impact caused by physical breaches As the access control market steadily grows in market value so does the requirement to have smart and reliable solutions that reduce network vulnerabilities, protect individual privacy and physically safeguard actual infrastructures and buildings. While most organisations focus on cybersecurity, access control deserves just as much attention and consideration as the financial impact caused by physical breaches remains significant. Security requirements The same study concluded that almost ten percent of all data breaches come from a physical breach The 2023 IBM Cost of a Data Breach Report identified the average cost of a data breach from a physical security collapse is $4.1 million. The same study concluded that almost ten percent of all data breaches come from a physical breach, and it could take up to 198 days to trace the breach back to the physical security violation and 69 additional days to repair the damage caused. Failure to meet these security requirements can also result in additional breaches and increased maintenance costs. New and unpredictable ways in the security industry “As technology continues to push the security industry in new and unpredictable ways, Iris ID prides itself with innovating Advanced Identity Authentication solutions for this market," says Mohammed Murad, VP, Iris ID Systems, Inc. "Traditional methods of providing access control such as access cards, pins and keypads and even legacy biometrics no longer offer the protections that are needed to secure physical locations. Our solutions are one step in the right direction of ensuring highest-level of security that can grow with organisations and does the most to keep bad actors at bay.”
Verkada, a pioneer in cloud-based physical security, announced a wide range of updates to its Command platform that will make it even easier for its customers around the world to keep their people and places safe. To strengthen and enhance the entry experience, Verkada has deepened the integration of Verkada Guest and Verkada Access Control. Now, its customers can grant guests temporary, customisable visitor access credentials. Verkada's roll call reports Each credential is unique, time-bound, and exactly matched to the visitor's needs The moment a visitor checks in with Verkada Guest, organisations can provision a temporary access badge with custom permissions, or they can send a door unlock link that enables a visitor to open authorised doors directly from their phones. Each credential is unique, time-bound, and exactly matched to the visitor's needs. Guests are also now fully integrated with Verkada's roll call reports. Verkada customers can manage all occupants – both employees and guests – in emergency situations from a single tool. Improvements to access control solution Verkada also announced several step-change improvements to its access control solution for large-scale deployments, including support for third-party OSDP door readers and two new APIs that automate access control operations: programmatic updates to door schedules and the ability to update the doors, schedule, or groups components of an access level from third-party software, eliminating the need to make these changes manually in Command. Verkada's platform controls access "Today, Verkada's platform controls access for more than 3.7 million users and checks in more than 1.5 million visitors every month," said Brandon Davito, Senior Vice President of Product and Operations at Verkada. "We know that security starts at the door, so we've made significant investments in our platform that will both strengthen and simplify the entry experience for our customers – especially for organisations managing access in enterprise environments." Range of additional product and platform updates Verkada also announced a range of additional product and platform updates, including: Broadened video search tools. With History Player Search, Verkada customers can now access a comprehensive overview of all sightings of an individual with a single click – another way to streamline and optimise investigations. Verkada also reimagined the search interface in Command to give security teams an even more granular list of search attributes – from makes and models of vehicles to bumper stickers and even vehicle body damage – to surface people and vehicles of interest in even less time. Continued commitment to interoperability. Verkada's Command Connector is now officially recognised as an Open Network Video Interface Forum (ONVIF) Profile S conformant client. In addition, Command Connector can now also ingest feeds from RTSP-compatible cameras that are not ONVIF Profile S conformant, bringing the number of compatible video security camera models to more than one thousand. This will ensure that even more organisations can bring legacy, non-Verkada cameras into its cloud platform in minutes as they migrate to Verkada's Command platform. Even more flexible security deployments. Verkada's new WiFi Gateway will enable customers to deploy a range of Verkada devices anywhere with power and Wi-Fi, making installation simple in hard-to-wire locations like parking lots, fence lines, and school grounds. Enhanced privacy features. Building on Verkada's robust privacy features and permissions, its new Person of Interest Only Face Search limits the application of facial recognition technology to only images matching a pre-defined user list of Persons of Interest (POI). When enabled, all other facial recognition detections not in the POI list will not be stored. Streamlined management for organisations operating at scale. Verkada introduced new user and licence management tools to empower large, multi-site enterprises to more efficiently streamline and delegate operations. With the User Directories feature, organisations can now create regional boundaries for users and permissions that mirror their organisational structure, allowing local IT teams to manage their specific user base while central IT teams maintain oversight. Expanded line of next-generation Dome cameras. Verkada's 5MP CD43 and CD53 dome cameras include advanced image sensors with enhanced low-light viewing capability and expanded IR range for precise nighttime monitoring, as well as onboard storage of up to 365 days' retention and nearly 3x optical zoom capabilities for the CD53.
Matrix made a strong impact at the FSAI Project Heads, Architects & Consultants Conclave (PACC) 2025, held at ITC Grand Chola, Chennai, from February 6-9. This major event brought together 750+ industry pioneers, including Smart City CEOs, government officials, architects, and security experts, to discuss the future of security solutions. Latest security solutions PACC 2025 provided Matrix with a significant platform to showcase its latest security solutions PACC 2025 provided Matrix with a significant platform to showcase its latest security solutions designed to address modern challenges. The company showcased its Ruggedised Network Camera, which provides superior-quality images in high-vibration mobile environments. With an impressive 100,000-hour Mean Time Between Failures (MTBF), Matrix Network Cameras stand out for their reliability and durability, ensuring continuous operation with minimal maintenance. Evolving security landscape Matrix discussed the latest feature update-OSDP support in its Access Control solutions, which enhances encrypted communication for secure access control. At the event, another new feature was highlighted-WhatsApp Alerts in IP Video Surveillance solutions, for real-time notifications. The event also provided valuable insights into the evolving security landscape. Discussions revolved around the increasing demand for cyber-secure surveillance, seamless access control, and AI-driven security analytics. Importance of integrating security technology Matrix absorbed these insights, which will shape its future product roadmap, ensuring that its solutions Experts emphasised the importance of integrating security technology with existing infrastructure to create safer and more responsive security ecosystems. Matrix absorbed these insights, which will shape its future product roadmap, ensuring that its solutions remain relevant and industry-pioneering. A defining moment at the event was the speech by Dr. Vikram Singh, one of India’s most respected police officers, at the Bravery Awards Celebration on February 8, 2025. He commended key contributors in the security industry and acknowledged the importance of technology-driven safety measures. His words reinforced the critical role that enterprises like Matrix play in enhancing national security through innovation. Matrix’s participation in PACC 2025 Matrix’s participation in PACC 2025 is expected to fuel business growth and reinforce its industry standing. By demonstrating its technological expertise, the company has established itself as a preferred security partner for large-scale projects across smart cities, industrial complexes, and government initiatives. As security challenges escalate, Matrix’s solutions will play a pivotal role in strengthening national security infrastructure. The learnings from PACC 2025 will drive Matrix’s ongoing commitment to providing advanced, reliable, and easy-to-integrate security solutions for businesses and public spaces across the nation.
Anviz (a business unit of Xthings Group, Inc.) has officially launched an OSDP (Open Supervisory Device Protocol)-enabled access control solution. The goal is simple: improve the shortcomings of legacy access control systems while enabling bi-directional, secure data interactions between systems and components. While communication standards ensure interoperability among diverse technologies designed and manufactured by global companies – evolving standards like OSDP allow the application of technological advances and mitigation of external threats and vulnerabilities. Legacy control protocols no longer meet industry needs Data transmitted over Wiegand is not encrypted, creating security exposure and vulnerability Legacy Wiegand functionality limits device capability to being a point-to-point system where the reader transmits data directly to the access control panel but not to other devices. Data transmitted over Wiegand is not encrypted, creating security exposure and vulnerability. Anviz is fully committed to global security and privacy requirements, as exemplified by its adherence to GDPR compliance. The feature deployment of OSDP meets the customer’s goals of creating, enhancing, and maintaining secure and capable access control solutions. Once OSDP was released as an industry standard, Anviz mandated an internally driven and committed OSDP-focused feature enhancement goal. OSDP: A more secure, feature-rich access control protocol Since security is at the core of the OSDP access control protocol, modern OSDP-equipped access control systems and devices encrypt data and provide bi-directional communication, making them more secure--yet giving them greater application power and flexibility. OSDP key advantages Anviz OSDP-enabled devices can be deployed on legacy RS-485 networks Anviz OSDP-enabled devices can be deployed on legacy RS-485 networks, so site impact on infrastructure is reduced. When installed, the products offer data encryption for the highest data security, controller status monitoring at a glance, and visual feedback during user interaction. Anviz support for Wiegand and OSDP The SAC921 access controller supports legacy Wiegand readers and C2KA-OSDP readers. As shown, each door cassette on the SAC921 has connection points for legacy Wiegand and OSDP Anviz readers--for maximum installed or new site support. Anviz is constantly refining and updating its security systems--optimising components to maintain maximum flexibility while staying ahead of evolving threats. They strive to provide products to business end users that enable them to benefit from higher security and enhanced features – but with the advantages of long-term, regular technology updates Anviz offers.
Sielox, the established industry pioneer in layered access control and crisis event management solutions, is demonstrating its latest security innovations at ISC West 2025 at stand 11109. Sielox is showcasing its flagship Pinnacle Access Control Platform that features hundreds of user-selectable filters, enabling security teams to aggregate and manage access data and events with unprecedented insights and visibility. Future of access control Sielox is showcasing its vision Pinnacle's intuitive automated access control features and streamlined workflows"At ISC West we’re highlighting the future of access control with real intelligence. Pinnacle, and our broader portfolio of layered solutions, empower security teams with the proactive insights they need to identify and mitigate evolving threats,” said Karen Evans, President and CEO of Sielox. “We're not just reactive. Sielox delivers proactive data-driven intelligence." Sielox is showcasing this vision with live demonstrations of Pinnacle's intuitive automated access control features and streamlined workflows. Visitors will experience how this comprehensive access control ecosystem creates layered protection that adapts to evolving security challenges while remaining remarkably easy to implement and manage. Next-gen access control solutions Alongside Pinnacle, Sielox is highlighting a variety of powerful security solutions designed to make access control smarter and more efficient, including: Sielox AnyWare A web-based access control platform that lets users monitor and manage security in real time from anywhere. It supports up to 64 doors and 25,000 cardholders and allows authorised personnel to manage security events instantly from any device, anywhere. This plug-and-play system operates via LAN, WAN, WiFi or cellular networks with no monthly fees, configuring in minutes while providing enterprise-grade protection with a lower total cost of ownership. 2700 Controller An intelligent, secure, and fully distributed access controller supporting up to 34 doors with continuous operation even during communication interruptions. This true IP controller features OSDP compatibility, wireless lock integration, and 32GB of memory for redundant configuration—all secured by an embedded Linux OS with AES 256 encryption. CLASS (Crisis Lockdown Alert Status System) Demo An award-winning real-time emergency alert and response system designed to improve communication and safety during critical situations. The solution provides colour-coded status updates on any device, features two-way chat between occupants and responders, and integrates with cameras and access control systems to enable faster, more coordinated emergency responses and real-time lockdown. WaveLynx integration A strategic partnership that enhances Sielox's access control ecosystem with WaveLynx's advanced reader and credential technologies, including secure mobile credentials via Bluetooth. This integration delivers superior security and convenience across financial, commercial, government, and educational environments—giving users flexible credentialing options for migrating from prox credentials. Pinnacle’s UI/UX unveiled “ISC West attendees can get a preview of the Pinnacle new UI and UX,” said Evans, “We encourage attendees to join the end users and CSIs who have guided our development with feedback and direction of their own.”
Invixium, a pioneer in biometric access control, workforce, and visitor management, along with RTLS-connected worker solutions, is set to exhibit its latest Enterprise Series biometric solutions at ISC WEST. Making its entry into the North American market is Invixium’s effectively priced IXM ROSTO (face + card) and IXM TOUCH 3 (finger + card). These new products are purposely designed with relevant features for the Small-to-Medium Business (SMB) market. Invixium end-to-end solutions In addition, Invixium will also showcase its trusted portfolio of end-to-end solutions for heavy industries and critical infrastructure. “There’s never been a more exciting time to visit Invixium at ISC WEST,” said Shiraz Kapadia, CEO & President of Invixium. “We have achieved tremendous success in the industrial sector, and with the launch of the Enterprise Series, our goal is to deliver high-performance yet economical biometric solutions for the SMB market.” ROSTO features Enterprise Series solutions are sleek and versatile biometric devices designed for fast access control The Enterprise Series solutions, IXM ROSTO and IXM TOUCH 3, are sleek and versatile biometric devices designed for fast and secure access control, workforce, and visitor management. ROSTO features dual cameras for fast face recognition and a 5″ IPS LCD touchscreen for a clear and user-friendly interface. Equipped with a large 1:50K user capacity and Wiegand and OSDP connectivity to pioneering Access Control Panels, it also supports RFID, mobile, and QR code credentials, providing versatile authentication options. Invixium’s flagship solution TOUCH 3 is the newest member of the best-selling TOUCH series, offering advanced fingerprint authentication. It features a vibrant and responsive 3.5″ IPS LCD touchscreen, providing a clear and user-friendly interface for easy interaction. Equipped with an FBI-certified 500dpi optical fingerprint sensor, TOUCH 3 ensures precise and secure authentication. Attendees can also experience IXM TITAN 2nd Generation, now faster than ever, with an exceptional speed and high throughput of 28 faces per minute. Celebrated as Invixium’s flagship solution, TITAN is NDAA-compliant and specifically designed to withstand the toughest industrial and critical infrastructure environments. Invixium’s RTLS-connected worker solution Another highlight will be Triax, Invixium’s RTLS-connected worker solution Another highlight will be Triax, Invixium’s RTLS-connected worker solution. This innovative, easy-to-deploy solution features a patented and scalable mesh network, compact hardware, and actionable dashboards that identify and eliminate productivity pinch points. It enhances site safety, reduces muster times, tracks equipment usage, and triggers alerts for worker-generated injuries, delivering significant labour savings and maximising ROI. Invixium’s solutions at Stand 20103 Visitors will have the opportunity to experience live demos of Invixium’s solutions at Stand 20103. Thanks to strategic partnerships and seamless integrations with esteemed technology partners, their solutions will also be exhibited at Genetec – Stand 13062, Galaxy Control Systems – Stand 3077, and Honeywell – Stand 18059.
Iris ID, the pioneer in iris recognition technology for 25 years, enthusiastically debuts the all new IrisAccess® iA1000 concurrent iris and face recognition access control reader. Piggybacking off of key core technology and the success of the IrisAccess iCAM 7S Series, the iA1000 is the access control solution of the future. The iA1000 with two configurations, is equipped with capabilities to suit varied budgets as well as diverse access control needs. Key certifications of iA1000 The iA1000 meets key certifications, can be used in a variety of use cases and comes with the new iA-MS™ Depending on which configuration is chosen to secure operations, the iA1000 is equipped with a touchscreen LCD, Wi-Fi and PoE capabilities, OSDP and Wiegand protocols, and card reader that supports multiple card formats as well as mobile credentials. The iA1000 meets key certifications, can be used in a variety of use cases and comes with the new iA-MS™, a centralised web-based application for managing iA1000 devices. Impact caused by physical breaches As the access control market steadily grows in market value so does the requirement to have smart and reliable solutions that reduce network vulnerabilities, protect individual privacy and physically safeguard actual infrastructures and buildings. While most organisations focus on cybersecurity, access control deserves just as much attention and consideration as the financial impact caused by physical breaches remains significant. Security requirements The same study concluded that almost ten percent of all data breaches come from a physical breach The 2023 IBM Cost of a Data Breach Report identified the average cost of a data breach from a physical security collapse is $4.1 million. The same study concluded that almost ten percent of all data breaches come from a physical breach, and it could take up to 198 days to trace the breach back to the physical security violation and 69 additional days to repair the damage caused. Failure to meet these security requirements can also result in additional breaches and increased maintenance costs. New and unpredictable ways in the security industry “As technology continues to push the security industry in new and unpredictable ways, Iris ID prides itself with innovating Advanced Identity Authentication solutions for this market," says Mohammed Murad, VP, Iris ID Systems, Inc. "Traditional methods of providing access control such as access cards, pins and keypads and even legacy biometrics no longer offer the protections that are needed to secure physical locations. Our solutions are one step in the right direction of ensuring highest-level of security that can grow with organisations and does the most to keep bad actors at bay.”


Expert commentary
Enterprise security directors often count on an integration firm to handle jobs ranging from day-to-day activities to long-term, technology-laden projects. However, before entering a relationship, you must know what's reasonable to expect from an integrator – as not all are created equal. Here are some tips that might make the selection process easier. Completing comprehensive classwork An integrator's experience working in an enterprise environment is an obvious consideration. Ideally, that experience fits well with your business. Any enterprise experience is a plus, but local, state, and federal regulations create precise yet very different rules for securing a utility instead of a hospital. That's also true for university campuses, manufacturing facilities, and many other operations. Many manufacturers offer certifications awarded after completing comprehensive classwork and testing Look for certifications indicative of an integrator's commitment to staying on top of industry changes. Organisations such as ASIS International and the Security Industry Association offer certifications showing an integrator's team members have mastered security principles and skills. Many manufacturers offer certifications awarded after completing comprehensive classwork and testing. Also, ensure an integrator sells and services equipment that integrates with your current security systems. Using multiple systems for the same function is less efficient. Project update meetings Go beyond an integrator's slick brochures and websites to ask tough questions about previous experience. How would the integrator handle a hypothetical situation in one of your facilities? Ask the integrator if there will be one project manager for all jobs. And ensure that person handles all interactions with security subcontractors. Ask if the integrator provides regularly scheduled project update meetings. It's frustrating to wonder how your project is progressing. Ask if the integrator's team can work during the hours and days that result in the least interference to your daily operations. Ask for onsite system training to save time and eliminate travel costs. Gathering sensitive data Look for an integrator with proven experience working with an enterprise IT department A malfunctioning component may be more than an inconvenience – it may be a severe security threat. You need to know how quickly your integrator can respond when things go wrong. Ask about available service plans. And consider the embedded staff approach in which the integrator places employees on your site full time to handle day-to-day and emergency activities. Much of the security equipment – video, access control, intercoms, visitor management, and more – is wireless and dependent upon networks operated by your IT department. Network-based devices provide more opportunities for hackers to gather sensitive data or cause critical equipment to malfunction. Don't trust your security operations with an Integrator unfamiliar with at least basic cybersecurity principles. Look for an integrator with proven experience working with an enterprise IT department. At a minimum, ensure the integrator can set and change security device IP addresses and port locations. Certifications from providers such as Cisco, Microsoft, and IBM indicate an understanding of various IT technologies. Potential security partners Knowledgeable integrators work with the well-encrypted Open Supervised Data Protocol (OSDP), now an internationally recognised standard. Run from any integrator who suggests operating an access control system with used Wiegand technology offering no encryption between cards and readers. It's easy for hackers to capture data and clone a working credential. Technology moves at a rapid pace. Your modern system of a few years ago may be long-of-tooth. You need an integrator capable of bringing new and innovative ideas to the table. You want an integrator who conducts in-house testing of new products, not relying solely on a manufacturer's claims. You want an integrator capable of thinking outside the box to solve a complex security problem. These ideas are just a start in assessing an integrator's value to your enterprise operation. However, they will help you sort through potential security partners to find one that best meets your needs.
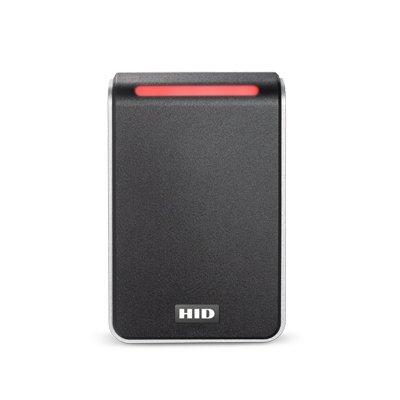
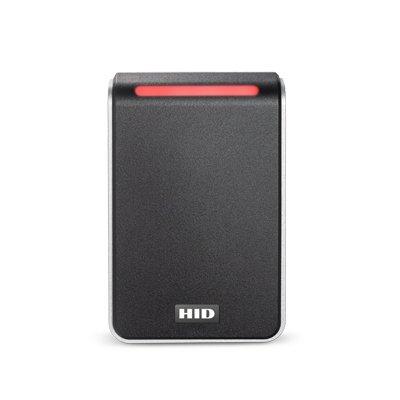
Access control and management of trusted identities are the building blocks of security, safety, and site management policies for many businesses and organisations. The current pandemic has compounded this with the introduction of new policies and regulations, particularly around social distancing and contact tracing. Most organisations will have some form of legacy access control in place, ranging from the most simplistic options, such as locks and keys, to technology-based systems. The issue with legacy systems of any type is that risks, just like technology, evolve. What was secure, convenient, and efficient a few years ago is often found wanting as the threat landscape changes. The standards governing the development and testing of physical access control systems (PACS) have also evolved to improve security and product interoperability. An example is the Open Supervised Device Protocol (OSDP), introduced 10 years ago as an alternative to the antiquated and vulnerable Clock-and-Data and Wiegand protocols. However, when it comes to planning infrastructure upgrades or implementing new tools, businesses must carry out due diligence to ensure the solutions are future-proof and deliver the expected level of security. Vulnerabilities and challenges In the early 1980s, Clock-and-Data and Wiegand protocols were widely adopted as the de-facto standard for interoperability between access control readers and physical access controllers. Those de-facto standards were later formalised and adopted into industry standards by the Security Industry Association in the 1990s. Wiegand is unencrypted and unable to protect from “man in the middle” attacks and vulnerabilities There were weaknesses, though, Wiegand is unencrypted and unable to protect from “man in the middle” attacks and vulnerabilities from the reader to the controller. Not only that, but Wiegand delivers limited range options and is operationally inefficient. It is also easy to target via its learnable language and a host of hacking devices available via online sources. Furthermore, the retrofitting installation alongside a legacy system is complicated for integrators and expensive for organisations, as most readers require dedicated home-run wiring. Extensive wiring on a large-scale project, such as a school or corporate campus, results in considerable — often prohibitive — costs for the installation of a PACS. Legacy access control protocol Despite the well-publicised vulnerabilities and weaknesses, Wiegand is still one of the most common protocols in legacy access control, with estimates indicating it is used in more than 90 percent of installed systems. This not only presents issues about physical security but also raises concerns relating to the protection of personal data. Access control systems not only contain information about who can and cannot use certain doors. OSDP is a communication standard Modern systems include a wide range of personal data, ranging from qualifications and certifications of individuals, home contact details, and even medical conditions or HR and employment information. With the potential fines associated with GDPR breaches, companies need to take this concern seriously. These weaknesses pushed the security industry to adopt a new protocol: Open Supervised Device Protocol (OSDP). This access control communications standard was developed by Mercury Security (now part of HID Global) and HID Global in 2008, and donated, free of intellectual property, to the Security Industry Association (SIA) to improve interoperability among access control and security products. Since then, it has been adopted as a standard by SIA, becoming the first secure, bidirectional reader/controller protocol to be governed by a major standards body in the security industry. In 2020 OSDP reached an additional milestone in becoming an International Electrotechnical Commission (IEC) standard. Why implement OSDP as a standard? OSDP is the only protocol that is secure and open for communication between readers and controllers The growth of networked devices, such as video and access control products, has led to an increased demand for converged solutions. Businesses and organisations recognise the value of implementing an integrated solution to enhance security and add value to technology investment. OSDP is the only protocol that is secure and open for communication between readers and controllers and is also being widely adopted by industry-leading reader and controller manufacturers. It is an evolving, ‘living standard,’ making it a safer, more robust, future-proof option for governing physical access control systems. OSDP offers important benefits: 1) Increased security Implementing OSDP standards can increase security, as OSDP with Secure Channel Protocol (SCP) supports AES-128 encryption that is required in U.S. federal government applications. Additionally, OSDP constantly monitors wiring to protect against tampering, removing the guesswork since the encryption and authentication are predefined. 2) Bidirectional communication Early on, communication protocols such as Wiegand were unidirectional, with external card readers sending information one way to a centralized access control platform. OSDP has transformed the ability for information to be collected, shared, and acted upon with the addition of bidirectional communication for configuration, status monitoring, tampering, and malfunction detection, and other valuable functions. In fact, OSDP is the only open, non-proprietary, bidirectional, secure protocol for communication between card reader and physical access controller. 3) Open and interoperable OSDP adds new technology that enhances its ability to protect incoming and outgoing data collection OSDP supports IP communications and point-to-point serial interfaces, enabling customers to flexibly enhance system functionality as needs change and new threats emerge. They also can proactively add new technology that enhances their ability to protect incoming and outgoing data collection through a physical access control system. 4) Reduced installation costs OSDP’s use of two wires (as compared to a potential of 11 wires with Wiegand) allows for multi-drop installation, supervised connections to indicate reader malfunctions, and scalability to connect more field devices. Daisy-chaining accommodates many readers connected to a single controller, eliminating the need to run home-run wiring for each reader, and the use of a four-conductor cable achieves up to 10x longer distances between reader and controller than Wiegand while also powering the reader and sending/receiving data. 5) User friendly OSDP gives credential holders greater ease of use, with audio and visual feedback such as coloured lights, audible beeps, and the ability to display alerts on the reader. For security administrators, managing and servicing OSDP-enabled readers also becomes increasingly convenient, as OSDP-enabled readers can be remotely configured from network-connected locations. Users can poll and query readers from a central location, eliminating the cost and time to physically visit and diagnose malfunctioning devices. Unlimited application enhancements OSDP streamlines installations and upgrades while saving organisations the expense of replacing readers OSDP supports advanced smartcard technology applications, including PKI/FICAM and biometrics, and other enhanced authentication protocols used in applications that require Federal Information Processing Standards (FIPS) compliance and interactive terminal capabilities. Audio-visual user feedback mechanisms provide a rich, user-centric access control environment. OSDP offers advantages for users, administrators, and integrators, alike. It adds security and real-world efficiencies, and its interoperability ensures that organisations can use systems from numerous manufacturers as they invest in infrastructure that maximises the protection of critical data. For our part, HID Global’s range of HID Signo readers is OSDP verified, ensuring they offer the intended interoperability and security for secure bidirectional communication and provide an easy migration from Wiegand devices. In a campus environment, OSDP streamlines installations and upgrades while saving organisations the expense of replacing readers if a new access control solution is implemented. There are also service and maintenance benefits as OSDP encourages continuous monitoring of system uptime and allows for remote configuration of -- or upgrades to -- a reader. Cost savings upon system upgrade Integrators can also capitalise on the introduction of OSDP by encouraging open standards, which can, in turn, help them build new customer relationships and win more projects. Although upgrading to access control systems that adhere to OSDP standards is a significant initiative, the range of benefits outweighs the cost of upgrading. Increased security coupled with business efficiencies adds value for those administering the system and a high level of interoperability ensures users can deploy systems from numerous third-party manufacturers. Integrators who understand the benefits of OSDP can also help their customers support both current and future technology requirements. When a site’s needs change, OSDP offers significant cost savings as the open functionality makes adding new devices easier and reduces the expense of requiring all readers to be replaced if a new solution is installed. Businesses and organisations transitioning to OSDP will also enhance value in terms of operational costs such as servicing and maintenance.
Today’s security industry technology standards create a common framework for achieving predictable performance. Systems are made more secure and easier to install, use and integrate with other devices. Standards are also intended to be living documents, open to continual refinements to benefit manufacturers, integrators and end users. An excellent example is the Open Supervised Data Protocol (OSDP), which is now the industry’s gold standard for physical access control installations. It was designed to offer a higher level of security with more flexible options than the aging defacto Weigand wiring standard. Updating OSDP-readers simultaneously One recent addition enables end users to push firmware and software updates to thousands of OSDP-enabled card readers simultaneouslyOSDP, first introduced in 2011 by the Security Industry Association (SIA), continues to evolve with significant manufacturer input. One recent addition enables end users to push firmware and/or software updates to a few or thousands of OSDP-enabled card readers simultaneously. Weigand technology requires updates to be made one at a time at each reader. Regularly changing reader encryption keys is an excellent way to enhance facility security. It’s easy using the OSDP file transfer capability and the latest DESFire EV2 credentials containing multiple encryption keys. You can transfer the next code on the card to all readers and the job is done. And there’s no need to create a new card for each user or reprogram each individual reader. AES-128 encryption ensures cybersecurity It’s time to migrate entirely away from Weigand technology. If greater security, convenience and reduced labour from the latest OSDP updates isn’t reason enough, here are a few more things to consider. The 40-year-old Weigand protocol provides no signal encryption, making it easy for hackers to capture the raw data transmitted between cards and readers. OSDP readers support AES-128 encryption while providing continuous monitoring of wires to guard against cybercriminals. Weigand reader installations require homerun cable pulls from the control panel to each peripheral device. OSDP readers can be daisy chained, providing additional savings on cabling and installation time. Weigand technology is simply too slow to work with today’s most versatile and secure card technologies. OSDP readers work with virtually all modern access control cards. The OSDP standard also works with biometric devices; Weigand does not. Meeting requirements of FICAM guidelines SIA is pushing to make the latest OSDP version a standard recognised by the ANSI, a move to enhance the global competitiveness of U.S. security businessesAlso, OSDP is becoming a must-have standard for organisations demanding the highest security levels. The standard meets requirements of the Federal Identity, Credential and Access Management (FICAM) guidelines that affect how the access control industry does business with the federal government. SIA is pushing to make the latest OSDP version a standard recognised by the American National Standard Institute (ANSI), a move to enhance the global competitiveness of U.S. security businesses. There’s still a large worldwide reader installation base that works solely with the Weigand protocol. Admittedly, changing them all at one time may be prohibitively expensive; however, standards should be viewed as a journey, not a destination. That’s why a measured migration is the right choice for many organisations. Begin by securing the perimeter. Replace only the outside-facing Weigand readers. As long as the walls are secured, the inside can remain a softer target until OSDP-compatible readers can be added indoors. The case for moving to OSDP as a standard is compelling. It offers our industry the opportunity to design access control software and products that provide what end users want most – greater security, flexibility and convenience.
Security beat
ISC West 2024 mirrored a vibrant industry on the precipice of accelerated change. Factors such as the cloud, artificial intelligence (AI), edge computing, and biometrics are shaping the future of the security marketplace, and they were front-and-centre at the industry’s biggest U.S. show in Las Vegas. Foot traffic was steady and impressive, including more than 29,000 security industry professionals viewing 750 exhibitors. A torrent of eager attendees crowded the lobby on the first day and could not wait for the doors to open. When they were admitted, the wealth of technological innovation and business opportunity did not disappoint. Focus on cloud systems Cloud systems were high-profile at ISC West. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference. Meanwhile, Genetec officially launched their Security Centre SaaS platform, which aims at eliminating points of friction to enable integrators to easily embrace cloud systems from quoting and ordering to provisioning and installing. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference Cloud provider Eagle Eye Networks promoted their new “Eagle Eye 911 Camera Sharing” technology under which both non-Eagle Eye Cloud VMS customers (via Eagle Eye 911 Public Safety Camera Sharing) and Eagle Eye customers can opt to share their video feeds for use by 911 operators in case of emergency. If users opt-in, 911 operators can have access to live video as an emergency unfolds. Eagle Eye Networks provides the feature by integrating with RapidSOS call centre software. Camera locations are based on geolocation coordinates, and customers can choose if they want to participate and which cameras they want to share. Biometrics in the mainstream Biometrics were well represented at ISC West, including Alcatraz AI, which introduced an outdoor version of their biometric face recognition product. The Rock X works well despite harsh lighting. Alcatraz’s products do not have to be integrated, they communicate just like a card reader using OSDP or Wiegand protocol. “At the show, customers are excited about moving to a frictionless environment and getting rid of existing credentialing,” said Tina D’Agostin, CEO and co-founder of Alcatraz. “We are making access control frictionless, secure and private. The experience can be as passive as possible – people can just walk in.” Multiple types of authentication, and the ability to detect tailgating and stream video SAFR from Real Networks also featured biometric face recognition, emphasising feature sets, convenience, and price/performance. They offer multiple types of authentication, and the ability to detect tailgating and stream video. A new device is a small mullion mount that is “approaching the price of a card reader, factoring in the need to purchase cards,” said Brad Donaldson, Vice President and General Manager. SAFR focuses on convenience: You don’t have to take out your phone to pass through a door. Enrolment is easy by incorporating existing databases, and costs are lower than competitors, said Donaldson. The system analyses multiple points on the face, turns it into data and then encrypts it, providing a “unique signature for each person.” Credentials in Apple Wallet and Google Wallet AMAG Technology announced the compatibility of credentials with the Apple Wallet and Google Wallet. The company is also embracing a new strategic direction under President David Sullivan. They launched a new website in January, are developing dynamic resources and a partner page, and they now integrate with 120 tech partners. AMAG Technology Financial Services now enables their channel partners to offer leasing and financing options to customers. The big new booth at ISC West reflected an effort to “market different and look different,” according to the company. The big new booth at ISC West reflected an effort to “market different and look different" The new Symmetry Control Room, a command-and-control system, is a relaunch of an earlier AMAG product with enhanced features. Suitable for large enterprise customers, the software enables a big video wall to display all the various systems and incorporates all the data into a single “pane of glass.” Operators can “draw a lasso” around cameras they want to display on the video wall and can follow action across multiple camera feeds. Navigating megatrends A breakfast meeting for integrators, sponsored by Assa Abloy Opening Solutions, was built around the theme “Navigating Megatrends for Sustainable Growth." The megatrends are artificial intelligence, sustainability and cybersecurity. Related to cybersecurity, there are 350 common vulnerabilities and exposures (CVE) published per week, reflecting the continuing threat to cybersecurity. Physical security has a “data lake” of information from various physical security systems that can be an attractive target for cybersecurity breaches. Data sets can be exploited and/or poisoned. The security industry needs to apply “defence in depth” to the challenges of protecting data. “The threat landscape is always changing, and security technology is an iterative process,” said Antoinette King, i-PRO’s head of cyber convergence, one of the panellists. Natural language systems Natural language systems are a newer approach making an early appearance at ISC West Natural language systems are a newer approach making an early appearance at ISC West. Brivo, for example, has an early prototype of its “natural language search capabilities” that can answer questions such as “Who is in the office?” or “Where is Bob and what has he done?” Brivo also promoted its all-in-one door station device that combines a card reader and a camera (for facial authentication) and serves as a video intercom, thus eliminating the need for multiple devices at the door. Brivo is also emphasising tailgate prevention, facial authentication, and people counting using AI at the edge. Also promoting natural language systems was Verkada, which unveiled a beta version of its AI Search feature that embraces national language capabilities. With AI Search, users will soon be able to use natural language to search for people or items. For example, a search could be “person climbing over a fence” or “person making phone call” or “person wearing football jersey.” Verkada wants to be thoughtful with the rollout and make sure effective guardrails are implemented to prevent abuse and bias. The release should happen in the coming months. Multi-family applications Allegion is promoting the XE360 hardware lock platform in various formats, including cylindrical lock, mortise lock, deadbolt and exit trim. At the show, Allegion noted an enthusiasm for multi-family applications. “We have been surprised by the people who want to add electronics and to retrofit existing multi-family facilities to compete with newer facilities,” said Henry “Butch” Holland, Allegion’s Regional Director, Channel Sales East Region. Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec Allegion also offers an “indicator” display on its locks, showing at a glance whether a door is locked or unlocked. The “indicator” might also display “occupied” or “vacant.” Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec. Integrator M&A trends Everon looks for acquisitions in areas where they do not currently have support for national accounts A conversation with Everon at ISC West provided insights into the accelerating trend of mergers and acquisitions among the integrator community. Everon, formerly ADT Commercial, has done six acquisitions of local integrators since they changed their name last year. In targeting companies to acquire, they look for a good company with a good reputation, and they consider how the new company’s competencies complement their own. Some M&A strategy is geographic, as Everon looks for acquisitions in areas where they do not currently have support for national accounts. They also consider density, seeking to add new acquisitions in larger markets where they don’t currently have a big market share. “A lot of investment is coming into security because it is seen by investors as recession-proof,” said Michael Kennedy, VP, Mergers and Acquisitions, for Everon. Kennedy met with 95 businesses last year for possible acquisition, and the company only finalised a handful – reflecting that Everon is selective and careful that corporate cultures are aligned. “With an acquisition, the goal is to keep every customer and every employee,” said Kennedy. Voice of the customer ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. “We have every kind of problem come to the booth,” commented Heather Torrey, Honeywell’s General Manager, Commercial Security, Americas. “People are passionate, interested and very specific with their questions and comments,” she said. “We are driving a complete system, but we are flexible, helping our customers to meet their needs and not try to fit every foot into the same shoe. Sometimes meeting customer needs involves working with competitors," Torrey commented. “It truly comes back to listening to the customer, not just ‘this is what we have to offer,’” she adds. ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. Edge applications are everywhere at ISC West, and one company is promoting a new approach to expand functionality at the edge. Camera company i-PRO advocates the use of the “Docker” platform for app development, an option they offer on their cameras. Docker “containers” package deep-learning algorithms to make it easier to embed software into edge devices. Anyone can run Docker apps on i-PRO cameras that use the powerful Ambarella chip. A Docker “swarm” can combine multiple edge devices to work together and share resources. For example, the approach can increase computing power at the edge to increase the capabilities of instant analytics. It’s faster and provides better redundancies. A “distributed computing platform” ensures less latency than communicating analytics to a central server. Unification of capabilities Johnson Controls (JCI) also promotes the trend of combining multiple systems into a single pane of glass. Their “Open Blue” platform, with a security version unveiled at the show, integrates various security systems into one, combining data and monitoring device health. Basically, the system manages all resources holistically. JCI also notes a trend toward “unification of capabilities,” e.g., combining access control and video. “The scope of security is evolving from a focus on protection to a broader focus on operations,” commented Julie M. Brandt, JCI’s President, Building Solutions North America.
Collaboration among manufacturers in the physical security industry can result in systems that are easier to install for integrators and that provide a better customer experience for end users. Illustrating the point is the recent collaboration among a turnstile technology company, a supplier of short-range wireless readers/writers, and a biometric business focused on ‘frictionless’ access control. “The more manufacturers collaborate with each other, the more benefits for end users,” says Steve Caroselli, the Chief Executive Officer (CEO) of Orion Entrance Control. Better collaboration means a better user experience We look for opportunities to collaborate and make sure the experience is above and beyond" Steve Caroselli adds, “Better collaboration means a better user experience. We look for opportunities to collaborate and make sure the experience is above and beyond.” Orion’s collaboration with ELATEC RFID Systems and SAFR touchless biometrics by RealNetworks Inc. highlights the advantages of manufacturers working together to ensure technologies operate smoothly in the real world. Taking ownership of the customer experience When Orion Entrance Control provides a SpeedGate swing-glass optical turnstile, they take full ownership of the customer’s experience. That means ensuring the turnstile application operates as it should, regardless of which component of the broader system might be at fault. To the customer experience, a card reader that doesn’t work is the equivalent of a turnstile that doesn’t work. Which component is at fault is irrelevant, and in fact, invisible, to the overall customer experience. Importance of dependable operation of turnstiles As the most visible element in many access control systems, dependable operation of turnstiles reflects positively on the manufacturer and on the entire system. Orion tests various third-party components with their turnstiles To ensure an optimum customer experience, Orion tests various third-party components with their turnstiles, in order to ensure flawless operation before a turnstile is delivered to a customer. Customers buying an Orion turnstile send the card readers they want to use to Orion’s corporate headquarters in Laconia, New Hampshire, USA, where Orion engineers ensure seamless operation. Ensuring optimum customer experience All readers are designed to be bolted to the wall rather than installed inside a turnstile In addition to scenario-based testing, readers are placed inside the turnstile for a streamline appearance, which can be a challenge given the variety of sizes and types of readers a customer might choose. All readers are designed to be bolted to the wall rather than installed inside a turnstile, which complicates adaptation efforts. In short, historically for Orion, ensuring the optimum customer experience involved extra time and effort, although obviously it was worth it. Providing flexibility for any environment Seeking to simplify the process, Orion has found an alternative to using many different types and models of card readers for its turnstiles. Deploying an RFID reader/writer from ELATEC provides flexibility to operate in a variety of card and reader environments, including almost all 125 kHz and 13.56 MHz contactless technologies. The product is compatible with low-frequency (LF), high-frequency (HF), near field communication (NFC) or Bluetooth Low Energy (BLE) signals. An integrated BLE module supports mobile ID and authentication solutions. There is an integrated antenna for LF and HF to ensure excellent contactless performance. ‘Universal’ configuration of the ELATEC reader hardware Using applicable firmware, the ‘universal’ configuration of the ELATEC reader hardware is compatible with any card system. It works with all the access control protocols, including SEOS, OSDP and other open protocols. “We can stock an open SKU and flash the firmware as per the customer requirement,” says Steve Caroselli. The small form factor (around 1 1/2 inches square) of the ELATEC module lends itself to easy installation inside the turnstile housing. Easy availability of the ELATEC readers helps Orion continue to serve customers, despite recent disruptions in the supply chain. And, ELATEC’s reader hardware has earned global certifications that enable Orion to use their products for customers around the world. Testing to ensure smooth operation ELATEC was responsive at every stage as the relationship evolved, providing sample equipment for testing Before embracing the ELATEC reader module, Orion tested it for several months to ensure compatibility with its turnstiles. ELATEC was responsive at every stage as the relationship evolved, providing sample equipment for testing and working closely with the Orion team. Everyone in the ELATEC sales and engineering team, right up the company’s C-suite, worked to support Orion during the testing phase. In the end, in addition to other advantages, ELATEC’s detection speed and read range compares favorably to competing technologies. “We move really fast as an organisation, so we are looking for other organisations that move very fast,” says Steve Caroselli, adding “We met with ELATEC one week and had the equipment for testing the next week. We like to work with companies that move fast, and they are culturally aligned with how we do business.” Orion turnstiles with ELATEC TWN4 Palon Compact panel The Orion turnstiles incorporate an ELATEC TWN4 Palon Compact panel, a versatile panel-mount reader designed for integration into third-party products and devices. It supports enhanced interfaces, especially RS-485, and reflects the advantages and integrated tool support of the ELATEC TWN4 family. Orion is implementing SAFR SCAN biometric technology using hardware and software from RealNetworks Inc. “The selection of ELATEC products allows Orion to provide their customers and partners with a flexible RFID reader solution that supports numerous credential options and virtually all transponder technologies,” said Paul Massey, the Chief Executive Officer (CEO) of ELATEC, Inc., adding “This is especially valuable in multi-tenet, multi-credential environments.” Orion works with all the various stakeholders – architects, consultants, integrators, and end users – to ensure total satisfaction with an installation. Biometric technology for ‘frictionless’ access control Orion is also implementing SAFR SCAN biometric technology into their turnstiles using hardware and software from RealNetworks Inc. The facial recognition reader technology, designed for mainstream commercial access control, provides a ‘frictionless’ experience, and allows users to pass through turnstiles at a walk. The system can authenticate up to 30 individuals per minute with 99.9% accuracy, despite varied lighting conditions. SAFR’s system provides a good user experience Orion designed a mounting system to incorporate the biometric reader into their turnstile design Orion designed a mounting system to incorporate the biometric reader into their turnstile design. SAFR’s system provides a good user experience, when it comes to enrollment. On each turnstile, the SAFR technology can operate separate from the ELATEC reader or in conjunction with it for multi-factor authentication in higher-security applications. Innovation for new applications A broad approach to the customer experience reflects Orion’s positioning as a technology company, in addition to being a manufacturer of turnstiles. Their Infinity software is the ecosystem ‘nerve centre’ platform to ensure operation and connected through a single ‘pane of glass.’ The need to protect more entrances beyond the lobby led Orion to develop its recently patented DoorGuard, a LIDAR-based solution that detects each person who passes through a doorway and prevents tailgating (like a turnstile) for applications, such as stairway doors, perimeter doors, data centres, IDF closets, etc. The software mimics the advantages of a turnstile to monitor access control and occupancy. Removing friction during installation and beyond Orion’s Constellation is a presence detection system that uses UWB (ultra-wideband) radar to sense where people are in a building for emergency response and building utilisation applications. “One of our core values is to remove friction and make customers’ lives easier,” says Steve Caroselli, adding “Our people-first philosophy is: What can we do to make your life better? We want to be systematic, and everything must be repeatable in terms of how we react and interact with customers.”
John Wiegand died in 1986, but the communications protocol that bears his name is still alive and well, connecting access control readers to controllers using two wires – one to transmit “zeros” and the other to transmit “ones.” The Wiegand protocol persists despite its limitations, including one-way communication, lack of encryption, and inability to manage the readers in a system centrally. In a Wiegand system, a controller provides no acknowledgement that data has been received. Systems that still use the Wiegand protocol are performing below accepted industry standards and are vulnerable to over-the-counter exploits. A session at ISC West’s Virtual Event highlighted a replacement technology that solves those problems and expands the security, flexibility and functionality of systems. The technology is called OSDP (Open Supervised Device Protocol), which is now a standard managed by the Security Industry Association (SIA) and designated as an international standard by the International Electrotechnical Commission (IEC 60839-11-5). Aligning three components OSDP requires alignment of three critical components – the access control system, readers and controllers. The access control system, readers and controllers OSDP is an RS-485 protocol used to pass card format data from the reader to the controller. Like the Wiegand protocol, it uses two wires, but in this case one wire transmits data and the other receives data. Installation is simplified because no system needs more than four wires – two for OSDP communication and two more for power. In contrast, using Wiegand, additional wires are needed to add other capabilities – up to 8 or more wires in all. OSDP cable runs can extend up to 4,000 ft (compared to 500 feet for Wiegand). Resolving problems Therefore, unlike Wiegand, OSDP sends information in both directions and provides “supervision” of the readers. If there is a problem with a reader, such as a reader communication error or disconnect, that notification is sent back to the access control management system. OSDP also supports encryption for greater security, in effect enabling end-to-end encryption for a host system, controller, I/O modules, readers and credentials. That notification is sent back to the access control management system OSDP also provides additional capabilities, such as control of a reader’s LED and buzzer as well as sending text notifications and messages to compatible displays. Integrators and/or end users can also push configuration and firmware updates to readers all at once. Because OSDP is “open,” there are more third-party integrations and standardizations. OSDP is particularly valuable for U.S. government applications because it meets federal access control requirements such as PKI for FICAM. Wiring requirements Best practice dictates rewiring a project using RS-485 cabling. Specific wiring requirements are needed for OSDP, including 24 gauge (AWG) stranded cables that are a shielded twisted pair with 120 Ohm impedance and overall lower capacitance. However, especially for shorter cable runs, existing wire from Wiegand installations can sometimes suffice, say if it is a cable run of less than 100 ft. Installers should prove their competency before being deployed to an outside installation “Installation of OSDP is not hard, just different than field technicians are used to deploying,” said Tony Diodato of Cypress Integration Solutions, one of the ISC West presenters. Therefore, training of technicians is paramount, and installers should prove their competency before being deployed to an outside installation in order to avoid problems. Integrators or installing teams should have a “lab” setup to thoroughly familiarise themselves with installation to ensure successful deployments. Various in-line devices are available to help transition existing Wiegand applications to OSDP, even if one component or other does not support OSDP. For example, data converters enable installation of an OSDP reader with a legacy Wiegand control panel. Replacing existing devices in legacy Wiegand systems with OSDP devices and using data converters can provide some benefits of OSDP without requiring a full “rip-and-replace” installation.
Case studies
Australian company High Frequency designed a “self-service” linen portal for a commercial laundry servicing the thriving short-stay accommodation market. Called the “Mobile Linen Hub”, this modified shipping container provides access to linen for users 24/7. After taking the linen they need, the cost is then added to their account as they exit the hub. Access control with Wiegand 125 kHz reader High Frequency’s initial prototype used a standard Wiegand 125 kHz reader to control access. Each customer’s card, upon scanning, granted entry to the Mobile Linen Hub while activating UHF readers inside. However, the prototype encountered several problems with its 125 kHz Wiegand readers. The readers’ lack of security allowed cards to be copied, and their lack of data storage prevented them from displaying why a card had been declined, for example. Reasons for denied entry Ultimately, the inflexibility of a 125 kHz reader led to confusion and a lot of support calls Customers only heard a ‘denial’ buzz and saw a red light. Meanwhile, there were multiple reasons a customer could be denied entry. Their card could be invalid, their account could be suspended from non-payment, or simply, someone else could be using the Mobile Linen Hub. Ultimately, the inflexibility of a 125 kHz reader led to confusion and a lot of support calls. MIFARE DESFire reader High Frequency solved the problem by switching to Idesco’s 8 CD 2.0 D Pin RFID display readers. “A highly secure MIFARE DESFire reader, 8 CD 2.0 D Pin instantly solved our card cloning issue, with zero impact on our solution since Idesco handles both our card encoding and reader programming," notes Isaac Hayes, High Frequency. “Our new system deployed a single Idesco reader on both sides of our Mobile Linen Hub, connected to an RS485/Ethernet converter, with our bespoke software communicating with them across OSDP," Isaac continues. Display reader solution High Frequency discovered that the OSDP standard made displaying private messages in an RFID reader possible This new display reader solution has greatly decreased support call frequency while increasing the product’s usability. Confusion surrounding denied access was also solved, with the reader displaying messages on its screen for users, such as “Access Granted”, “Access Denied, Account on Hold” and “Portal Busy, please wait before entering”. While looking for a new solution for their system, High Frequency discovered that the OSDP standard made displaying private messages in an RFID reader possible. “During my research, it became apparent that Idesco was the only reputable company with a colour display, OSDP-compatible reader”, Isaac Hayes recalls. Mobile access solutions enhancing security “Idesco 8 CD 2.0 D Pin reader is now an integral part of Mobile Linen Hub’s design, and will be included in all manufactured models for the foreseeable future," he reports. Idesco Oy is a pioneer of RFID technology, with more than 30 years of experience. Idesco RFID readers and transponders, mobile access solutions, controllers, and touch screen devices. Its products collect data and enhance security in several access control, vehicle identification, and logistics settings around the world. High Frequency specialises in helping commercial laundries around the world implement RFID in a way that provides value to their business.
Compania Naţională de Căi Ferate ‘CFR’ - SA, the state railway carrier of Romania, has invested in an integrated security and safety solution from Johnson Controls, to protect passengers travelling on a new railway link, connecting the Otopeni Henri Coandă International Airport to Bucharest Nord main railway station, in Bucharest, Romania. Securing Bucharest’s new rail link The 2.95 km rail link, which was planned to facilitate the large number of fans travelling from the international airport to attend the Bucharest-hosted EURO 2020 football matches and was completed in just 14 months, from the design stage, at a cost of approximately 120 million Euros, is now being increasingly used by business travellers and tourists, who wish to visit the city of Bucharest. The contract to design and execute the entire project was won, as part of a competitiveness tender process, by the Arcada – ISPCF – DB Engineering consortium. Alfred Net, a systems integrator that specialises in designing and implementing turnkey security, telecommunications and network solutions, was subsequently tasked to provide the new railway terminal’s safety and security systems, as well as the passenger communications and information systems. Need for a sophisticated security solution We were very pleased to have the opportunity to use our experience of providing sophisticated solutions" “We were very pleased to have the opportunity to use our experience of providing sophisticated solutions for complex and mission critical applications, in order to contribute to the success of this important project,” said Alex Vladutoiu, the Managing Director & Solutions Architect at Alfred Net. Alex Vladutoiu said, “With the new link terminating within the airport, we immediately realised that any security and safety solution that we recommended to the consortium would need to meet the demanding requirements of airport security, as well as railway- related EU regulations and directives.” Deep integration of security components He adds, “This meant that as well as being robust, ultra-reliable and cyber secure, the various component parts of the solution would need to be deeply integrated with each other, so as to provide control room operators with a high level of situational awareness, which would enable them to react quickly and effectively to any incidents.” Alex Vladutoiu further said, “With this in mind, our previous experience led us to recommend that all the security and safety products should be single sourced from the Johnson Controls’ access control, fire, intrusion and video surveillance brands, which come under its Tyco umbrella. Simply put, we knew these various brands could collectively provide us with everything needed to put together an effective solution for this project.” He adds, “Importantly, we were confident that the various products, which to a large extent are ‘plug & play’, could be easily integrated without the time-consuming process of developing new drivers and interfaces.” Tyco victor security management platform The Alfred Net design team specified the Tyco victor security management platform The Alfred Net design team specified the Tyco victor security management platform, to be at the heart of the safety and security solution. In addition to helping control room operators manage and monitor the images, captured by Tyco Illustra high-definition IP network cameras, victor’s graphical user interface (GUI) alerts operators in real time, as to any fire or intrusion events, as well as any access control activity. The design of the security and safety solution was based on a rigorous Risk Assessment Report, which took into account the worst case scenarios, in terms of the threat to the safety of passengers, disruption and the protection of assets. Unified security solution “By providing a unified solution, which can manage the combined data captured by the intrusion detection, access control, fire detection and video surveillance systems, victor offers authorised users with all the information they need, to monitor and strictly control the movement of passengers.” The products include: Video Surveillance & AI Analytics: In addition to the Tyco Illustra cameras and VideoEdge video recorders, which have been deployed to monitor the railway terminal proximity, mission critical machinery, platforms and areas open to the public, control room operators are also able to take advantage of video analytics, in order to help them quickly detect any suspicious activity or danger. Tripwire detection, for example, can generate an alert, if a passenger oversteps a platform’s safety line, while people counting analytics can alert security personnel to overcrowding. It can also be used by operations personnel to help them make best use of human resources, by having a greater understanding of which parts of the station are busy, at different times of the day. Access Control: A CEM Systems AC2000 access control software platform, together with eDCM350 OSDP protocol IP door controllers, are supporting smart card readers and encrypted cards, to limit access to sensitive areas throughout the railway station, such as communications, signalling, staff and locker rooms. As a highly scalable solution, AC2000 enabled Alfred Net to implement access control throughout expansive areas of the railway. By utilising RS485 serial communications with strong AES 128 encryption between the eDCM 350 intelligent door controllers, the OSDP readers and the smart cards, the railways is protected against the threat of controller signal cloning, as well as the threat of personnel card cloning. Fire Detection: Zettler Profile Flexible addressable panels, flame detectors and smoke sensors have been installed throughout the station terminal, to ensure mandatory compliance with EU fire regulations. Integration with the station’s PAVA system means that pre-recorded announcements are automatically broadcast, when a fire-related event occurs. Intrusion Detection: A DSC PowerSeries Neo intrusion system is providing protection for areas, which may be left unattended, such as cash handling areas, with integrated panic buttons to ensure there is a rapid reaction to any intrusion alarm. Johnson Controls and Alfred Net partnership Alfred Net worked closely with the Johnson Controls’ pre-sales team, in order to ensure the best products were specified for each location and application, and the comprehensive security and safety solution was installed, alongside the station’s iPIS communications and information software. Alex Vladutoiu said, “This was without doubt the most complex project that the client has been involved with and reflects its determination to invest in the latest technology, to ensure maximum operational efficiency and to protect its passengers and assets.” Video analytics and flame detection This has resulted in diverse solutions, such as video analytics and flame detection" He adds, “This has resulted in diverse solutions, such as video analytics and flame detection, based on video technology interacting with laser detection, RGB LED displays, digital signage, Text-to-Speech and many other state-of-the-art technologies, to deliver a highly effective total solution.” Since December 2020, when the new rail link became operational, the highly complex and integrated security and safety solution from Johnson Controls has been playing a key role, in ensuring the smooth operation of the train station and the running of 72 trains per day, (36 pairs), which arrive and depart every 20 minutes, both from and to the airport. Tyco suite of security products Alex Vladutoiu, Managing Director and Solutions Architect at Alfred Net, concludes “As a solution architect, Tyco is indeed my preferred security provider for integrated projects. As a unified solution, the Tyco suite of products are almost ‘plug and play’ and give you everything you need to build-up an integrated system, without spending additional time or money on developing other interfaces. He concludes, “We were delighted to have designed and implemented the new Otopeni Airport Railway Terminal project in less than one year and we look forward to our continued partnership with Tyco.”
The National Bank of Kuwait (NBK) is known as ‘The Bank You Know and Trust’. Kuwait’s largest financial institution, it has 68 branches in its homeland and more than 143 worldwide. When NBK moved its operations to newly built headquarters, it chose AEOS access control by Nedap to protect them. NBK also wanted to centralise its access control. Having already used AEOS in some locations for over a decade, it knew that this flexible, scalable system could help to achieve that. AEOS is implemented not only at NBK’s iconic headquarters, a building it owns and manages, but at its bank branches and data centres across Kuwait too. Adaptable, centralised control NBK was looking to update its security policies and take a centralised approach to monitor and controlling access. With facilities spread across Kuwait, it wanted to unify access control for employees across all its locations. NBK wanted its new security system to have the integration capabilities to fit into its IT ecosystem, it needed to be based on an open platform. Flexibility was also very important for NBK. It wanted to be able to address the changing needs of its security policies based on risk assessments, compliance regulations, and other potential future changes. Unified, central access AEOS made it possible for NBK to monitor and control access centrally and to manage daily operations After in-depth discussions, NBK was confident that Nedap could help it achieve its security goals. AEOS would provide all the features it needs such as map alarm handler, zoning, customised reporting, and lift integration. NBK’s future-proof AEOS system has been implemented and is helping the bank to manage daily operations. With just one server and database for all its locations spread across the country, NBK can monitor and control access centrally. OSDP integration One of the most important features NBK was looking for was OSDP integration with HID card readers. This project has set a benchmark in Kuwait because of its ability to connect with HID readers via the OSDP communication protocol due to AEOS blue controllers. Easier management AEOS’s visitor management module has also made it easy for NBK to capture visitor data by integrating with passport and national ID readers. And its security level functionality ensures visitor access is restricted to designated zones. A presence list feature helps to track and trace the location of employees or visitors inside the building. And it also generates alarms for the IT and security teams if someone tries are to access a zone they’re not authorised for. Extending use with integrations NBK’s AEOS system not only offers many valuable features and complies with all banking IT standards; it enables straightforward integration with technologies provided by other suppliers too. Destination control for passenger lifts has, for example, been integrated with AEOS. And a time attendance system has been integrated to record employees’ working hours and produce customised reports. Key benefits Flexibility and scalability to meet future needs Centralised monitoring and control saves time and increases security High levels of functionality add value and allow tailoring to specific requirements AEOS’s open platform enables integrations to extend the system’s capabilities “As we were making an investment that would be used across many sites, we wanted to be sure we selected absolutely the right system. Nedap proved that AEOS would provide not only the unification and specific features that we need, but the flexibility to make future adaptations and integrations too. Also, AEOS is cleverly designed around the people using it, so it brings value in terms of time saved and increased convenience, as well as improved security,” says Mr. Ezzat Hallal, General Manager - Engineering Services Expert technical support To ensure the system’s smooth running, Nedap has ensured the NBK security team has all the technical support they need. Not just during the implementation and post-implementation phases but for ongoing maintenance too.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over a two-year period by specialist security installer, Scottish Communications Group. HID Mobile Access licences University has purchased 10,000 HID Mobile Access licences to offer its academic community In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. “We wanted a modern system which is safe, secure and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. HID solution: future-proof equipment Stebbing added: “Complying with forthcoming legislation was also another important project requirement. With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we have a duty to protect to ensure everyone is safe." "The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” Ambitious development plans University of Dundee is a research institute in Scotland, noted for its academic merit in dentistry The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering and life sciences. Based in the heart of the city, it is home to over 16,000 students, 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. New HID Signo readers The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP (Open Supervised Device Protocol) and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers, thereby speeding up the rollout. RFID cards access buildings The university used to print and issue plastic RFID cards so staff and students could access buildings Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week, when some 2,500 – 3,000 undergraduate and postgraduate students enrol. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Origo management software Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, validating or revoking of IDs – all of which is now done virtually and remotely. Improve the mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Integrate with digital campus cards While the strategy and aspiration are for the university population to shift wholesale to mobile access While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach now is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO range of ID card printers Given that RFID cards are still required now, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. HID’s reputation University of Dundee utilises its FARGO DTC4500e printers to back up this shift to digital change “HID Signo readers are going in now across the main buildings, including the new Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications and authentication standards. Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” MOTORTRBO Ion smart radios In addition, Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems and CriticalArc Safezone® App, security staff need carry only a single device to fulfil their duties.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure, and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. Mobile-ready HID Signo readers The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over two years by a specialist security installer, Scottish Communications Group. In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. Safe and secure modern system “We wanted a modern system which is safe, secure, and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. “Complying with forthcoming legislation was also another important project requirement." "With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we must protect to ensure everyone is safe. The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” University of Dundee A thriving institution with ambitious development plans, it is currently building a new £40 million facility The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering, and life sciences. Based in the heart of the city, it is home to over 16,000 students, and 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting, and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. Touchless smartphone entry The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP [Open Supervised Device Protocol] and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers thereby speeding up the rollout. University's challenges Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week when some 2,500 – 3,000 undergraduate and postgraduate students enrolled. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Mobile Access Shifting to HID Mobile Access completely changes this and delivers wireless credentialling Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, and validating or revoking of IDs – all of which are done virtually and remotely. Mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Dual system approach While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO DTC4500e printers FARGO range integrates easily with the AEOS software so that Student Services staff can issue physical IDs Given RFID cards are still required, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. “HID Signo readers are going in now across the main buildings including the Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. Encryption, communications, and authentication standards “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications, and authentication standards." "Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” Motorola MOTORTRBO Ion smart radios In addition, the Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems, and CriticalArc Safezone® App, security staff need to carry only a single device to fulfill their duties.
ASSA ABLOY, the pioneer in access solutions, has received approval to utilise its integrated locking solutions on U.S. federal government access control Federal Identify, Credential, and Access Management (FICAM) applications. This significant milestone was reached after a lengthy and detailed government and third-party security vulnerability and interoperability testing process. Products The following products are on the General Services Administration’s (GSA) FIPS 201 Evaluation Program Approved Product List (APL): Corbin Russwin SN Series Integrated Lock Corbin Russwin SN Series Integrated Lock With Keypad SARGENT SN Series Integrated Lock SARGENT SN Series Integrated Lock With Keypad HES KS210 Series Integrated Server Cabinet Lock Integrated access control locks Locks feature OSDP technology that allows for secure channel and serial communication between reader and PACS These integrated access control locks feature Open Supervised Device Protocol (OSDP) technology that allows for secure channel and serial communication between the reader and the Physical Access Control System (PACS). These products were tested and approved by the U.S federal government in conjunction with the LenelS2 OnGuard® access control system, including the LNL-X4420 intelligent controller with the embedded HID® pivCLASS® Authentication Module. FICAM-approved solutions “We’re excited to expand our suite of FICAM-approved solutions for OnGuard access control system customers,” says Derek Greenland, Director, Federal Government Solutions, LenelS2. “The ASSA ABLOY integrated locks for doors and server cabinets provide high-quality choices for government facilities implementing FICAM controls to protect critical assets.” Physical access control system “We are excited to be able to offer government facilities more options to expand their PACS [physical access control system],” says Jeff Huggins, Vice President of Government Programs, ASSA ABLOY Opening Solutions. “Having these specific integrated OSDP access control locks approved for applications mandated by the Homeland Security Presidential Directive 12 (HSPD-12), along with our varying wireless, WiFi, and PoE locking options, make it easier and more affordable to support the use and implementation of card reader technology deeper into each facility, even server cabinet doors."
Australian company High Frequency designed a “self-service” linen portal for a commercial laundry servicing the thriving short-stay accommodation market. Called the “Mobile Linen Hub”, this modified shipping container provides access to linen for users 24/7. After taking the linen they need, the cost is then added to their account as they exit the hub. Access control with Wiegand 125 kHz reader High Frequency’s initial prototype used a standard Wiegand 125 kHz reader to control access. Each customer’s card, upon scanning, granted entry to the Mobile Linen Hub while activating UHF readers inside. However, the prototype encountered several problems with its 125 kHz Wiegand readers. The readers’ lack of security allowed cards to be copied, and their lack of data storage prevented them from displaying why a card had been declined, for example. Reasons for denied entry Ultimately, the inflexibility of a 125 kHz reader led to confusion and a lot of support calls Customers only heard a ‘denial’ buzz and saw a red light. Meanwhile, there were multiple reasons a customer could be denied entry. Their card could be invalid, their account could be suspended from non-payment, or simply, someone else could be using the Mobile Linen Hub. Ultimately, the inflexibility of a 125 kHz reader led to confusion and a lot of support calls. MIFARE DESFire reader High Frequency solved the problem by switching to Idesco’s 8 CD 2.0 D Pin RFID display readers. “A highly secure MIFARE DESFire reader, 8 CD 2.0 D Pin instantly solved our card cloning issue, with zero impact on our solution since Idesco handles both our card encoding and reader programming," notes Isaac Hayes, High Frequency. “Our new system deployed a single Idesco reader on both sides of our Mobile Linen Hub, connected to an RS485/Ethernet converter, with our bespoke software communicating with them across OSDP," Isaac continues. Display reader solution High Frequency discovered that the OSDP standard made displaying private messages in an RFID reader possible This new display reader solution has greatly decreased support call frequency while increasing the product’s usability. Confusion surrounding denied access was also solved, with the reader displaying messages on its screen for users, such as “Access Granted”, “Access Denied, Account on Hold” and “Portal Busy, please wait before entering”. While looking for a new solution for their system, High Frequency discovered that the OSDP standard made displaying private messages in an RFID reader possible. “During my research, it became apparent that Idesco was the only reputable company with a colour display, OSDP-compatible reader”, Isaac Hayes recalls. Mobile access solutions enhancing security “Idesco 8 CD 2.0 D Pin reader is now an integral part of Mobile Linen Hub’s design, and will be included in all manufactured models for the foreseeable future," he reports. Idesco Oy is a pioneer of RFID technology, with more than 30 years of experience. Idesco RFID readers and transponders, mobile access solutions, controllers, and touch screen devices. Its products collect data and enhance security in several access control, vehicle identification, and logistics settings around the world. High Frequency specialises in helping commercial laundries around the world implement RFID in a way that provides value to their business.
Compania Naţională de Căi Ferate ‘CFR’ - SA, the state railway carrier of Romania, has invested in an integrated security and safety solution from Johnson Controls, to protect passengers travelling on a new railway link, connecting the Otopeni Henri Coandă International Airport to Bucharest Nord main railway station, in Bucharest, Romania. Securing Bucharest’s new rail link The 2.95 km rail link, which was planned to facilitate the large number of fans travelling from the international airport to attend the Bucharest-hosted EURO 2020 football matches and was completed in just 14 months, from the design stage, at a cost of approximately 120 million Euros, is now being increasingly used by business travellers and tourists, who wish to visit the city of Bucharest. The contract to design and execute the entire project was won, as part of a competitiveness tender process, by the Arcada – ISPCF – DB Engineering consortium. Alfred Net, a systems integrator that specialises in designing and implementing turnkey security, telecommunications and network solutions, was subsequently tasked to provide the new railway terminal’s safety and security systems, as well as the passenger communications and information systems. Need for a sophisticated security solution We were very pleased to have the opportunity to use our experience of providing sophisticated solutions" “We were very pleased to have the opportunity to use our experience of providing sophisticated solutions for complex and mission critical applications, in order to contribute to the success of this important project,” said Alex Vladutoiu, the Managing Director & Solutions Architect at Alfred Net. Alex Vladutoiu said, “With the new link terminating within the airport, we immediately realised that any security and safety solution that we recommended to the consortium would need to meet the demanding requirements of airport security, as well as railway- related EU regulations and directives.” Deep integration of security components He adds, “This meant that as well as being robust, ultra-reliable and cyber secure, the various component parts of the solution would need to be deeply integrated with each other, so as to provide control room operators with a high level of situational awareness, which would enable them to react quickly and effectively to any incidents.” Alex Vladutoiu further said, “With this in mind, our previous experience led us to recommend that all the security and safety products should be single sourced from the Johnson Controls’ access control, fire, intrusion and video surveillance brands, which come under its Tyco umbrella. Simply put, we knew these various brands could collectively provide us with everything needed to put together an effective solution for this project.” He adds, “Importantly, we were confident that the various products, which to a large extent are ‘plug & play’, could be easily integrated without the time-consuming process of developing new drivers and interfaces.” Tyco victor security management platform The Alfred Net design team specified the Tyco victor security management platform The Alfred Net design team specified the Tyco victor security management platform, to be at the heart of the safety and security solution. In addition to helping control room operators manage and monitor the images, captured by Tyco Illustra high-definition IP network cameras, victor’s graphical user interface (GUI) alerts operators in real time, as to any fire or intrusion events, as well as any access control activity. The design of the security and safety solution was based on a rigorous Risk Assessment Report, which took into account the worst case scenarios, in terms of the threat to the safety of passengers, disruption and the protection of assets. Unified security solution “By providing a unified solution, which can manage the combined data captured by the intrusion detection, access control, fire detection and video surveillance systems, victor offers authorised users with all the information they need, to monitor and strictly control the movement of passengers.” The products include: Video Surveillance & AI Analytics: In addition to the Tyco Illustra cameras and VideoEdge video recorders, which have been deployed to monitor the railway terminal proximity, mission critical machinery, platforms and areas open to the public, control room operators are also able to take advantage of video analytics, in order to help them quickly detect any suspicious activity or danger. Tripwire detection, for example, can generate an alert, if a passenger oversteps a platform’s safety line, while people counting analytics can alert security personnel to overcrowding. It can also be used by operations personnel to help them make best use of human resources, by having a greater understanding of which parts of the station are busy, at different times of the day. Access Control: A CEM Systems AC2000 access control software platform, together with eDCM350 OSDP protocol IP door controllers, are supporting smart card readers and encrypted cards, to limit access to sensitive areas throughout the railway station, such as communications, signalling, staff and locker rooms. As a highly scalable solution, AC2000 enabled Alfred Net to implement access control throughout expansive areas of the railway. By utilising RS485 serial communications with strong AES 128 encryption between the eDCM 350 intelligent door controllers, the OSDP readers and the smart cards, the railways is protected against the threat of controller signal cloning, as well as the threat of personnel card cloning. Fire Detection: Zettler Profile Flexible addressable panels, flame detectors and smoke sensors have been installed throughout the station terminal, to ensure mandatory compliance with EU fire regulations. Integration with the station’s PAVA system means that pre-recorded announcements are automatically broadcast, when a fire-related event occurs. Intrusion Detection: A DSC PowerSeries Neo intrusion system is providing protection for areas, which may be left unattended, such as cash handling areas, with integrated panic buttons to ensure there is a rapid reaction to any intrusion alarm. Johnson Controls and Alfred Net partnership Alfred Net worked closely with the Johnson Controls’ pre-sales team, in order to ensure the best products were specified for each location and application, and the comprehensive security and safety solution was installed, alongside the station’s iPIS communications and information software. Alex Vladutoiu said, “This was without doubt the most complex project that the client has been involved with and reflects its determination to invest in the latest technology, to ensure maximum operational efficiency and to protect its passengers and assets.” Video analytics and flame detection This has resulted in diverse solutions, such as video analytics and flame detection" He adds, “This has resulted in diverse solutions, such as video analytics and flame detection, based on video technology interacting with laser detection, RGB LED displays, digital signage, Text-to-Speech and many other state-of-the-art technologies, to deliver a highly effective total solution.” Since December 2020, when the new rail link became operational, the highly complex and integrated security and safety solution from Johnson Controls has been playing a key role, in ensuring the smooth operation of the train station and the running of 72 trains per day, (36 pairs), which arrive and depart every 20 minutes, both from and to the airport. Tyco suite of security products Alex Vladutoiu, Managing Director and Solutions Architect at Alfred Net, concludes “As a solution architect, Tyco is indeed my preferred security provider for integrated projects. As a unified solution, the Tyco suite of products are almost ‘plug and play’ and give you everything you need to build-up an integrated system, without spending additional time or money on developing other interfaces. He concludes, “We were delighted to have designed and implemented the new Otopeni Airport Railway Terminal project in less than one year and we look forward to our continued partnership with Tyco.”
The National Bank of Kuwait (NBK) is known as ‘The Bank You Know and Trust’. Kuwait’s largest financial institution, it has 68 branches in its homeland and more than 143 worldwide. When NBK moved its operations to newly built headquarters, it chose AEOS access control by Nedap to protect them. NBK also wanted to centralise its access control. Having already used AEOS in some locations for over a decade, it knew that this flexible, scalable system could help to achieve that. AEOS is implemented not only at NBK’s iconic headquarters, a building it owns and manages, but at its bank branches and data centres across Kuwait too. Adaptable, centralised control NBK was looking to update its security policies and take a centralised approach to monitor and controlling access. With facilities spread across Kuwait, it wanted to unify access control for employees across all its locations. NBK wanted its new security system to have the integration capabilities to fit into its IT ecosystem, it needed to be based on an open platform. Flexibility was also very important for NBK. It wanted to be able to address the changing needs of its security policies based on risk assessments, compliance regulations, and other potential future changes. Unified, central access AEOS made it possible for NBK to monitor and control access centrally and to manage daily operations After in-depth discussions, NBK was confident that Nedap could help it achieve its security goals. AEOS would provide all the features it needs such as map alarm handler, zoning, customised reporting, and lift integration. NBK’s future-proof AEOS system has been implemented and is helping the bank to manage daily operations. With just one server and database for all its locations spread across the country, NBK can monitor and control access centrally. OSDP integration One of the most important features NBK was looking for was OSDP integration with HID card readers. This project has set a benchmark in Kuwait because of its ability to connect with HID readers via the OSDP communication protocol due to AEOS blue controllers. Easier management AEOS’s visitor management module has also made it easy for NBK to capture visitor data by integrating with passport and national ID readers. And its security level functionality ensures visitor access is restricted to designated zones. A presence list feature helps to track and trace the location of employees or visitors inside the building. And it also generates alarms for the IT and security teams if someone tries are to access a zone they’re not authorised for. Extending use with integrations NBK’s AEOS system not only offers many valuable features and complies with all banking IT standards; it enables straightforward integration with technologies provided by other suppliers too. Destination control for passenger lifts has, for example, been integrated with AEOS. And a time attendance system has been integrated to record employees’ working hours and produce customised reports. Key benefits Flexibility and scalability to meet future needs Centralised monitoring and control saves time and increases security High levels of functionality add value and allow tailoring to specific requirements AEOS’s open platform enables integrations to extend the system’s capabilities “As we were making an investment that would be used across many sites, we wanted to be sure we selected absolutely the right system. Nedap proved that AEOS would provide not only the unification and specific features that we need, but the flexibility to make future adaptations and integrations too. Also, AEOS is cleverly designed around the people using it, so it brings value in terms of time saved and increased convenience, as well as improved security,” says Mr. Ezzat Hallal, General Manager - Engineering Services Expert technical support To ensure the system’s smooth running, Nedap has ensured the NBK security team has all the technical support they need. Not just during the implementation and post-implementation phases but for ongoing maintenance too.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over a two-year period by specialist security installer, Scottish Communications Group. HID Mobile Access licences University has purchased 10,000 HID Mobile Access licences to offer its academic community In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. “We wanted a modern system which is safe, secure and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. HID solution: future-proof equipment Stebbing added: “Complying with forthcoming legislation was also another important project requirement. With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we have a duty to protect to ensure everyone is safe." "The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” Ambitious development plans University of Dundee is a research institute in Scotland, noted for its academic merit in dentistry The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering and life sciences. Based in the heart of the city, it is home to over 16,000 students, 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. New HID Signo readers The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP (Open Supervised Device Protocol) and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers, thereby speeding up the rollout. RFID cards access buildings The university used to print and issue plastic RFID cards so staff and students could access buildings Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week, when some 2,500 – 3,000 undergraduate and postgraduate students enrol. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Origo management software Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, validating or revoking of IDs – all of which is now done virtually and remotely. Improve the mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Integrate with digital campus cards While the strategy and aspiration are for the university population to shift wholesale to mobile access While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach now is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO range of ID card printers Given that RFID cards are still required now, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. HID’s reputation University of Dundee utilises its FARGO DTC4500e printers to back up this shift to digital change “HID Signo readers are going in now across the main buildings, including the new Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications and authentication standards. Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” MOTORTRBO Ion smart radios In addition, Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems and CriticalArc Safezone® App, security staff need carry only a single device to fulfil their duties.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure, and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. Mobile-ready HID Signo readers The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over two years by a specialist security installer, Scottish Communications Group. In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. Safe and secure modern system “We wanted a modern system which is safe, secure, and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. “Complying with forthcoming legislation was also another important project requirement." "With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we must protect to ensure everyone is safe. The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” University of Dundee A thriving institution with ambitious development plans, it is currently building a new £40 million facility The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering, and life sciences. Based in the heart of the city, it is home to over 16,000 students, and 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting, and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. Touchless smartphone entry The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP [Open Supervised Device Protocol] and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers thereby speeding up the rollout. University's challenges Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week when some 2,500 – 3,000 undergraduate and postgraduate students enrolled. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Mobile Access Shifting to HID Mobile Access completely changes this and delivers wireless credentialling Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, and validating or revoking of IDs – all of which are done virtually and remotely. Mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Dual system approach While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO DTC4500e printers FARGO range integrates easily with the AEOS software so that Student Services staff can issue physical IDs Given RFID cards are still required, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. “HID Signo readers are going in now across the main buildings including the Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. Encryption, communications, and authentication standards “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications, and authentication standards." "Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” Motorola MOTORTRBO Ion smart radios In addition, the Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems, and CriticalArc Safezone® App, security staff need to carry only a single device to fulfill their duties.
ASSA ABLOY, the pioneer in access solutions, has received approval to utilise its integrated locking solutions on U.S. federal government access control Federal Identify, Credential, and Access Management (FICAM) applications. This significant milestone was reached after a lengthy and detailed government and third-party security vulnerability and interoperability testing process. Products The following products are on the General Services Administration’s (GSA) FIPS 201 Evaluation Program Approved Product List (APL): Corbin Russwin SN Series Integrated Lock Corbin Russwin SN Series Integrated Lock With Keypad SARGENT SN Series Integrated Lock SARGENT SN Series Integrated Lock With Keypad HES KS210 Series Integrated Server Cabinet Lock Integrated access control locks Locks feature OSDP technology that allows for secure channel and serial communication between reader and PACS These integrated access control locks feature Open Supervised Device Protocol (OSDP) technology that allows for secure channel and serial communication between the reader and the Physical Access Control System (PACS). These products were tested and approved by the U.S federal government in conjunction with the LenelS2 OnGuard® access control system, including the LNL-X4420 intelligent controller with the embedded HID® pivCLASS® Authentication Module. FICAM-approved solutions “We’re excited to expand our suite of FICAM-approved solutions for OnGuard access control system customers,” says Derek Greenland, Director, Federal Government Solutions, LenelS2. “The ASSA ABLOY integrated locks for doors and server cabinets provide high-quality choices for government facilities implementing FICAM controls to protect critical assets.” Physical access control system “We are excited to be able to offer government facilities more options to expand their PACS [physical access control system],” says Jeff Huggins, Vice President of Government Programs, ASSA ABLOY Opening Solutions. “Having these specific integrated OSDP access control locks approved for applications mandated by the Homeland Security Presidential Directive 12 (HSPD-12), along with our varying wireless, WiFi, and PoE locking options, make it easier and more affordable to support the use and implementation of card reader technology deeper into each facility, even server cabinet doors."


Products


Videos
OSDP: Manufacturers & Suppliers

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download