Axis Communications Access Controllers (2)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
- Make
- Axis Communications
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasises the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
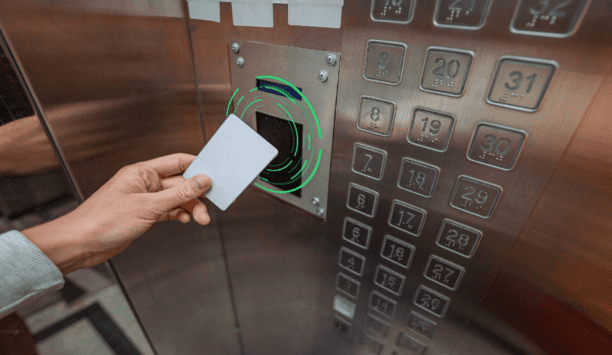
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Latest Axis Communications news

ADI | Snap One is demonstrating its expansive portfolio at ISC West 2025 from April 2 – 4, at The Venetian Expo in Las Vegas, Nevada, USA. In Booth #12043, visitors can expl...

Altronix, a recognised pioneer in power and data transmission for the professional security industry, is showcasing its latest innovations at stand 5/K30 during The Security E...

The Security Industry Association (SIA) has announced its new Board of Directors chair-elect and presented its new and returning members to the SIA Board of Directors on...
Related white papers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge
Trending topic articles
Retailers now often find themself in a precarious situation. Profit margins are being squeezed by widespread shoplifting: The Council on Criminal Justice reports that between the first half of 2023 an...
UK Connect, a pioneering connectivity and communications solutions provider, has announced a strategic partnership with BlueFort, the UK's premier independent Security Solutions Partner, to significan...
ADI | Snap One is demonstrating its expansive portfolio at ISC West 2025 from April 2 – 4, at The Venetian Expo in Las Vegas, Nevada, USA. In Booth #12043, visitors can explore an assortment of...
Rubrik announced that Rubrik Annapurna and Agentspace will explore ways to enable enterprises to securely access and utilise their data for AI-driven applications. By acting as a secure data source f...
Robotic Assistance Devices, Inc. (RAD), a subsidiary of Artificial Intelligence Technology Solutions, Inc., announced the expansion of its popular RIO™ solar-powered, mobile security solution li...
DeterTech, a pioneer in intruder detection and identification, is proud to announce the immediate availability of SmartSpray® for rental or purchase. It is considered a game-changer in tackling r...
Sentinel Photonics, a pioneering UK-based designer and manufacturer of advanced laser detection and protection systems, announces three pivotal partnerships in Eastern Europe. The company has establi...
Vodafone has connected its 200 millionth Internet of Things (IoT) device, part of a worldwide network of smart devices and machines that monitor people’s health, protect endangered animals, thwa...
Altronix, a recognised pioneer in power and data transmission for the professional security industry, is showcasing its latest innovations at stand 5/K30 during The Security Event 2025 in Birming...
The UK’s pioneering Perimeter Intrusion Detection manufacturer Harper Chalice announces it is combining product lines, brands and organisation with fellow Vitaprotech company Hirsch for their UK...
iDenfy, a US-based fraud prevention and identity verification company best known for its AI-powered RegTech automation solutions, partners with Reppublika Data Analytics & Technologies, a pioneer...
HID, a pioneer in trusted identity solutions, introduces the HID Amico™ biometric facial recognition readers—designed to address the growing demand for secure, seamless and contactless acc...
Morse Watchmans, the industry pioneer in key control and asset management systems, is highlighting its advanced solutions at stand 5/E20 during The Security Event UK 2025. The company will demonstrat...
Milestone Systems is pleased to announce the acquisition of brighter AI, effective April 1, 2025. The Berlin-based technology company, brighter AI, provides anonymisation solutions for video data base...
Corsha, the pioneer in securing machine-to-machine (M2M) traffic for operational systems and critical infrastructure. Has announced an $18 million Series A-1 funding round led by SineWave Ventures, w...
A modern guide to data loss prevention
Download7 proven solutions for law enforcement key control and asset management
DownloadThe truth behind 9 mobile access myths
DownloadAccess control system planning phase 2
DownloadSecurity practices for hotels
Download