PTZ cameras
LOOKOUT, a pioneering provider of marine AI systems for safety, announced the expansion of its product line by introducing a new camera featuring an integrated navigation light. This new camera system offers enhanced safety and greater installation flexibility and is available in LOOKOUT's classic blue and white, matte black with carbon accents and custom colours by request, to complement a wider range of vessel designs. Advanced AI vision cameras LOOKOUT has solved a common installation dile...
Omada by TP-Link and VIGI by TP-Link, TP-Link Systems Inc.’s exclusive business solutions brands, are set to make waves at ISC West 2025 with the debut of their groundbreaking unified networking and surveillance solutions. At the event, the brands will showcase a seamless integration of VIGI’s cutting-edge surveillance solutions, Omada’s comprehensive networking systems, and the Omada Central platform—a revolutionary cloud-based solution that unifies the management of ne...
3xLOGIC, a pioneering provider of integrated and intelligent security and business solutions, will showcase new product developments for video management, and business intelligence solutions at The Security Event 2025. It will promote the launch of VIGIL 13 – the latest software and camera release for its advanced video management solution. This solution increases functionality and improves performance for new and existing 3xLOGIC customers. New video management solutions VI...
At The Security Show (TSE), on stand 5/G55, i-PRO Co., Ltd. (formerly Panasonic Security), a pioneering manufacturer of edge computing cameras for security and public safety, will showcase its brand new U-series range of AI-powered cameras for the first time in the UK. Designed and manufactured in Japan, the U-Series delivers the accuracy of AI-based object detection to entry-level security installations. Benefit from AI-driven analytics U-Series delivers the accuracy of A...
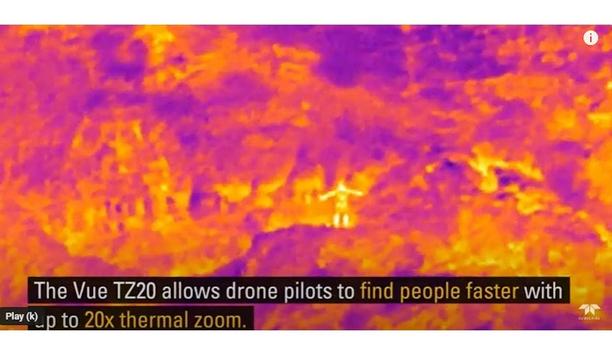
LVT (LiveView Technologies, Inc.), the pioneer of rapidly deployable security solutions, announced multiple new capabilities powered by proprietary AI models that empower security teams to implement proactive, data-driven security strategies for 24/7 coverage in any environment. The capabilities, currently in beta, include industry-first agentic AI-powered personalised audio messages that automatically detect, validate, and deter by referencing identifiable features of an individual, a pan/tilt...
Quanergy Solutions, Inc., the pioneer in high-performance 3D LiDAR security and smart space solutions, is highlighting its expanded integrations with industry-leading security partners Hanwha Vision and Avigilon at ISC West 2025 booth #29081. The integration of Quanergy’s advanced 3D LiDAR solutions with Hanwha’s Wisenet WAVE 6.0 VMS and Motorola’s Avigilon Unity On-Premise Video Security Platform delivers enhanced perimeter security, intrusion detection, and object classifica...
News
Konica Minolta has announced the sale of its entire 65% stake in MOBOTIX AG, along with all associated shareholder loans, to CERTINA Software Investments AG, a 100% subsidiary of the Munich-based family equity investor CERTINA Group. The CERTINA Software Division of CERTINA Group specialises in the development and expansion of technology-driven businesses worldwide. CERTINA expands portfolio KONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globallyKONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globally. CERTINA acquires the stock-listed MOBOTIX AG shares from KONICA MINOLTA and strengthens its software division. Acquisition of an established software and hardware manufacturer of high-end video and surveillance systems Strategic step to further expand the existing CERTINA Software Division and strengthen joint development activities Increased sales The purchase price has not been disclosed, including to the company. Closing is expected to occur in May 2025, and will be subject to mandatory antitrust clearance. The divestment is part of KONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globally, as outlined in their recent statement. KONICA MINOLTA’s Imaging-IoT Solutions business will continue to provide highly value-added video solution services centered on security and safety. KONICA MINOLTA will keep sourcing from MOBOTIX also in the future. A new chapter for MOBOTIX AG The CERTINA Software Division of CERTINA Group specialises in the development and expansion of technology-driven businesses worldwide. With a strong track record in strategic investments and business transformation, CERTINA brings deep industry expertise and financial backing to support MOBOTIX’s next phase of growth. By leveraging synergies within its broader portfolio, CERTINA aims to enhance MOBOTIX’s market position and drive continued innovation in security and video solutions. MOBOTIX joins CERTINA Tobias Eiblmeier, Head of Mergers & Acquisitions CERTINA Group: “The acquisition of MOBOTIX is a strategic step to further strengthen our software investments and underlines our long-term growth ambitions in our Group.” "We are excited to bring MOBOTIX into our portfolio, as we firmly believe our strategic expertise and commitment to innovation provide the best home for its future. By leveraging synergies with our existing technology investments, we are committed to supporting MOBOTIX’s next phase of growth and market pioneership," said Giovanni Santamaria, Managing Partner of CERTINA´s Software division. Revitalising MOBOTIX vision “We look forward to working with CERTINA as a strong partner on our side. The combination of our unique hardware designs with innovative software solutions on the edge based on our MOBOTIX DNA will bring exciting opportunities to grow together while utilising the synergies from all portfolio companies”, stated Christian Cabirol, CTO of MOBOTIX AG. Klaus Kiener, CFO of MOBOTIX AG, adds: “This transaction will also revitalise the MOBOTIX equity story for our 35% minority shareholders”. Transition and governance changes CERTINA intends to be represented on the supervisory board of MOBOTIX AGIt is expected that all current members of the supervisory board of MOBOTIX AG will resign in the course of the closing of the transaction. CERTINA intends to be appropriately represented on the supervisory board of MOBOTIX AG. Additionally, key pioneership updates include: Klaus Kiener (CFO) and Christian Cabirol (CTO) have extended their contracts until March 2027, ensuring continuity in financial and technological pioneership. Thomas Lausten (CEO) will leave MOBOTIX in mutual understanding at the end of his current contract in June 2025, working closely with the new pioneership team to ensure a smooth transition until then. Next steps for growth “It has been a pleasure to work with our many colleagues, partners and customers around the world during the past 8 years and it is now a good time to change pioneership with a new investor. CERTINA will bring significant value to our company with their experience in technology companies and I look forward to work with Giovanni Santamaria, Tobias Eiblmeier and their teams during the transition next months”, says Thomas Lausten.
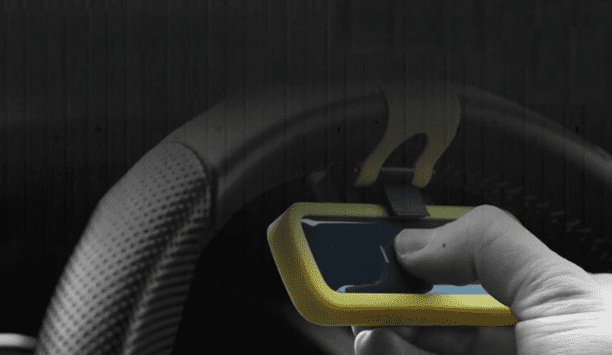
Pyronix announces new campaign offering a complimentary CarDefender inside every Enforcer Kit purchase, in promotion-labelled packs and while stocks last in distributors. This promotion will give installers immediate access to a free, award-winning peripheral when they buy one of our best-selling products. Next-gen auto safety The device’s inbuilt shock/tilt sensor offers three configurable detection modesThe CarDefender is an innovative wireless peripheral offering protection against car and vehicle theft. The device’s inbuilt shock/tilt sensor offers three configurable detection modes which ensures any unwanted interference with a vehicle will trigger the home’s alarm, when connected to and in range of the Pyronix security system. This multi-award-winning peripheral (including Innovative Security Project of the Year at the British Security Awards) is a novel device that may be unfamiliar to many homeowners, so the free product offering is a great way to introduce the CarDefender into the installer’s sales conversations with customers. Smart theft protection “We developed the CarDefender because we saw an opportunity to help combat the rising trend of vehicle theft, especially with the recent emergence of wireless key theft,” commented Laurence Kenny, Product Director at Pyronix. “We have created an innovative product to tackle theft of all vehicles, from cars to vans and bikes/e-bikes, and even farming equipment.” Wireless security solutions The kits are an ideal way to begin building an alarm system, alongside a range of wireless peripherals The free CarDefender is inside labelled, promotional boxes of our range of Enforcer Kits. This includes Enforcer Kits 1-6 as well as both of the Enforcer Arming Station Kits – the whole range. The kits are an ideal way to begin building an alarm system and come with our flagship wireless panel, the Enforcer V11, alongside a range of wireless peripherals including shocks, contacts, PIR detectors and Deltabell modules, depending on which kit is purchased. The Enforcer V11 is also compatible with our free smartphone app, HomeControl2.0, meaning that homeowners are able to control the entire Pyronix ecosystem from anywhere. Cloud-powered growth For installers, app connectivity also introduces an upselling opportunity for cloud subscriptions, which can also result in recurring revenue benefits. An Enforcer Kit creates the core of a security system which can then be added to when tailoring an install to the specific needs of the customer, and now installers can include a free CarDefender too.
Motorola Solutions announced the new Pelco, an innovative portfolio of artificial-intelligence-powered devices that are purpose-built for enterprises operating in some of the most challenging environments, like oil and gas and ports. Backed by the company’s deep engineering expertise and significant investments in research and development. Smart surveillance The portfolio brings together specialised security technologies from the strategic acquisitions of VideotecPelco’s device lineup features fixed cameras, ruggedised and long-range cameras, smart sensors and AI analytics that easily integrate with a broad set of third-party video management systems (VMS). Since acquiring Pelco in 2020, Motorola Solutions has completely transformed the camera line, which has more than doubled in breadth since the company brought engineering and design in-house. Under a contemporary new Pelco mark, the portfolio brings together specialised security technologies from the strategic acquisitions of Videotec, IP Video and Silent Sentinel. Advanced threat detection “Pelco provides security operators with robust AI-powered security solutions capable of performing across a wide range of environmental conditions,” said Hamish Dobson, corporate vice president, Pelco. “We’ve purposefully created Pelco to combine rugged hardware, state-of-the-art sensing and AI-powered analytics for a VMS-agnostic device portfolio that is driving higher standards in critical infrastructure security.” Expanding security solutions Expansions to the portfolio broaden growth opportunities with enterprises and critical infrastructure verticals like transportation, aviation, maritime and utilities. Such operations routinely endure extreme weather, corrosive elements and other hazardous conditions where standard security cameras and devices would quickly be damaged. Precision in protection Pelco’s new specialised portfolio includes: Esprit Anti-Corrosion cameras that can withstand the harsh elements of maritime environments. The ExSite Enhanced Thermal 2 fixed camera, which gives hazardous sites like power plants a thermal imaging security camera with global explosion-proof certifications. The Halo Smart Sensor, an all-in-one intelligent sensor that protects privacy while detecting events like vaping, gunshots, abnormal noises, motion and emergency keywords like “help.” The Aeron and Jaegar cameras, which offer detection capabilities at distances of up to 20 miles in extreme environments associated with military, aviation, maritime and critical infrastructure. All Pelco devices are supported by Elevate, a cloud-based camera support platform. Elevate assesses camera health and expands the sensing capabilities of the camera with cloud-based AI. Future-ready surveillance Pelco devices are engineered to be compatible with Open Network Video Interface Forum (ONVIF) -conformant systems, simplifying installation, enabling flexible integrations and alleviating costly system overhauls. Pelco IP cameras enable regulatory compliance with the current National Defense Authorisation Act (NDAA) Sec. 889 rules for the procurement of secure equipment. Experience the new Pelco at booth #14059 at ISC West from April 2-4 in Las Vegas.
FLIR, pioneer in high-performance marine thermal-imaging systems, announced the launch of the new FLIR JCU-4 remote control, offering precision camera control and an elevated, yet simplified user experience. Providing confident control of FLIR marine thermal and visible cameras, the FLIR JCU-4 remote control is designed for FLIR marine cameras and is compatible with the M232, M300, M400/M400XR and M500 series, as well as legacy models. It offers pan, tilt, and zoom capabilities, and control of all additional camera functions with an ergonomic keypad and responsive joystick control. Camera operation and easy access The JCU-4 is a meaningful upgrade for those who actively navigate using thermal technology Designed by mariners, for mariners, the JCU-4 is a meaningful upgrade for those who actively navigate using thermal technology and require dependable and intuitive control of their FLIR camera. The rugged, low-profile three-axis joystick is mounted with a 2.9-inch colour LCD and keypad, to simplify camera operation and offer easy access to the joystick setup menus. A dimmable colour LCD and back-lit keypad preserves the operator’s vision during nighttime operations. User-defined camera functions The JCU-4 can be easily configured with intuitive pairing between FLIR marine cameras and marine monitors or chartplotters. Three custom keys can be pre-programmed for quick access to the most used user-defined camera functions. The FLIR JCU-4 is available for $1,699 USD.
Hanwha Vision, a pioneer in security and surveillance solutions, introduces the TNO-A26081, an ultra-high-resolution AI-powered camera designed to deliver unmatched imaging clarity and powerful analytical capabilities. With 26MP resolution at 30 frames per second, this camera captures every detail, making it ideal for large-area surveillance and high-security environments. Furthermore, its AI features ensure precise object detection, improved operational efficiency, and seamless integration into modern surveillance systems. Crystal-clear view and versatile AI-based analytics provide business intelligence abilities, including people and vehicle counting The TNO-A26081's 26MP resolution offers a level of detail surpassing 4K cameras, ensuring that even the smallest details are captured in real time. Ideal for stadiums and arenas, this camera addresses critical safety and crowd control needs. Its AI-based analytics provide business intelligence capabilities, including people and vehicle counting, queue management, and heat mapping, helping users manage events more efficiently. Whether operators are monitoring large outdoor areas, parking lots, or high-traffic locations, this camera provides crystal-clear images that ensure no detail is missed. Essential for security and operational efficiency With its high sensitivity, the TNO-A26081 is also perfect for critical surveillance points, such as airports, seaports, and manufacturing sites, where capturing fine details can be essential for security and operational efficiency. The model is equipped with a built-in zoom lens (55-250mm), for a versatile field of view that allows users to zoom in on distant subjects while capturing wide areas with ease. Its adjustable field of view is ideal for large outdoor spaces, enabling detailed surveillance without the need for multiple cameras. Powerful AI analytics With AI-based motion detection, the camera reduces false alarms by distinguishing between human movement, animals, and other motion, for example swaying trees or shadows, ensuring only relevant events are flagged to operators. The WiseAI app, pre-installed on this camera, includes advanced object attribute extraction capabilities, recognising identifiers such as clothing colour (upper/lower), and whether a person is wearing a mask or glasses. For vehicles, it detects type (car, truck, bus, motorcycle, bicycle) and colour, enhancing forensic investigations and enabling precise monitoring. Complementary AI pack licences Camera’s abilities can be further enhanced with one of two complementary AI pack licences Furthermore, the camera’s capabilities can be further enhanced with one of two complementary AI pack licences, designed for traffic or industrial applications, to offer tailored analytics that bolster operations. Blocked exit detection, slip and fall detection, and forklift detection, are examples of key features that can be found across the packs. Excelling in low-light, harsh conditions Equipped with an APS-C CMOS sensor, the TNO-A26081 excels in low-light conditions, ensuring clear images day and night. Its superior low-light capabilities allow for continuous surveillance even in challenging lighting environments. This ensures that security teams can rely on the camera to deliver consistent and high-quality footage, regardless of the time of day or lighting conditions. The model is built to withstand all manner of environments. Its robust design, including IP67-rated weather-proofing and IK10 impact resistance, plus an expansive operating temperature of −40°C to 55°C, ensures that the camera can function reliably in extreme conditions, whether it is mounted outdoors in harsh weather or in high-traffic areas prone to physical impact.
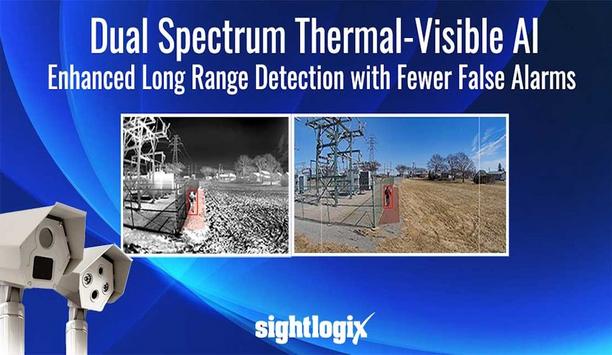
SightLogix, a pioneer in intelligent outdoor security solutions, has announced dual-spectrum AI for its dual-sensor SightSensor product series. This new capability integrates thermal and visible AI validation, providing unmatched, real-time intrusion detection that minimises false alarms. Reliable and immediate awareness is mandatory for high-performing perimeter security solutions in critical infrastructure and commercial remote video monitoring applications. Edge-based intelligence The dual-spectrum AI capability uses visible and thermal AI false alarm filteringThe dual-spectrum AI capability for dual-sensor SightSensor cameras uses visible and thermal AI false alarm filtering, which correlates image detection from both thermal and visible video in real-time to validate threats. Built-in AI processing and analytics, more commonly known as “edged-based processing,” from visible and thermal sensors provide the highest levels of accuracy within a singular camera that excels in total darkness, optimal lighting, and any weather, including fog, rain, or extremely harsh conditions. Precision in security “Dual-spectrum AI significantly enhances security operations by instantly distinguishing real threats from environmental noise, ensuring highly accurate detection and reliable alarms. Customers can be confident that their security teams are only responding to real threats improving efficiency and increasing profitability,” states Babak Shir, vice president of engineering, SightLogix. “With the AI operating entirely within the camera, there is reduced network bandwidth demand, eliminating the need for additional servers, thus lowering overall system costs.” Enhanced AI Security The new dual-spectrum AI capability is a free firmware upgrade for existing SightSensor HD and SightSensor TC4 cameras, ensuring seamless integration for commercial and critical security applications.
Konica Minolta has announced the sale of its entire 65% stake in MOBOTIX AG, along with all associated shareholder loans, to CERTINA Software Investments AG, a 100% subsidiary of the Munich-based family equity investor CERTINA Group. The CERTINA Software Division of CERTINA Group specialises in the development and expansion of technology-driven businesses worldwide. CERTINA expands portfolio KONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globallyKONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globally. CERTINA acquires the stock-listed MOBOTIX AG shares from KONICA MINOLTA and strengthens its software division. Acquisition of an established software and hardware manufacturer of high-end video and surveillance systems Strategic step to further expand the existing CERTINA Software Division and strengthen joint development activities Increased sales The purchase price has not been disclosed, including to the company. Closing is expected to occur in May 2025, and will be subject to mandatory antitrust clearance. The divestment is part of KONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globally, as outlined in their recent statement. KONICA MINOLTA’s Imaging-IoT Solutions business will continue to provide highly value-added video solution services centered on security and safety. KONICA MINOLTA will keep sourcing from MOBOTIX also in the future. A new chapter for MOBOTIX AG The CERTINA Software Division of CERTINA Group specialises in the development and expansion of technology-driven businesses worldwide. With a strong track record in strategic investments and business transformation, CERTINA brings deep industry expertise and financial backing to support MOBOTIX’s next phase of growth. By leveraging synergies within its broader portfolio, CERTINA aims to enhance MOBOTIX’s market position and drive continued innovation in security and video solutions. MOBOTIX joins CERTINA Tobias Eiblmeier, Head of Mergers & Acquisitions CERTINA Group: “The acquisition of MOBOTIX is a strategic step to further strengthen our software investments and underlines our long-term growth ambitions in our Group.” "We are excited to bring MOBOTIX into our portfolio, as we firmly believe our strategic expertise and commitment to innovation provide the best home for its future. By leveraging synergies with our existing technology investments, we are committed to supporting MOBOTIX’s next phase of growth and market pioneership," said Giovanni Santamaria, Managing Partner of CERTINA´s Software division. Revitalising MOBOTIX vision “We look forward to working with CERTINA as a strong partner on our side. The combination of our unique hardware designs with innovative software solutions on the edge based on our MOBOTIX DNA will bring exciting opportunities to grow together while utilising the synergies from all portfolio companies”, stated Christian Cabirol, CTO of MOBOTIX AG. Klaus Kiener, CFO of MOBOTIX AG, adds: “This transaction will also revitalise the MOBOTIX equity story for our 35% minority shareholders”. Transition and governance changes CERTINA intends to be represented on the supervisory board of MOBOTIX AGIt is expected that all current members of the supervisory board of MOBOTIX AG will resign in the course of the closing of the transaction. CERTINA intends to be appropriately represented on the supervisory board of MOBOTIX AG. Additionally, key pioneership updates include: Klaus Kiener (CFO) and Christian Cabirol (CTO) have extended their contracts until March 2027, ensuring continuity in financial and technological pioneership. Thomas Lausten (CEO) will leave MOBOTIX in mutual understanding at the end of his current contract in June 2025, working closely with the new pioneership team to ensure a smooth transition until then. Next steps for growth “It has been a pleasure to work with our many colleagues, partners and customers around the world during the past 8 years and it is now a good time to change pioneership with a new investor. CERTINA will bring significant value to our company with their experience in technology companies and I look forward to work with Giovanni Santamaria, Tobias Eiblmeier and their teams during the transition next months”, says Thomas Lausten.
Pyronix announces new campaign offering a complimentary CarDefender inside every Enforcer Kit purchase, in promotion-labelled packs and while stocks last in distributors. This promotion will give installers immediate access to a free, award-winning peripheral when they buy one of our best-selling products. Next-gen auto safety The device’s inbuilt shock/tilt sensor offers three configurable detection modesThe CarDefender is an innovative wireless peripheral offering protection against car and vehicle theft. The device’s inbuilt shock/tilt sensor offers three configurable detection modes which ensures any unwanted interference with a vehicle will trigger the home’s alarm, when connected to and in range of the Pyronix security system. This multi-award-winning peripheral (including Innovative Security Project of the Year at the British Security Awards) is a novel device that may be unfamiliar to many homeowners, so the free product offering is a great way to introduce the CarDefender into the installer’s sales conversations with customers. Smart theft protection “We developed the CarDefender because we saw an opportunity to help combat the rising trend of vehicle theft, especially with the recent emergence of wireless key theft,” commented Laurence Kenny, Product Director at Pyronix. “We have created an innovative product to tackle theft of all vehicles, from cars to vans and bikes/e-bikes, and even farming equipment.” Wireless security solutions The kits are an ideal way to begin building an alarm system, alongside a range of wireless peripherals The free CarDefender is inside labelled, promotional boxes of our range of Enforcer Kits. This includes Enforcer Kits 1-6 as well as both of the Enforcer Arming Station Kits – the whole range. The kits are an ideal way to begin building an alarm system and come with our flagship wireless panel, the Enforcer V11, alongside a range of wireless peripherals including shocks, contacts, PIR detectors and Deltabell modules, depending on which kit is purchased. The Enforcer V11 is also compatible with our free smartphone app, HomeControl2.0, meaning that homeowners are able to control the entire Pyronix ecosystem from anywhere. Cloud-powered growth For installers, app connectivity also introduces an upselling opportunity for cloud subscriptions, which can also result in recurring revenue benefits. An Enforcer Kit creates the core of a security system which can then be added to when tailoring an install to the specific needs of the customer, and now installers can include a free CarDefender too.
Motorola Solutions announced the new Pelco, an innovative portfolio of artificial-intelligence-powered devices that are purpose-built for enterprises operating in some of the most challenging environments, like oil and gas and ports. Backed by the company’s deep engineering expertise and significant investments in research and development. Smart surveillance The portfolio brings together specialised security technologies from the strategic acquisitions of VideotecPelco’s device lineup features fixed cameras, ruggedised and long-range cameras, smart sensors and AI analytics that easily integrate with a broad set of third-party video management systems (VMS). Since acquiring Pelco in 2020, Motorola Solutions has completely transformed the camera line, which has more than doubled in breadth since the company brought engineering and design in-house. Under a contemporary new Pelco mark, the portfolio brings together specialised security technologies from the strategic acquisitions of Videotec, IP Video and Silent Sentinel. Advanced threat detection “Pelco provides security operators with robust AI-powered security solutions capable of performing across a wide range of environmental conditions,” said Hamish Dobson, corporate vice president, Pelco. “We’ve purposefully created Pelco to combine rugged hardware, state-of-the-art sensing and AI-powered analytics for a VMS-agnostic device portfolio that is driving higher standards in critical infrastructure security.” Expanding security solutions Expansions to the portfolio broaden growth opportunities with enterprises and critical infrastructure verticals like transportation, aviation, maritime and utilities. Such operations routinely endure extreme weather, corrosive elements and other hazardous conditions where standard security cameras and devices would quickly be damaged. Precision in protection Pelco’s new specialised portfolio includes: Esprit Anti-Corrosion cameras that can withstand the harsh elements of maritime environments. The ExSite Enhanced Thermal 2 fixed camera, which gives hazardous sites like power plants a thermal imaging security camera with global explosion-proof certifications. The Halo Smart Sensor, an all-in-one intelligent sensor that protects privacy while detecting events like vaping, gunshots, abnormal noises, motion and emergency keywords like “help.” The Aeron and Jaegar cameras, which offer detection capabilities at distances of up to 20 miles in extreme environments associated with military, aviation, maritime and critical infrastructure. All Pelco devices are supported by Elevate, a cloud-based camera support platform. Elevate assesses camera health and expands the sensing capabilities of the camera with cloud-based AI. Future-ready surveillance Pelco devices are engineered to be compatible with Open Network Video Interface Forum (ONVIF) -conformant systems, simplifying installation, enabling flexible integrations and alleviating costly system overhauls. Pelco IP cameras enable regulatory compliance with the current National Defense Authorisation Act (NDAA) Sec. 889 rules for the procurement of secure equipment. Experience the new Pelco at booth #14059 at ISC West from April 2-4 in Las Vegas.
FLIR, pioneer in high-performance marine thermal-imaging systems, announced the launch of the new FLIR JCU-4 remote control, offering precision camera control and an elevated, yet simplified user experience. Providing confident control of FLIR marine thermal and visible cameras, the FLIR JCU-4 remote control is designed for FLIR marine cameras and is compatible with the M232, M300, M400/M400XR and M500 series, as well as legacy models. It offers pan, tilt, and zoom capabilities, and control of all additional camera functions with an ergonomic keypad and responsive joystick control. Camera operation and easy access The JCU-4 is a meaningful upgrade for those who actively navigate using thermal technology Designed by mariners, for mariners, the JCU-4 is a meaningful upgrade for those who actively navigate using thermal technology and require dependable and intuitive control of their FLIR camera. The rugged, low-profile three-axis joystick is mounted with a 2.9-inch colour LCD and keypad, to simplify camera operation and offer easy access to the joystick setup menus. A dimmable colour LCD and back-lit keypad preserves the operator’s vision during nighttime operations. User-defined camera functions The JCU-4 can be easily configured with intuitive pairing between FLIR marine cameras and marine monitors or chartplotters. Three custom keys can be pre-programmed for quick access to the most used user-defined camera functions. The FLIR JCU-4 is available for $1,699 USD.
Hanwha Vision, a pioneer in security and surveillance solutions, introduces the TNO-A26081, an ultra-high-resolution AI-powered camera designed to deliver unmatched imaging clarity and powerful analytical capabilities. With 26MP resolution at 30 frames per second, this camera captures every detail, making it ideal for large-area surveillance and high-security environments. Furthermore, its AI features ensure precise object detection, improved operational efficiency, and seamless integration into modern surveillance systems. Crystal-clear view and versatile AI-based analytics provide business intelligence abilities, including people and vehicle counting The TNO-A26081's 26MP resolution offers a level of detail surpassing 4K cameras, ensuring that even the smallest details are captured in real time. Ideal for stadiums and arenas, this camera addresses critical safety and crowd control needs. Its AI-based analytics provide business intelligence capabilities, including people and vehicle counting, queue management, and heat mapping, helping users manage events more efficiently. Whether operators are monitoring large outdoor areas, parking lots, or high-traffic locations, this camera provides crystal-clear images that ensure no detail is missed. Essential for security and operational efficiency With its high sensitivity, the TNO-A26081 is also perfect for critical surveillance points, such as airports, seaports, and manufacturing sites, where capturing fine details can be essential for security and operational efficiency. The model is equipped with a built-in zoom lens (55-250mm), for a versatile field of view that allows users to zoom in on distant subjects while capturing wide areas with ease. Its adjustable field of view is ideal for large outdoor spaces, enabling detailed surveillance without the need for multiple cameras. Powerful AI analytics With AI-based motion detection, the camera reduces false alarms by distinguishing between human movement, animals, and other motion, for example swaying trees or shadows, ensuring only relevant events are flagged to operators. The WiseAI app, pre-installed on this camera, includes advanced object attribute extraction capabilities, recognising identifiers such as clothing colour (upper/lower), and whether a person is wearing a mask or glasses. For vehicles, it detects type (car, truck, bus, motorcycle, bicycle) and colour, enhancing forensic investigations and enabling precise monitoring. Complementary AI pack licences Camera’s abilities can be further enhanced with one of two complementary AI pack licences Furthermore, the camera’s capabilities can be further enhanced with one of two complementary AI pack licences, designed for traffic or industrial applications, to offer tailored analytics that bolster operations. Blocked exit detection, slip and fall detection, and forklift detection, are examples of key features that can be found across the packs. Excelling in low-light, harsh conditions Equipped with an APS-C CMOS sensor, the TNO-A26081 excels in low-light conditions, ensuring clear images day and night. Its superior low-light capabilities allow for continuous surveillance even in challenging lighting environments. This ensures that security teams can rely on the camera to deliver consistent and high-quality footage, regardless of the time of day or lighting conditions. The model is built to withstand all manner of environments. Its robust design, including IP67-rated weather-proofing and IK10 impact resistance, plus an expansive operating temperature of −40°C to 55°C, ensures that the camera can function reliably in extreme conditions, whether it is mounted outdoors in harsh weather or in high-traffic areas prone to physical impact.
SightLogix, a pioneer in intelligent outdoor security solutions, has announced dual-spectrum AI for its dual-sensor SightSensor product series. This new capability integrates thermal and visible AI validation, providing unmatched, real-time intrusion detection that minimises false alarms. Reliable and immediate awareness is mandatory for high-performing perimeter security solutions in critical infrastructure and commercial remote video monitoring applications. Edge-based intelligence The dual-spectrum AI capability uses visible and thermal AI false alarm filteringThe dual-spectrum AI capability for dual-sensor SightSensor cameras uses visible and thermal AI false alarm filtering, which correlates image detection from both thermal and visible video in real-time to validate threats. Built-in AI processing and analytics, more commonly known as “edged-based processing,” from visible and thermal sensors provide the highest levels of accuracy within a singular camera that excels in total darkness, optimal lighting, and any weather, including fog, rain, or extremely harsh conditions. Precision in security “Dual-spectrum AI significantly enhances security operations by instantly distinguishing real threats from environmental noise, ensuring highly accurate detection and reliable alarms. Customers can be confident that their security teams are only responding to real threats improving efficiency and increasing profitability,” states Babak Shir, vice president of engineering, SightLogix. “With the AI operating entirely within the camera, there is reduced network bandwidth demand, eliminating the need for additional servers, thus lowering overall system costs.” Enhanced AI Security The new dual-spectrum AI capability is a free firmware upgrade for existing SightSensor HD and SightSensor TC4 cameras, ensuring seamless integration for commercial and critical security applications.


Expert commentary
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximise your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimise your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
Open platform video technology software is more than just a product; it's a tool that helps customers achieve their desired business outcomes. Safety, round-the-clock security, and increased operational efficiencies are now the norm due to video technology. Responsible Technology Despite humanity’s impressive technological advances, we also recognise the immense responsibility that comes with technological innovation. It's not enough to focus solely on the positive impact video technology can make, we must also be vigilant in identifying and addressing any potential negative consequences it can have on society and its citizens. This is the role of Responsible Technology. Data privacy We want to use all the good things that technology innovation brings, whether it be video, AI, ML, facial recognition, etc. We want to use all the good things that technology innovation brings, whether it be video, Artificial Intelligence, machine learning, facial recognition, etc. to serve people in societies in a responsible way. That means making sure that we regulate technology in a way that respects human rights and data privacy. Addressing the challenges The challenge is, that rather often technology leaders and policymakers either have conflicting interests or collaborate too late. To be responsible, business leaders must support their societies and policymakers in making regulations in the interest of the common good. At Milestone Systems, we are actively looking at how we develop our software responsibly, how our partners responsibly sell our software, and very importantly, how our customers use our software with a responsible mindset. Ensuring good corporate governance As a long-time partner within the security industry, we’re celebrating our 25th Anniversary this year, we are supporting the regulation of video technology for the good of society. However, it of course needs to strike the fine line between the right legislation and not hindering innovation. UNGP The UNGP is the most authoritative and widely adopted set of principles for responsible business At Milestone Systems, we want to play an active role in this and that is why we have pledged our support to the UN's Guiding Principles on Business and Human Rights (UNGP). The UNGP is the most authoritative and widely adopted set of principles for responsible business. The principles call on governments and companies to identify, prevent, mitigate, and remedy actual and potential human rights abuses. Since its launch in 2011, the UNGPs have received wide support from states, civil society organisations, and the private sector, making them the key global foundation for business and human rights. Protect, respect, and remedy Through this commitment, we are taking steps to ensure good corporate governance and ethical standards in the development of our technology. We're generating mechanisms to prevent misuse and we are building educational practices internally. Based on the UNGP’s three pillars: protect, respect, and remedy, we are developing a set of Responsible Technology Principles and procedures for the development, selling, and use of our products. Need for video technology regulation In addition, we are currently evaluating all the various technology areas in which our video software can be used, such as with third-party integrations that utilise e.g., facial recognition. We are mapping out the advantages and disadvantages for societies. One key area of concern is how local authorities are mapping and storing data about us as individuals. This is the reason why we're inviting more legislation to regulate video technology rather than less. Engaging With policymakers We are meeting ministers and trade organisations as we believe this needs to be a joint effort where all parties are heard We are proactively reaching out to and connecting with policymakers and other relevant stakeholders to discuss our approach to and take on Responsible Technology and encouraging the political landscape to work with us around regulation and legislation. We are meeting ministers and trade organisations as we believe this needs to be a joint effort where all parties are heard and where we can openly weigh the advantages and the challenges of technology, whether it is video, facial recognition, machine learning, Artificial Intelligence, or other technologies. Striking a balance Implementing Responsible Technology is a journey, not a destination. To give it the focus needed, we have created a dedicated team to implement this initiative at Milestone Systems. At the same time, we are reaching out to the political landscape to discuss how we balance regulation without hindering innovation. Video technology used ethically We are a global company with worldwide operations, and we are having dialogues about how video technology is being used and how we can have meaningful talks about what regulation and legislation should look like. However, we don’t necessarily want to limit access to the technology itself. Facial recognition We encourage the policymakers to engage with us in the industry so that together we can strike the fine line Facial recognition is a great example of this. The EU is considering making live facial recognition illegal. That would be a huge inhibitor of proactive terrorism prevention. For example, if a well-known terrorist is walking down the street and is being mapped out against Interpol’s most wanted list, the authorities should be able to react. However, if a person walking down the street but is not mapped out or does not have any priors then the city should not be allowed to store the data of that individual’s whereabouts at that point in time. This potential legislation is concerning to me as a citizen of Europe. Instead, we encourage the policymakers to engage with us in the industry so that together we can strike the fine line for the better good of all of us. Maintaining high ethical standards We have a firm understanding and expectation that ethical standards are a huge driver in the security business. Citizens are not in favour of technology companies abusing data about them and monetising from things that they have not opted in to do. Soon, I think we will see many more companies and governments leaning toward suppliers that do have a responsible mindset and high ethical standards for partnerships. Ethical practices Our journey toward Responsible Technology is an ongoing process, and we must remain steadfast in our commitment to ethical practices and the protection of human rights. We recognise that the rapidly changing technological landscape continually presents new challenges and opportunities. For this reason, we continuously look into how we can improve, for example, our end user licence agreements to avoid potential human rights abuses. An industry responsibility Security companies must prioritise careful planning and preparation, including developing policies and procedures For Responsible Technology to truly become a reality, compliance with international human rights laws and data privacy regulations is critical. Security companies must prioritise careful planning and preparation, including developing policies and procedures that govern the ethical use of video surveillance systems. The secure and ethical community In today's technology environment where deep integrations, machine learning, and artificial intelligence are becoming the norm, Responsible Technology is more relevant than ever. The security industry has a unique opportunity to set an example for other sectors by promoting a secure and ethical development community that prioritises Responsible Technology, trustworthy data collection, and the protection of human rights. We must all rise to this challenge and embrace our role as ethical leaders for the greater good of both people and societies.
Inadequate security measures on your essential infrastructure can have severe consequences. Consequences Consider the rail industry: If a vandal cuts the cables on a vital mechanism that controls train signals, train safety is jeopardised. To avoid train collisions or derailments and thus significant damage to property and potential loss of life, the operating company must shut down the service until the infrastructure is repaired and the network is up and running again. The disruption affects the rail ecosystem itself, but also the people using the trains, the transportation of cargo, and more. The financial cost of repairing the damage, restoring signal functionality, and compensating for delays can be substantial. For another example, consider electrical substations: A fire or targeted attack can damage the system and lead to devastating power outages. Traditional surveillance limitations Traditional video surveillance has its limits when it comes to protecting transformer stations Traditional video surveillance has its limits when it comes to protecting transformer stations. The facilities are often located in rural areas, where straying animals or flying leaves trigger false alarms. 3D Surveillance solutions overcome these challenges by volumetrically securing the area and immediately detecting intruders only raising the alarm in the event of a human intruder and even identifying drone attacks. Protecting critical infrastructure with 3D surveillance Critical infrastructure must be monitored. It remains at risk if operators do not have systems for monitoring entire areas rather than just the periphery if security personnel has limited information in case of an intrusion and if security response protocols are not automated. 3D Surveillance solutions 3D Surveillance is an important tool for protecting critical infrastructure and ensuring the safety of those who rely on it. Integrating LiDAR technology, 3D Surveillance solutions provide a comprehensive view of the area being monitored with real-time monitoring and response, protecting critical infrastructure from damage and providing a more comprehensive security system. Advanced analytics and artificial intelligence Security personnel can identify and verify threats more easily and track the movements of individuals or vehicles, as well as respond to incidents as they happen. 3D Surveillance systems can be equipped with advanced analytics and artificial intelligence (AI) capabilities to detect patterns and anomalies that may indicate a potential threat. This can help to prevent potential attacks or accidents before they occur, as well as enable more accurate responses to incidents. Talent challenge Turning to autonomy by implementing sensor- and software-based solutions requires fewer if any, in-person patrols 3D Surveillance can also help tackle the talent challenge in the industry: Recruiting security professionals involves extensive background checks, and jobs in the industry are notorious for their low salaries, which results in high staff turnover. Turning to autonomy by implementing sensor- and software-based solutions requires fewer if any, in-person patrols and ensure reliable infrastructure protection. Additional security measures In many countries, more stringent legislation now mandates the implementation of additional security measures to safeguard critical infrastructure, particularly at a country's points of entry, such as airports and harbours. Protecting the perimeter is no longer enough. For instance, airport management must ensure that critical areas, including the space around aircraft and near unauthorised access points, are secure. While multi-layered screening of individuals at the perimeter is a valuable security measure, it must be complemented by smooth and efficient surveillance of the entire area, which can only be achieved through advanced technology. Different adoption rates 3D Surveillance technology is only beginning to gain traction in most locations, and adoption rates differ significantly from one region to another. For instance, Scandinavia and Eastern Europe have embraced 3D Surveillance to a greater extent than Western Europe. Regions with lower adoption rates will likely catch up as they seek to reinforce the security of their critical infrastructure, especially given the conflict in Eastern Europe. Vandalism and damage protection 3D Surveillance enhances the security of critical infrastructure, reduces the risk of downtime and loss of revenue 3D Surveillance offers reliable protection against vandalism and damage - major concerns for companies that rely on critical infrastructure. LiDAR-based, software-enhanced 3D Surveillance solutions provide real-time insights and enable automatic processing of the information so that operators can autonomously and quickly detect and respond to potential threats. These solutions are scalable and customisable, allowing companies to adapt their security measures to their unique needs and changing environments. 3D Surveillance enhances the security of critical infrastructure, reduces the risk of downtime and loss of revenue, and ensures compliance with regulatory requirements. Asset management and maintenance planning Beyond its security benefits, 3D Surveillance can help with tasks such as asset management and maintenance planning. It can help identify potential problems or maintenance needs before they become more serious issues by providing a real-time view of the monitored infrastructure. This can help to reduce downtime and keep critical infrastructure running smoothly. Real-time management The same technology can also perform volume monitoring tasks and thus facilitate the management of valuable resources such as bulk material, grain, wood chips, or chemicals. By scanning the stock 24/7 and automatically calculating stock volume updating records in real-time, this technology supports lean production systems and automated processing.
Security beat
Companies at GSX 2023 emphasised new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasises ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the mid-market to the cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for the pure cloud, but there are benefits to be realised from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realise the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘soft’ features for integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organisation more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organisation more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centres around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasising performance, protection (cybersecurity), and price, their data centres are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring centre where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
New buzzwords were abundant in the articles that generated the most clicks on our website in 2022. From the metaverse to the Internet of Things, from frictionless access control to artificial intelligence (AI), the topics most popular among our site’s visitors were at the cutting edge of change and innovation in the physical security marketplace. Here is a review of the Top 10 Articles of 2022, based on reader clicks, including links to the original content: Metaverse will promote collaboration and enable more efficiencies for security Metaverse is a familiar buzzword currently, but few people grasp what it means. In the simplest terms, the metaverse is an online “place” where physical, virtual, and augmented realities are shared. The term, Metaverse, suggests a more immersive online environment that combines elements of augmented reality (AR) and virtual reality (VR). For the physical security industry, the looming creation of a complex online environment offers possibilities and challenges. Establishing identity will be a central principle of the metaverse, and various biometrics are at the core of ensuring the identity of someone interacting in the virtual world. Cybersecurity elements are also key. On the benefits side, the security market is already taking advantage of technologies related to the eventual evolution of the metaverse. For example, the industry has deployed AR to provide information about a door lock’s status on a screen, headset, or smart glasses as a patrolling guard walks by. What are the security challenges of the transportation industry? Because transit agencies rely on several IoT devices, they get exposed to higher cybersecurity risks Rapid technological advancement, increasing urbanisation, and the growing expectations of commuters and governments are pressuring transit industry players to modernise. Commuters, urban planners, first responders, and other stakeholders want to use transit data to support their decision-making. Transit agencies’ security and operations teams need closer collaboration to stay ahead. However, for many years, most transit agencies have relied on siloed, proprietary systems. Because transit agencies rely on an ever-growing number of Internet of Things (IoT) devices, they also get exposed to higher cybersecurity risks as there are more network access points to manage. The future is here: ADT’s innovation lab evaluating robots and indoor drones New robots and indoor drones for security applications are on the horizon, based on the work of ADT Commercials’ Innovation Lab, which is evaluating the latest technologies’ value to customers and some typical use cases. The ideal use of humanoid robots is to perform jobs that are considered repetitive, dirty, dangerous, and/or mundane. In security, that describes most security guard positions. As the name implies, autonomous indoor drones are focused on flying indoors versus the outdoor environment, which is heavily regulated by the U.S. Federal Aviation Administration (FAA). Flying autonomously indoors not only eliminates FAA oversight but also will enable ADT Commercial to offer another choice to customers to further reduce their dependencies on and costs of human guards. Innovative security: the key to business efficiency, cost savings, and more Organisations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend. More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organisations looking to drive higher productivity and profitability margins should consider security upgrades that prioritise integrated analytics and automation. Shoplifting today is more sophisticated, and so are the tools to fight it One tool to fight shoplifting is analytics, which can be used to determine where shrink is occurring Shoplifting is often viewed as petty theft by individuals, but that is not always the case. Overall, shoplifting is becoming more sophisticated and coordinated. Traditional “shoplifting” has two major differences when compared to organised retail crime (ORC). The differences are numbers and motivation. ORC consists of groups working together to monetise theft, very different than an individual taking an item they need. One tool to fight to shoplift is analytics, which can be used to determine where shrink is occurring. Understanding where crimes take place helps retailers make strategic decisions about where to place their loss prevention efforts. Oosto offers 10 reasons to switch to frictionless access control in commercial buildings Access control for buildings is nothing new. It’s only in recent years that the urgency to implement smarter, more efficient, and more convenient forms of access control has increased, in the context of public and private sector digital transformation. Upheavals from the COVID-19 pandemic have forced organisations to re-think, pivot, and invest in new technology solutions that will incorporate Artificial Intelligence (AI) and Machine Learning, to gain speed in their operations, glean actionable insights from their video analytics, and enhance productivity with their teams. Which security trend is here to stay? Technologies and trends in the security marketplace come and go with some regularity. But how can you tell which trends are gaining traction and which amount to “the flavor of the month.” For example, while many physical security departments were hesitant to consider cloud-connected solutions in the past, they now better understand the benefits these solutions bring and how they can help them utilize their resources to achieve business goals while minimising overall operational complexity. Other technologies mentioned in the article include mobile credentials, AI-based analytics, video management systems, cybersecurity, and a new emphasis on data. What do these technology trends have in common? They are opening new possibilities for greater system efficiency and functionality. In short, they are playing a role in transforming our industry. GSX 2022 reflects changing technologies and evolving role of security The role of the security director increasingly will encompass facets of cybersecurity and physical security GSX 2022 in Atlanta highlighted the changing role of security in the enterprise. The role of the security director increasingly will encompass facets of cybersecurity as well as physical security. Transitioning to an operation that incorporates both disciplines requires a workforce that embraces education and building new skills. Education and the opportunity to build new skills are evident everywhere at GSX, including in the hundreds of education sessions and also in the knowledge shared on the show floor in the exhibit hall. Consolidation changing the face of the security market Consolidation is a dominant trend in the security marketplace. Large companies typically swallow up smaller companies as a means of expanding both their technology portfolios and their geographic reach. Sometimes a big fish is swallowed up by an even bigger fish. Despite the pandemic and resulting economic challenges, the security market has continued to be a desirable environment for both big players and startups, which then provide abundant acquisition targets for larger companies. This article highlighted recent mergers and acquisition news. Six trends at the intersection of video and AI Video has evolved beyond the capabilities of advanced imaging and performance to include another level: Artificial Intelligence. Video imaging technology combines with AI, delivers a wealth of new data, not just for traditional physical security applications, but for a much deeper analysis of past, present, and even future events across the enterprise. This is more than a big development for the physical security industry; it is a monumental paradigm shift that is changing how security system models are envisioned, designed, and deployed. Much of the heightened demand for advanced video analytics is being driven by six prevalent industry trends.
For an enterprise, addressing cyber security requires that stakeholders have immediate access to critical information compiled from multiple sources and presented where and how they need it. Various data sources monitor the cyber security status of a company’s computer systems to provide real-time visibility. Aggregating that data into visual dashboards and presenting it to operators enables any cyber security problems to be flagged quickly and resolved. Software system enhances cyber security Userful Corporation provides a software system that enhances cyber security operations for an enterprise Userful Corporation provides a software system that enhances cyber security operations for an enterprise, enabling stakeholders to envision various cyber security factors, such as application security, network security, cloud security and IoT (Internet of Things) security. The software system empowers operators to respond more efficiently. Working in conjunction with a company’s existing IT infrastructure, Userful software combines datasets from diverse systems into a visual format and delivers the information to a desktop computer, a video wall, or even to a home office. Real-time visibility “It provides a new dynamic to how cyber security issues are resolved,” said Shane Vega, Userful Corporation’s Vice President (VP) of Product Marketing, adding “The individuals who have flagged a cyber security issue may not be the ones to respond. Having real-time visibility provides more value to the overall response.” A typical cyber security operations centre resembles a physical security command or emergency management hub – large video walls, individual desktop workstations, and operators that need to share information and respond quickly to any incident. Userful’s software helps in managing operations centres Userful’s software manages how data is presented in an operations centre environment, without relying on proprietary hardware, operating outside an end-user customer’s IT infrastructure. Managing operations centres is a core offering for Userful Corporation, including command centres of all types, from traditional network operation centres to emergency network systems to security systems. The ability to use one software system throughout an enterprise is appealing to companies that have historically grappled with proprietary and siloed systems. Solutions that are easy to deploy, manage and scale Cyber security professionals need solutions that are easy to deploy, manage and scale" “We are a platform that can be utilised across the enterprise,” said Shane Vega, adding “Cyber security professionals need solutions that are easy to deploy, manage and scale, so they can manage all the threats every day.” Compiling and displaying information to an operations centre has historically involved silos of proprietary audio/video (AV) hardware. Ironically, the hardware approach presents cyber security risks that undermine the very mission of protecting a company’s data and networks. The proprietary systems operate outside the company’s network infrastructure, and IT professionals do not have visibility into the systems. Security Orchestration, Automation and Response (SOAR) Instead of hardware, displaying information on Security Orchestration, Automation and Response (SOAR) can be accomplished using software running on off-the-shelf components, managed by the IT department and featuring all the cyber security protections required, throughout the enterprise’s network infrastructure. SOAR includes threat and vulnerability management, security incident response and security operations automation, enabling companies to collect threat-related data from several sources and automate the responses. Cyber security threats Possible threats might include an influx of packet generation, malware, someone seeking access to the network, or a malicious email. Various tools manage each threat, and each must be visualised. Because the threats are related, a comprehensive dashboard enables operators to create parallels and respond more efficiently. The software-as-a-service system ensures that all software is updated and can operate on the latest hardware In the Userful AV-over-IP scenario, an IT department takes full ownership of the computers and subsystems installed on the network. The software-as-a-service system ensures that all software is updated and can operate on the latest hardware. Companies always have an ecosystem of interconnectivity. Single platform/solution The single platform/solution also extends beyond operations centres to include meeting rooms and digital signage. All images are captured using existing protocols, such as Real Time Streaming Protocol (RTSP), HTTP Live Streaming (HLS), Web Real-Time Communication (WebRTC), and so forth. In contrast, the AV industry is hardware-centric and has been known to circumvent software approaches in order to justify selling more hardware. AV systems typically operate in terms of pixels rather than bytes of information and use proprietary software. Companies always have an ecosystem of interconnectivity Different departments in a company have historically installed their own specific AV systems, based on proprietary hardware, so that each department is siloed from the rest of the organisation. Dangers of random hardware on a network Random hardware on a network, beyond the reach of the IT department, can provide access points to the network for hackers and other cyber security threats. Each proprietary hardware system exists outside the existing security protocols of the enterprise and each represents a cyber security vulnerability. Some companies end up with five or six different operations centres that involve three or four manufacturers, all siloed. Software versus hardware Our biggest challenge is to get people to understand what is possible with software versus hardware" “Our biggest challenge is to get people to understand what is possible with software versus hardware,” said Shane Vega, adding “The industry is inundated with hardware, and the risk is the unknown. Customers may not be familiar with a software solution that can accomplish what they have historically depended on hardware for.” Userful Corporation works through channel partners (integrators), who assemble complete systems using Userful software and other components, such as video screens, large-format commercial displays, groups of tiled displays, projectors – any type of display with an input. Corporate policy specifies security at every level Userful’s corporate policy specifies security at every level, including user authentication, encryption, endpoint security, air-gapped servers, information security policies, General Data Protection Regulation (GDPR), and a solution built on industry-leading IT standards. To spread the word about Userful Corporation’s capabilities related to cyber security, the company will be participating in Infosecurity Europe 2022, taking place from June 21 to June 23, 2022 at ExCeL, London, United Kingdom (UK).
Case studies
The City of Edinburgh is the capital of Scotland and the second most populous city in the country. It is the seat of the Scottish Government and the official residence of the British monarch in Scotland. As well as serving a vital role in government, the city is economically significant for the region, attracting global tourism as well as being home to a world-renowned university. Protecting citizens and visitors as they move through the city and keeping Edinburgh’s roads running smoothly is of the utmost importance. Transforming into a smart city City of Edinburgh Council leadership modernises security and surveillance across the capital The City of Edinburgh Council leadership needed to modernise security and surveillance across the capital. This involved upgrading the control centre to a new smart city operations centre to receive real-time data from Edinburgh’s surveillance network. The centre also integrates with traffic and transport platforms to enhance operational management and improve city planning. Hanwha Vision IP cameras The new control centre gives operators access to real-time data and analytics, for insights that improve response times and situational awareness. Smart technology solutions provider, North, designed a security solution built with more than 100 high-resolution Hanwha Vision IP cameras including the PNM-9322VQP multi-directional PTZ camera and XNO-8080R 5MP IR bullet camera. The solution also incorporates a video management system from Genetec. Comprehensive coverage and intelligence Multi-directional cameras are ideal for monitoring large and complex areas such as city centres Multi-directional cameras are ideal for monitoring large and complex areas such as city centres. The multi-directional PNM-9322VQP features five camera sensors in a single device, minimising the amount of cabling and server infrastructure required compared to installing five separate devices, to improve cost-efficiency while streamlining installation. The XNO-8080R is a 5MP IR bullet camera with accurate video analytics. These analytics - carried out on the device to reduce server needs - include loitering, directional detection, audio detection and sound classification. It features Hallway View to cover narrow areas such as alleyways. Additionally, using the proprietary compression technology WiseStream II improves bandwidth by up to 75% while retaining video quality. Best-in-class cybersecurity Cybersecurity is crucial in a smart city, given the number of connected devices that could be exploited. Hanwha Vision has been hardening its cybersecurity measures for many years with the National Defense Authorization Act compliance (NDAA), UL CAP Certification, and a dedicated security vulnerability response team (S-CERT). Furthermore, North is part of Genetec’s “network of trust” initiative, signalling the close partnership between the two solution providers and their shared focus on securing network and critical surveillance infrastructure. Low-carbon technology Hanwha Vision has been hardening its cybersecurity measures for many years with the NDAA “The new operations centre has been years in the making and it’s fantastic to see it live in action,” said Councillor Jane Meagher, Council Leader, The City of Edinburgh Council. “With cutting-edge low-carbon technology designed to keep the city moving and our communities safe, it drastically steps up our capabilities as a council. Edinburgh is fast becoming an example of a truly smart city and it’s thanks to trailblazing projects like this.” New video surveillance system Andrew Foster, MD – Public Services at North, added: “Helping to drive positive change through smart technology and improved operational systems across Edinburgh is something that North is incredibly proud of. Working together, the city now has access to real-time data that will influence the future of city planning, improve large-scale events and create a greener environment for generations to come.” The new video surveillance system provides Edinburgh with a future-proofed smart city solution with the option to expand and add connected devices such as air quality sensors, smart parking applications and flood sensors.
KA Beveren is a sports school located in Belgium, known for providing sports education and nurturing many student-athletes. Recently KA Beveren underwent a significant upgrade to its security infrastructure, aiming to improve the safety of students, staff, and facilities. VIVOTEK, the pioneering security solution provider, played a pivotal role in the project. In collaboration with distributor Optima Networks and integrator Educorner bvba, VIVOTEK’s advanced AI solutions, helped KA Beveren achieve a state-of-the-art security system, offering superior monitoring and AI-driven analytics. Challenge KA Beveren faced the challenge of achieving total range across indoor and outdoor spaces KA Beveren faced the challenge of achieving comprehensive coverage across both indoor and outdoor spaces, eliminating blind spots and ensuring continuous security. The security solution was designed to deter vandalism and unauthorised access, creating a safer environment for both students and staff. Additionally, it plays a crucial role in monitoring and reducing incidents of bullying and physical altercations, aiding in the identification of individuals involved in such events. The solution was required to detect security threats in real time, providing actionable insights to administrators and security personnel. Due to the school's large size and dynamic environment, the solution had to offer both wide-ranging and detailed security coverage. Provide comprehensive coverage with minimal blind spots. Enable efficient monitoring and management using AI-driven technology. Be scalable to accommodate future growth and evolving security needs. Reduce the total cost of ownership by minimising the number of cameras required and simplifying maintenance. Provide comprehensive coverage with minimal blind spots. Solutions VIVOTEK partnered with Educorner bvba to implement a customised solution centred around advanced camera which included Fixed Dome, Fisheye, Multi-Sensor Panoramic cameras, and integration with Network Optix VMS. Placed Fixed Dome cameras in key locations such as entry points, hallways, and high-traffic areas, these cameras ensure robust monitoring of critical areas. Their design is built to withstand the harsh environmental conditions typical of sports facilities. With VIVOTEK’s AI analytics, these cameras can distinguish between humans and vehicles, effectively reducing false alarms and improving reliability. Fisheye Cameras were strategically mounted at the corners of buildings, maximising coverage while minimising the number of cameras required. Their wide-angle design allows the school to reduce installation complexity and cost. These fisheye cameras, in combination with Network Optix’s dewarping technology, provide multiple views from a single device, offering comprehensive coverage of large areas. This innovative setup replaces the need for multiple Fixed Dome cameras or even PTZ cameras, enhancing efficiency while maintaining high-quality coverage. Multi-Sensor Panoramic Cameras offers a 180-degree view, and ideal for monitoring expansive outdoor areas such as sports fields and parking lots. With their multi-sensor design, the cameras deliver a seamless panoramic image, ensuring every corner is covered. Built-in AI analytics enable real-time detection of unusual activities, further enhancing the system’s effectiveness. To maximise the utility of VIVOTEK’s surveillance system, the project incorporated the Network Optix video management system (VMS). The VMS’s intuitive interface, paired with the Deep Search Plugin, enhances the security team’s ability to quickly locate specific individuals or incidents across the network. The AI-driven search tool filters video based on attributes such as gender, age group (adult/kid), or even body parts, allowing for more efficient and accurate investigations. Benefits VIVOTEK’s AI solution has significantly enhanced the security of KA Beveren Sports School, offering several key benefits: Enhanced Safety: The advanced AI analytics integrated into VIVOTEK cameras provide real-time threat detection, allowing security personnel to swiftly address potential security incidents. Comprehensive Coverage: With a strategic mix of Fixed Dome, Fisheye and Multi-Sensor Panoramic cameras, the school enjoys full coverage, ensuring that no area is left unmonitored. Efficient Monitoring: The Network Optix VMS, enriched with the Deep Search Plugin, simplifies the monitoring process, enabling the security team to respond rapidly with accurate and specific information. Future-Proofing: The scalability of the system ensures that KA Beveren’s security infrastructure can evolve with future needs and challenges, providing a long-term solution that grows with the institution. Results and customer feedback "As TAC at KA Beveren Sports School, my focus is on ensuring a secure and supportive learning environment for both students and staff. With VIVOTEK’s surveillance system now in place, we’ve significantly raised the level of safety on campus. The system is reliable and easy for our team to manage, which lets us focus on what we do best: providing quality education. Working with Educorner bvba on this project was smooth from start to finish, and we now have full confidence that our school is well-protected," Pascal Verleyen, Technisch Adviseur-Coördinator, KA Beveren Sports School. VIVOTEK continuously offers the most trusted cutting-edge security solutions to its customers and deeply develops various vertical markets in the future, including the educational sector that fosters knowledge.
Tenerife Norte-Ciudad de La Laguna Airport has significantly improved its safety by installing state-of-the-art video technology from German manufacturer Dallmeier. The Panomera® multifocal sensor cameras are used for comprehensive monitoring of the movement area. A major hub for domestic flights Tenerife Norte-Ciudad de La Laguna Airport (TFN) is located about 10 kilometres west of the capital, Santa Cruz de Tenerife, in the municipality of San Cristóbal de La Laguna. It mainly handles domestic flights: connecting flights to the other Canary Islands, such as Gran Canaria or Lanzarote, as well as scheduled flights to the Spanish mainland. The main destination is Madrid-Barajas, with over one million passengers, followed by Barcelona, Seville, and Bilbao. Tender for detection, supervision, and recording The tender documents specified the installation of a monitoring and control system to detect To further increase safety at Tenerife Norte-Ciudad de La Laguna Airport and to improve airport operations, the entire movement area was to be covered. The tender documents specified the installation of a monitoring and control system to detect, supervise, and record operations in that area in high resolution. Installation sites as critical points The total area to be monitored is huge, with the runway (with the focus at both ends), apron, taxiways, and service roads adjacent to the apron. The main challenge was that it was not possible to place camera masts randomly on the movement area, so existing buildings had to be used as installation points. Simplified maintenance “We wanted to minimise the number of installation points and camera systems to avoid the need for additional infrastructure such as masts, cabling, communication interfaces, etc., and to simplify subsequent maintenance processes,” says Carlos Jesús Delgado Gómez, Head of the Director’s Office at TFN. “And, of course, airports have strict regulations for any type of installation, especially in the movement area. That’s why there were very limited options when it came to selecting installation points. Nevertheless, the desired area had to be monitored at the highest resolution and the recording always had to be at maximum resolution.” High-resolution coverage High-resolution coverage of large areas under these conditions could not be satisfactorily achieved High-resolution coverage of large areas under these conditions – a minimum number of installation points and camera systems – could not be satisfactorily achieved with conventional single-sensor cameras. Tenerife Norte-Ciudad de La Laguna Airport therefore decided to use Dallmeier’s patented Panomera® multifocal sensor technology. Maximum resolution at long distances By combining multiple lenses and sensors with different focal lengths in a single optical unit, multifocal sensor technology offers high resolution across the entire object space. This means that even distant objects can be captured clearly, and significantly fewer systems are required overall than with conventional single-sensor cameras. “We were able to install the Panomera® on existing building facades and roofs without any problems”, says Carlos Jesús Delgado Gómez. “No other camera system was able to cover such a large area with so few cameras and installation points at such a high resolution.” Increasing operational safety and optimising processes The installed video technology not only increases operational safety but also allows processes to be optimised and disputes to be resolved quickly and clearly. One of the areas monitored is the aprons, where aircraft park and are prepared for the next flight. Since every minute spent parking is money for the airport company, there are always disputes about who is responsible for delays and the resulting additional parking fees. Was the fuel truck there on time? Did the catering arrive on time? Damage management can now be carried out quickly and objectively thanks to clear video recordings. For example, did the damage occur while the aircraft was parked or docked, or was it already there? The advantage of multi-user capability Any number of operators can access the image at the same time, each zooming in on the area of interest In addition to its ability to cover large areas, multifocal sensor technology is characterised by its multi-user capability. Panomera® works like a virtual combination of any number of PTZ cameras with the key advantage that the operator moves virtually in the image, rather than moving the camera mechanically as with PTZ cameras. As a result, any number of operators can access the image at the same time, each zooming in on the area of interest. Unlike conventional PTZ cameras, the entire image is always recorded. Bandwidth savings thanks to multicast capability As several users always need to access the live stream at the same time, the so-called multicast capability was also a decisive advantage of the Panomera®. Multicast capability allows data from a single source to be sent to multiple recipients simultaneously. This means that the video stream can be efficiently distributed to multiple devices or users without having to send the data multiple times. Multicast reduces network load and makes more efficient use of bandwidth. 3D simulation of the project, “CamCards” The entire project was precisely planned by Dallmeier with the help of a 3D simulation and pre-configured and tested in the company‘s own FAT Centre according to the customer‘s specifications. So-called CamCards, created by the Dallmeier 3D team, made the installation easier for the installer on site, as they show exactly where and at what angle the individual Panomera® cameras are to be mounted. Mountera® mounting system The Mountera® mounting system also proved its worth in practice, as Miguel Ángel Rodríguez Domínguez The Mountera® mounting system also proved its worth in practice, as Miguel Ángel Rodríguez Domínguez, project manager at installer Cobra Instalaciones y Servicios, Delegación Canarias, confirms, “The biggest challenge for us as installers was the high humidity and salt content due to the island location." "We therefore had to have bespoke, rust-proof, and robust masts and brackets made for the cameras. The actual installation of the Panomera® cameras with the Mountera® wall bracket and mast adapter was very easy.” Satisfied with the solution The video system has lived up to expectations and Tenerife North Airport is happy with its choice. Both the installer and the end customer are also satisfied with the support provided during the project. “We are very grateful for the support and solution-oriented assistance from Dallmeier Spain throughout the entire process, but especially during the implementation,” says Carlos Jesús Delgado Gómez. With the Dallmeier solution, consisting of a camera, recorder, and video management system, Tenerife Norte-Ciudad de La Laguna Airport is also well equipped for the future: The system is modular and can therefore be easily expanded or adapted to new challenges at any time.
The space-saving yet full-function video spectral comparator Regula 4306 has been deployed at Wattay International Airport in Vientiane, the Lao People’s Democratic Republic, to strengthen the country’s border security. This initiative aims to combat transnational crimes, including human trafficking, smuggling, and irregular migration. Forged identity documents Lao People’s Democratic Republic faces growing challenges in identifying forged identity documents Like many countries, the Lao People’s Democratic Republic faces growing challenges in identifying forged identity documents used by criminals and irregular migrants. Until recently, document verification at border checkpoints relied heavily on manual inspection, which was time-consuming, prone to errors, and less effective against increasingly sophisticated forgery techniques. Adopting a forensic solution In collaboration with International Organisation for Migration (IOM), the Lao immigration authorities began modernising their approach by adopting a forensic solution to strengthen document authentication and border security. In partnership with IOM in the Lao People’s Democratic Republic and the Australian Department of Home Affairs, the Lao immigration authorities deployed the Regula 4306 video spectral comparator at the country’s major airport in Vientiane. This step equipped border officials with advanced forensic tools for in-depth document authentication, and significantly automated the whole process. Array of features in the Regula 4306 With an array of features in the Regula 4306, ID proof at the Lao border earned much precision With a vast array of features in the Regula 4306, ID verification at the Lao border achieved much-needed high precision. For instance, the device’s high-resolution 8 MP camera with 60x optical zoom captures document images at up to 18,900 ppi and enables officials to analyse even the finest details, including printing techniques. Hyperspectral imaging module Additionally, with over 40 types of light sources and 18 light filters, the Regula 4306 allows authorities at the second line of border control to examine the most intricate document security features, such as holograms, watermarks, microprinting, and optically variable elements, ensuring a more reliable fraud detection process. Apart from that, 3D visualisation helps analyse a document’s surface relief and intersecting lines, and the hyperspectral imaging module enables forensic experts to detect document alterations, differentiate ink properties, or recover faded text. Regula Forensic Studio cross-platform software Regula 4306 is controlled via Regula Forensic Studio (RFS) cross-platform software Regula 4306 is controlled via Regula Forensic Studio (RFS) cross-platform software. With RFS, an expert can perform a wide range of examinations, conduct precise measurements and comparisons, process images in various modes, and generate comprehensive examination reports without losing a single detail. Its powerful tools and intuitive interface ensure accuracy and reliability, enabling thorough and efficient forensic investigations. Regula’s identity document template database Integrated with Regula Document Reader SDK, RFS enables comprehensive, automated document checks, eliminating the need for additional equipment or software. Regula Document Reader SDK can instantly recognise and validate IDs’ machine-readable zones (MRZs), RFID chips, barcodes, and invisible personal information (IPI), significantly reducing manual workload and minimising human error. Also, as it is backed up by Regula’s identity document template database (the most comprehensive in the world), this software is able to verify a wide range of IDs from 251 countries and territories, even the rarest ones. Adoption of Regula 4306 Regula experts conducted specialised training sessions for the Lao immigration officials To ensure seamless adoption of Regula 4306 at Wattay International Airport, Regula experts conducted specialised training sessions for the Lao immigration officials. This ensured that they had hands-on experience and were fully equipped to handle advanced document verification. “Integrating Regula’s devices into the Lao border management operations is a vital step toward combating serious crimes such as human trafficking and irregular migration. This technology enables detection of fraudulent documents with higher accuracy, eliminating human errors,” says Shareen Tuladhar, Chief of Mission, IOM in the Lao People’s Democratic Republic. Lao immigration authorities “Border crossings are the frontline of many serious crimes, making border security crucial to the country's overall safety. We are honoured to contribute to strengthening Lao border security." "By equipping the Lao immigration authorities with our top-selling video spectral comparator, the Regula 4306, we are providing them with advanced forensic tools to precisely detect even the most sophisticated document forgeries and stop criminals before they can cause harm,” comments Alex Lewanowicz, Director of Hardware Engineering at Regula.
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the full U.S. Department of Homeland Security SAFETY Act Designation. Announced that its proactive gun detection and intelligent situational awareness solution has been deployed by Carbon Cliff-Barstow School District (CCBSD) in Rock Island County, Illinois. Strengthening security with AI The ZeroEyes Gun Violence Research Centre has already analysed 34 gun-related eventsThe AI technology will be implemented at the district’s Pre-K through 8th grade school to enhance security and reduce response times in the event of a gun-related threat. The ZeroEyes Gun Violence Research Centre has already analysed 34 gun-related events at Illinois K-12 school districts this year alone. Recognising the ongoing threat of gun-related violence, the district is taking an important step by integrating ZeroEyes’ AI gun detection system to further bolster its security measures and protect against potential threats. Commitment to campus safety CCBSD maintains a comprehensive, multi-layered security programme in partnership with the Rock Island County Sheriff's Department to ensure the safety of students and staff. Alongside the district’s school resource officer, CCBSD has invested in a third-party monitored alarm system and recently upgraded its camera infrastructure. An on-site behavioural interventionist is also employed to build strong relationships with students and families. Strengthening security “We take great pride in ensuring the safety and success of all students and staff members at our school,” said Eric Lawson, Superintendent of CCBSD. “By incorporating ZeroEyes, we’re adding another important layer of safety to our campus, and we’re confident that this proactive approach will help us promote a safe learning environment.” Smart solutions with ZeroEyes CCBSD serves 240 students from diverse backgrounds in an urban area of northwest Illinois CCBSD serves 240 students from diverse backgrounds in an urban area of northwest Illinois, part of the Quad Cities region. The district’s mission is to prepare students to be academically successful and career-ready, foster a love for learning, and help students reach their full potential as confident, lifelong learners. The district’s 40 staff members are dedicated to ensuring the safety and educational success of every student. ZeroEyes' AI gun detection and intelligent situational awareness software layers onto CCBSD’s existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC. Protecting with precision The industry's only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to first responders and local staff as quickly as 3 to 5 seconds from detection. Innovating school security “The safety of students and staff is a priority for Carbon Cliff-Barstow, and we are honored to play a role in supporting that mission," said Mike Lahiff, CEO and co-founder of ZeroEyes. “Our AI gun detection system will provide the district with the actionable intelligence needed to mitigate potential threats, helping to ensure a safer environment for students and staff."
The City of Edinburgh is the capital of Scotland and the second most populous city in the country. It is the seat of the Scottish Government and the official residence of the British monarch in Scotland. As well as serving a vital role in government, the city is economically significant for the region, attracting global tourism as well as being home to a world-renowned university. Protecting citizens and visitors as they move through the city and keeping Edinburgh’s roads running smoothly is of the utmost importance. Transforming into a smart city City of Edinburgh Council leadership modernises security and surveillance across the capital The City of Edinburgh Council leadership needed to modernise security and surveillance across the capital. This involved upgrading the control centre to a new smart city operations centre to receive real-time data from Edinburgh’s surveillance network. The centre also integrates with traffic and transport platforms to enhance operational management and improve city planning. Hanwha Vision IP cameras The new control centre gives operators access to real-time data and analytics, for insights that improve response times and situational awareness. Smart technology solutions provider, North, designed a security solution built with more than 100 high-resolution Hanwha Vision IP cameras including the PNM-9322VQP multi-directional PTZ camera and XNO-8080R 5MP IR bullet camera. The solution also incorporates a video management system from Genetec. Comprehensive coverage and intelligence Multi-directional cameras are ideal for monitoring large and complex areas such as city centres Multi-directional cameras are ideal for monitoring large and complex areas such as city centres. The multi-directional PNM-9322VQP features five camera sensors in a single device, minimising the amount of cabling and server infrastructure required compared to installing five separate devices, to improve cost-efficiency while streamlining installation. The XNO-8080R is a 5MP IR bullet camera with accurate video analytics. These analytics - carried out on the device to reduce server needs - include loitering, directional detection, audio detection and sound classification. It features Hallway View to cover narrow areas such as alleyways. Additionally, using the proprietary compression technology WiseStream II improves bandwidth by up to 75% while retaining video quality. Best-in-class cybersecurity Cybersecurity is crucial in a smart city, given the number of connected devices that could be exploited. Hanwha Vision has been hardening its cybersecurity measures for many years with the National Defense Authorization Act compliance (NDAA), UL CAP Certification, and a dedicated security vulnerability response team (S-CERT). Furthermore, North is part of Genetec’s “network of trust” initiative, signalling the close partnership between the two solution providers and their shared focus on securing network and critical surveillance infrastructure. Low-carbon technology Hanwha Vision has been hardening its cybersecurity measures for many years with the NDAA “The new operations centre has been years in the making and it’s fantastic to see it live in action,” said Councillor Jane Meagher, Council Leader, The City of Edinburgh Council. “With cutting-edge low-carbon technology designed to keep the city moving and our communities safe, it drastically steps up our capabilities as a council. Edinburgh is fast becoming an example of a truly smart city and it’s thanks to trailblazing projects like this.” New video surveillance system Andrew Foster, MD – Public Services at North, added: “Helping to drive positive change through smart technology and improved operational systems across Edinburgh is something that North is incredibly proud of. Working together, the city now has access to real-time data that will influence the future of city planning, improve large-scale events and create a greener environment for generations to come.” The new video surveillance system provides Edinburgh with a future-proofed smart city solution with the option to expand and add connected devices such as air quality sensors, smart parking applications and flood sensors.
KA Beveren is a sports school located in Belgium, known for providing sports education and nurturing many student-athletes. Recently KA Beveren underwent a significant upgrade to its security infrastructure, aiming to improve the safety of students, staff, and facilities. VIVOTEK, the pioneering security solution provider, played a pivotal role in the project. In collaboration with distributor Optima Networks and integrator Educorner bvba, VIVOTEK’s advanced AI solutions, helped KA Beveren achieve a state-of-the-art security system, offering superior monitoring and AI-driven analytics. Challenge KA Beveren faced the challenge of achieving total range across indoor and outdoor spaces KA Beveren faced the challenge of achieving comprehensive coverage across both indoor and outdoor spaces, eliminating blind spots and ensuring continuous security. The security solution was designed to deter vandalism and unauthorised access, creating a safer environment for both students and staff. Additionally, it plays a crucial role in monitoring and reducing incidents of bullying and physical altercations, aiding in the identification of individuals involved in such events. The solution was required to detect security threats in real time, providing actionable insights to administrators and security personnel. Due to the school's large size and dynamic environment, the solution had to offer both wide-ranging and detailed security coverage. Provide comprehensive coverage with minimal blind spots. Enable efficient monitoring and management using AI-driven technology. Be scalable to accommodate future growth and evolving security needs. Reduce the total cost of ownership by minimising the number of cameras required and simplifying maintenance. Provide comprehensive coverage with minimal blind spots. Solutions VIVOTEK partnered with Educorner bvba to implement a customised solution centred around advanced camera which included Fixed Dome, Fisheye, Multi-Sensor Panoramic cameras, and integration with Network Optix VMS. Placed Fixed Dome cameras in key locations such as entry points, hallways, and high-traffic areas, these cameras ensure robust monitoring of critical areas. Their design is built to withstand the harsh environmental conditions typical of sports facilities. With VIVOTEK’s AI analytics, these cameras can distinguish between humans and vehicles, effectively reducing false alarms and improving reliability. Fisheye Cameras were strategically mounted at the corners of buildings, maximising coverage while minimising the number of cameras required. Their wide-angle design allows the school to reduce installation complexity and cost. These fisheye cameras, in combination with Network Optix’s dewarping technology, provide multiple views from a single device, offering comprehensive coverage of large areas. This innovative setup replaces the need for multiple Fixed Dome cameras or even PTZ cameras, enhancing efficiency while maintaining high-quality coverage. Multi-Sensor Panoramic Cameras offers a 180-degree view, and ideal for monitoring expansive outdoor areas such as sports fields and parking lots. With their multi-sensor design, the cameras deliver a seamless panoramic image, ensuring every corner is covered. Built-in AI analytics enable real-time detection of unusual activities, further enhancing the system’s effectiveness. To maximise the utility of VIVOTEK’s surveillance system, the project incorporated the Network Optix video management system (VMS). The VMS’s intuitive interface, paired with the Deep Search Plugin, enhances the security team’s ability to quickly locate specific individuals or incidents across the network. The AI-driven search tool filters video based on attributes such as gender, age group (adult/kid), or even body parts, allowing for more efficient and accurate investigations. Benefits VIVOTEK’s AI solution has significantly enhanced the security of KA Beveren Sports School, offering several key benefits: Enhanced Safety: The advanced AI analytics integrated into VIVOTEK cameras provide real-time threat detection, allowing security personnel to swiftly address potential security incidents. Comprehensive Coverage: With a strategic mix of Fixed Dome, Fisheye and Multi-Sensor Panoramic cameras, the school enjoys full coverage, ensuring that no area is left unmonitored. Efficient Monitoring: The Network Optix VMS, enriched with the Deep Search Plugin, simplifies the monitoring process, enabling the security team to respond rapidly with accurate and specific information. Future-Proofing: The scalability of the system ensures that KA Beveren’s security infrastructure can evolve with future needs and challenges, providing a long-term solution that grows with the institution. Results and customer feedback "As TAC at KA Beveren Sports School, my focus is on ensuring a secure and supportive learning environment for both students and staff. With VIVOTEK’s surveillance system now in place, we’ve significantly raised the level of safety on campus. The system is reliable and easy for our team to manage, which lets us focus on what we do best: providing quality education. Working with Educorner bvba on this project was smooth from start to finish, and we now have full confidence that our school is well-protected," Pascal Verleyen, Technisch Adviseur-Coördinator, KA Beveren Sports School. VIVOTEK continuously offers the most trusted cutting-edge security solutions to its customers and deeply develops various vertical markets in the future, including the educational sector that fosters knowledge.
Tenerife Norte-Ciudad de La Laguna Airport has significantly improved its safety by installing state-of-the-art video technology from German manufacturer Dallmeier. The Panomera® multifocal sensor cameras are used for comprehensive monitoring of the movement area. A major hub for domestic flights Tenerife Norte-Ciudad de La Laguna Airport (TFN) is located about 10 kilometres west of the capital, Santa Cruz de Tenerife, in the municipality of San Cristóbal de La Laguna. It mainly handles domestic flights: connecting flights to the other Canary Islands, such as Gran Canaria or Lanzarote, as well as scheduled flights to the Spanish mainland. The main destination is Madrid-Barajas, with over one million passengers, followed by Barcelona, Seville, and Bilbao. Tender for detection, supervision, and recording The tender documents specified the installation of a monitoring and control system to detect To further increase safety at Tenerife Norte-Ciudad de La Laguna Airport and to improve airport operations, the entire movement area was to be covered. The tender documents specified the installation of a monitoring and control system to detect, supervise, and record operations in that area in high resolution. Installation sites as critical points The total area to be monitored is huge, with the runway (with the focus at both ends), apron, taxiways, and service roads adjacent to the apron. The main challenge was that it was not possible to place camera masts randomly on the movement area, so existing buildings had to be used as installation points. Simplified maintenance “We wanted to minimise the number of installation points and camera systems to avoid the need for additional infrastructure such as masts, cabling, communication interfaces, etc., and to simplify subsequent maintenance processes,” says Carlos Jesús Delgado Gómez, Head of the Director’s Office at TFN. “And, of course, airports have strict regulations for any type of installation, especially in the movement area. That’s why there were very limited options when it came to selecting installation points. Nevertheless, the desired area had to be monitored at the highest resolution and the recording always had to be at maximum resolution.” High-resolution coverage High-resolution coverage of large areas under these conditions could not be satisfactorily achieved High-resolution coverage of large areas under these conditions – a minimum number of installation points and camera systems – could not be satisfactorily achieved with conventional single-sensor cameras. Tenerife Norte-Ciudad de La Laguna Airport therefore decided to use Dallmeier’s patented Panomera® multifocal sensor technology. Maximum resolution at long distances By combining multiple lenses and sensors with different focal lengths in a single optical unit, multifocal sensor technology offers high resolution across the entire object space. This means that even distant objects can be captured clearly, and significantly fewer systems are required overall than with conventional single-sensor cameras. “We were able to install the Panomera® on existing building facades and roofs without any problems”, says Carlos Jesús Delgado Gómez. “No other camera system was able to cover such a large area with so few cameras and installation points at such a high resolution.” Increasing operational safety and optimising processes The installed video technology not only increases operational safety but also allows processes to be optimised and disputes to be resolved quickly and clearly. One of the areas monitored is the aprons, where aircraft park and are prepared for the next flight. Since every minute spent parking is money for the airport company, there are always disputes about who is responsible for delays and the resulting additional parking fees. Was the fuel truck there on time? Did the catering arrive on time? Damage management can now be carried out quickly and objectively thanks to clear video recordings. For example, did the damage occur while the aircraft was parked or docked, or was it already there? The advantage of multi-user capability Any number of operators can access the image at the same time, each zooming in on the area of interest In addition to its ability to cover large areas, multifocal sensor technology is characterised by its multi-user capability. Panomera® works like a virtual combination of any number of PTZ cameras with the key advantage that the operator moves virtually in the image, rather than moving the camera mechanically as with PTZ cameras. As a result, any number of operators can access the image at the same time, each zooming in on the area of interest. Unlike conventional PTZ cameras, the entire image is always recorded. Bandwidth savings thanks to multicast capability As several users always need to access the live stream at the same time, the so-called multicast capability was also a decisive advantage of the Panomera®. Multicast capability allows data from a single source to be sent to multiple recipients simultaneously. This means that the video stream can be efficiently distributed to multiple devices or users without having to send the data multiple times. Multicast reduces network load and makes more efficient use of bandwidth. 3D simulation of the project, “CamCards” The entire project was precisely planned by Dallmeier with the help of a 3D simulation and pre-configured and tested in the company‘s own FAT Centre according to the customer‘s specifications. So-called CamCards, created by the Dallmeier 3D team, made the installation easier for the installer on site, as they show exactly where and at what angle the individual Panomera® cameras are to be mounted. Mountera® mounting system The Mountera® mounting system also proved its worth in practice, as Miguel Ángel Rodríguez Domínguez The Mountera® mounting system also proved its worth in practice, as Miguel Ángel Rodríguez Domínguez, project manager at installer Cobra Instalaciones y Servicios, Delegación Canarias, confirms, “The biggest challenge for us as installers was the high humidity and salt content due to the island location." "We therefore had to have bespoke, rust-proof, and robust masts and brackets made for the cameras. The actual installation of the Panomera® cameras with the Mountera® wall bracket and mast adapter was very easy.” Satisfied with the solution The video system has lived up to expectations and Tenerife North Airport is happy with its choice. Both the installer and the end customer are also satisfied with the support provided during the project. “We are very grateful for the support and solution-oriented assistance from Dallmeier Spain throughout the entire process, but especially during the implementation,” says Carlos Jesús Delgado Gómez. With the Dallmeier solution, consisting of a camera, recorder, and video management system, Tenerife Norte-Ciudad de La Laguna Airport is also well equipped for the future: The system is modular and can therefore be easily expanded or adapted to new challenges at any time.
The space-saving yet full-function video spectral comparator Regula 4306 has been deployed at Wattay International Airport in Vientiane, the Lao People’s Democratic Republic, to strengthen the country’s border security. This initiative aims to combat transnational crimes, including human trafficking, smuggling, and irregular migration. Forged identity documents Lao People’s Democratic Republic faces growing challenges in identifying forged identity documents Like many countries, the Lao People’s Democratic Republic faces growing challenges in identifying forged identity documents used by criminals and irregular migrants. Until recently, document verification at border checkpoints relied heavily on manual inspection, which was time-consuming, prone to errors, and less effective against increasingly sophisticated forgery techniques. Adopting a forensic solution In collaboration with International Organisation for Migration (IOM), the Lao immigration authorities began modernising their approach by adopting a forensic solution to strengthen document authentication and border security. In partnership with IOM in the Lao People’s Democratic Republic and the Australian Department of Home Affairs, the Lao immigration authorities deployed the Regula 4306 video spectral comparator at the country’s major airport in Vientiane. This step equipped border officials with advanced forensic tools for in-depth document authentication, and significantly automated the whole process. Array of features in the Regula 4306 With an array of features in the Regula 4306, ID proof at the Lao border earned much precision With a vast array of features in the Regula 4306, ID verification at the Lao border achieved much-needed high precision. For instance, the device’s high-resolution 8 MP camera with 60x optical zoom captures document images at up to 18,900 ppi and enables officials to analyse even the finest details, including printing techniques. Hyperspectral imaging module Additionally, with over 40 types of light sources and 18 light filters, the Regula 4306 allows authorities at the second line of border control to examine the most intricate document security features, such as holograms, watermarks, microprinting, and optically variable elements, ensuring a more reliable fraud detection process. Apart from that, 3D visualisation helps analyse a document’s surface relief and intersecting lines, and the hyperspectral imaging module enables forensic experts to detect document alterations, differentiate ink properties, or recover faded text. Regula Forensic Studio cross-platform software Regula 4306 is controlled via Regula Forensic Studio (RFS) cross-platform software Regula 4306 is controlled via Regula Forensic Studio (RFS) cross-platform software. With RFS, an expert can perform a wide range of examinations, conduct precise measurements and comparisons, process images in various modes, and generate comprehensive examination reports without losing a single detail. Its powerful tools and intuitive interface ensure accuracy and reliability, enabling thorough and efficient forensic investigations. Regula’s identity document template database Integrated with Regula Document Reader SDK, RFS enables comprehensive, automated document checks, eliminating the need for additional equipment or software. Regula Document Reader SDK can instantly recognise and validate IDs’ machine-readable zones (MRZs), RFID chips, barcodes, and invisible personal information (IPI), significantly reducing manual workload and minimising human error. Also, as it is backed up by Regula’s identity document template database (the most comprehensive in the world), this software is able to verify a wide range of IDs from 251 countries and territories, even the rarest ones. Adoption of Regula 4306 Regula experts conducted specialised training sessions for the Lao immigration officials To ensure seamless adoption of Regula 4306 at Wattay International Airport, Regula experts conducted specialised training sessions for the Lao immigration officials. This ensured that they had hands-on experience and were fully equipped to handle advanced document verification. “Integrating Regula’s devices into the Lao border management operations is a vital step toward combating serious crimes such as human trafficking and irregular migration. This technology enables detection of fraudulent documents with higher accuracy, eliminating human errors,” says Shareen Tuladhar, Chief of Mission, IOM in the Lao People’s Democratic Republic. Lao immigration authorities “Border crossings are the frontline of many serious crimes, making border security crucial to the country's overall safety. We are honoured to contribute to strengthening Lao border security." "By equipping the Lao immigration authorities with our top-selling video spectral comparator, the Regula 4306, we are providing them with advanced forensic tools to precisely detect even the most sophisticated document forgeries and stop criminals before they can cause harm,” comments Alex Lewanowicz, Director of Hardware Engineering at Regula.
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the full U.S. Department of Homeland Security SAFETY Act Designation. Announced that its proactive gun detection and intelligent situational awareness solution has been deployed by Carbon Cliff-Barstow School District (CCBSD) in Rock Island County, Illinois. Strengthening security with AI The ZeroEyes Gun Violence Research Centre has already analysed 34 gun-related eventsThe AI technology will be implemented at the district’s Pre-K through 8th grade school to enhance security and reduce response times in the event of a gun-related threat. The ZeroEyes Gun Violence Research Centre has already analysed 34 gun-related events at Illinois K-12 school districts this year alone. Recognising the ongoing threat of gun-related violence, the district is taking an important step by integrating ZeroEyes’ AI gun detection system to further bolster its security measures and protect against potential threats. Commitment to campus safety CCBSD maintains a comprehensive, multi-layered security programme in partnership with the Rock Island County Sheriff's Department to ensure the safety of students and staff. Alongside the district’s school resource officer, CCBSD has invested in a third-party monitored alarm system and recently upgraded its camera infrastructure. An on-site behavioural interventionist is also employed to build strong relationships with students and families. Strengthening security “We take great pride in ensuring the safety and success of all students and staff members at our school,” said Eric Lawson, Superintendent of CCBSD. “By incorporating ZeroEyes, we’re adding another important layer of safety to our campus, and we’re confident that this proactive approach will help us promote a safe learning environment.” Smart solutions with ZeroEyes CCBSD serves 240 students from diverse backgrounds in an urban area of northwest Illinois CCBSD serves 240 students from diverse backgrounds in an urban area of northwest Illinois, part of the Quad Cities region. The district’s mission is to prepare students to be academically successful and career-ready, foster a love for learning, and help students reach their full potential as confident, lifelong learners. The district’s 40 staff members are dedicated to ensuring the safety and educational success of every student. ZeroEyes' AI gun detection and intelligent situational awareness software layers onto CCBSD’s existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC. Protecting with precision The industry's only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to first responders and local staff as quickly as 3 to 5 seconds from detection. Innovating school security “The safety of students and staff is a priority for Carbon Cliff-Barstow, and we are honored to play a role in supporting that mission," said Mike Lahiff, CEO and co-founder of ZeroEyes. “Our AI gun detection system will provide the district with the actionable intelligence needed to mitigate potential threats, helping to ensure a safer environment for students and staff."


Round table discussion
As physical security technologies become more complex, it is incumbent on the dealer/integrator to have the skills and expertise needed to ensure that a system operates smoothly. The value of integrators increasingly rests on the skill sets they bring to bear when installing a system. If the skills are missing, there is a problem. We asked this week’s Expert Panel Roundtable: What missing skills among security integrators can cause problems for customers?
The role of the integrator/installer in the physical security marketplace is shifting as technologies evolve and applications expand. Integrators are being faced with a need to augment their expertise both in a wider range of systems and deeper into the specifics of each increasingly complex technology. At the end of the day, it falls to the integrator/installer to ensure a system performs as promised, however much a consultant or even a manufacturer might be involved in the process. We asked this week’s Expert Panel Roundtable: How is the role of the security installer/integrator changing?
“Deep learning” is recently among the more prevalent jargon in the physical security industry, and for good reason. The potential benefits of this subset of artificial intelligence (AI) are vast, and those benefits are only now beginning to be understood and realised. But how can we separate the marketing hype from reality? How can we differentiate between future potential and the current state of the art? To clarify the latest on this new technology, we asked this week’s Expert Panel Roundtable: What is “deep learning?” How well does the security industry understand its full potential?
Products


Videos
PTZ cameras: Manufacturers & Suppliers
- Hikvision PTZ cameras
- Dahua Technology PTZ cameras
- Hanwha Vision PTZ cameras
- AV Costar PTZ cameras
- LILIN PTZ cameras
- Bosch PTZ cameras
- Axis Communications PTZ cameras
- Pelco PTZ cameras
- Vicon PTZ cameras
- Avigilon PTZ cameras
- Verkada PTZ cameras
- Videotec PTZ cameras
- Honeywell Security PTZ cameras
- Sony PTZ cameras
- Messoa PTZ cameras
- IDIS PTZ cameras
- FLIR Systems PTZ cameras
- Illustra PTZ cameras
- TruVision PTZ cameras
- Visionhitech PTZ cameras

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download