IP security solutions
With the recent update of its Document Reader SDK, Regula became the first identity verification (IDV) vendor to make it possible to verify all the dynamic security features of documents in real time. With the latest addition of Dynaprint® checks, the solution ensures more robust physical document authentication during remote onboarding. The innovation has arrived at a time when 58% of businesses globally face fake or modified IDs during digital onboarding. Dynamic se...
Kaseya, the pioneering provider of AI-powered cybersecurity and IT management software, has announced its Spring 2025 release with new features that equips MSPs and internal IT teams with new capabilities to automate workflows, enhance the end-user experience, and strengthen security posture ahead of Kaseya Connect, where the company will debut the latest evolution of Kaseya 365. “Innovation is not just part of our roadmap — it’s embedded in our DNA,” said Jim Lippie, Ch...
Everon, a pioneering security integrator and premier provider of commercial security, video, fire and life safety solutions in the U.S., announced the promotion of Chris Heugle to Senior Vice President, Commercial Sales & Integrated Solutions, and Greg Mastroserio to Vice President, Commercial & Integrated Solutions Sales to lead companywide strategic sales initiatives. With nearly 20 years of industry experience, Heugle will now oversee Everon’s overarching sales strategy, bringi...
The Physical Security Interoperability Alliance (PSIA) hosted a well-attended cocktail reception and live demonstration during ISC West 2025 to unveil its latest advancement: the PKOC 3.0 specification, an exciting solution for secure, open credentialing in physical access control systems. Jason Ouellette, Chairman of the PSIA and Corporate VP of Innovation and Technical Partnerships at ELATEC, led the presentation. He shared an overview of PKOC’s progre...
For all the emphasis on cloud systems and centralised servers at ISC West, a lot of innovation in security video systems is happening at the edge. New advancements inside video cameras are boosting capabilities at the edge, from advancements in processing power to artificial intelligence (AI) and machine learning (ML) algorithms that can now be deployed directly on the cameras or edge devices. Advancements in AI algorithms The progress of video systems becoming smarter at the edge is driven...
i-PRO Co., Ltd. (formerly Panasonic Security), a pioneer in professional security and public safety solutions, announces that from October 1, 2025, the Saga Factory (Tosu City, Saga Prefecture, Japan) will be positioned and operated as the core factory, starting with the production of security cameras. They will expand the system to supply high-quality "Made in Japan" products from Japan to the world. Production of security cameras The monthly production volume will start at approximately 14,...
News
SERMA Safety and Security has become the first laboratory to be accredited under the EUCC scheme by ANSSI (Agence Nationale de la Sécurité des Systèmes d’Information, the French National Cybersecurity Agency). This strategic recognition allows SERMA to assess hardware and software products under the new European Union Common Criteria (EUCC) security framework, contributing to the harmonisation and digital sovereignty of Europe. Laboratory to conduct EUCC evaluations SERMA Safety & Security is the first laboratory to have conducted security evaluations in Europe SERMA Safety & Security is the first laboratory to have conducted security evaluations, pioneering the issuance of the first EUCC certificates in Europe. Issued by ANSSI, these certificates, valid for five years, mark a key milestone in the European recognition of cybersecurity solutions. Ranked among the top 5 security laboratories worldwide and the second-best globally for Common Criteria evaluations, SERMA takes a new step forward with its EUCC accreditation. SERMA accreditation With this accreditation, SERMA is now authorised to assess: Critical equipment embedded in sensitive infrastructures (energy, transport, telecommunications), Cybersecurity solutions for industries and institutions. European Cybersecurity Certification Conference The announcement was made on March 13, 2025, during the European Cybersecurity Certification Conference in Warsaw. Supported by the European Commission and the Polish presidency, this event brought together leading experts and decision-makers in the certification sector. As cyber threats continue to rise, the European Union has introduced the EUCC scheme to harmonise cybersecurity certification requirements. With this accreditation, SERMA Safety & Security establishes itself as a key player in this transition toward a unified and strengthened European cybersecurity framework.
Bugcrowd, the pioneer in crowdsourced security, announced an alliance with GlobalDots, the cloud innovation and security specialist. Under the agreement, Germany-based GlobalDots will integrate Bugcrowd’s crowdsourced security platform into its portfolio of cloud infrastructure, CDN, DevOps, and AI solutions. Bugcrowd’s AI-powered platform The alliance will make Bugcrowd’s AI-powered crowdsourcing platform available to GlobalDots’ 350-plus international client base, which includes Lufthansa, Playtika, AppsFlyer, Fiat and Payoneer. GlobalDots clients will have access to the full range of Bugcrowd’s advanced security solutions including bug bounty, vulnerability disclosure programmes, penetration testing, AI bias assessment and attack surface management. Security point solutions Bugcrowd was driven by rising demand for serial testing and disenchantment with security point solutions GlobalDots said the relationship with Bugcrowd was driven by rising demand for continuous testing and disenchantment with security point solutions. Ben Dagani, Head of Business Development, GlobalDots, said: “Partnering with Bugcrowd is a strategic move because we’re witnessing increasing demand for their solution both in Israel and across Europe. It’s not just a one-time compliance tool — our customers now rely on it continuously to keep pace with a dynamic and evolving threat landscape." Bugcrowd’s continuous testing services Dagani added: “Integrating their platform enhances our proactive cybersecurity offerings, aligning with our mission to deliver cutting-edge cloud security solutions.” Paul Ciesielski, Chief Revenue Officer of Bugcrowd, said: “GlobalDots has been a pioneer in cloud optimisation and innovation for more than two decades, working with a formidable ecosystem of vendors to deliver secure, high-performance applications and services for a wide range of use cases." "We’re delighted that they have decided to add Bugcrowd’s continuous testing services to their portfolio, enabling GlobalDots customers to harden their security and development processes.”
iDenfy, a globally recognised RegTech company specialising in identity verification, fraud prevention, and compliance solutions, unveiled its Partner Program, designed to foster collaboration with businesses, consultants, and technology providers. The program aims to extend iDenfy's advanced Know Your Customer (KYC), Anti-Money Laundering (AML), and Know Your Business (KYB) solutions to a broader market, enabling partners to test seamless identity verification solutions while generating new revenue streams. Identity verification solutions As cyber threats escalate and regulatory requirements tighten, businesses across industries face increasing pressure to implement robust identity verification and compliance solutions. The global demand for secure KYC, AML, and other fraud prevention tools has never been higher that created an opportunity for companies to capitalise on this growing market. AI-powered identity verification iDenfy, a RegTech pioneer in AI-powered identity verification, has launched its Partner Program Recognising this need, iDenfy, a globally trusted RegTech pioneer in AI-powered identity verification, has launched its Partner Program, a strategic initiative that allows businesses to monetise the booming demand for compliance solutions by earning revenue share from every successfully onboarded client. By teaming up with iDenfy, partners gain access to cutting-edge verification technology testing accounts to better understand the product company offers and get all necessary information, such as banners, images, and important information to kickstart affiliate careers. Fintech innovators and compliance experts Domantas Ciulde, CEO of iDenfy, emphasised the program's strategic importance: "Our Partner Program is more than just a business opportunity; it's a commitment to empowering organisations with best-in-class identity verification tools." "By collaborating with fintech innovators and compliance experts, we can expand our reach while helping businesses combat fraud and meet regulatory demands efficiently." KYC/AML solutions The program is primarily designed for financial institutions that need strong AML, KYC, and KYB tools The program is primarily designed for financial institutions that need strong AML, KYC, and KYB tools, but it's also widely used by e-commerce platforms and iGaming businesses looking to prevent fraud and integrate identity verification into their operations. According to iDenfy’s team, it’s an ideal solution for tech companies looking to enhance their platforms with identity verification, consulting firms advising clients on compliance and fraud prevention, financial service providers needing scalable KYC/AML solutions, and marketplaces and gig economy platforms requiring user authentication. iDenfy fraud prevention tools Partners receive exclusive incentives, including custom pricing, marketing support, and technical training, to maximise their success. As a trusted RegTech provider, iDenfy delivers a suite of compliance and fraud prevention tools combining AI, biometric analysis, and liveness detection to prevent identity fraud. Its automated KYC and KYB verification processes enable businesses to validate identities efficiently. AML screening feature The AML screening feature provides real-time monitoring against global sanctions and PEP lists Biometric authentication, including facial recognition and liveness detection, helps prevent spoofing attempts, while AI-powered document verification ensures the authenticity of IDs, passports, and utility bills. The AML screening feature provides real-time monitoring against global sanctions and politically exposed persons (PEP) lists. Furthermore, advanced fraud detection systems analyse people's behaviour to identify suspicious activities, helping businesses mitigate risks. These solutions help businesses reduce fraud, streamline onboarding, and maintain regulatory compliance across industries such as banking, fintech, cryptocurrency, healthcare, and gig economy platforms. iDenfy's flexible API integrations iDenfy's flexible API integrations make it easy for partners to embed verification services into their existing platforms, ensuring a frictionless experience for end-users. Partners benefit from competitive revenue-sharing models, dedicated support, and co-marketing opportunities to drive mutual growth. According to recent studies, identity fraud costs businesses over $50 million annually, with synthetic identity fraud being one of the fastest-growing threats.
ASSA ABLOY has acquired Pedestal PRO, a US manufacturer of access control pedestals, bollards, and innovative mounting solutions. "I am very pleased to welcome Pedestal PRO into the ASSA ABLOY Group. This acquisition delivers on our strategy to strengthen our position in mature markets through adding complementary products and solutions to our core business,” says Nico Delvaux, President and CEO of ASSA ABLOY. Pedestal PRO electromechanical solutions "Pedestal PRO is an established innovator that seamlessly integrates design, architectural elements, and access control technology, and I am excited for them to be part of ASSA ABLOY," says Lucas Boselli, Executive Vice President of ASSA ABLOY and Head of the Americas Division. "Their product portfolio enhances our offering for electromechanical solutions and solidifies our position as a go-to partner for access control equipment manufacturers, system integrators, and security professionals." Pedestal PRO in USA Pedestal PRO was founded in 2002 and has some 50 employees. The main office and factory are located in Lindon, Utah, USA. Sales for 2024 amounted to about MUSD 11 (approx. MSEK 120) with a good EBIT margin. The acquisition will be accretive to EPS from the start.
The Monitoring Association (TMA) is pleased to announce David Charney, senior vice president video command centre, Everon, will deliver the keynote address at the 2025 TMA Virtual Mid-Year Meeting on Tuesday, April 29, 2025, at 10:00 AM/ET. His address, titled, 'Inspiring Leadership in a Changing World,' will speak directly to the evolving landscape of leadership in the monitoring industry. The 2025 TMA Virtual Mid-Year Meeting will take place virtually over three days, Tuesday, April 29th-Thursday, May 1st. New video technologies and AI solutions “The monitoring industry is in a transformative phase as new video technologies and AI solutions have emerged and introduced new heights of efficiency and effectiveness,” stated TMA President Steve Butkovich. “We’re grateful to have David to deliver the opening keynote address at this year’s meeting. He is a dynamic, seasoned, and respected pioneer who has successfully navigated change and inspired transformation. His unique insights are certain to inspire our attendees.” How to cultivate a leadership mindset Charney will examine changes in leadership and how to cultivate a leadership mindset that embraces change In his keynote presentation, Charney will examine changes in leadership and how to cultivate a leadership mindset that embraces change and drives innovation. “No matter who you are, what your purpose and your level of comfort, we are all going through change. Perspective matters,” stated David Charney. “My comments will help monitoring professionals navigate through monitoring industry adaptations taking place now and provide key steps for success along the way.” Prior roles of Charney Charney joined Everon in March 2025 after more than 15 years at Stealth Monitoring, where he served in four successive positions, beginning as President in October 2011 and concluding as Chief Customer Officer. Charney was responsible for 17 offices in three countries and more than 1200 employees in his role as Chief Operating Officer at Stealth. An avid public speaker, he speaks to crowds on topics ranging from thought leadership across technical topics to motivational speeches at University Campuses.
3DX-Ray has sold two AXIS-CXi, cabinet-based x-ray systems to secure high-threat sites in Rome, Italy. AXIS-CXi was originally designed to bring the same colour-differentiating image technology used in airport baggage screening, to the mail room environment. AXIS-CXi quickly showed its potential in a whole variety of security scenarios, from embassy lobbies to the homes of high-net-worth individuals. AXIS-CXi differentiated scans Grey scale is used for the recognition of shapes and the form of objects The AXIS-CXi was a huge step forward in mail room scanning, as colour differentiated scans enable operators to determine not just the shape but, the nature of the materials being scanned. Orange shows organics, such as; explosives, chemicals and drugs, as well as more innocent items such as foodstuffs. Blue shows metals, such as; guns, knives, and potential IED components. Green shows inorganic materials like those used in homemade explosives. Grey scale is used for the recognition of shapes and the form of objects. This allows the operator, with very little training, to analyse items more accurately, quickly and easily. AXIS-CXi range of security scenarios But another major innovation is in the design itself. The AXIS-CXi has an extra-large inspection chamber, whilst maintaining a small footprint. So, not only can it scan mail and parcels, but it can also scan bags up to and including aircraft cabin bags. The system is mobile and aesthetically sympathetic, meaning that it can be used in offices, hotel lobbies, banks, retail centres, in fact anywhere! 3DX-RAY LTD, CEO, Vincent Deery said: “AXIS-CXi with its combination technology and unobtrusive good looks has once again proved its usefulness in an ever-growing range of security scenarios.”
SERMA Safety and Security has become the first laboratory to be accredited under the EUCC scheme by ANSSI (Agence Nationale de la Sécurité des Systèmes d’Information, the French National Cybersecurity Agency). This strategic recognition allows SERMA to assess hardware and software products under the new European Union Common Criteria (EUCC) security framework, contributing to the harmonisation and digital sovereignty of Europe. Laboratory to conduct EUCC evaluations SERMA Safety & Security is the first laboratory to have conducted security evaluations in Europe SERMA Safety & Security is the first laboratory to have conducted security evaluations, pioneering the issuance of the first EUCC certificates in Europe. Issued by ANSSI, these certificates, valid for five years, mark a key milestone in the European recognition of cybersecurity solutions. Ranked among the top 5 security laboratories worldwide and the second-best globally for Common Criteria evaluations, SERMA takes a new step forward with its EUCC accreditation. SERMA accreditation With this accreditation, SERMA is now authorised to assess: Critical equipment embedded in sensitive infrastructures (energy, transport, telecommunications), Cybersecurity solutions for industries and institutions. European Cybersecurity Certification Conference The announcement was made on March 13, 2025, during the European Cybersecurity Certification Conference in Warsaw. Supported by the European Commission and the Polish presidency, this event brought together leading experts and decision-makers in the certification sector. As cyber threats continue to rise, the European Union has introduced the EUCC scheme to harmonise cybersecurity certification requirements. With this accreditation, SERMA Safety & Security establishes itself as a key player in this transition toward a unified and strengthened European cybersecurity framework.
Bugcrowd, the pioneer in crowdsourced security, announced an alliance with GlobalDots, the cloud innovation and security specialist. Under the agreement, Germany-based GlobalDots will integrate Bugcrowd’s crowdsourced security platform into its portfolio of cloud infrastructure, CDN, DevOps, and AI solutions. Bugcrowd’s AI-powered platform The alliance will make Bugcrowd’s AI-powered crowdsourcing platform available to GlobalDots’ 350-plus international client base, which includes Lufthansa, Playtika, AppsFlyer, Fiat and Payoneer. GlobalDots clients will have access to the full range of Bugcrowd’s advanced security solutions including bug bounty, vulnerability disclosure programmes, penetration testing, AI bias assessment and attack surface management. Security point solutions Bugcrowd was driven by rising demand for serial testing and disenchantment with security point solutions GlobalDots said the relationship with Bugcrowd was driven by rising demand for continuous testing and disenchantment with security point solutions. Ben Dagani, Head of Business Development, GlobalDots, said: “Partnering with Bugcrowd is a strategic move because we’re witnessing increasing demand for their solution both in Israel and across Europe. It’s not just a one-time compliance tool — our customers now rely on it continuously to keep pace with a dynamic and evolving threat landscape." Bugcrowd’s continuous testing services Dagani added: “Integrating their platform enhances our proactive cybersecurity offerings, aligning with our mission to deliver cutting-edge cloud security solutions.” Paul Ciesielski, Chief Revenue Officer of Bugcrowd, said: “GlobalDots has been a pioneer in cloud optimisation and innovation for more than two decades, working with a formidable ecosystem of vendors to deliver secure, high-performance applications and services for a wide range of use cases." "We’re delighted that they have decided to add Bugcrowd’s continuous testing services to their portfolio, enabling GlobalDots customers to harden their security and development processes.”
iDenfy, a globally recognised RegTech company specialising in identity verification, fraud prevention, and compliance solutions, unveiled its Partner Program, designed to foster collaboration with businesses, consultants, and technology providers. The program aims to extend iDenfy's advanced Know Your Customer (KYC), Anti-Money Laundering (AML), and Know Your Business (KYB) solutions to a broader market, enabling partners to test seamless identity verification solutions while generating new revenue streams. Identity verification solutions As cyber threats escalate and regulatory requirements tighten, businesses across industries face increasing pressure to implement robust identity verification and compliance solutions. The global demand for secure KYC, AML, and other fraud prevention tools has never been higher that created an opportunity for companies to capitalise on this growing market. AI-powered identity verification iDenfy, a RegTech pioneer in AI-powered identity verification, has launched its Partner Program Recognising this need, iDenfy, a globally trusted RegTech pioneer in AI-powered identity verification, has launched its Partner Program, a strategic initiative that allows businesses to monetise the booming demand for compliance solutions by earning revenue share from every successfully onboarded client. By teaming up with iDenfy, partners gain access to cutting-edge verification technology testing accounts to better understand the product company offers and get all necessary information, such as banners, images, and important information to kickstart affiliate careers. Fintech innovators and compliance experts Domantas Ciulde, CEO of iDenfy, emphasised the program's strategic importance: "Our Partner Program is more than just a business opportunity; it's a commitment to empowering organisations with best-in-class identity verification tools." "By collaborating with fintech innovators and compliance experts, we can expand our reach while helping businesses combat fraud and meet regulatory demands efficiently." KYC/AML solutions The program is primarily designed for financial institutions that need strong AML, KYC, and KYB tools The program is primarily designed for financial institutions that need strong AML, KYC, and KYB tools, but it's also widely used by e-commerce platforms and iGaming businesses looking to prevent fraud and integrate identity verification into their operations. According to iDenfy’s team, it’s an ideal solution for tech companies looking to enhance their platforms with identity verification, consulting firms advising clients on compliance and fraud prevention, financial service providers needing scalable KYC/AML solutions, and marketplaces and gig economy platforms requiring user authentication. iDenfy fraud prevention tools Partners receive exclusive incentives, including custom pricing, marketing support, and technical training, to maximise their success. As a trusted RegTech provider, iDenfy delivers a suite of compliance and fraud prevention tools combining AI, biometric analysis, and liveness detection to prevent identity fraud. Its automated KYC and KYB verification processes enable businesses to validate identities efficiently. AML screening feature The AML screening feature provides real-time monitoring against global sanctions and PEP lists Biometric authentication, including facial recognition and liveness detection, helps prevent spoofing attempts, while AI-powered document verification ensures the authenticity of IDs, passports, and utility bills. The AML screening feature provides real-time monitoring against global sanctions and politically exposed persons (PEP) lists. Furthermore, advanced fraud detection systems analyse people's behaviour to identify suspicious activities, helping businesses mitigate risks. These solutions help businesses reduce fraud, streamline onboarding, and maintain regulatory compliance across industries such as banking, fintech, cryptocurrency, healthcare, and gig economy platforms. iDenfy's flexible API integrations iDenfy's flexible API integrations make it easy for partners to embed verification services into their existing platforms, ensuring a frictionless experience for end-users. Partners benefit from competitive revenue-sharing models, dedicated support, and co-marketing opportunities to drive mutual growth. According to recent studies, identity fraud costs businesses over $50 million annually, with synthetic identity fraud being one of the fastest-growing threats.
ASSA ABLOY has acquired Pedestal PRO, a US manufacturer of access control pedestals, bollards, and innovative mounting solutions. "I am very pleased to welcome Pedestal PRO into the ASSA ABLOY Group. This acquisition delivers on our strategy to strengthen our position in mature markets through adding complementary products and solutions to our core business,” says Nico Delvaux, President and CEO of ASSA ABLOY. Pedestal PRO electromechanical solutions "Pedestal PRO is an established innovator that seamlessly integrates design, architectural elements, and access control technology, and I am excited for them to be part of ASSA ABLOY," says Lucas Boselli, Executive Vice President of ASSA ABLOY and Head of the Americas Division. "Their product portfolio enhances our offering for electromechanical solutions and solidifies our position as a go-to partner for access control equipment manufacturers, system integrators, and security professionals." Pedestal PRO in USA Pedestal PRO was founded in 2002 and has some 50 employees. The main office and factory are located in Lindon, Utah, USA. Sales for 2024 amounted to about MUSD 11 (approx. MSEK 120) with a good EBIT margin. The acquisition will be accretive to EPS from the start.
The Monitoring Association (TMA) is pleased to announce David Charney, senior vice president video command centre, Everon, will deliver the keynote address at the 2025 TMA Virtual Mid-Year Meeting on Tuesday, April 29, 2025, at 10:00 AM/ET. His address, titled, 'Inspiring Leadership in a Changing World,' will speak directly to the evolving landscape of leadership in the monitoring industry. The 2025 TMA Virtual Mid-Year Meeting will take place virtually over three days, Tuesday, April 29th-Thursday, May 1st. New video technologies and AI solutions “The monitoring industry is in a transformative phase as new video technologies and AI solutions have emerged and introduced new heights of efficiency and effectiveness,” stated TMA President Steve Butkovich. “We’re grateful to have David to deliver the opening keynote address at this year’s meeting. He is a dynamic, seasoned, and respected pioneer who has successfully navigated change and inspired transformation. His unique insights are certain to inspire our attendees.” How to cultivate a leadership mindset Charney will examine changes in leadership and how to cultivate a leadership mindset that embraces change In his keynote presentation, Charney will examine changes in leadership and how to cultivate a leadership mindset that embraces change and drives innovation. “No matter who you are, what your purpose and your level of comfort, we are all going through change. Perspective matters,” stated David Charney. “My comments will help monitoring professionals navigate through monitoring industry adaptations taking place now and provide key steps for success along the way.” Prior roles of Charney Charney joined Everon in March 2025 after more than 15 years at Stealth Monitoring, where he served in four successive positions, beginning as President in October 2011 and concluding as Chief Customer Officer. Charney was responsible for 17 offices in three countries and more than 1200 employees in his role as Chief Operating Officer at Stealth. An avid public speaker, he speaks to crowds on topics ranging from thought leadership across technical topics to motivational speeches at University Campuses.
3DX-Ray has sold two AXIS-CXi, cabinet-based x-ray systems to secure high-threat sites in Rome, Italy. AXIS-CXi was originally designed to bring the same colour-differentiating image technology used in airport baggage screening, to the mail room environment. AXIS-CXi quickly showed its potential in a whole variety of security scenarios, from embassy lobbies to the homes of high-net-worth individuals. AXIS-CXi differentiated scans Grey scale is used for the recognition of shapes and the form of objects The AXIS-CXi was a huge step forward in mail room scanning, as colour differentiated scans enable operators to determine not just the shape but, the nature of the materials being scanned. Orange shows organics, such as; explosives, chemicals and drugs, as well as more innocent items such as foodstuffs. Blue shows metals, such as; guns, knives, and potential IED components. Green shows inorganic materials like those used in homemade explosives. Grey scale is used for the recognition of shapes and the form of objects. This allows the operator, with very little training, to analyse items more accurately, quickly and easily. AXIS-CXi range of security scenarios But another major innovation is in the design itself. The AXIS-CXi has an extra-large inspection chamber, whilst maintaining a small footprint. So, not only can it scan mail and parcels, but it can also scan bags up to and including aircraft cabin bags. The system is mobile and aesthetically sympathetic, meaning that it can be used in offices, hotel lobbies, banks, retail centres, in fact anywhere! 3DX-RAY LTD, CEO, Vincent Deery said: “AXIS-CXi with its combination technology and unobtrusive good looks has once again proved its usefulness in an ever-growing range of security scenarios.”


Expert commentary
As city managers, law enforcement agencies, and first responders face mounting pressure to combat crime and respond to emergencies with limited resources, real-time crime centres empowered by a new generation of data-driven technologies are emerging as an effective force multiplier. Real-time crime centres Real-time crime centres (RTCCs) serve as centralised hubs where dedicated personnel leverage pioneering-edge technologies to analyse diverse data streams and provide critical support to law enforcement and emergency operations. These 24/7 facilities are transforming how agencies gather, process, and act upon information, enabling more proactive and efficient policing strategies. The core functions of RTCCs These centres provide officers with unprecedented situational awareness and real-time intelligence At their core, RTCCs are tasked with three primary objectives: enhancing safety, facilitating identification, and supporting apprehension. By integrating data from a wide range of data sources, these centres provide officers with unprecedented situational awareness and real-time intelligence. Integrated data approach This integrated data approach allows RTCCs to alert officers to potential threats, quickly identify suspects, and guide responders during critical incidents. For instance, in the event of a robbery, RTCC operators can rapidly search camera and licence plate data to track suspect vehicles, significantly improving the chances of a swift arrest. According to the Bureau of Justice Assistance at the U.S. Department of Justice, the mission of an RTCC is to centralise a broad range of current and evolving technologies, coordinate sworn and non-sworn human resources, and direct the attention to high-crime areas, active crimes in progress, high-profile or highly recidivistic offenders, and large-scale public events that may require law enforcement presence or response. The technology powering RTCCs The effectiveness of an RTCC hinges on its ability to seamlessly integrate a wide array of technologies: Open Platform Video Technology: At the heart of many crime centres is an open platform video management software (VMS) that serves as the central nervous system, unifying diverse data streams into a cohesive operational picture. By leveraging open APIs and SDKs, the VMS can incorporate a wide range of cameras, sensors, and analytics tools. This data-driven approach to video technology enables seamless alert distribution to both the RTCC and field officers via mobile applications. IP Camera Networks: The eyes of an RTCC, these systems combine fixed, PTZ, multi-sensor, thermal, and other specialty cameras to provide continuous city monitoring. Strategically placed throughout urban areas, cameras offer comprehensive coverage of critical locations such as transportation hubs, commercial districts, and high-crime zones. This network forms the foundation for real-time monitoring and incident response. Sensor Arrays: Beyond visual data, RTCCs employ various sensor technologies. Acoustic sensors can detect sounds such as gunshots, shouts for help, breaking glass, and other sounds instantly alerting officers and cueing nearby cameras. Environmental sensors monitor air quality for gasses, smoke, and other non-visible hazards. Licence Plate Recognition (LPR): LPR systems act as a force multiplier, continuously scanning for vehicles of interest. By generating real-time alerts for stolen or wanted vehicles, these systems significantly enhance the ability to track suspects and recover stolen property, contributing to reduced auto theft rates. Aerial Surveillance: Many RTCCs incorporate drone technology, providing on-demand aerial perspectives of developing situations. This capability is particularly valuable for monitoring large-scale events, assessing natural disasters, supporting operations in hard-to-reach areas, and serving as a powerful first response for crime scene situational awareness. AI-Powered Analytics: At the heart of many RTCC operations are sophisticated AI algorithms that analyse video data in real-time. These systems can identify a range of suspicious activities, from unattended packages to unauthorised intrusions. By rapidly processing vast amounts of video data, they help operators focus on potential threats and anomalies. Geospatial Mapping: To make sense of the influx of data, RTCCs rely on advanced mapping software. These tools visualise events, alerts, and data streams geographically, allowing operators to quickly identify patterns, clusters of activity, and relationships between incidents. Database Integration: RTCCs maintain direct connections to various law enforcement databases, including local, state, and federal resources like the National Crime Information centre (NCIC). This integration allows for rapid background checks and threat assessments, providing crucial context for ongoing operations. Cloud Infrastructure: The scalability and flexibility of cloud computing are revolutionising RTCC capabilities. Cloud and hybrid solutions offer secure, off-site storage and facilitate easy data sharing between agencies. This approach not only reduces initial costs but also allows for incremental upgrades, making advanced RTCC functionality accessible even to agencies with limited budgets. Real-world impact RTCC operators tracked shooting suspects via camera feeds, guiding officers to their location The proliferation of RTCCs across the United States with over 80 centres in operation speaks to their proven effectiveness. Cities that have implemented these high-tech command centres are reporting significant improvements in response times, clearance rates, and overall public safety. Real-time surveillance In Winston-Salem, North Carolina, the local RTCC leverages over 1,300 live video feeds to provide real-time surveillance across the city. This extensive network, combined with gunshot detection technology and licence plate readers, has already demonstrated its value. In a recent incident, RTCC operators were able to track shooting suspects via camera feeds, guiding officers to their location for a quick apprehension. Video analysis by RTCC Similarly, Newport News, Virginia, saw an immediate impact after launching its RTCC in 2021. The centre has played a crucial role in solving homicides caught on video and rapidly closing a series of carjacking cases. These success stories underscore the game-changing potential of RTCCs when it comes to solving crimes and gathering evidence. In Memphis, Tennessee, video analysis by RTCC detectives helped identify a shooter in custody following an incident at a community basketball court even when no witnesses had come forward. Identifying suspects with RTCC Officers and analysts can view street and body camera footage to monitor crowds at parades The Jackson Police Department in Mississippi has seen similar benefits since building an RTCC in 2019, part of a broader effort that included deploying 100 cameras and 271 body cams. Officers and analysts can view street and body camera footage to monitor crowds at parades and other events. During pursuits, the cameras provide extra surveillance, allowing officers to identify suspects or witnesses to help solve crimes. Enhancing crime mitigation and emergency response While RTCCs have proven their worth in responding to active incidents, their true potential lies in proactive crime prevention and enhanced emergency preparedness. By leveraging advanced analytics and integrated data sources, RTCCs are evolving into powerful predictive tools for law enforcement. Pattern recognition algorithms For instance, pattern recognition algorithms can analyse historical crime data alongside real-time video feeds to identify potential hotspots for criminal activity. This allows law enforcement to strategically deploy resources, increasing visible presence in high-risk areas before crimes occur. Similarly, anomaly detection systems can alert RTCC operators to unusual behaviors or suspicious activities, enabling early intervention in potentially dangerous situations. Asset and property protection, automated alerts RTCCs can monitor critical infrastructure, government buildings, and other high-value assets 24/7 Asset and property protection is another area where RTCCs excel. By integrating with access control systems and using AI-powered video analytics, RTCCs can monitor critical infrastructure, government buildings, and other high-value assets 24/7. Automated alerts for perimeter breaches, unauthorised access attempts, or suspicious objects left in restricted areas allow for an immediate response, significantly enhancing security postures. Emergency response and preparedness In terms of emergency response and preparedness, RTCCs serve as vital command and coordination centres during crises. Whether facing natural disasters, major accidents, or other large-scale emergencies, RTCCs provide a centralised hub for information gathering and dissemination. Real-time video streams from affected areas, combined with data from environmental sensors and emergency service communications, allow for rapid situational assessment and coordinated response efforts. Post-incident investigation and analysis RTCCs can also play an active role in post-incident investigation and analysis. The ability to quickly compile and analyse vast amounts of data from multiple sources can significantly accelerate case resolution and help identify patterns to prevent future incidents. As RTCCs continue to evolve, their capacity for integrating diverse data streams and leveraging advanced analytics positions them as indispensable tools in modern law enforcement strategy. The future of technology-driven policing The integration of artificial intelligence and machine learning promises to enhance video analytics As RTCCs continue to evolve, they are likely to incorporate even more advanced technologies. The integration of artificial intelligence and machine learning promises to enhance video analytics capabilities, enabling faster and more accurate threat detection. Additionally, the expanding use of drones, subject to FAA regulations, could provide RTCCs with cost-effective aerial surveillance options. Effective and ethical operations However, the implementation of RTCCs is not without challenges. Agencies must navigate issues of privacy, data security, and community trust. Ongoing training for personnel and careful planning is essential to ensure these centres operate effectively and ethically. Data-driven approach Despite these hurdles, the trend toward technology-driven policing shows no signs of slowing. RTCCs represent a shift from reactive to proactive law enforcement strategies, offering a data-driven approach to crime prevention and response. As these centres become more prevalent, they will play an increasingly vital role in helping agencies maximise their resources and make informed decisions, ultimately contributing to safer communities for all.
Security manufacturers throw around the term “scalable” a lot these days, but few dive into what scalable really means for modern organisations and their security programs. Achieving true scalability, or as I like to refer to as “expandable with a purpose,” takes planning and coordination from security pioneers alongside the broader organisation. Implementing a flexible strategy is critically important in the age of advancing analytics and intelligence-driven technology. So what exactly do we mean by “scalable”? "Scalable" refers to the capability of a system, process, or technology to handle growth or increased demand without compromising performance, efficiency, or quality. To put it simply, scalability refers to the ability of a solution to expand or adapt to accommodate larger workloads, higher volumes of data, or increased complexity without requiring significant changes to its underlying architecture or design. It’s not enough to create a “fix it and forget it” security program. Not only do the needs of the organisations shift, but growth (or even shrink) is inevitable. How to Approach Growth Pioneers must be prepared to adapt their strategies and approaches to manage security risks For many security pioneers, growth has a trickle-down effect. Expansion through mergers and acquisitions or organic growth, in addition to decreases in facility or employee count, directly impacts the security program. Whether it’s an increase or decrease in size, workload, or scope, these pioneers must be prepared to adapt their strategies and approaches to efficiently manage security risks while maintaining operational efficiency. Here are some ways security pioneers can approach growth: Assess the here and now: Begin by looking at the current state of your security program, including the resources, capabilities, processes, and technology infrastructure. Understanding existing strengths, weaknesses, and areas for improvement can help inform planning for the future. Align with the business: This might be one of the most important considerations to make, but ensuring security pioneers understand the organisation’s growth objectives, priorities, and risk tolerance levels is critical to the success of a security program. The most successful security pioneers will be able to align security strategies with business goals to ensure security investments and planning are enabling the company’s growth initiatives. Invest in scalable solutions: Invest in solutions that offer flexibility and can adapt to the changing needs of the organisation. Closed systems that can’t integrate fully with new technologies will severely limit the security team’s ability to seamlessly manage the security portfolio. Optimize processes: Reviewing security processes and workflows – or investing in a platform that can streamline this for you – can improve efficiency and effectiveness for your security team. Identifying opportunities for automation and standardisation can allow for scaling as business needs change. Collaborate across departments: Preparing for growth initiatives requires extensive communication across departments, including leadership teams, human resources, legal, IT, facilities, and many other stakeholders ensure that security priorities, challenges, and requirements are effectively communicated and integrated. Adopting these approaches helps put security teams in the driver’s seat, effectively managing periods of growth and change without compromising the safety and security of the organisation. Technology considerations As security pioneers navigate investments in new technologies that achieve some of the approaches listed above, such as aligning strategy with business goals, optimising processes, and cross-departmental collaboration, there are several considerations to make. Looking at how technology can support (or even hinder) future growth. For example, when making a buying decision around access control systems, security pioneers must consider the number of users, number of credentials, server requirements, facilities, hardware end points, and software features. As these items are being addressed in an RFP or in conversations with a vendor, security pioneers must ask themselves, “Is there a scenario where my program will outgrow the system’s capabilities in any of these areas?” If so, the answer might be to select a different solution. Security pioneers must consider interoperability. We talk a little about this above, but the importance here cannot be overstated: integration is key. The ability to leverage multiple point solutions, such as access control systems and video surveillance cameras – regardless of manufacturer – provides growing companies with the ability to scale quickly and more efficiently than ever before. Centralising the ability to pull these solutions into a single security operations management platform allows security pioneers a better view of their security programs in a current – and even future – state. Cloud-based solutions can provide the ultimate scalability factor, providing flexibility and accessibility advantages compared to traditional on-premise systems. Cloud-based, or Software-as-a-Service (SaaS) platforms, can easily scale up or down based on changing needs, accommodate distributed environments, and provide remote access and management capabilities, making them well-suited for scalable physical security deployments. Data-driven insights and analytics can drive decision-making beyond security, making technology investments that provide these critical. Automated workflows, event-triggered alerts, and AI-driven analytics can streamline security processes, improve threat detection capabilities, and reduce manual intervention, enabling security teams to manage larger environments more efficiently. Centralised management of technology investments can create cohesion for security teams. Centralised management and monitoring of physical security systems across multiple locations or facilities enables personnel to efficiently oversee and control security operations, access controls, and incident response activities. Being able to manage security in a single platform provides security pioneers with the ability to assess staffing levels, streamline training, allocate resources effectively, and scale to additional sites and/or solutions as needed. Tasked with building a security program that can adapt to the changing needs of the organisation, security pioneers must consider a number of factors when setting strategy. First and foremost, taking a close look at the existing program to identify strengths and weaknesses, then truly assessing the technology and processes in place, is the best way to move forward and future-proof the organisation.
The days of being reactive are over. That’s right, we as an industry, can no longer afford to be reactive. As threats evolve, the need for proactive security is critical. While traditional methods, including physical barriers and security personnel, are still necessary, the future of our approach is built on the backs of emerging technologies. Substantial vulnerabilities As an industry, we’ve operated reactively for decades, it has been common for security teams to address threats only after they occur. The growing risk landscape proves that this approach has significant limitations. Human oversight, delayed responses, and the inability to monitor large areas have exposed substantial vulnerabilities. Emergence of AI AI enables real-time monitoring, advanced data analysis, and more accurate risk detection Times are changing though and it’s largely due to the emergence of AI. AI is revolutionising the security landscape by making technology smarter. It enables real-time monitoring, advanced data analysis, and more accurate risk detection. This ensures a higher level of security and safety, minimising potential incidents' impact while enhancing overall safety. Focus on strategic aspects AI's ability to process vast amounts of data quickly and accurately is, quite frankly, a game-changer. It can identify patterns and anomalies that can provide stakeholders with critical insights to respond in a more prepared manner. By automating routine tasks and highlighting potential issues, AI also allows operators to focus on more complex and strategic aspects of security management, rather than responding to false alarms. The future is AI The future of security lies in AI. The Security Industry Association (SIA) has recognised AI as one of the top security megatrends in 2024. However, the challenge is not adopting AI, it is about effectively using it to enhance security. AI can enhance video surveillance by improving object detection and enabling real-time, informed responses AI systems can easily integrate with existing infrastructures, providing a layered defence that combines traditional methods with more modern technology. For example, AI can enhance video surveillance by improving object detection, reducing false alarms, and enabling real-time, informed responses. This ensures that security measures are adaptive, scalable, and capable of addressing the evolving risk landscape. Don’t react, anticipate One of AI's most significant benefits is its ability to provide proactive insights. AI can predict potential breaches by analysing behaviour patterns and detecting anomalies allowing security pioneers to do something before an event happens. This shift, from reactive to anticipatory measures, marks a significant advancement in asset protection and risk management. AI systems can also continuously analyse data and distinguish between everyday events and real-world threats. It’s AI's continuous learning capabilities that mean the systems can adapt and improve over time to become more accurate and efficient in threat detection and response. Save money, scale on demand Contrary to common belief, adopting AI technologies will not put a security department over budget. It may be surprising, but these solutions offer cost-effective and scalable alternatives to traditional security measures. An initial investment in AI technology can result in substantial long-term savings (and ROI) by reducing the need for physical infrastructure and on-site security personnel. Customisable solutions The ability to scale and customise AI solutions makes them an efficient choice for enhancing perimeter defence AI systems are also inherently scalable and can be tailored to meet the specific needs of different environments. This ensures the system can evolve with emerging threats and technological advancements without requiring a complete system overhaul. The ability to scale and customise AI solutions makes them a practical and efficient choice for enhancing perimeter defence. How’s that for staying within budget? Embrace the possibilities Integrating AI into perimeter security is the future of proactive and intelligent security. As these technologies continue to evolve, we can expect even more refined solutions that are predictive, autonomous, and capable of directly addressing new and emerging threats. We’re experiencing an exhilarating transformation as AI becomes more trusted, precise, and advanced on multiple levels. This evolution is bigger than pilots and small, low-profile deployments. AI in perimeter security For instance, France is preparing to deploy AI-powered video surveillance as it gears up to host the 2024 Olympics, part of its efforts to detect sudden crowd movements, abandoned objects, and suspicious activities. Think about the sheer scale of that project. We’re finally moving forward, and staying one step ahead must be our priority. But this shift requires a significant change in mindset. Are you ready to make the change?
Security beat
AI has the potential to enhance the usability of traditionally complex access control and physical security systems. The application of AI (artificial intelligence) within access control is still relatively new, but rapid advancements in generative AI are already transforming how security systems operate. acre security is driving the deployment of generative AI in access control through its acquisition of REKS earlier this year. REKS is a purpose-built generative AI solution designed specifically for acre’s access control platform. Unlike generic AI tools, REKS understands both system and security-specific terminology, allowing users to ask natural-language questions like, “Show me all access denied events at a specific location,” and receive instant results. AI workflows and AI agents “We're starting to see how AI workflows and AI agents, that leverage language models, can potentially be used in conjunction with access control to create new, automated processes around false alarm reduction, system configuration, report generation, data analysis, threat detection, and in-system customer support,” says Adam Groom, Director of Business Development, AI Development Team, acre security. “We expect AI-driven capabilities to evolve rapidly, but the full range of benefits will depend on continued development and real-world application,” he adds. Integrate AI-driven capabilities acre’s ability to integrate AI-driven capabilities across the company’s product portfolio positions The best way to think of REKS is as an acre access control expert you can talk to, says Groom. “As AI adoption grows in security, REKS will expand its capabilities, making access control more usable and more efficient.” Groom says acre’s ability to integrate AI-driven capabilities across the company’s product portfolio positions the company as a pioneer in next-generation physical security. “These features will add long-term value by enhancing usability and operational insights across various segments,” says Groom. “Work is already under way to incorporate REKS into acre access control, and we’ll evaluate other integration opportunities in the future.” REKS' AI capabilities According to acre, REKS simplifies daily operations, automating routine tasks, and delivering real-time, actionable intelligence. With REKS' AI capabilities, users can interact with the system to retrieve more detailed insights and actionable information from their acre access control system. “This eliminates the need for complex reports, navigating drop-down menus, or manually reviewing logs,” says Groom. “It significantly enhances efficiency and usability for security professionals.” Enhancing productivity and customer satisfaction Key concern is ensuring that system configuration, enactment, and servicing remain within their scope For integrators, the key concern is ensuring that system configuration, implementation, and servicing remain within their scope of expertise. With REKS, that doesn’t change — but the process becomes significantly faster and more efficient. Instead of manually configuring every panel, input, and output — a traditionally time-consuming task — REKS enables integrators to use natural language commands to streamline setup and adjustments, says Groom. This eliminates tedious steps and dramatically improves operational efficiency, allowing integrators to deploy and fine-tune systems with greater speed and accuracy, ultimately enhancing both productivity and customer satisfaction, he adds. Cloud-enabled ecosystems “We are committed to helping organisations modernise their security infrastructure by transitioning from legacy systems to cloud-enabled ecosystems at their own pace — ensuring minimal disruption while maximising value,” says Groom. “By integrating AI-driven capabilities, we enhance usability and deliver deeper operational insights across all segments.” “Security’s future isn’t about forcing change — it’s about empowering choice,” adds Groom. “Whether staying on-prem, migrating to the cloud, or adopting a hybrid model, we plan to provide a seamless, zero-disruption transition, prioritising interoperability, automation, and security at every stage.” Generic AI tools AI must be purpose-built for security applications because security demands precision, reliability, and context-aware decision-making, which only focused AI offerings like REKS bring to the table, says Groom. In contrast, generic AI tools, like ChatGPT, are designed to perform a wide variety of tasks, like how humans can learn and do many different things. Instead, purpose-built AI is built to do just one specific function. “REKS adds specially designed artificial intelligence to our access control solutions to enhance both intelligence gathering and the user experience,” says Groom. New applications in access control The integration of generative AI into acre's access control platforms and their broader portfolio A new AI development team will lead AI initiatives at acre, driving the integration of generative AI into acre's access control platforms and their broader portfolio. This team will seek to push boundaries in applying AI to new applications in access control, intrusion detection, and beyond, empowering security professionals to interact with their systems in a smarter, more intuitive way. But don’t worry, AI will not take the human element out of security entirely. AI human capabilities “The reality is that AI will improve upon human capabilities because it is a versatile tool that supports and strengthens security operations, not a replacement for human decision-making,” comments Groom. “It helps operators process large amounts of data quickly and detect patterns that might be missed otherwise.” Rather than removing the human element, AI allows security teams to work more efficiently by automating repetitive tasks and providing actionable data, enabling professionals to focus on critical responsibilities. {##Poll1743085396 - What is the biggest challenge you face with your current access control system?##}
The practice of executive protection changed forever on Dec. 4, 2024, when UnitedHealthcare CEO Brian Thompson was shot outside a Manhattan, New York, hotel. The shocking event raised awareness in board rooms around the world about the need for, and challenges of, executive protection. Questions followed immediately, including why was the high-level executive not protected? Combination of risk and reward UnitedHealthcare’s stock price has gone down more than 20% since the shooting The event also highlighted what is at stake for companies, extending beyond the safety of executives and impacting many factors, even including a company’s stock price. UnitedHealthcare’s stock price has gone down more than 20% since the shooting, equating to tens of billions of dollars. “Companies are considering the combination of risk and reward like never before when it comes to executive protection,” says Glen Kucera, President of Allied Universal Enhanced Protection Services. “What are the chances this could happen? Before Dec. 4 many thought it was zero. And what are the financial implications for a company if it happens? Executive protection is a small investment to protect against a worst-case scenario.” Evaluation of an executive protection Before the UnitedHealthcare shooting raised awareness, fewer than 50% of executives had protection. But concerns that previously fell on deaf ears now have the full attention of companies, says Kucera. “Boards of directors are having to figure this out,” he adds. “They may not have executive protection, but now they have to do it.” A threat assessment, conducted by a company such as Allied Universal, provides an independent evaluation of a company’s executive protection needs. The assessment evaluates factors such as an executive’s travel habits, the safety of their home, etc. Does the executive need protection 24/7, or just when they travel into more dangerous areas? Risks increase related to corporate earnings Sometimes, cases increase the need for executive protection, such as an internal threat In assessing threats, security professionals also look beyond the individual to consider the safety of a corporate facility, for example. “Is there a visual deterrent, controlling who comes and goes?” asks Kucera. “If there is good security, it all ties together. We do home assessment, facility assessment, route assessment, and travel assessment as needed.” Sometimes, circumstances increase the need for executive protection, such as an internal threat. Timing is a factor, and risks increase related to corporate earnings releases, new product announcements, and corporate layoffs or consolidation. Monitoring social media tracks shifting threats that impact the need for executive protection. UnitedHealthcare shooting “He didn’t have it and probably didn’t think he needed it,” comments Kucera about the UnitedHealthcare executive who was gunned down in the streets of New York City. “He was staying at the hotel across the street and was used to walking down the street every day.” “Sometimes executives want to preserve their privacy and be able to walk down the street,” says Kucera. “Getting protection can be seen as a sign of weakness. Some CEOs in the past have said they just didn’t want it.” However, the UnitedHealthcare shooting raised the stakes of the need for more vigilance. “The bottom line is you have to yet beyond objections and make the investment to protect against a worst-case scenario,” says Kucera. Anti-capitalist sentiment in the general population An internal police bulletin warned of an online hit list naming eight executives and their salaries Threats to executives sometimes arise from anti-capitalist sentiment in the general population about perceived inequalities in wealth and power. Executives provide symbolic targets for anyone who fights the system, and social media has amplified the voices of those who oppose capitalism. For example, a "Most Wanted CEO” card deck seeks to shine a spotlight on "titans of greed." Also, in the aftermath of the UnitedHealthcare shooting, CEO "wanted" posters appeared across New York City, threatening various executives of large companies. An internal police bulletin warned of an online hit list naming eight executives and their salaries. Careful monitoring of social media posts Careful monitoring of social media posts and other sources enables executive protection professionals to analyse data and separate the dangerous threats from the merely negative ones. Sadly, positive support of the UnitedHealthcare shooting was expressed by the 300,000 or so followers of the shooter, who became a celebrity of sorts. A huge outcry of negative sentiment toward the insurance industry led to fear that copycat incidents might occur. “There has been an unprecedented amount of positive support for committing murder,” commented Kucera. Executive protection requests HR executives can be at risk, especially at a time of layoffs or consolidation “Let’s face it, there has been a lot of controversy, from COVID to the Middle East crisis, to the political campaign, and there is negativity on both sides,” says Kucera. “People have opportunities to pick sides, and there is a lot of sentiment going both ways, and there is a small percentage of people who will act aggressively.” Executive protection requests now extend beyond the CEO to include others in the management ranks of companies. Basically, any public-facing executive is at risk, including anyone who makes statements to the press. Human resource (HR) executives can be at risk, especially at a time of layoffs or consolidation. Private information on the Internet Typically, an executive is assigned a single armed operative for protection. The firearm serves primarily as a visual deterrent that hopefully makes a potential perpetrator think twice. “When they plan an event like this, their expectation is that it will be a soft target,” says Kucera. “If there is an officer, it gives them pause.” Controversial or high-profile CEOs are typically protected 24/7, including when they travel with their family. Adding risks is the fact that private information is now posted on the Internet, including where an executive lives and where their children go to school. Internet monitoring Internet monitoring also includes the “dark web,” which includes sometimes dangerous information “We offer social media monitoring, and we advise them to be more careful with what they post,” says Kucera. “We monitor reactions to posts including any that might be threatening. We watch social media carefully if a company announces earnings or a change in their service or product offering.” Internet monitoring also includes the “dark web,” which includes sometimes dangerous information that is intentionally hidden and requires specific software, configurations, or authorisation to access. Own layer of protection Public and government officials can also come under fire in a variety of scenarios. FEMA officials faced threats after the recent floods in the Southeast, for example, among other situations where perceived unfair treatment promotes thoughts of retribution. Although government agencies have their own layer of protection, there are instances when they call on companies such as Allied Universal for additional help. Ad hoc protection for various executives In the aftermath of the UnitedHealthcare shooting, calls to Allied Universal’s Command Centre increased by 600%, reflecting requests for ad hoc protection for various executives. These requests are in addition to the company’s business providing “embedded” operatives that travel with executives all or some of the time. On that side of the business, requests for services are up probably 300%, says Kucera. {##Poll1742194323 - Has the recent increase in violent threats changed your company's view on executive protection?##}
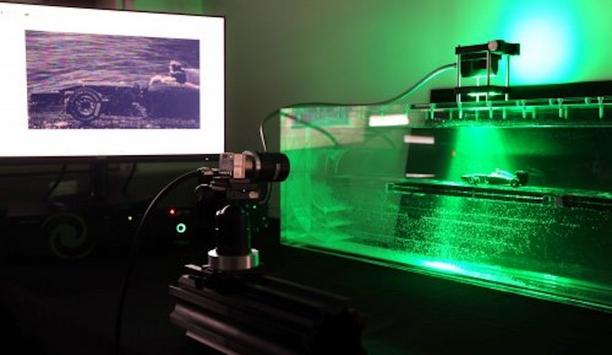
Casinos face multiple security issues caused by potential bad actors, everything from cheating to vandalism, from theft to vagrancy. A new intelligent technology can monitor for specific keywords and behaviours. The technology scans the entire casino premises constantly for potential threats and notifies key personnel when they happen. Casinos are among the environments deploying the OpticSense system by Huvr Inc., which uses special fibre optic technology called an interferometer to secure large areas. Imagine a very sensitive loop made of fibre-optic cables placed around the perimeter of a facility. System’s artificial intelligence Basically, it converts the entire facility into a highly sensitive microphone, detecting any slight disturbances, such as an unusual movement or sound. When the system senses something out of the ordinary, it immediately triggers cameras to look at the disturbance and record a short video. The system’s artificial intelligence (AI) then analyses both the sound and video to determine what's happening. It compiles a detailed report and immediately sends the information to security teams. OpticSense OpticSense can hear, see, and analyse potential threats automatically before they get out of control. “This makes it possible for fewer people to do more,” says Herman C. DeBoard III, CEO and Founder of Huvr Inc, adding “When you don’t need as many personnel to monitor video feeds and analyse data, you can drastically reduce your labour costs. Best of all, when you optimise your resource allocation, your security teams can respond more effectively to each threat.” The system’s AI analyses sound and video to define what's happening. Combining fibre optics and AI Huvr was originally designed as a platform to provide immersive virtual travel experiences Huvr was originally designed as a platform to provide immersive virtual travel experiences. However, with the acquisition of OpticSense and Grip Places, the company pivoted to integrate advanced fibre-optic technology and AI-driven analytics into a comprehensive security system. The system’s artificial intelligence and fibre-optic interferometer technology work together to detect and analyse real-time threats. When the Fibre Optic Ring Interferometer (FoRi) detects even minute audio abnormalities, it triggers AI analysis. In split seconds, the AI directs cameras to record 60 seconds of video, compiles a detailed report, and then texts the real-time intelligence to security teams and authorities. Intelligent security solutions The growing need for intelligent security solutions can help to drive Huvr's entry into the security marketplace. Advanced technology enables the company to meet the increasing concerns surrounding public safety and the growing need for real-time threat analysis. The AI system classifies each detected anomaly according to its severity and stores data from various incidents to improve its risk assessment abilities over time. This continuous learning enables the AI to become more adept at accurately identifying and responding to threats specific to the casino environment. AI system classifies each detected anomaly according to its severity. Simple and discreet installation The system involves installing fibre optic cables around the casino’s perimeter The system involves installing fibre optic cables around the casino’s perimeter. It’s a simple job that typically requires less than a day. “These cables allow the casino to establish a smart perimeter detection system without significant infrastructure alterations,” says DeBoard Casinos typically employ upwards of 6,000 cameras, but human security teams cannot feasibly monitor all the incoming data at once. Huvr's OpticSense product becomes like the brain of the casino, constantly monitoring disturbances and responding in real time. Huvr’s fibre optic cables Huvr’s advanced detection algorithms work in tandem with a casino’s existing camera infrastructure, simply adding a layer of security that converts traditional security measures into an intelligent system that continuously monitors and analyses video footage. With Huvr’s fibre optic cables easily hidden or buried and the server roughly the size of a shoe box, the system is designed to be extremely discreet. It can be operated by a single person using a small handheld device. The security system is simple to scale and manage without disrupting casino operations. Security system is simple to work without disrupting casino operations. Autonomy boosts productivity Huvr automates surveillance and anomaly detection to decrease the load on security teams Autonomy is an important aspect of this new technology. Traditional security systems have required constant human monitoring, but Huvr automates surveillance and anomaly detection to decrease the load on security teams. “Without any human direction, Huvr detects minute disturbances, triggering the AI system to direct cameras and analyse video footage instantaneously,” says DeBoard. He adds, “The intelligent system rapidly monitors every anomaly and accurately decides which present potential threats. When it detects an issue, it compiles a detailed report that includes the number of individuals involved, their appearances, direction of movement, and licence plates. It takes only seconds to text this report to security teams and authorities.” Applications beyond casinos Beyond casinos, Huvr already provides proactive security in a wide variety of settings. In banks, the system monitors parking lots and ATM machines for suspicious activity. In large stadiums, it proactively detects target words such as “help” or “gun.” In schools, Huvr’s fibre optic ring interferometer secures campuses against unauthorised intrusions. In hospitals, it alerts medical staff when patients need immediate care. In airport terminals, it monitors for suspicious behaviour. In restaurants or construction sites, the system learns to monitor for safety violations and health hazards. Smart perimeters around critical infrastructure The fibre optic cables also form smart perimeters around critical infrastructure like power grids, cell towers, and bridges to watch for physical disturbances or tampering. “Because the system can be customised to each new environment and can learn quickly, the applications are virtually limitless,” says DeBoard. {##Poll1728555696 - Do you believe AI-driven perimeter detection systems will significantly reduce security labour costs?##}
Case studies
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over a two-year period by specialist security installer, Scottish Communications Group. HID Mobile Access licences University has purchased 10,000 HID Mobile Access licences to offer its academic community In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. “We wanted a modern system which is safe, secure and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. HID solution: future-proof equipment Stebbing added: “Complying with forthcoming legislation was also another important project requirement. With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we have a duty to protect to ensure everyone is safe." "The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” Ambitious development plans University of Dundee is a research institute in Scotland, noted for its academic merit in dentistry The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering and life sciences. Based in the heart of the city, it is home to over 16,000 students, 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. New HID Signo readers The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP (Open Supervised Device Protocol) and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers, thereby speeding up the rollout. RFID cards access buildings The university used to print and issue plastic RFID cards so staff and students could access buildings Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week, when some 2,500 – 3,000 undergraduate and postgraduate students enrol. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Origo management software Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, validating or revoking of IDs – all of which is now done virtually and remotely. Improve the mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Integrate with digital campus cards While the strategy and aspiration are for the university population to shift wholesale to mobile access While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach now is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO range of ID card printers Given that RFID cards are still required now, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. HID’s reputation University of Dundee utilises its FARGO DTC4500e printers to back up this shift to digital change “HID Signo readers are going in now across the main buildings, including the new Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications and authentication standards. Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” MOTORTRBO Ion smart radios In addition, Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems and CriticalArc Safezone® App, security staff need carry only a single device to fulfil their duties.
Thames Valley Police worked with local authorities to improve CCTV coverage, cut costs, and boost efficiency. It’s made public spaces safer and ensured long-term, reliable monitoring across the region. Thames Valley Police is the largest non-metropolitan police force in England and Wales, covering 2,218 square miles and a population of 2.42 million people. Its jurisdiction includes multiple towns, city centres and council areas across the three counties of Berkshire, Buckinghamshire and Oxfordshire. Setting a long-term vision for public space CCTV Public space CCTV is vital in deterring and detecting crime across the Thames Valley Public space CCTV is vital in deterring and detecting crime across the Thames Valley. However, significant pressure on local authority budgets has made it increasingly difficult for councils to provide public space CCTV. There was real jeopardy that financial constraints would result in unmaintained systems, with limited or no real-time monitoring. A fresh approach was needed, so the Thames Valley CCTV partnership between Genetec™ and Hanwha Vision was formed. The first major challenge was securing funding to overhaul several local authorities’ ageing systems, which were proving increasingly expensive to upgrade and maintain. The second was to manage the ongoing costs of staffing control rooms to ensure the long-term sustainability of monitored CCTV across the Thames Valley. Ownership and monitoring of public space CCTV Ambitious plans were devised to pool resources and replace many disparate systems with one police-owned system that could extend across multiple authorities. In effect, the aim was to transfer the ownership and monitoring of public space CCTV from local authorities to dedicated Thames Valley Police control rooms. It would be led by the Thames Valley Police & Crime Commissioner (PCC) Matthew Barber, collaborating with any local authority who chose to participate. It was a feat that had never been attempted in the UK on this scale that held the potential to drive efficiencies and enhance CCTV provision in areas it might otherwise have deteriorated. Ongoing commitment and investment “CCTV is an important part of community safety; benefitting police and local communities in helping to deter crime and antisocial behaviour, identify offenders and support prosecutions." "Ongoing commitment and investment enables high quality, consistent and sustainable CCTV provision now and into the future”, explains Matthew Barber, PCC, Thames Valley. Centralisation creates area-wide visibility and control Several control rooms in the Thames Valley, like Windsor & Maidenhead, had implemented Genetec Security Centre Several control rooms in the Thames Valley, such as Windsor & Maidenhead, had already implemented Genetec Security Centre and were very happy with its operation. Furthermore, as an open platform video management system, it could minimise costs by supporting a phased unification or “takeover” of existing systems across the Thames Valley. Finally, its hybrid cloud architecture provided Thames Valley with maximal flexibility to leverage any combination of cloud or on-premises infrastructure according to Name Thames Valley Police Industries Public Safety Location Thames Valley, United Kingdom Products Genetec Security Centre; Genetec Cloud Services; Federation Technology Partners Hanwha Vision Channel Partners CDS Systems what made sense for each application and location. This made it the obvious choice on which to standardise. Range of multidirectional AI-enabled cameras Following a competitive tender, Thames Valley chose CDS Systems to implement its proposed solution. This would be built on Genetec Security Centre and incorporate a range of multidirectional AI-enabled cameras from Hanwha Vision. A key driver in the decision was the high levels of commitment shown by all three parties to cybersecurity. Another was the recognition that the system design and technology selection could ensure a cost-effective implementation that could continue to evolve in line with the needs of its users. Integration between Genetec and Hanwha Vision technology Legacy cameras were retained and reused to maximise the return on existing investment wherever possible “We urgently needed to improve the quality of CCTV, enhance collaboration, and drive efficiencies for all partners. The respective capabilities and seamless integration between Genetec and Hanwha Vision technology was the optimal way of meeting Thames Valley’s requirements,” says Sam Thomas, CDS Systems. Phase one of the deployment involved CDS taking over an existing control room in Milton Keynes, replacing the legacy analogue infrastructure with a modern IP backbone. It then installed Genetec Security Centre to establish one platform through which officers could smartly interact with all incoming video feeds. Legacy cameras were retained and reused to maximise the return on existing investment wherever possible. A second Genetec workstation was also set up inside Slough Police Station, allowing officers to rapidly review footage for improved community response. Hanwha Vision’s AI-enabled multidirectional cameras CDS then introduced Hanwha Vision’s AI-enabled multidirectional 4k cameras to improve CCTV coverage and quality in public spaces. Each of these cameras incorporates up to five cameras in one device for wide-area surveillance, which would previously have required several separate devices, simplifying installation and resulting in significantly less associated cabling and infrastructure. They also provide powerful AI analytics, including accurate object detection and classification, to enable forensic search and save operators' time when responding to incidents. For example, identifying and establishing the movement of specific people or vehicles based on attributes such as vehicle type. Thames Valley CCTV partnership Phase two will see four additional control rooms in Oxfordshire merged into a single hub Phase two will see four additional control rooms in Oxfordshire merged into a single hub inside Abingdon Police station, also built on the Genetec Security Centre. This and the control room in Milton Keynes will be interlinked, adding further resilience as each site will be able to act as a fallback for the other. At this point, there will be a dedicated team of eighteen staff responsible for monitoring CCTV and enhancing CCTV for all participating communities in the Thames Valley CCTV Partnership. Innovative and cost-effective solutions “The CCTV Command Suite enabled by CDS, Genetec and Hanwha Vision has improved our workflows beyond recognition, enabling staff to quickly review and package evidence for frontline officers or more complex investigations. It has received several plaudits from officers for its ease of use,” says Jason Owen, CCTV Operations Manager, Thames Valley Police. “This collaboration between Thames Valley Police, Genetec, CDS Systems, and Hanwha Vision showcases the power of partnership in driving innovative, cost-effective solutions that improve public safety,” says John Boorman, Head of Product and Marketing at Hanwha Vision Europe. “Our AI-enabled cameras are designed to reduce false alarms and streamline operations, ensuring teams can focus on real incidents and drive efficiency across their monitoring.” Efficiency, at a lower cost All CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers Pooling resources and transferring ownership to the police has brought about significant cost efficiencies for participating authorities, while also enhancing the quality and reliability of public spaces CCTV. Just as importantly, it has dramatically improved the police’s direct access to quality video evidence. Unlike in a traditional council-run control room, all CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers. This means they have full access to Thames Valley’s suite of police databases and reporting software packages. They are better equipped to rapidly report incidents, support front-line officers, and communicate effectively with investigators as a result. On average, it handles between 300 – 500 incidents a month and has substantially increased the number of successful requests for supporting footage. “We’ve immediately seen the benefit of our investment in equipment and CCTV operators, with the police now much better equipped to deter and detect crime across the Thames Valley,” adds Barber. A solid platform for further improvements Control room operators’ intuition will always be the driving force that brings results Looking forward, Thames Valley has plans to use the Genetec platform to connect its people and mobile surveillance assets back to its control rooms for better cross-force interaction. Genetec Federation as a Service is already allowing live and recorded video to be shared with officers in the field. Soon it will also be extended to ensure video from police CCTV vans and drones is immediately available in the control room. In both cases this is achieved without complex network configuration, requiring only an internet connection. It is also at the beginning of its journey of fully realising the value of the AI-equipped Hanwha Vision cameras specified by CDS. Control room operators’ intuition will always be the driving force that brings results, but AI is freeing them up to do what they do best by saving time on routine monitoring and searches. Cost savings, resilience, and efficiencies Finally, talks continue that would see the addition of further control rooms across the Thames Valley to the Thames Valley CCTV Partnership. Having proven the model, would allow it to scale operations further to deliver even greater cost savings, resilience, and efficiencies. “We’re proud of what we’ve achieved to date but have no intention of resting on our laurels. The foundations we’ve established will ensure continued high-quality, consistent, and sustainable CCTV provision for our communities,” concludes Owen.
Modern measurement technologies enable high-precision detection of the movement of liquids and gases - and thus provide valuable data for numerous applications. How does the air flow around an aeroplane? How does the blood move through our veins? And how can pollutant emissions in combustion processes be minimised? For this purpose, speed, direction, pressure and turbulence within a flow are analysed in order to increase efficiency, ensure safety and drive innovation in a wide variety of areas. Innovative sensor technology High-resolution cameras are used to track marked particles within a flow and analyse their movement A range of methods are available to measure these flows, including visual ones such as particle image velocimetry (PIV). High-resolution cameras are used to track marked particles within a flow and analyse their movement. iLA_5150 GmbH from Aachen (Germany) now also relies on EBIV. The abbreviation stands for Event-Based Particle Image Velocimetry and is a new optical method for the qualitative and quantitative visualisation of flows and flow velocities. It combines PIV with event-based cameras, here with a uEye EVS from IDS Imaging Development Systems GmbH. The innovative sensor technology of the industrial camera enables highly dynamic and energy-efficient detection, especially of fast and turbulent movements. Application In the EBIV method, tiny particles are added to a flowing fluid and illuminated in a plane, the so-called light section plane. They generate individual light pulses as they enter and exit the LED light section. This change in local brightness is recorded independently by the camera pixels and transmitted to the PC as a data stream of "change events". In contrast to conventional cameras, event-based models therefore only react to the changes in brightness registered in the image field. Stationary scattered light, such as background or a non-changing illuminated surface, does not generate a measurement signal. This reduces the amount of data considerably. Frame rates of up to 10,000 frames per second The data stream essentially contains information about what happens, when and where The data stream essentially contains information about what happens, when and where. In detail, these are the pixel coordinates on the sensor, microsecond time stamps of the pixel events and the information about the events: ON or OFF. This allows a distinction to be made between increasing intensity (ON event) and decreasing intensity (OFF event). Using suitable software, the stream can be converted into an image matrix in which both the spatial information and the linear time base of the stream are available. The result is comparable to the extremely high frame rate of a high-speed camera. EBIV measurement method "The EBIV measurement method differs fundamentally from conventional imaging methods. They usually generate very large amounts of data and require powerful peripherals that can process them. For exceptional frame rates of 1000 Hertz and more, the image-based cameras required are themselves very complex and expensive." "With the help of event-based camera technology, comparable frame rates of 10,000 frames per second are possible, whereby only standard PC interfaces such as USB with a few gigabits per second are required. The price of the event-based models themselves is significantly lower than that of corresponding high-speed cameras and is therefore also very interesting for smaller teaching and research institutions," explains Dr André Brunn - Head of Development at iLA_5150 GmbH. Further processing The user can optimise the display of the move paths and adapt them to unique study objectives The data stream is converted into image data and displayed in a front end - the so-called EBIV viewer - for direct online flow visualisation. The user can also select the integration time, which corresponds to the exposure time of an image camera, as well as the time increments of the sequence, i.e., the period between two consecutive shots. Classic image filters can also be used. With the help of these settings, the user can optimise the display of the movement paths and adapt them to individual examination objectives. Both fine flow details and large-scale patterns can be made more clearly recognisable. This ability to readjust the measurement results is another advantage of the event-based approach. Numerical analysis of the flow properties In the qualitative visualisation of the flow in the EBIV-View, particles are continuously illuminated so that they are visible as luminous traces. The method is therefore very well suited to visualising the flow. However, it does not provide exact measurements of its speed or direction. For a precise, numerical analysis of the flow properties, individual particles are illuminated for a moment using short, time-defined light pulses. Image sequences of the event-based camera As with classic PIV, the image sequences of the event-based camera can also be statistically analysed This allows their exact position to be recorded and their movement quantified. By comparing the particle positions in successive images, the speed and direction of the flow can be precisely calculated using PIV, for example. The result is a transient 2D vector field that changes over time - in other words, the vectors do not remain constant. As with classic PIV, the image sequences of the event-based camera can also be statistically analysed, for example, to determine mean values and fluctuations in the flow velocity. Camera and software On the camera side, iLA relies on a uEye XCP-E from IDS. The small, lightweight industrial camera offers event-based sensor technology in a robust die-cast zinc housing (29 × 29 × 17 mm) with screw-on USB Micro-B connection. It is compatible with all standard C-mount lens sizes. This makes it ideal for both industrial and non-industrial areas. The integrated event-based vision sensor (EVS) was developed by Sony and Prophesee. It is supported by the Metavision SDK, a seamlessly integrated suite of software tools and models, APIs and other training and development resources from Prophesee for efficient analysis, visualisation and customisation. Building on this, the EBIV viewer from iLA_5150/PIVTec is specially tailored to flow visualisation applications. Outlook The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions. A qualitative flow visualisation is often sufficient to understand effects and develop suitable control mechanisms. Until now, however, imaging fast flows with high temporal resolution was usually only possible with expensive high-speed cameras. Event-based camera technology offers a cost-effective alternative that requires significantly less technical effort. These “simple” methods have been lacking in teaching and research in particular. Thanks to the extreme data reduction, this technology also allows the use of several cameras or large camera arrays without the periphery becoming a limitation for data transfer. The compact design of the uEye EVS models also makes them ideal for mobile applications. This means that real application environments can be analysed directly for the first time - without having to rely on artificial flow models or channels. Established flow measurement methods Event-based cameras enable efficient, cost-effective and high-resolution visualisation and quantification of flows. Due to the small amounts of data generated, many processes can be analysed almost in real time, which also makes them interesting for use in fully automated systems. Established flow measurement methods such as Particle Image Velocimetry (PIV) can be seamlessly integrated and expanded. The technology can be used wherever flow information is captured by changes in scattered light intensity - be it from moving particles or vibrating surfaces.
ZeroEyes, the creators of the first AI-based gun detection video analytics platform to earn the US Department of Homeland Security SAFETY Act Designation, announced that its proactive gun detection and intelligent situational awareness solution has been deployed at Scott County R-IV School District in Benton, Missouri, to mitigate gun-related violence. The deployment was facilitated by Freedom Security, a local security provider serving the greater Missouri Area. Robust security upgrades Located in a rural community near the borders of Illinois and Kentucky, Scott County R-IV School District consists of a single campus with three interconnected buildings serving students from pre-K through 12th grade. The district educates approximately 800 students annually and employs around 125 teachers and administrators. ZeroEyes is the newest addition to the district's robust security upgrades, which include window tints, HAVEN locks, integrations with CrisisGo, and more. Digital security cameras ZeroEyes’ AI gun detection and intelligent situational awareness software layer onto existing cameras ZeroEyes’ AI gun detection and intelligent situational awareness software layer onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to local law enforcement and school administration as quickly as 3 to 5 seconds from detection. ZeroEyes safety strategy “ZeroEyes is not intrusive or invasive, and it does more than just detect; it alerts, responds, and continues to do so throughout any situation involving a potential threat,” said Dr. Bradley Kolwyck, Superintendent of Scott County R-IV School District. “This technology is the final piece we needed to ensure every layer of our safety strategy is connected, enabling us to provide the safest environment possible.” ZeroEyes deployment ZeroEyes and the district are hosting a Lunch & Learn session at 11:00 am at the Scott County ZeroEyes and the district are hosting a Lunch & Learn session at 11:00 am at the Scott County R-IV District Office (4035 State Highway 77, Benton, MO). It will feature demonstrations and discussion sessions, including reflections from school pioneers on the district’s successful ZeroEyes deployment. The event is open to local schools, law enforcement, and media. ZeroEyes’ innovation and protection “I commend Scott County R-IV School District for taking the initiative to lean into innovation and proactively protect its students from gun-related violence,” said Mike Lahiff, CEO and cofounder of ZeroEyes. “ZeroEyes’ ability to provide first responders and law enforcement with advance warning and situational awareness empowers them to act quickly and save lives.”
ZeroEyes, the creators of the first AI-based gun detection video analytics platform to earn the full US Department of Homeland Security SAFETY Act Designation, announced that its technology has been deployed at East Hill Synagogue in Englewood, New Jersey, to proactively address gun-related threats. East Hill Synagogue is a 20+ year-old house of worship serving a diverse community of Modern Orthodox Jews, offering Shabbat and holiday prayer services, adult education and family activities. Proactive security measures ZeroEyes is one of multiple solutions in East Hill’s multi-layered security approach ZeroEyes is one of multiple solutions in East Hill’s multi-layered security approach, enabling members to participate in religious activities without fear or distraction. Anti-Semitic attacks have reached new levels in the past 18 months, with the Anti-Defamation League reporting that the U.S. has seen a 200% increase in hate crimes. This concerning fact highlights the need for increased proactive security measures to protect congregants during worship services and other events. Overall security initiative “Jewish law dictates that preserving (saving) life is a top priority, and we take that quite literally at East Hill Synagogue; safety is our top priority,” said Jonathan Blinken, Directory of Security, East Hill Synagogue. “ZeroEyes is one of the most important layers that we have in our overall security initiative. It is an extremely powerful tool to help us protect those that we love, our institutions and everyone that comes to visit them.” Digital security cameras ZeroEyes' AI gun detection and awareness software layers onto existing digital security cameras ZeroEyes' AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to local law enforcement and synagogue staff as quickly as 3 to 5 seconds from detection. ZeroEyes to safeguard from gun-related threats "Every individual has the right to safety in their place of worship, and it’s deeply troubling when violence threatens that sense of peace," said Mike Lahiff, CEO and co-founder of ZeroEyes. "We thank East Hill Synagogue for trusting ZeroEyes to safeguard their congregation from gun-related threats, ensuring their community remains secure and welcoming."
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over a two-year period by specialist security installer, Scottish Communications Group. HID Mobile Access licences University has purchased 10,000 HID Mobile Access licences to offer its academic community In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. “We wanted a modern system which is safe, secure and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. HID solution: future-proof equipment Stebbing added: “Complying with forthcoming legislation was also another important project requirement. With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we have a duty to protect to ensure everyone is safe." "The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” Ambitious development plans University of Dundee is a research institute in Scotland, noted for its academic merit in dentistry The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering and life sciences. Based in the heart of the city, it is home to over 16,000 students, 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. New HID Signo readers The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP (Open Supervised Device Protocol) and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers, thereby speeding up the rollout. RFID cards access buildings The university used to print and issue plastic RFID cards so staff and students could access buildings Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week, when some 2,500 – 3,000 undergraduate and postgraduate students enrol. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Origo management software Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, validating or revoking of IDs – all of which is now done virtually and remotely. Improve the mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Integrate with digital campus cards While the strategy and aspiration are for the university population to shift wholesale to mobile access While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach now is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO range of ID card printers Given that RFID cards are still required now, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. HID’s reputation University of Dundee utilises its FARGO DTC4500e printers to back up this shift to digital change “HID Signo readers are going in now across the main buildings, including the new Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications and authentication standards. Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” MOTORTRBO Ion smart radios In addition, Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems and CriticalArc Safezone® App, security staff need carry only a single device to fulfil their duties.
Thames Valley Police worked with local authorities to improve CCTV coverage, cut costs, and boost efficiency. It’s made public spaces safer and ensured long-term, reliable monitoring across the region. Thames Valley Police is the largest non-metropolitan police force in England and Wales, covering 2,218 square miles and a population of 2.42 million people. Its jurisdiction includes multiple towns, city centres and council areas across the three counties of Berkshire, Buckinghamshire and Oxfordshire. Setting a long-term vision for public space CCTV Public space CCTV is vital in deterring and detecting crime across the Thames Valley Public space CCTV is vital in deterring and detecting crime across the Thames Valley. However, significant pressure on local authority budgets has made it increasingly difficult for councils to provide public space CCTV. There was real jeopardy that financial constraints would result in unmaintained systems, with limited or no real-time monitoring. A fresh approach was needed, so the Thames Valley CCTV partnership between Genetec™ and Hanwha Vision was formed. The first major challenge was securing funding to overhaul several local authorities’ ageing systems, which were proving increasingly expensive to upgrade and maintain. The second was to manage the ongoing costs of staffing control rooms to ensure the long-term sustainability of monitored CCTV across the Thames Valley. Ownership and monitoring of public space CCTV Ambitious plans were devised to pool resources and replace many disparate systems with one police-owned system that could extend across multiple authorities. In effect, the aim was to transfer the ownership and monitoring of public space CCTV from local authorities to dedicated Thames Valley Police control rooms. It would be led by the Thames Valley Police & Crime Commissioner (PCC) Matthew Barber, collaborating with any local authority who chose to participate. It was a feat that had never been attempted in the UK on this scale that held the potential to drive efficiencies and enhance CCTV provision in areas it might otherwise have deteriorated. Ongoing commitment and investment “CCTV is an important part of community safety; benefitting police and local communities in helping to deter crime and antisocial behaviour, identify offenders and support prosecutions." "Ongoing commitment and investment enables high quality, consistent and sustainable CCTV provision now and into the future”, explains Matthew Barber, PCC, Thames Valley. Centralisation creates area-wide visibility and control Several control rooms in the Thames Valley, like Windsor & Maidenhead, had implemented Genetec Security Centre Several control rooms in the Thames Valley, such as Windsor & Maidenhead, had already implemented Genetec Security Centre and were very happy with its operation. Furthermore, as an open platform video management system, it could minimise costs by supporting a phased unification or “takeover” of existing systems across the Thames Valley. Finally, its hybrid cloud architecture provided Thames Valley with maximal flexibility to leverage any combination of cloud or on-premises infrastructure according to Name Thames Valley Police Industries Public Safety Location Thames Valley, United Kingdom Products Genetec Security Centre; Genetec Cloud Services; Federation Technology Partners Hanwha Vision Channel Partners CDS Systems what made sense for each application and location. This made it the obvious choice on which to standardise. Range of multidirectional AI-enabled cameras Following a competitive tender, Thames Valley chose CDS Systems to implement its proposed solution. This would be built on Genetec Security Centre and incorporate a range of multidirectional AI-enabled cameras from Hanwha Vision. A key driver in the decision was the high levels of commitment shown by all three parties to cybersecurity. Another was the recognition that the system design and technology selection could ensure a cost-effective implementation that could continue to evolve in line with the needs of its users. Integration between Genetec and Hanwha Vision technology Legacy cameras were retained and reused to maximise the return on existing investment wherever possible “We urgently needed to improve the quality of CCTV, enhance collaboration, and drive efficiencies for all partners. The respective capabilities and seamless integration between Genetec and Hanwha Vision technology was the optimal way of meeting Thames Valley’s requirements,” says Sam Thomas, CDS Systems. Phase one of the deployment involved CDS taking over an existing control room in Milton Keynes, replacing the legacy analogue infrastructure with a modern IP backbone. It then installed Genetec Security Centre to establish one platform through which officers could smartly interact with all incoming video feeds. Legacy cameras were retained and reused to maximise the return on existing investment wherever possible. A second Genetec workstation was also set up inside Slough Police Station, allowing officers to rapidly review footage for improved community response. Hanwha Vision’s AI-enabled multidirectional cameras CDS then introduced Hanwha Vision’s AI-enabled multidirectional 4k cameras to improve CCTV coverage and quality in public spaces. Each of these cameras incorporates up to five cameras in one device for wide-area surveillance, which would previously have required several separate devices, simplifying installation and resulting in significantly less associated cabling and infrastructure. They also provide powerful AI analytics, including accurate object detection and classification, to enable forensic search and save operators' time when responding to incidents. For example, identifying and establishing the movement of specific people or vehicles based on attributes such as vehicle type. Thames Valley CCTV partnership Phase two will see four additional control rooms in Oxfordshire merged into a single hub Phase two will see four additional control rooms in Oxfordshire merged into a single hub inside Abingdon Police station, also built on the Genetec Security Centre. This and the control room in Milton Keynes will be interlinked, adding further resilience as each site will be able to act as a fallback for the other. At this point, there will be a dedicated team of eighteen staff responsible for monitoring CCTV and enhancing CCTV for all participating communities in the Thames Valley CCTV Partnership. Innovative and cost-effective solutions “The CCTV Command Suite enabled by CDS, Genetec and Hanwha Vision has improved our workflows beyond recognition, enabling staff to quickly review and package evidence for frontline officers or more complex investigations. It has received several plaudits from officers for its ease of use,” says Jason Owen, CCTV Operations Manager, Thames Valley Police. “This collaboration between Thames Valley Police, Genetec, CDS Systems, and Hanwha Vision showcases the power of partnership in driving innovative, cost-effective solutions that improve public safety,” says John Boorman, Head of Product and Marketing at Hanwha Vision Europe. “Our AI-enabled cameras are designed to reduce false alarms and streamline operations, ensuring teams can focus on real incidents and drive efficiency across their monitoring.” Efficiency, at a lower cost All CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers Pooling resources and transferring ownership to the police has brought about significant cost efficiencies for participating authorities, while also enhancing the quality and reliability of public spaces CCTV. Just as importantly, it has dramatically improved the police’s direct access to quality video evidence. Unlike in a traditional council-run control room, all CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers. This means they have full access to Thames Valley’s suite of police databases and reporting software packages. They are better equipped to rapidly report incidents, support front-line officers, and communicate effectively with investigators as a result. On average, it handles between 300 – 500 incidents a month and has substantially increased the number of successful requests for supporting footage. “We’ve immediately seen the benefit of our investment in equipment and CCTV operators, with the police now much better equipped to deter and detect crime across the Thames Valley,” adds Barber. A solid platform for further improvements Control room operators’ intuition will always be the driving force that brings results Looking forward, Thames Valley has plans to use the Genetec platform to connect its people and mobile surveillance assets back to its control rooms for better cross-force interaction. Genetec Federation as a Service is already allowing live and recorded video to be shared with officers in the field. Soon it will also be extended to ensure video from police CCTV vans and drones is immediately available in the control room. In both cases this is achieved without complex network configuration, requiring only an internet connection. It is also at the beginning of its journey of fully realising the value of the AI-equipped Hanwha Vision cameras specified by CDS. Control room operators’ intuition will always be the driving force that brings results, but AI is freeing them up to do what they do best by saving time on routine monitoring and searches. Cost savings, resilience, and efficiencies Finally, talks continue that would see the addition of further control rooms across the Thames Valley to the Thames Valley CCTV Partnership. Having proven the model, would allow it to scale operations further to deliver even greater cost savings, resilience, and efficiencies. “We’re proud of what we’ve achieved to date but have no intention of resting on our laurels. The foundations we’ve established will ensure continued high-quality, consistent, and sustainable CCTV provision for our communities,” concludes Owen.
Modern measurement technologies enable high-precision detection of the movement of liquids and gases - and thus provide valuable data for numerous applications. How does the air flow around an aeroplane? How does the blood move through our veins? And how can pollutant emissions in combustion processes be minimised? For this purpose, speed, direction, pressure and turbulence within a flow are analysed in order to increase efficiency, ensure safety and drive innovation in a wide variety of areas. Innovative sensor technology High-resolution cameras are used to track marked particles within a flow and analyse their movement A range of methods are available to measure these flows, including visual ones such as particle image velocimetry (PIV). High-resolution cameras are used to track marked particles within a flow and analyse their movement. iLA_5150 GmbH from Aachen (Germany) now also relies on EBIV. The abbreviation stands for Event-Based Particle Image Velocimetry and is a new optical method for the qualitative and quantitative visualisation of flows and flow velocities. It combines PIV with event-based cameras, here with a uEye EVS from IDS Imaging Development Systems GmbH. The innovative sensor technology of the industrial camera enables highly dynamic and energy-efficient detection, especially of fast and turbulent movements. Application In the EBIV method, tiny particles are added to a flowing fluid and illuminated in a plane, the so-called light section plane. They generate individual light pulses as they enter and exit the LED light section. This change in local brightness is recorded independently by the camera pixels and transmitted to the PC as a data stream of "change events". In contrast to conventional cameras, event-based models therefore only react to the changes in brightness registered in the image field. Stationary scattered light, such as background or a non-changing illuminated surface, does not generate a measurement signal. This reduces the amount of data considerably. Frame rates of up to 10,000 frames per second The data stream essentially contains information about what happens, when and where The data stream essentially contains information about what happens, when and where. In detail, these are the pixel coordinates on the sensor, microsecond time stamps of the pixel events and the information about the events: ON or OFF. This allows a distinction to be made between increasing intensity (ON event) and decreasing intensity (OFF event). Using suitable software, the stream can be converted into an image matrix in which both the spatial information and the linear time base of the stream are available. The result is comparable to the extremely high frame rate of a high-speed camera. EBIV measurement method "The EBIV measurement method differs fundamentally from conventional imaging methods. They usually generate very large amounts of data and require powerful peripherals that can process them. For exceptional frame rates of 1000 Hertz and more, the image-based cameras required are themselves very complex and expensive." "With the help of event-based camera technology, comparable frame rates of 10,000 frames per second are possible, whereby only standard PC interfaces such as USB with a few gigabits per second are required. The price of the event-based models themselves is significantly lower than that of corresponding high-speed cameras and is therefore also very interesting for smaller teaching and research institutions," explains Dr André Brunn - Head of Development at iLA_5150 GmbH. Further processing The user can optimise the display of the move paths and adapt them to unique study objectives The data stream is converted into image data and displayed in a front end - the so-called EBIV viewer - for direct online flow visualisation. The user can also select the integration time, which corresponds to the exposure time of an image camera, as well as the time increments of the sequence, i.e., the period between two consecutive shots. Classic image filters can also be used. With the help of these settings, the user can optimise the display of the movement paths and adapt them to individual examination objectives. Both fine flow details and large-scale patterns can be made more clearly recognisable. This ability to readjust the measurement results is another advantage of the event-based approach. Numerical analysis of the flow properties In the qualitative visualisation of the flow in the EBIV-View, particles are continuously illuminated so that they are visible as luminous traces. The method is therefore very well suited to visualising the flow. However, it does not provide exact measurements of its speed or direction. For a precise, numerical analysis of the flow properties, individual particles are illuminated for a moment using short, time-defined light pulses. Image sequences of the event-based camera As with classic PIV, the image sequences of the event-based camera can also be statistically analysed This allows their exact position to be recorded and their movement quantified. By comparing the particle positions in successive images, the speed and direction of the flow can be precisely calculated using PIV, for example. The result is a transient 2D vector field that changes over time - in other words, the vectors do not remain constant. As with classic PIV, the image sequences of the event-based camera can also be statistically analysed, for example, to determine mean values and fluctuations in the flow velocity. Camera and software On the camera side, iLA relies on a uEye XCP-E from IDS. The small, lightweight industrial camera offers event-based sensor technology in a robust die-cast zinc housing (29 × 29 × 17 mm) with screw-on USB Micro-B connection. It is compatible with all standard C-mount lens sizes. This makes it ideal for both industrial and non-industrial areas. The integrated event-based vision sensor (EVS) was developed by Sony and Prophesee. It is supported by the Metavision SDK, a seamlessly integrated suite of software tools and models, APIs and other training and development resources from Prophesee for efficient analysis, visualisation and customisation. Building on this, the EBIV viewer from iLA_5150/PIVTec is specially tailored to flow visualisation applications. Outlook The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions. A qualitative flow visualisation is often sufficient to understand effects and develop suitable control mechanisms. Until now, however, imaging fast flows with high temporal resolution was usually only possible with expensive high-speed cameras. Event-based camera technology offers a cost-effective alternative that requires significantly less technical effort. These “simple” methods have been lacking in teaching and research in particular. Thanks to the extreme data reduction, this technology also allows the use of several cameras or large camera arrays without the periphery becoming a limitation for data transfer. The compact design of the uEye EVS models also makes them ideal for mobile applications. This means that real application environments can be analysed directly for the first time - without having to rely on artificial flow models or channels. Established flow measurement methods Event-based cameras enable efficient, cost-effective and high-resolution visualisation and quantification of flows. Due to the small amounts of data generated, many processes can be analysed almost in real time, which also makes them interesting for use in fully automated systems. Established flow measurement methods such as Particle Image Velocimetry (PIV) can be seamlessly integrated and expanded. The technology can be used wherever flow information is captured by changes in scattered light intensity - be it from moving particles or vibrating surfaces.
ZeroEyes, the creators of the first AI-based gun detection video analytics platform to earn the US Department of Homeland Security SAFETY Act Designation, announced that its proactive gun detection and intelligent situational awareness solution has been deployed at Scott County R-IV School District in Benton, Missouri, to mitigate gun-related violence. The deployment was facilitated by Freedom Security, a local security provider serving the greater Missouri Area. Robust security upgrades Located in a rural community near the borders of Illinois and Kentucky, Scott County R-IV School District consists of a single campus with three interconnected buildings serving students from pre-K through 12th grade. The district educates approximately 800 students annually and employs around 125 teachers and administrators. ZeroEyes is the newest addition to the district's robust security upgrades, which include window tints, HAVEN locks, integrations with CrisisGo, and more. Digital security cameras ZeroEyes’ AI gun detection and intelligent situational awareness software layer onto existing cameras ZeroEyes’ AI gun detection and intelligent situational awareness software layer onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to local law enforcement and school administration as quickly as 3 to 5 seconds from detection. ZeroEyes safety strategy “ZeroEyes is not intrusive or invasive, and it does more than just detect; it alerts, responds, and continues to do so throughout any situation involving a potential threat,” said Dr. Bradley Kolwyck, Superintendent of Scott County R-IV School District. “This technology is the final piece we needed to ensure every layer of our safety strategy is connected, enabling us to provide the safest environment possible.” ZeroEyes deployment ZeroEyes and the district are hosting a Lunch & Learn session at 11:00 am at the Scott County ZeroEyes and the district are hosting a Lunch & Learn session at 11:00 am at the Scott County R-IV District Office (4035 State Highway 77, Benton, MO). It will feature demonstrations and discussion sessions, including reflections from school pioneers on the district’s successful ZeroEyes deployment. The event is open to local schools, law enforcement, and media. ZeroEyes’ innovation and protection “I commend Scott County R-IV School District for taking the initiative to lean into innovation and proactively protect its students from gun-related violence,” said Mike Lahiff, CEO and cofounder of ZeroEyes. “ZeroEyes’ ability to provide first responders and law enforcement with advance warning and situational awareness empowers them to act quickly and save lives.”
ZeroEyes, the creators of the first AI-based gun detection video analytics platform to earn the full US Department of Homeland Security SAFETY Act Designation, announced that its technology has been deployed at East Hill Synagogue in Englewood, New Jersey, to proactively address gun-related threats. East Hill Synagogue is a 20+ year-old house of worship serving a diverse community of Modern Orthodox Jews, offering Shabbat and holiday prayer services, adult education and family activities. Proactive security measures ZeroEyes is one of multiple solutions in East Hill’s multi-layered security approach ZeroEyes is one of multiple solutions in East Hill’s multi-layered security approach, enabling members to participate in religious activities without fear or distraction. Anti-Semitic attacks have reached new levels in the past 18 months, with the Anti-Defamation League reporting that the U.S. has seen a 200% increase in hate crimes. This concerning fact highlights the need for increased proactive security measures to protect congregants during worship services and other events. Overall security initiative “Jewish law dictates that preserving (saving) life is a top priority, and we take that quite literally at East Hill Synagogue; safety is our top priority,” said Jonathan Blinken, Directory of Security, East Hill Synagogue. “ZeroEyes is one of the most important layers that we have in our overall security initiative. It is an extremely powerful tool to help us protect those that we love, our institutions and everyone that comes to visit them.” Digital security cameras ZeroEyes' AI gun detection and awareness software layers onto existing digital security cameras ZeroEyes' AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence — including visual description, gun type, and last known location — to local law enforcement and synagogue staff as quickly as 3 to 5 seconds from detection. ZeroEyes to safeguard from gun-related threats "Every individual has the right to safety in their place of worship, and it’s deeply troubling when violence threatens that sense of peace," said Mike Lahiff, CEO and co-founder of ZeroEyes. "We thank East Hill Synagogue for trusting ZeroEyes to safeguard their congregation from gun-related threats, ensuring their community remains secure and welcoming."
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.


Round table discussion
Physical security technologies are a prominent tool used by correctional facilities to provide a safe, secure, and controlled environment for staff, inmates, and the wider community. Among several functions, security technologies are used to prevent unauthorised access, to detect contraband, to monitor inmate movements and activities, and to protect staff. For security technology manufacturers, integrators and consultants, the corrections market presents distinctive challenges. We asked our Expert Panel Roundtable: What are the unique aspects of the corrections market, and how should the physical security industry adapt?
The security marketplace has its share of buzzwords, which are words or phrases that become popular and widely used in a specific industry. Buzzwords can be useful for conveying complex ideas quickly, but they can also be misused or misunderstood. Within a specific industry, such as security, buzzwords can create a sense of shared understanding and belonging. We asked this week’s Expert Panel Roundtable: What new buzzword have you heard, and what does it mean for the security industry?
Port forwarding is a networking technique that allows incoming traffic on a specific port number to be redirected to a particular device or application on a local network. Open ports on the network expose an IP video system to the internet. This makes it a potential target for malicious cyberattacks. In the physical security industry, the elimination of port forwarding is seen as a basic and manageable precaution to shore up cybersecurity. We asked this week's Expert Panel Roundtable: What are the risks of port forwarding, and how can manufacturers and/or integrators mitigate those risks?
Products


White papers

Security investments retailers should consider for their 2021 budget
Download
Optimise your business with analytics and AI
DownloadMaking sense of today’s security camera options
Download
How to drive B2B security & operations with smart surveillance
Download
Making your surveillance cyber secure
Download
Is access control in the cloud more cost effective?
Download
What are the security technology needs of the hotel sector?
Download
Network Security Redefined: IP-Enabled Access Control
Download
Top 7 trends to watch in the physical security industry
Download
Troubleshooting IP video systems
Download
Simple Security Solutions for SMBs
Download
5 question check-up: Test your camera's cybersecurity
Download
How to migrate to an IP-based access control system
Download
Six ways to eliminate costs, risks and disruption to your network
Download
The critical importance of Trusted Execution Environment in access control
Download
Security investments retailers should consider for their 2021 budget
Download
Optimise your business with analytics and AI
DownloadMaking sense of today’s security camera options
Download
How to drive B2B security & operations with smart surveillance
Download
Making your surveillance cyber secure
Download
Is access control in the cloud more cost effective?
Download
What are the security technology needs of the hotel sector?
Download
Network Security Redefined: IP-Enabled Access Control
Download
Top 7 trends to watch in the physical security industry
Download
Troubleshooting IP video systems
Download
Simple Security Solutions for SMBs
Download
5 question check-up: Test your camera's cybersecurity
Download
How to migrate to an IP-based access control system
Download
Six ways to eliminate costs, risks and disruption to your network
Download
The critical importance of Trusted Execution Environment in access control
Download
Security investments retailers should consider for their 2021 budget
Download

Videos
IP security solutions: Manufacturers & Suppliers
- Dahua Technology IP security solutions
- Hikvision IP security solutions
- exacqVision IP security solutions
- Honeywell Security IP security solutions
- Bosch IP security solutions
- AV Costar IP security solutions
- LILIN IP security solutions
- Pelco IP security solutions
- Axis Communications IP security solutions
- Messoa IP security solutions
- Hanwha Vision IP security solutions
- IDIS IP security solutions
- VIVOTEK IP security solutions
- BCDVideo IP security solutions
- Vicon IP security solutions
- Climax Technology IP security solutions
- eneo IP security solutions
- Avigilon IP security solutions
- Software House IP security solutions
- Illustra IP security solutions

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download