Progeny Access Controllers (13)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
- Make
- Progeny
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasises the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
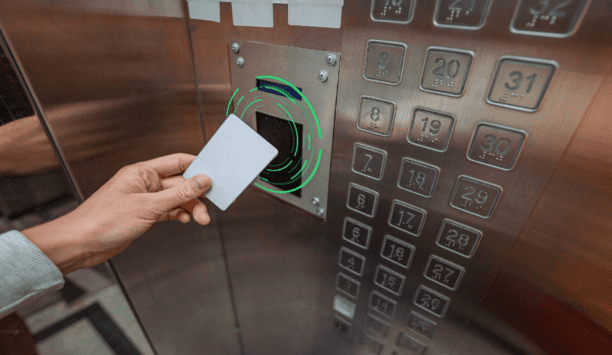
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Latest HID news

The PSA Network (PSA), the world's largest consortium of professional systems integrators, will host its annual convention October 14–17 in Marco Island, Florida, at the JW M...

HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs&nda...

HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs &nd...
Related white papers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge
Mobile access articles
HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs–from harsh condit...
HID, a worldwide pioneer in trusted identity solutions, announces the expansion of its signature line of Signo™ Readers to include models that meet varying customer needs – from harsh cond...
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous t...
Radiofrequency (RF) technology specialists, SPX Communication Technologies launched Evenlode Lite, an entry-level video downlink system designed for regions new to airborne surveillance or those looki...
Wavelynx Technologies, a trailblazer in advanced, secure, and versatile reader and credential solutions, announced the launch of its industry-first app, Configure by Wavelynx, to revolutionise th...
Genetec Inc., a pioneering technology provider of unified security, public safety, operations, and business intelligence solutions, announced the launch of Operations Centre, a cloud-based work m...
Hanwha Vision, the global vision solution provider, has released the XRN-426S-1T recorder - a compact NVR with a built-in 1TB solid-state drive (SSD). The 4-channel recorder supports AI search, when...
Fences, gates, storage cages, racks, containers, tool cabinets, and other non-standard openings often require restricted access and greater control. In many cases, they are secured with mechanical loc...
IDEMIA Public Security North America, the global provider of convenient and trusted biometric-based solutions, including physical and digital secure credentialing in the U.S, is partnering with My Fam...
ABLOY rose to the top of the list as Finland’s most valued brand of 2024, according to an annual survey by pollster Taloustutkimus. Market research company - Taloustutkimus surveys Finnish consu...
Signo Express and Seos Essentials provide a comprehensive, affordable access control solution designed for small to mid-sized businesses. This suite maximises security and flexibility without complex...
Award-winning security manufacturer, Gallagher, has announced the appointment of Merv Williams as Chief Marketing Officer (CMO). Williams will lead the development and delivery of Gallagher Security&r...
Level Home, Inc., the company redefining the smart home, announced the release of professional installer editions of its industry-renowned, award-winning smart locks, Level Bolt and Level Lock+ includ...
The most common wearable device deployed by security professionals is the body-worn camera. Traditionally used by law enforcement professionals, these devices are finding more and more uses in the cor...
Sharry, a global workplace experience platform built around digital employee badges, has successfully delivered its enterprise solution to London’s new international hub opened by PATRIZIA, a gl...
The security challenges of data centers
DownloadSecurity practices for hotels
DownloadAccess control system planning phase 2
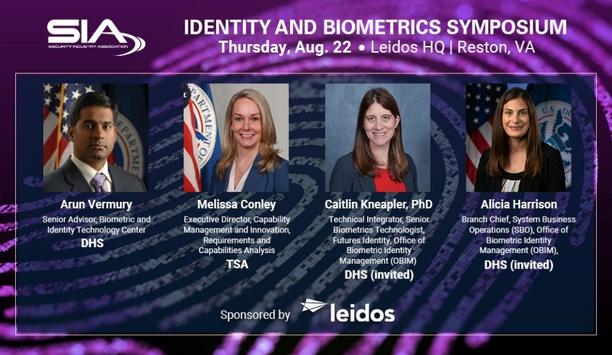
DownloadSIA Identity and Biometrics Symposium
DownloadBank security
Download- ASSA ABLOY eCLIQ: Secure Access At Hofbräuhaus Munich
- AMPELMANN GmbH enhances security with ASSA ABLOY eCLIQ solution
- Anviz transforms traditional property management into a smart reality, making digitisation more than just talk
- Matrix's COSEC VYOM, a cloud-based attendance system, enhances efficiency across various locations for a UK-based Indian multinational public sector bank