HID Access Controllers (13)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
- Make
- HID
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasises the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
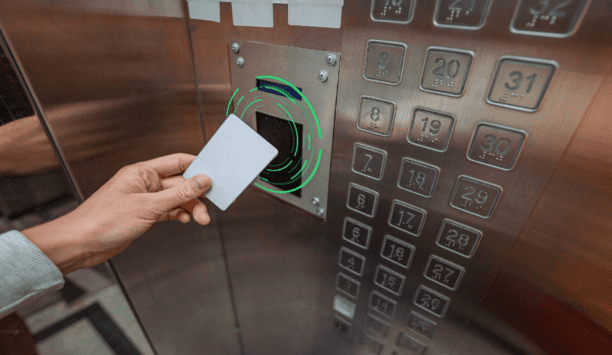
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Latest HID news

In many cases, architectural design and layout dictate optimal placement of security devices like cameras, access control readers, and sensors. Poor design can lead to blind spots,...

HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and si...

HID, the company behind the security card readers and access systems used in office buildings, universities, and government facilities worldwide – including several UK landma...
Related white papers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge
Trending topic articles
Global cybersecurity provider Hornetsecurity has partnered with Amazon to provide Amazon Simple Email Service (SES) Mail Manager customers with its Vade Advanced Email Security Add-On. Util...
Rapid7, a pioneer in extended risk and threat detection, announced the launch of Intelligence Hub, an integrated threat intelligence solution designed to provide security teams with meaningful conte...
In an era marked by escalating cyber threats, Yubico, the pioneering provider of hardware authentication security keys, is proud to empower the future of cybersecurity pioneers by recently provid...
Lenovo announced its largest storage portfolio refresh in company history, unveiling new Lenovo Data Storage Solutions that prepare enterprise IT for the age of AI with better efficiency, performance...
In many cases, architectural design and layout dictate optimal placement of security devices like cameras, access control readers, and sensors. Poor design can lead to blind spots, reduced coverage, a...
Custom Intelligent Security specialises in risk analysis, system design, installation, and maintenance of unified high-security solutions. Their extensive portfolio includes Government, commercial, a...
DigiCert, Inc., one of the global provider of digital trust, announces a record-breaking Q4 for FY2025, closing at 104% of target net new annual contract value (NNACV), 25% higher than the largest NNA...
CSignum, the pioneering provider of wireless technology extending IoT communications beneath the surface, has completed a £6 million Series A funding round. The investment will accelerate growt...
The Security Industry Association has sent a letter to U.S. Trade Representative - Jamieson Greer and U.S. Secretary of Commerce - Howard Lutnick requesting relief from tariffs for security industry p...
The G2E Asia Conference and Asian IR Summit are set to return this May, bringing top industry leaders together to tackle the most pressing issues and opportunities within the entertainment and integra...
Scality, a pioneer in cyber-resilient storage for the AI era, unveiled a first-of-its-kind unified software appliance developed in collaboration with Veeam® Software, a pioneer in data resilience....
Permiso, the pioneer in real-time identity security, launches its new platform to help security teams assess and reduce exposure risk in addition to their extensive threat detection capabilities. Per...
Frequentis Germany has been awarded the contract to plan and supply the operations and control centre system for the police of the Free State of Thuringia. As a general contractor, Frequentis i...
Dallmeier electronic, one of the pioneering manufacturers of video technology “Made in Germany”, presents innovative solutions for more security and efficiency in logistics at the Transpor...
IDIS, the largest in-country manufacturer of trusted South Korean-made video tech, now offers an extensive and versatile range of intrinsically safe explosion-proof ATEX, UL, and IP68-rated cameras. T...
Global cybersecurity provider Hornetsecurity has partnered with Amazon to provide Amazon Simple Email Service (SES) Mail Manager customers with its Vade Advanced Email Security Add-On. Util...
Rapid7, a pioneer in extended risk and threat detection, announced the launch of Intelligence Hub, an integrated threat intelligence solution designed to provide security teams with meaningful conte...
In an era marked by escalating cyber threats, Yubico, the pioneering provider of hardware authentication security keys, is proud to empower the future of cybersecurity pioneers by recently provid...
Lenovo announced its largest storage portfolio refresh in company history, unveiling new Lenovo Data Storage Solutions that prepare enterprise IT for the age of AI with better efficiency, performance...
In many cases, architectural design and layout dictate optimal placement of security devices like cameras, access control readers, and sensors. Poor design can lead to blind spots, reduced coverage, a...
Custom Intelligent Security specialises in risk analysis, system design, installation, and maintenance of unified high-security solutions. Their extensive portfolio includes Government, commercial, a...
DigiCert, Inc., one of the global provider of digital trust, announces a record-breaking Q4 for FY2025, closing at 104% of target net new annual contract value (NNACV), 25% higher than the largest NNA...
CSignum, the pioneering provider of wireless technology extending IoT communications beneath the surface, has completed a £6 million Series A funding round. The investment will accelerate growt...
The Security Industry Association has sent a letter to U.S. Trade Representative - Jamieson Greer and U.S. Secretary of Commerce - Howard Lutnick requesting relief from tariffs for security industry p...
The G2E Asia Conference and Asian IR Summit are set to return this May, bringing top industry leaders together to tackle the most pressing issues and opportunities within the entertainment and integra...
Scality, a pioneer in cyber-resilient storage for the AI era, unveiled a first-of-its-kind unified software appliance developed in collaboration with Veeam® Software, a pioneer in data resilience....
Permiso, the pioneer in real-time identity security, launches its new platform to help security teams assess and reduce exposure risk in addition to their extensive threat detection capabilities. Per...
Frequentis Germany has been awarded the contract to plan and supply the operations and control centre system for the police of the Free State of Thuringia. As a general contractor, Frequentis i...
Dallmeier electronic, one of the pioneering manufacturers of video technology “Made in Germany”, presents innovative solutions for more security and efficiency in logistics at the Transpor...
IDIS, the largest in-country manufacturer of trusted South Korean-made video tech, now offers an extensive and versatile range of intrinsically safe explosion-proof ATEX, UL, and IP68-rated cameras. T...
Global cybersecurity provider Hornetsecurity has partnered with Amazon to provide Amazon Simple Email Service (SES) Mail Manager customers with its Vade Advanced Email Security Add-On. Util...
Using artificial intelligence (AI) to automate physical security systems
DownloadA modern guide to data loss prevention
Download7 proven solutions for law enforcement key control and asset management
DownloadThe truth behind 9 mobile access myths
DownloadAccess control system planning phase 2
Download