Network cameras
Hikvision has achieved two prestigious international certifications: ETSI EN 303 645 and EN 18031. The certifications were awarded by Bureau Veritas, a globally renowned third-party inspection, testing and certification organisation. This achievement underscores Hikvision’s commitment to security and compliance in its IoT products. ETSI EN 303 645 certification ETSI EN 303 645 certification is a European standard focused on the security of IoT devices The ETSI EN 303 645 certification...
Entrust, the pioneer in identity-centric security solutions, announced the Entrust Cryptographic Security Platform, the industry’s first unified, end-to-end cryptographic security management solution for keys, secrets, and certificates. Cyberattacks on data security and identity systems are exploding in scale and sophistication. Securing data and identities Traditional approaches to securing data and identities aren't working, and in digital-first environments, every connected dev...
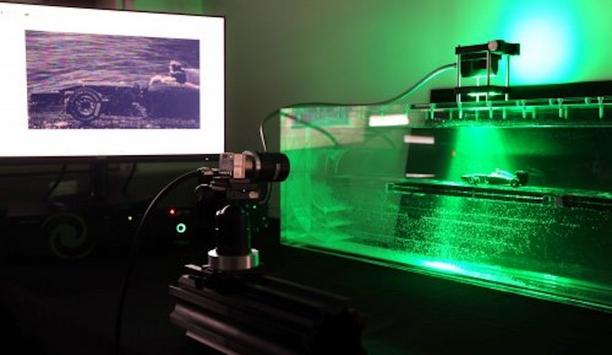
Hikvision has collaborated with the French software developer, FWA. The partnership has enabled FWA to integrate Hikvision’s automatic number plate recognition (ANPR) licence plate detection technology into its DuckTheLine logistics queue management solution. DuckTheLine enables site managers to schedule when trucks should arrive, and to optimise their progress through the facility whilst they are on-site. Process of loading and unloading The alliance with Hikvision enables FWA to autom...
Genetec Inc., the pioneer in enterprise physical security software, has announced the dates for its annual empower360 roadshow. Scheduled to take place in Dubai, United Arab Emirates (UAE), on 17 April 2025, the partner-focused event will bring together industry professionals to explore the evolving role of physical security in the country. Adaptable deployment models According to the Genetec State of Physical Security Report 2025, 66% of physical security consultants and channel partne...
Robotic Assistance Devices Inc. (RAD), a subsidiary of Artificial Intelligence Technology Solutions, Inc., has secured the deployment of two ROSA-P 360 devices through a proactive engagement with a prominent municipal Business Improvement District. The units are being deployed to enhance safety and visibility across key public spaces managed by the local community improvement organisation. This strategic placement reflects RAD’s growing influence in urban safety initia...
VIVOTEK (3454-TW), the pioneering security solution provider, celebrates its 25th anniversary by reaffirming its commitment to pioneering AI and cloud-based technologies. At ISC West—the largest international security technology expo in the western United States—VIVOTEK introduced the latest innovations in its cloud-based VORTEX platform and premiered a commemorative video marking 25 years of global impact. Smarter security with AI-powered search One of the key highlights at ISC W...
News
MOBOTIX consolidates its position as a pioneering provider of innovative fire protection technologies: MOBOTIX thermographic cameras have again received the “Technical Evaluation of Suitability” (Evaluación Técnica de Idoneidad). The certification according to the strict requirements of the Spanish Fire Protection Systems Regulation (Reglamento de Instalaciones de Protección Contra Incendios/RIPCI) was issued by Applus, a certification body recognised by the Spanish Ministry of Industry. MOBOTIX solutions in security projects Extension opens up new possibilities for the use of MOBOTIX solutions in complex fire protection Not only has the certification been renewed, but also significantly extended. In addition to the proven MOBOTIX thermal sensors, it now also covers the new interface boxes (Mx-4IOA-Box and Mx-NPAA-Box) as well as the full range of Thermal Radiometry (TR) sensors available. This extension opens up new possibilities for the use of MOBOTIX solutions in complex fire protection and security projects. Conventional fire alarm systems “With this extended certification, we are underlining our innovative strength and our strong position in the Spanish market,” says Christian Cabirol, CTO of MOBOTIX AG. “Our technology proves its strength precisely where conventional fire alarm systems reach their limits - for example in extensive outdoor areas or large halls.” Early fire detection at the highest level With up to 20 per configurable detection zones per thermal sensor, the plans are highly versatile MOBOTIX thermal cameras offer an outstanding early fire detection solution. They detect potential hazards before flames or smoke become visible, enabling a faster and more effective response. Thanks to the high flexibility, temperature detection parameters can be precisely adapted to specific fire risks. With up to 20 individually configurable detection zones per thermal sensor, the systems are highly versatile. The renewed certification also confirms that the MOBOTIX thermal systems can be easily integrated into existing fire alarm systems. They also meet the requirements of insurance companies and building regulations. Global trends drive growth in the fire protection market The demand for innovative fire protection solutions is growing steadily: studies forecast a global market volume of up to USD 150 billion by 2030. Stricter regulations and the need for more effective technologies are driving this development. With the renewed and extended RIPCI certification, MOBOTIX is excellently positioned to benefit from this trend and continue to set standards in early fire detection. “Our certificates and the continuous expansion of our portfolio are proof of our commitment to always being one step ahead,” explains Thomas Lausten, CEO, adding: ”In a fire, every second counts. Our mission is to help our customers protect lives and property - with technologies that are reliable and forward-looking.”
Trusted Connectivity Alliance (TCA) has released Version 3.4 of its eUICC Profile Package: Interoperable Format Technical Specification (Interoperable Profile Package Specification). The latest version includes major updates to support full alignment with 3GPP Release 18 to enable advanced 5G functionality and secure authentication in 5G network slicing, as well as enabling the remote management of eSIM profiles on low-power and network-constrained devices. Interoperable connectivity profiles Mobile operators to load interoperable connectivity profiles in an eSIM Additional updates and clarifications to promote security and interoperability have also been made. TCA’s Interoperable Profile Package Specification – which is used in every eSIM deployed in the field – standardises the format used for the remote loading of subscriptions onto eSIMs across deployed devices. This enables mobile operators to load interoperable connectivity profiles in an eSIM, regardless of the SIM vendor. Key updates in Version 3.4 Full alignment with 3GPP Release 18 – this includes support of Slice SIM (SSIM), allowing operators to utilise the proven security capabilities of eUICC / eSIM to authenticate subscribers and enable secure access to 5G network slices. This will help to enhance the security of 5G networks and protect subscriber privacy. Support for GlobalPlatform’s standardised Secure Channel Protocol Amendment M– which enables remote application and file management on constrained IoT devices that could not previously be updated or patched due to the absence of SMS support. This addresses an immediate interoperability challenge by making it easier to remotely provision and manage eSIM profiles on constrained NarrowBand IoT (NB-IoT) devices. Benefits of eSIM technology TCA also estimates that the total available market for eSIM was 514 million units Denis Praca, Chair of the TCA eUICC Working Group, comments: “Since it was first published 10 years ago, TCA’s Interoperable Profile Package Specification has played a foundational role in promoting trust, consistency and reliability across the eSIM ecosystem." "These latest enhancements stand to further extend the capabilities and benefits of eSIM technology, bringing seamless connectivity and advanced security to new and established use-cases.” Latest TCA eSIM market data The publication of the new specification follows the release of the latest TCA eSIM market data, which revealed that 2024 was a landmark year of growth across the eSIM ecosystem. eSIM shipment volumes collectively reported by TCA members in 2024 surpassed half a billion units, increasing 35% year-on-year to reach 503 million. TCA also estimates that the total available market for eSIM was 514 million units. The growing availability of eSIM-enabled devices was matched by increasing consumer adoption, with consumer eSIM profile downloads rising by 56%. Enhancement of eSIM technology TCA published Version 3.3.1.2 of eUICC Profile Package: Interoperable Format Test Specification Bertrand Moussel, Chair of the TCA Board, adds: “As the eSIM ecosystem continues to expand, TCA is committed to shaping the continued standardisation and enhancement of eSIM technology in close collaboration with pioneering industry stakeholders.” TCA has also published Version 3.3.1.2 of eUICC Profile Package: Interoperable Format Test Specification, which provides a globally standardised means of testing products to ensure the eSIM profile is correctly loaded. GSMA’s eSIM Test Specifications Version 3.3.1.2 is a GlobalPlatform-approved test suite, which is part of the GSMA Consumer and IoT eSIM compliance programmes and referenced in GSMA’s eSIM Test Specifications (SGP.23 and SGP.33) – the dedicated, globally-backed remote SIM test specifications for Consumer and IoT. Work is currently ongoing in TCA to develop the test specification for Interoperable Profile Package Technical Specification v3.4.
AtlasIED, a pioneer in the security and commercial audio industries, announces the launch of its new Rapid Alert system, which includes the IP-PB wearable panic button and the IP-RC BLE-controlled relay board. This system is designed to enhance emergency communication and integrates seamlessly with AtlasIED’s IPX IP Endpoints, providing immediate accessibility to trigger notifications during critical events. Improving response times The IP-PB panic button is worn on a lanyard and connects wirelessly to the IP-RC relay board via Bluetooth Low Energy (BLE). In emergency situations, users can press the panic button to activate notifications, including pre-programmed alerts that play throughout the facility. These notifications can be distributed through InformaCast or Revolution, ensuring that relevant personnel are promptly informed of the incident. “The Rapid Alert system represents a remarkable advancement in enhancing emergency response capabilities,” said Michael Peveler, VP of Sales for AtlasIED, adding “By integrating reliable wireless communication with our IPX Series, the system ensures quick and effective responses during critical situations. With the new panic button, an immediate and coordinated reaction can be initiated, significantly improving response times and emergency outcomes.” Reliable wireless connection The IP-RC BLE-controlled relay board connects directly to the IPX Series control boards The system is composed of two core components. The wearable IP-PB panic button utilises BLE 5.0 Ultra Wide Band communication to provide a reliable wireless connection. It features a lithium-ion battery with a lifespan of up to three years and is IP67 rated, making it both durable and resistant to environmental factors. The IP-RC BLE-controlled relay board connects directly to the IPX Series control boards and offers two relay closures that can be configured to trigger specific actions across the network. This capability enables users to initiate customised notifications for different emergency scenarios. Multiple activation sequences The system is designed to support multiple activation sequences to meet different response protocols. A quick double press of the button on the IP-PB activates one relay, while six or more button presses can automatically trigger a lockdown and immediately notify stakeholders and responders. This customisation of emergency responses offers exceptional flexibility. The Rapid Alert system integrates easily into existing AtlasIED IPX Series devices, ensuring seamless operation across various commercial environments and further proving the capability of AtlasIED’s Security Technology Solutions Ecosystem. It is ideal for schools, hospitals, industrial facilities, and corporate offices, where clear and timely communication is crucial during emergencies. The addition of the IP-PB enables AtlasIED to become Alyssa’s Law compliant, meeting the legislative requirements implemented in select states. The IP-PB wearable panic button and IP-RC relay board are now available.
Illumio, the breach containment company, announced the launch of Illumio Insights, the industry’s first cloud detection and response (CDR) solution powered entirely by an AI security graph. A key part of Illumio’s breach containment platform, Insights can observe and protect every workload and resource, spanning hybrid and multi-cloud environments. It provides AI-powered observability into the organisation’s traffic, flows, and connections, surfacing risk throughout the connected landscape. Illumio Insights SOC analysts Threats can be dynamically quarantined, with impacted workloads fully isolated, reducing the blast radius Illumio Insights helps SOC analysts, incident responders, and threat hunters uncover hidden risks by observing all flows and connections and discovering risky, malicious, and anomalous activity. Insights visualises dangerous traffic and behaviour and prioritises lateral movement risks across environments, enabling rapid detection and response. Threats can be dynamically quarantined, with impacted workloads completely isolated, reducing the blast radius and significantly boosting resilience. Key benefits of Illumio Insights Rapid Cloud-Scale Deployment: Push-button, agentless deployment delivers AI security graph-powered insights across millions of workloads in minutes. Unmatched Threat Detection with AI Observability: Significantly reduces the mean time to detect (MTTD) by uncovering unseen threats and attack paths. One-Click Attack Containment: Immediately neutralises potential risks and reduces the mean time to respond (MTTR) with one-click containment. AI-driven Illumio Insights analytics pipeline “When an organisation is under attack, understanding the connectivity graph is crucial. Bringing together the Illumio security graph with the AI-driven Illumio Insights analytics pipeline allows organisations, for the first time, to understand how threats and risks are moving through their environment. This is the power of an AI security graph,” says Andrew Rubin, CEO and Founder of Illumio. “Illumio Insights is vital for protecting the environment as it offers unparalleled observability to understand threat and malicious activity in the cloud. Illumio Insights connects the dots and finds every needle in every haystack. When integrated with Illumio Segmentation, breaches are contained and cyber disasters avoided.” Illumio’s AI security graph Illumio’s AI security graph enables Insights to ingest network flow and resource data at cloud scale Illumio’s AI security graph enables Insights to ingest network flow and resource data at cloud scale, automatically classify traffic and resources, and immediately find the risk. The graph helps security teams to form a complete picture of attacker movement across the entire environment and drives faster, more informed response decisions. AI-powered security graphs "As the cybersecurity landscape continues to evolve, it's no longer about having more technology — it's about having smarter, more adaptive solutions. The need for intelligent systems has never been greater, and AI is at the heart of this transformation,” said Frank Dickson, group vice president, Security and Trust at IDC. “AI-powered security graphs are a game-changer, enabling businesses to proactively identify, assess, and mitigate risks in near real-time. These sophisticated tools streamline security efforts and enhance decision-making by learning from patterns and behaviours, offering a level of insight and protection that traditional offerings simply can't match." Illumio Insights and Illumio Segmentation Illumio Insights and Illumio Segmentation are integral components of the Illumio Platform According to Thomas Vavra, manager, Network & Security Operations, Mondi Group, “Illumio Insights will give us real-time visibility and control over our risky ports, significantly reducing our risk exposure and improving compliance with industry standards. This will enable us to quickly identify vulnerabilities and address them before they become threats.” Illumio Insights and Illumio Segmentation are integral components of the Illumio Platform, the first cybersecurity platform focused on breach containment. Overall cyber resilience Illumio Insights helps organisations quickly identify and detect threats, while Illumio Segmentation contains breaches, protects critical assets, and enables instant response. Together, these solutions help identify and mitigate risks, contain attacks, and enhance overall cyber resilience. To see a demo of Illumio Insights, and to learn more about Illumio’s breach containment offerings, stop by the Illumio booth (North Hall #5670) at RSAC in San Francisco April 28-May 1.
Hailo, the pioneering provider of edge AI processors, will demonstrate smart security cameras empowered by its vision processing units (VPUs) as well as video management systems empowered by its AI accelerators at ISC West 2025 in Las Vegas, Nevada at booth #31065 of the Venetian Expo. At the heart of Hailo’s showcase is its full suite of AI processors, including the Hailo-15 vision processors, which integrate seamlessly into pioneering security cameras to deliver superior image quality and real-time analytics. Generative AI applications Its powerful AI capabilities enhance image quality while also efficiently handling multiple complex classic and generative AI applications at full scale. Alongside them, the Hailo-8 and Hailo-10 AI accelerators, selected by the world’s top security brands, power video management systems and other next-generation applications that require high-performance AI at the edge. What’s possible in AI for security Hailo will also demonstrate some of the industry’s most advanced models running entirely on camera Pushing the boundaries of what’s possible in AI for security, Hailo will also demonstrate some of the industry’s most advanced models running entirely on camera, at low power and independent of cloud connectivity. Demonstrations include zero-shot classification for real-time image search and query, and Vision-Language Models (VLMs) for automatic video captioning. Visitors will be able to experience edge-deployed chatbots powered by LLMs such as DeepSeek-R1 operating offline and locally on-device, ensuring privacy and security without compromising on AI capabilities. Advanced video analytics “As AI continues to revolutionise security and surveillance, Hailo is at the forefront, delivering the most widely deployed edge AI processors to a vast community of thousands of developers,” said Orr Danon, CEO of Hailo. “By removing compute limitations, we are enabling smart cameras to feature both best-in-class image quality and advanced video analytics, making security systems more intelligent, efficient, and responsive than ever before.” Hailo’s leadership in edge AI Hailo’s leadership in edge AI is further reinforced by the cutting-edge solutions showcased in cooperation Hailo’s leadership in edge AI is further reinforced by the cutting-edge solutions showcased in cooperation with its partners at the booth. Demonstrations include a Digital Watchdog VMS integration, real-time facial anonymisation by AlgoFace, AI-powered crowd and drive-through monitoring for retail applications by AT&T and Capgemini, live video stream analysis using semantic segmentation on a Dell 3200 gateway, and a Deep Perception analytics solution running on an HP Engage Flex Mini G2 connected to a Milestone VMS, among others. Hailo’s processors unmatched AI performance Hailo’s processors deliver unmatched AI performance in terms of both power-efficiency and cost-efficiency, making it the go-to choice for security solutions providers, ranging from low-power smart cameras to large-scale video management systems. With hundreds of customers and tens of thousands of developers driving innovation on its platform, Hailo continues to set the standard as the #1 edge AI processor provider, powering the future of AI-driven security. To experience the next generation of edge AI in action, and for more information, visit the website and stop by Booth #31065 at ISC West 2025 between April 2 and April 4, 2025.
As Taiwan's security industry continues to evolve with technological advancements and increased diversification, various vertical markets are poised for significant growth. Secutech, scheduled for 7–9 May 2025 at the Taipei Nangang Exhibition Centre, aims to capitalise on this burgeoning demand. Around 400 international and local exhibitors are set to showcase the latest technologies and solutions across six zones and pavilions at the fair, which serves as a vital platform to connect security and fire safety suppliers with key industry players in Taiwan. Demand for upgrading equipment and systems AIoT landscape is reshaping mixed industries and driving an increasing demand for upgrading kit Recent reports indicate that Taiwan's security market is projected to compound at an annual rate of 6.6%, reaching an estimated USD 119.9 million by 2029. At the same time, the artificial intelligence of things (AIoT) landscape is reshaping various industries and driving an increasing demand for upgrading equipment and systems aimed at improving fire and safety efficiency. Affected settings include hospitals, industrial sites, parking facilities, old buildings, factories, shopping malls, and energy storage facilities. Security and fire safety equipment Exhibitors at Secutech 2025 will be integral to this wave of advanced technology, showcasing the integration of 5G, AI, and IoT in security and fire safety equipment for real-time monitoring, predictive analytics, and automated responses, ensuring higher efficiency and safety across multiple industries. The 26th edition will welcome prominent international brands in the global security landscape, including NetworkOptix, Panasonic, Blazecut Group, and Mabu Valley Outdoor Ltd. Key local exhibitors With Taiwan's longstanding reputation as one of Asia-Pacific’s technological hubs and its expanding influence in high-tech industries, major Taiwanese manufacturers are pivotal players in the global security manufacturing space. At the show, key local exhibitors will feature their advanced technology, including: TDV - Triple Domain Vision Co Ltd will showcase advanced front-end intelligent video analytics to enhance surveillance effectiveness and operational efficiencies. Avadesign Technology Co Ltd will display a comprehensive suite of security monitoring and management services, focusing on IP video intercom and house automation solutions. Formosa Plastics Corporation is set to modernise information chains and applications with smart workplace safety management platforms, facial recognition access controls, electronic fence detection technologies, and security monitoring dashboards. Himax Technologies Ltd will exhibit cutting-edge image processing technologies tailored for security applications, including CMOS sensors, wafer-level optics for AR devices, 3D sensing technologies, and ultralow-power AI image sensing technologies. Vivotek will showcase a range of IP surveillance products and solutions driven by advanced AI algorithms, supported by a one-stop monitoring cloud platform. Marson Technology will present high-quality barcode scanning equipment along with complete OEM/ODM services. Exploring key industry trends for diverse applications This year’s show will feature six zones and pavilions, where key manufacturers will showcase their innovative solutions, aiming to capture critical trends across various vertical industries. These areas create a comprehensive environment for exploring cross-sector sourcing and collaboration opportunities: AI Innovation Application Zone (Transportation / Logistics / Retail) SmartHome and Building Pavilion Security and AIoT Smart Security Pavilion Smart Factory, Industrial Safety and Sanitation Application Pavilion Innovative Fire Prevention and Protection Technology Application Pavilion ESG Total Solution Pavilion Adoption of AIoT drives information security innovations Taiwan’s emphasis on data security grows increasingly critical, evidenced by calls to enrich digital security As AIoT evolves alongside the security market, Taiwan’s emphasis on information security grows increasingly critical, evidenced by government calls to enhance digital security and recent information security sector growth forecasts. The upcoming show will also showcase innovative information security technologies from renowned exhibitors, including InfoKeyVault Technology and Infineon Technologies Taiwan, aiming to advance solutions that address emerging threats and enhance data protection across smart manufacturing, smart home technology, and healthcare industries. Secutech sharing insights for fairgoers In this landscape, Secutech serves as an essential platform, facilitating business connections and sharing insights for fairgoers to stay ahead in a dynamic market. Secutech is organised by Messe Frankfurt (HK) Ltd – Taiwan Branch and is part of a global network of Safety, Security, and Fire trade fairs.
MOBOTIX consolidates its position as a pioneering provider of innovative fire protection technologies: MOBOTIX thermographic cameras have again received the “Technical Evaluation of Suitability” (Evaluación Técnica de Idoneidad). The certification according to the strict requirements of the Spanish Fire Protection Systems Regulation (Reglamento de Instalaciones de Protección Contra Incendios/RIPCI) was issued by Applus, a certification body recognised by the Spanish Ministry of Industry. MOBOTIX solutions in security projects Extension opens up new possibilities for the use of MOBOTIX solutions in complex fire protection Not only has the certification been renewed, but also significantly extended. In addition to the proven MOBOTIX thermal sensors, it now also covers the new interface boxes (Mx-4IOA-Box and Mx-NPAA-Box) as well as the full range of Thermal Radiometry (TR) sensors available. This extension opens up new possibilities for the use of MOBOTIX solutions in complex fire protection and security projects. Conventional fire alarm systems “With this extended certification, we are underlining our innovative strength and our strong position in the Spanish market,” says Christian Cabirol, CTO of MOBOTIX AG. “Our technology proves its strength precisely where conventional fire alarm systems reach their limits - for example in extensive outdoor areas or large halls.” Early fire detection at the highest level With up to 20 per configurable detection zones per thermal sensor, the plans are highly versatile MOBOTIX thermal cameras offer an outstanding early fire detection solution. They detect potential hazards before flames or smoke become visible, enabling a faster and more effective response. Thanks to the high flexibility, temperature detection parameters can be precisely adapted to specific fire risks. With up to 20 individually configurable detection zones per thermal sensor, the systems are highly versatile. The renewed certification also confirms that the MOBOTIX thermal systems can be easily integrated into existing fire alarm systems. They also meet the requirements of insurance companies and building regulations. Global trends drive growth in the fire protection market The demand for innovative fire protection solutions is growing steadily: studies forecast a global market volume of up to USD 150 billion by 2030. Stricter regulations and the need for more effective technologies are driving this development. With the renewed and extended RIPCI certification, MOBOTIX is excellently positioned to benefit from this trend and continue to set standards in early fire detection. “Our certificates and the continuous expansion of our portfolio are proof of our commitment to always being one step ahead,” explains Thomas Lausten, CEO, adding: ”In a fire, every second counts. Our mission is to help our customers protect lives and property - with technologies that are reliable and forward-looking.”
Trusted Connectivity Alliance (TCA) has released Version 3.4 of its eUICC Profile Package: Interoperable Format Technical Specification (Interoperable Profile Package Specification). The latest version includes major updates to support full alignment with 3GPP Release 18 to enable advanced 5G functionality and secure authentication in 5G network slicing, as well as enabling the remote management of eSIM profiles on low-power and network-constrained devices. Interoperable connectivity profiles Mobile operators to load interoperable connectivity profiles in an eSIM Additional updates and clarifications to promote security and interoperability have also been made. TCA’s Interoperable Profile Package Specification – which is used in every eSIM deployed in the field – standardises the format used for the remote loading of subscriptions onto eSIMs across deployed devices. This enables mobile operators to load interoperable connectivity profiles in an eSIM, regardless of the SIM vendor. Key updates in Version 3.4 Full alignment with 3GPP Release 18 – this includes support of Slice SIM (SSIM), allowing operators to utilise the proven security capabilities of eUICC / eSIM to authenticate subscribers and enable secure access to 5G network slices. This will help to enhance the security of 5G networks and protect subscriber privacy. Support for GlobalPlatform’s standardised Secure Channel Protocol Amendment M– which enables remote application and file management on constrained IoT devices that could not previously be updated or patched due to the absence of SMS support. This addresses an immediate interoperability challenge by making it easier to remotely provision and manage eSIM profiles on constrained NarrowBand IoT (NB-IoT) devices. Benefits of eSIM technology TCA also estimates that the total available market for eSIM was 514 million units Denis Praca, Chair of the TCA eUICC Working Group, comments: “Since it was first published 10 years ago, TCA’s Interoperable Profile Package Specification has played a foundational role in promoting trust, consistency and reliability across the eSIM ecosystem." "These latest enhancements stand to further extend the capabilities and benefits of eSIM technology, bringing seamless connectivity and advanced security to new and established use-cases.” Latest TCA eSIM market data The publication of the new specification follows the release of the latest TCA eSIM market data, which revealed that 2024 was a landmark year of growth across the eSIM ecosystem. eSIM shipment volumes collectively reported by TCA members in 2024 surpassed half a billion units, increasing 35% year-on-year to reach 503 million. TCA also estimates that the total available market for eSIM was 514 million units. The growing availability of eSIM-enabled devices was matched by increasing consumer adoption, with consumer eSIM profile downloads rising by 56%. Enhancement of eSIM technology TCA published Version 3.3.1.2 of eUICC Profile Package: Interoperable Format Test Specification Bertrand Moussel, Chair of the TCA Board, adds: “As the eSIM ecosystem continues to expand, TCA is committed to shaping the continued standardisation and enhancement of eSIM technology in close collaboration with pioneering industry stakeholders.” TCA has also published Version 3.3.1.2 of eUICC Profile Package: Interoperable Format Test Specification, which provides a globally standardised means of testing products to ensure the eSIM profile is correctly loaded. GSMA’s eSIM Test Specifications Version 3.3.1.2 is a GlobalPlatform-approved test suite, which is part of the GSMA Consumer and IoT eSIM compliance programmes and referenced in GSMA’s eSIM Test Specifications (SGP.23 and SGP.33) – the dedicated, globally-backed remote SIM test specifications for Consumer and IoT. Work is currently ongoing in TCA to develop the test specification for Interoperable Profile Package Technical Specification v3.4.
AtlasIED, a pioneer in the security and commercial audio industries, announces the launch of its new Rapid Alert system, which includes the IP-PB wearable panic button and the IP-RC BLE-controlled relay board. This system is designed to enhance emergency communication and integrates seamlessly with AtlasIED’s IPX IP Endpoints, providing immediate accessibility to trigger notifications during critical events. Improving response times The IP-PB panic button is worn on a lanyard and connects wirelessly to the IP-RC relay board via Bluetooth Low Energy (BLE). In emergency situations, users can press the panic button to activate notifications, including pre-programmed alerts that play throughout the facility. These notifications can be distributed through InformaCast or Revolution, ensuring that relevant personnel are promptly informed of the incident. “The Rapid Alert system represents a remarkable advancement in enhancing emergency response capabilities,” said Michael Peveler, VP of Sales for AtlasIED, adding “By integrating reliable wireless communication with our IPX Series, the system ensures quick and effective responses during critical situations. With the new panic button, an immediate and coordinated reaction can be initiated, significantly improving response times and emergency outcomes.” Reliable wireless connection The IP-RC BLE-controlled relay board connects directly to the IPX Series control boards The system is composed of two core components. The wearable IP-PB panic button utilises BLE 5.0 Ultra Wide Band communication to provide a reliable wireless connection. It features a lithium-ion battery with a lifespan of up to three years and is IP67 rated, making it both durable and resistant to environmental factors. The IP-RC BLE-controlled relay board connects directly to the IPX Series control boards and offers two relay closures that can be configured to trigger specific actions across the network. This capability enables users to initiate customised notifications for different emergency scenarios. Multiple activation sequences The system is designed to support multiple activation sequences to meet different response protocols. A quick double press of the button on the IP-PB activates one relay, while six or more button presses can automatically trigger a lockdown and immediately notify stakeholders and responders. This customisation of emergency responses offers exceptional flexibility. The Rapid Alert system integrates easily into existing AtlasIED IPX Series devices, ensuring seamless operation across various commercial environments and further proving the capability of AtlasIED’s Security Technology Solutions Ecosystem. It is ideal for schools, hospitals, industrial facilities, and corporate offices, where clear and timely communication is crucial during emergencies. The addition of the IP-PB enables AtlasIED to become Alyssa’s Law compliant, meeting the legislative requirements implemented in select states. The IP-PB wearable panic button and IP-RC relay board are now available.
Illumio, the breach containment company, announced the launch of Illumio Insights, the industry’s first cloud detection and response (CDR) solution powered entirely by an AI security graph. A key part of Illumio’s breach containment platform, Insights can observe and protect every workload and resource, spanning hybrid and multi-cloud environments. It provides AI-powered observability into the organisation’s traffic, flows, and connections, surfacing risk throughout the connected landscape. Illumio Insights SOC analysts Threats can be dynamically quarantined, with impacted workloads fully isolated, reducing the blast radius Illumio Insights helps SOC analysts, incident responders, and threat hunters uncover hidden risks by observing all flows and connections and discovering risky, malicious, and anomalous activity. Insights visualises dangerous traffic and behaviour and prioritises lateral movement risks across environments, enabling rapid detection and response. Threats can be dynamically quarantined, with impacted workloads completely isolated, reducing the blast radius and significantly boosting resilience. Key benefits of Illumio Insights Rapid Cloud-Scale Deployment: Push-button, agentless deployment delivers AI security graph-powered insights across millions of workloads in minutes. Unmatched Threat Detection with AI Observability: Significantly reduces the mean time to detect (MTTD) by uncovering unseen threats and attack paths. One-Click Attack Containment: Immediately neutralises potential risks and reduces the mean time to respond (MTTR) with one-click containment. AI-driven Illumio Insights analytics pipeline “When an organisation is under attack, understanding the connectivity graph is crucial. Bringing together the Illumio security graph with the AI-driven Illumio Insights analytics pipeline allows organisations, for the first time, to understand how threats and risks are moving through their environment. This is the power of an AI security graph,” says Andrew Rubin, CEO and Founder of Illumio. “Illumio Insights is vital for protecting the environment as it offers unparalleled observability to understand threat and malicious activity in the cloud. Illumio Insights connects the dots and finds every needle in every haystack. When integrated with Illumio Segmentation, breaches are contained and cyber disasters avoided.” Illumio’s AI security graph Illumio’s AI security graph enables Insights to ingest network flow and resource data at cloud scale Illumio’s AI security graph enables Insights to ingest network flow and resource data at cloud scale, automatically classify traffic and resources, and immediately find the risk. The graph helps security teams to form a complete picture of attacker movement across the entire environment and drives faster, more informed response decisions. AI-powered security graphs "As the cybersecurity landscape continues to evolve, it's no longer about having more technology — it's about having smarter, more adaptive solutions. The need for intelligent systems has never been greater, and AI is at the heart of this transformation,” said Frank Dickson, group vice president, Security and Trust at IDC. “AI-powered security graphs are a game-changer, enabling businesses to proactively identify, assess, and mitigate risks in near real-time. These sophisticated tools streamline security efforts and enhance decision-making by learning from patterns and behaviours, offering a level of insight and protection that traditional offerings simply can't match." Illumio Insights and Illumio Segmentation Illumio Insights and Illumio Segmentation are integral components of the Illumio Platform According to Thomas Vavra, manager, Network & Security Operations, Mondi Group, “Illumio Insights will give us real-time visibility and control over our risky ports, significantly reducing our risk exposure and improving compliance with industry standards. This will enable us to quickly identify vulnerabilities and address them before they become threats.” Illumio Insights and Illumio Segmentation are integral components of the Illumio Platform, the first cybersecurity platform focused on breach containment. Overall cyber resilience Illumio Insights helps organisations quickly identify and detect threats, while Illumio Segmentation contains breaches, protects critical assets, and enables instant response. Together, these solutions help identify and mitigate risks, contain attacks, and enhance overall cyber resilience. To see a demo of Illumio Insights, and to learn more about Illumio’s breach containment offerings, stop by the Illumio booth (North Hall #5670) at RSAC in San Francisco April 28-May 1.
Hailo, the pioneering provider of edge AI processors, will demonstrate smart security cameras empowered by its vision processing units (VPUs) as well as video management systems empowered by its AI accelerators at ISC West 2025 in Las Vegas, Nevada at booth #31065 of the Venetian Expo. At the heart of Hailo’s showcase is its full suite of AI processors, including the Hailo-15 vision processors, which integrate seamlessly into pioneering security cameras to deliver superior image quality and real-time analytics. Generative AI applications Its powerful AI capabilities enhance image quality while also efficiently handling multiple complex classic and generative AI applications at full scale. Alongside them, the Hailo-8 and Hailo-10 AI accelerators, selected by the world’s top security brands, power video management systems and other next-generation applications that require high-performance AI at the edge. What’s possible in AI for security Hailo will also demonstrate some of the industry’s most advanced models running entirely on camera Pushing the boundaries of what’s possible in AI for security, Hailo will also demonstrate some of the industry’s most advanced models running entirely on camera, at low power and independent of cloud connectivity. Demonstrations include zero-shot classification for real-time image search and query, and Vision-Language Models (VLMs) for automatic video captioning. Visitors will be able to experience edge-deployed chatbots powered by LLMs such as DeepSeek-R1 operating offline and locally on-device, ensuring privacy and security without compromising on AI capabilities. Advanced video analytics “As AI continues to revolutionise security and surveillance, Hailo is at the forefront, delivering the most widely deployed edge AI processors to a vast community of thousands of developers,” said Orr Danon, CEO of Hailo. “By removing compute limitations, we are enabling smart cameras to feature both best-in-class image quality and advanced video analytics, making security systems more intelligent, efficient, and responsive than ever before.” Hailo’s leadership in edge AI Hailo’s leadership in edge AI is further reinforced by the cutting-edge solutions showcased in cooperation Hailo’s leadership in edge AI is further reinforced by the cutting-edge solutions showcased in cooperation with its partners at the booth. Demonstrations include a Digital Watchdog VMS integration, real-time facial anonymisation by AlgoFace, AI-powered crowd and drive-through monitoring for retail applications by AT&T and Capgemini, live video stream analysis using semantic segmentation on a Dell 3200 gateway, and a Deep Perception analytics solution running on an HP Engage Flex Mini G2 connected to a Milestone VMS, among others. Hailo’s processors unmatched AI performance Hailo’s processors deliver unmatched AI performance in terms of both power-efficiency and cost-efficiency, making it the go-to choice for security solutions providers, ranging from low-power smart cameras to large-scale video management systems. With hundreds of customers and tens of thousands of developers driving innovation on its platform, Hailo continues to set the standard as the #1 edge AI processor provider, powering the future of AI-driven security. To experience the next generation of edge AI in action, and for more information, visit the website and stop by Booth #31065 at ISC West 2025 between April 2 and April 4, 2025.
As Taiwan's security industry continues to evolve with technological advancements and increased diversification, various vertical markets are poised for significant growth. Secutech, scheduled for 7–9 May 2025 at the Taipei Nangang Exhibition Centre, aims to capitalise on this burgeoning demand. Around 400 international and local exhibitors are set to showcase the latest technologies and solutions across six zones and pavilions at the fair, which serves as a vital platform to connect security and fire safety suppliers with key industry players in Taiwan. Demand for upgrading equipment and systems AIoT landscape is reshaping mixed industries and driving an increasing demand for upgrading kit Recent reports indicate that Taiwan's security market is projected to compound at an annual rate of 6.6%, reaching an estimated USD 119.9 million by 2029. At the same time, the artificial intelligence of things (AIoT) landscape is reshaping various industries and driving an increasing demand for upgrading equipment and systems aimed at improving fire and safety efficiency. Affected settings include hospitals, industrial sites, parking facilities, old buildings, factories, shopping malls, and energy storage facilities. Security and fire safety equipment Exhibitors at Secutech 2025 will be integral to this wave of advanced technology, showcasing the integration of 5G, AI, and IoT in security and fire safety equipment for real-time monitoring, predictive analytics, and automated responses, ensuring higher efficiency and safety across multiple industries. The 26th edition will welcome prominent international brands in the global security landscape, including NetworkOptix, Panasonic, Blazecut Group, and Mabu Valley Outdoor Ltd. Key local exhibitors With Taiwan's longstanding reputation as one of Asia-Pacific’s technological hubs and its expanding influence in high-tech industries, major Taiwanese manufacturers are pivotal players in the global security manufacturing space. At the show, key local exhibitors will feature their advanced technology, including: TDV - Triple Domain Vision Co Ltd will showcase advanced front-end intelligent video analytics to enhance surveillance effectiveness and operational efficiencies. Avadesign Technology Co Ltd will display a comprehensive suite of security monitoring and management services, focusing on IP video intercom and house automation solutions. Formosa Plastics Corporation is set to modernise information chains and applications with smart workplace safety management platforms, facial recognition access controls, electronic fence detection technologies, and security monitoring dashboards. Himax Technologies Ltd will exhibit cutting-edge image processing technologies tailored for security applications, including CMOS sensors, wafer-level optics for AR devices, 3D sensing technologies, and ultralow-power AI image sensing technologies. Vivotek will showcase a range of IP surveillance products and solutions driven by advanced AI algorithms, supported by a one-stop monitoring cloud platform. Marson Technology will present high-quality barcode scanning equipment along with complete OEM/ODM services. Exploring key industry trends for diverse applications This year’s show will feature six zones and pavilions, where key manufacturers will showcase their innovative solutions, aiming to capture critical trends across various vertical industries. These areas create a comprehensive environment for exploring cross-sector sourcing and collaboration opportunities: AI Innovation Application Zone (Transportation / Logistics / Retail) SmartHome and Building Pavilion Security and AIoT Smart Security Pavilion Smart Factory, Industrial Safety and Sanitation Application Pavilion Innovative Fire Prevention and Protection Technology Application Pavilion ESG Total Solution Pavilion Adoption of AIoT drives information security innovations Taiwan’s emphasis on data security grows increasingly critical, evidenced by calls to enrich digital security As AIoT evolves alongside the security market, Taiwan’s emphasis on information security grows increasingly critical, evidenced by government calls to enhance digital security and recent information security sector growth forecasts. The upcoming show will also showcase innovative information security technologies from renowned exhibitors, including InfoKeyVault Technology and Infineon Technologies Taiwan, aiming to advance solutions that address emerging threats and enhance data protection across smart manufacturing, smart home technology, and healthcare industries. Secutech sharing insights for fairgoers In this landscape, Secutech serves as an essential platform, facilitating business connections and sharing insights for fairgoers to stay ahead in a dynamic market. Secutech is organised by Messe Frankfurt (HK) Ltd – Taiwan Branch and is part of a global network of Safety, Security, and Fire trade fairs.


Expert commentary
March is Women in Security Month, a time dedicated to celebrating and promoting the contributions of women in the security field—particularly in cybersecurity. This observance aligns with Women’s History Month, providing an opportunity to reflect on the progress made and the work still needed to advance gender equity in security. Evolving role of women in security The security industry has witnessed a steady increase in women's participation. According to ISC2 Research in its “Women’s Role in Filling the Workforce Gap” report, women make up an estimated 20 to 25 percent of the security industry. Promisingly, younger generations are entering the profession at higher rates, with 26 percent of working professionals under 30 identifying as women. The security industry has witnessed a steady increase in women's participation The research tells us that women are thriving in a variety of roles, from engineering and system administration to sales, marketing, and project leadership. Key factors driving this transformation include mentorship programs, male allies advocating for gender equality, and cultural shifts recognising the unique perspectives and strengths women bring to security challenges. These efforts are fostering more inclusive environments and ultimately strengthening the industry. The value of diverse perspectives in security Security is not a one-size-fits-all industry—each organisation and facility has unique needs that require varied perspectives. Greater representation of women has introduced fresh approaches to problem-solving, fostering collaboration and driving innovation. By integrating diverse viewpoints, security professionals can create more effective solutions that better address end-user needs. Industry support for women’s professional growth SIA's WISF offers subcommittees such as NavigateHER, SupportHER, and UpLiftHER Organisations like the Security Industry Association (SIA) and ASIS International have established networking platforms and initiatives to support women in security. Events such as the Security LeadHER Conference provide valuable professional development and networking opportunities. Companies are also investing in science, technology, engineering, and mathematics (STEM) initiatives, hands-on training, and recruitment programs to attract more women into the field. Additionally, SIA's Women in Security Forum (WISF) offers subcommittees such as NavigateHER, SupportHER, and UpLiftHER, which provide pathways for engagement and growth. Challenges women in security face Despite progress, challenges remain. Many women still feel it necessary to repeatedly prove their expertise, take on additional informal responsibilities, or carefully navigate workplace dynamics. Imposter syndrome can be another hurdle, even for accomplished professionals. However, women in security are addressing these challenges by setting boundaries, advocating for themselves, and supporting one another through mentorship. By excelling in leadership and technical roles, women are reshaping outdated perceptions and advocating for more inclusive workplace policies. Steps industry pioneers can take To further support women in security, industry pioneers could: Provide targeted professional development and career advancement opportunities. Foster strong, supportive communities that recognise and mentor women. Implement structured mentorship programs that connect experienced professionals with newcomers. Promote workplace flexibility to help employees balance personal and career commitments. Actively challenge biases and advocate for meaningful change within organisations. Advice for women entering the security field Here are key pieces of advice for women considering a career in security: Own Your Expertise – Have confidence in your knowledge and skills. Seek Out Mentors & Allies – Connect with supportive professionals who can guide your career. Build a Strong Network – Join organisations like ASIS Women in Security, SIA Women in Security Forum, or Women in CyberSecurity (WiCyS), and attend industry events to expand your connections. Speak Up & Take Space – Confidently share your ideas and challenge outdated norms. Develop Resilience & Advocate for Yourself – Push past biases, demand the respect you deserve, and negotiate for fair salaries and promotions. Keep Learning & Stay Ahead – Continually build your expertise to stay competitive in the evolving security industry. The future of women in security As the security industry evolves with technological advancements and global changes, opportunities for women will continue to expand. Women are not just participating in the industry’s growth—they are shaping its future. With growing mentorship programs, male allies advocating for gender equality, and ongoing cultural shifts, the focus is no longer just on breaking barriers but on building bridges to new opportunities.
Technology advances in the security industry are transforming the way modern systems are designed and installed. Customers today are looking for greater scalability and flexibility, lower up-front costs, and operational efficiency. Cloud-based software as a service (SaaS) solutions, AI-enhanced tools, and IoT-enabled sensors and devices are increasingly in demand. The traditional role of the systems integrator is evolving as a result. While security integrators have always worked closely with end users, today’s pioneers go beyond installation and maintenance. They align security strategies with evolving business needs, integrating IT, cybersecurity, and data-driven insights into their offerings. A look at the past and present Integrators are often asked to help tailor solutions and provide expertise in IT and cybersecurity Traditionally, systems integrators specialised in installing and maintaining wired physical security systems like CCTV, access control, and alarms. The service model was built around large, up-front investments and project-based installations. However, today customers are seeking comprehensive solutions. They’re looking to wirelessly integrate security infrastructure with cloud-based SaaS systems and IoT devices. While modern systems are often faster to deploy, they’re most effective when supported by ongoing consulting and strategic planning. Integrators are often asked to help tailor solutions and provide expertise in IT and cybersecurity. Data requirements and modern systems Data requirements have also changed. Modern systems collect vast amounts of data. Advanced analytics, machine learning, and automation are now must-have tools for actionable insights. Security integrators can help end users set up custom dashboards, automations, and continuous system optimisation. Let’s look at some of the specific ways the role of systems integrators is evolving and how to adapt and succeed. Strengthen your IT expertise Integrators with IT expertise can ensure that hardware is optimised and maintained for peak performance The competitive landscape today includes not just security specialists but also IT-focused integrators and SaaS providers. Systems integrators with expertise in traditional physical security solutions plus IT experience offer unique value. They understand the real-world security challenges and opportunities, along with cybersecurity and network best practices. Integrators with IT expertise can also ensure that hardware is optimised and maintained for peak performance. Their experience with legacy systems allows them to offer practical recommendations on cost-effective approaches, such as upgrading or integrating older hardware with new digital solutions. Consider who’s making the purchase decisions Traditionally, security integrators primarily sold to security directors, facility managers, and operations teams. Now, multiple stakeholders may be involved in decision-making. IT teams, CIOs, and CTOs often weigh in on purchase decisions when cloud-based security and SaaS solutions are under consideration. Customers today aren’t just shopping for cameras, access control panels, alarms, and other hardware components. They’re looking for security ecosystems that can integrate with enterprise-wide IT infrastructure and business applications. When working with these different teams, consider outlining the system's return on investment (ROI). How can the solution reduce risk for various departments? Can it help improve operational efficiency or reduce the time required to onboard and train staff? Will it make regulatory compliance easier to manage? Focus on the long-term value for the entire organisation. Take a consultative approach Another way systems integrators are adding value is by offering vertical specialisation Installation fees remain important for many integrators, but there may be additional consultative opportunities to build long-term relationships with customers. Offer services such as roadmap planning, hardware and integration maintenance, training to certify end users on the manufacturer’s product, and cybersecurity services. While cloud-based solutions reduce on-premises maintenance, they don’t eliminate the need for ongoing support and training. Consider offering training opportunities. These can lead to other benefits as well. Better-educated and technically proficient customers are usually more willing to adopt new technologies. They understand the value of these investments and have more confidence that they’ll see results. Another way systems integrators are adding value is by offering vertical specialisation. Healthcare, sports venues, critical infrastructure, education, retail - each specialty has its own set of challenges, partner networks, regulatory restrictions, training needs, and business requirements. Integrators who specialise are uniquely positioned to offer key sector-specific insights that are invaluable to their clients. Embrace the cloud A key growth area for integrators is supporting customers in their shift to cloud deployments. Cloud solutions aren’t a one-size-fits-all solution. Each organisation is evaluating options and deciding whether cloud, hybrid, or fully on-prem solutions are the right fit for its unique needs. A key growth area for integrators is helping clients in their shift to cloud deployments Helping customers navigate and adopt cloud or hybrid solutions opens new opportunities to expand your business and deepen your relationship with your customers. Systems integrators who sell cloud solutions have the opportunity to add new layers to services for more value for customers. With a cloud solution that's easy and fast to deploy and managed and maintained by the provider, you can reduce overhead costs, staff training, and truck rolls via remote customer support. These benefits also allow you to spend time developing greater expertise in your customers’ processes. Using this knowledge, you can tailor your services towards potential productivity gains for your customers and turn them into additional sales. You ensure that your customers get the most out of the technology that’s available and that they have already purchased. Highlight your focus on cybersecurity Cybersecurity is no longer solely an IT department's responsibility. While dedicated IT security teams may still handle broader network defense, integrators play a crucial role in securing access control, surveillance, and IoT devices within a security framework. If unsecured, these devices can provide an entry point for cyber criminals to gain access to an organisation’s network. Cybersecurity is no longer solely an IT department's responsibility To best protect end users from cyberattacks, choose physical security systems with built-in security and privacy-by-design features. Help customers implement best practices to ensure their entire ecosystem is designed, built, and managed with end-to-end security in mind. Once implemented, work with your manufacturers, consultants, and end users to ensure that vulnerabilities are identified and mitigated. Every person on the network plays a role in keeping cyber threats at bay. Lean into the power of partnerships In today’s complex and dynamic security landscape, choosing the right technology partners is crucial. Ask potential partners to share their technology roadmap, and how you can offer feedback or participate in discussions about industry trends. Ideally, your partners will have a program in place to get input from integrators and end users, so they can develop products that are designed to address their most pressing issues and concerns. Your manufacturer partners should be working to help identify the evolving needs of customers and communicate these insights to systems integrators. Seek partners who actively support integrators to understand how security is evolving In addition to a good experience for the end user, strong manufacturer partners also offer solutions to streamline and automate workflows for integrators. It should be easy to order and check your shipping statuses online, for example. These are simple things that save you time and demonstrate your partner’s care for your business. Seek partners who actively support integrators to understand how security is evolving. While training is often offered on-site, some companies are now also offering blended learning models so integrators and their technicians can reduce classroom time and stay out in the field. Evolution is an opportunity Security integrators with traditional physical security expertise remain indispensable because they understand real-world risks and regulatory requirements. They can provide hands-on system deployment and optimisation. Now, there are new opportunities to build long term customer relationships. As the physical security industry undergoes this profound shift, adaptation is key. By embracing cloud and hybrid solutions, integrators can unlock new revenue streams, enhance customer relationships, and stay ahead of technological advancements. With the right partnerships and a forward-thinking mindset, systems integrators can navigate this transformation and take advantage of new opportunities being presented by evolving technology. Leverage your deep industry experience while upskilling in cloud, cybersecurity, and IT. The strongest approach is for end users, systems integrators, IT specialists, and manufacturers to work together to navigate industry changes.
A survey conducted by Blackhawk Network finds the average shopper plans to spend almost half of their holiday budget to buy gift cards this year versus only 39% in 2023. The global gift card market was valued at $1.3 billion USD in 2023, and it is projected to reach more than $5.2 billion USD by 2032. Fraud - a growing concern While gift cards continue to be top of mind for consumers for streamlined gifting, gift card fraud is a growing concern for consumers and businesses alike. According to the U.S. Department of Homeland Security’s Homeland Security Investigations (HSI) unit, gift card fraud, perpetrated by Chinese and other organised retail theft (ORT) rings, can be attributed to losses in the hundreds of millions of dollars globally, and is being used to fund other illicit crimes such as drug and human trafficking. The retailers implement procedures to mitigate attacks. Using data insights to detect emerging threats and identify hidden connections is among the ways retailers can protect the integrity of their gift card programs. How gift card fraud is manifested Typical physical gift card scheme involves purchasing items using stolen credit cards Gift card fraud occurs both at physical locations and online. A typical physical gift card scheme involves purchasing items using stolen credit cards and then returning the items for store credit or gift cards. While some stores have strict and well-enforced return policies to ensure that only customers entitled to refunds receive them, fraudsters employ fake tracking ID (FTID) tactics that focus on bypassing identification checks during returns, enabling them to return stolen merchandise or exploit refund policies. They use a combination of fake IDs and altered receipts or rely on lax return processes to achieve their goals. Once gift cards are obtained, criminals can sell them at a discount or use them for personal purchases, effectively converting stolen goods or false claims into untraceable funds. Tactics to convince consumers One tactic involves draining a gift card by obtaining the barcode, Card Verification Value (CVV) number, personal identification number (PIN), or activation code from beneath the slim cardboard packaging. Once they obtain the code(s) from physical cards, they reseal them, monitor online for consumers to buy and load the cards, then spend the balances before the consumers can. Some merchants have sought to combat this by keeping store-branded gift cards behind the checkout counter, handing them out after purchase. However, this approach can be costly and inconvenient for both retailers and customers, as it requires additional resources for in-store management and potentially slows the purchasing process. Other online tactics involve people who misrepresent themselves in a variety of phishing scams to convince consumers to purchase gift cards, then provide the card details to others who then drain the cards. Scammers tell the victim which gift card to buy (and where). They might say to put money on a card for an online store, a streaming service, or a specific retail store. These scammers often work as part of an organised crime network. Retailers leveraging open info, AI, to combat gift card fraud Retailers are empowered to improve the monitoring and analysis of gift card transaction patterns A growing number of retailers are leveraging publicly available (PAI) and hard-to-reach data and analytics to extract key insights that help fight various forms of gift card fraud and stay ahead of evolving fraud tactics. With such tools, retailers are empowered to improve the monitoring and analysis of gift card transaction patterns, identify anomalies, and implement proactive measures to prevent fraudulent activities before they can impact consumers and sales revenues. Retailers need this type of approach in their efforts to battle scammers, who continue to refine tactics for draining gift cards and committing other types of retail fraud. Beyond simply refining their techniques, fraudsters continue to advance their use of technology to commit their crimes. For example, cybercriminals also use bots to perform brute-force attacks on gift card websites. They are increasingly using AI to perpetrate gift card fraud. Leveraging Latest AI And LLMs Retailers need to continually upgrade their fraud-fighting strategies and technologies as well. They can lean into PAI and analytics, in conjunction with existing security operations and investigations, to safeguard the integrity of their gift card programs and demonstrate their commitment to customers, reinforcing brand trust. In addition to leveraging the latest versions of AI and large language models (LLMs), retailers can take advantage of open-source intelligence (OSINT). By leveraging PAI and difficult-to-obtain data with analytics, brands are using OSINT to more quickly seize on evolving threat patterns to recognise current and shifting fraud schemes and stay ahead of evolving fraud tactics. In this way, the AI operates as a resource multiplier, compiling and processing data at faster-than-human speeds, while enabling the ability to extract actionable insights at scale. Users can make more accurate and timely decisions. Retailers need to upgrade their fraud-fighting strategies and technologies. Safeguarding gift cards, customer trust, and brand integrity OSINT can inform retail security managers, loss prevention directors, fraud investigators, and others to help spot and deter gift card fraud. By using AI to detect patterns and anomalies, OSINT solutions can help fraud specialists spot patterns of suspicious activity that may indicate distinct instances of fraud. AI further helps fraud specialists identify members of ORT rings by uncovering hidden connections among seemingly unrelated individuals and transactions. The market for retail gift cards is large and continues to grow, and so too, is the gift card fraud threat. By adopting OSINT for fraud prevention, retailers can stay ahead of tech-savvy criminals, safeguarding gift card revenue streams, as well as customer trust and brand integrity.
Security beat
Big news on the mergers and acquisitions (M&A) front is closing out 2024, a year in which several shifts changed the face of the physical security manufacturer community. Announced in December, German giant Bosch Group is selling its Building Technologies division’s product business for security and communications technology to the European investment firm Triton. Bosch division selling to Triton The transaction encompasses three business units – Video, Access and Intrusion, and Communication – and thus the entire product business of Bosch Building Technologies that was offered for sale. All 4,300 associates employed in these units at more than 90 locations worldwide will be taken over. The transaction reflects a growing confidence in the security market among private equity companies such as Triton, Becklar, and Volaris. Sharing best practices Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership Acre Security, previously acquired by Triton, has benefited from Triton’s strategic guidance and expertise, according to the company, which is confident Bosch will experience the same level of support and opportunity to thrive. Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership, but will benefit from the potential to collaborate and share best practices as part of the broader Triton portfolio. Resideo acquires Snap One Earlier in 2024, there were other large M&A transactions. In the spring, Resideo Technologies, Inc., a manufacturer and distributor of technology-driven products and solutions, agreed to acquire Snap One Holdings Corp., a provider of smart-living products, services, and software to professional integrators. The transaction is valued at $1.4 billion, inclusive of net debt. Upon closing, Snap One becomes part of Resideo's ADI Global Distribution business. Honeywell buys Carrier’s Access Solutions In late 2023, Honeywell announced plans to enhance and strengthen its building automation capabilities with the acquisition of Carrier Global Corporation’s Global Access Solutions business for $4.95 billion, in an all-cash transaction. The acquisition, which played out through 2024, includes both hardware and software solutions, adding three respected brands to Honeywell’s portfolio with a focus on life safety and digital access solutions. Acquired brands include LenelS2, commercial and enterprise access solutions; Onity electronic locks; and Supra cloud-based electronic real estate lock boxes. Hirsch reemerges as an iconic brand The Identiv sale was originally announced in April, subject to regulatory approval Identiv announced plans to sell its physical security business and assets to Vitaprotech, the security solutions provider that also acquired British manufacturer, TDSI, in 2019. The Identiv sale was originally announced in April, subject to regulatory approval. As a result of the sale, Hirsch, a global security technology pioneer advancing physical security, video intelligence, cybersecurity, and digital identification solutions, announces the relaunch of its iconic brand and strengthened focus on the industry’s most complete high-security, end-to-end platform. Ease of use security solutions The move seeks to reposition Hirsch as the global pioneer in physical security, video intelligence, and identity solutions, protecting everything from small enterprises to critical national infrastructure. With a 43-year-strong foundation in the industry, Hirsch’s mission has always been empowering a secure, connected world, combining government-grade high security with ease of use. Milestone and Arcules unite Effective July 1, 2024, global video technology company Milestone Systems announced its merger with the cloud-based video surveillance solutions provider, Arcules. Both companies are owned by Japanese multinational Canon Inc. Based in Irvine, Calif., Arcules was spun off from Milestone in 2017. The merger brings together Milestone and Arcules’ best-in-class capabilities within video management software (VMS), video analytics, and video surveillance as a service (VSaaS), providing a complete video technology offering. More M&A stories in 2024 In other M&A moves in 2024, cloud-based workforce management software provider Synerion USA Inc. acquired cloud-based video surveillance and access control solutions platform Qumulex Inc. Also, the global pioneer in airspace awareness and security, Dedrone, became part of the public safety and technology company Axon. The acquisition unites two companies with a shared mission to improve public safety and national security by staying ahead of persistent and escalating threats, enabling faster, more effective responses and ultimately protecting more lives in more places.
The information age is changing. Today, we are at the center of addressing one of the most critical issues in the digital age: the misinformation age. While most awareness of this problem has emerged in the consumer and political worlds, the issue cannot be ignored when it comes to the authenticity and protection of video and security data. Video surveillance data SWEAR is a company with the mission to ensure the integrity of video surveillance data by mapping video data and writing it into the blockchain, providing real-time, immutable proof of authenticity. Blockchain, which is the underlying technology that enables cryptocurrencies, is a decentralised digital ledger that securely stores records across a network of computers in a way that is transparent, immutable, and resistant to tampering. SWEAR solution The SWEAR solution is based on proactive, foundational protection that validates data at the source The SWEAR solution is based on proactive, foundational protection that validates data at the source before any opportunity for manipulation can occur. “Our technology is about proving what’s real and our goal is to ensure that security content and video surveillance data remain untampered with and reliable when needed,” says Jason Crawforth, Founder and CEO of SWEAR. Real-time authentication Security leaders need to ensure that the content they are relying on to make mission-critical decisions is authentic. Once verified, organisations can be sure that their investment in video can be trusted for critical use cases, including intelligence operations, legal investigations, and enterprise-scale security strategies. SWEAR seeks to embed trust and authenticity directly into video surveillance content at the point of creation. This ensures real-time authentication while proactively preventing tampering or manipulation before it can happen. AI-generated content The rise of AI-generated content, such as deepfakes, introduces significant challenges As AI transforms the landscape of video surveillance by enhancing threat detection and predictive analysis, it also introduces the very real risk of manipulation through AI-generated content. This presents a significant challenge in protecting critical security data, especially in mission-critical applications. The rise of AI-generated content, such as deepfakes, introduces significant challenges when it comes to ensuring the protection of digital media like video surveillance. Recent study findings It is a fact that digital media content is being questioned more regularly, which puts businesses, legal systems, and public trust at risk. A recent study from the Pew Research Center found that 63 percent of Americans believe altered videos and images create significant confusion about the facts of current issues. Last month, California Governor Gavin Newsom signed three bills aimed at curbing the use of AI to create fake images or videos in political ads ahead of the 2024 election. Footage authenticity “While most of the news cycle has centered on the use of fake content in politics, we need to think about how manipulated videos could affect security,” says Crawforth. “In video surveillance, ensuring the authenticity of footage is critical for keeping operations secure and safe around the world. That means verifying and protecting video data is a must.” Organisations must be capable of performing thorough digital investigations, which involve retrieving and analysing video and security data from devices and networks through a chain of evidence. Digital forensic capabilities Strong digital forensic capabilities also enhance incident response, risk management, and proactive security An in-depth understanding of who has handled video data, how it was handled, and where it has been is an important step in responding to security incidents, safeguarding assets, and protecting critical infrastructure. Strong digital forensic capabilities also enhance incident response, risk management, and proactive security measures, all essential for risk management, regulatory compliance, and cost control, says Crawforth. An unbroken chain of custody “By using tools to identify, preserve, and analyse digital evidence, organisations can ensure swift and accurate responses to security incidents,” he adds. “Using the latest tools and techniques is vital for maintaining a strong security posture." "But you must ensure your digital content isn’t manipulated.” SWEAR’s technology provides an unbroken chain of custody, ensuring that video evidence can be trusted and admissible in court and forensic applications. Authenticating content Authenticating content also strengthens accountability and trust, protecting organisations By verifying video content is protected from tampering, manipulation, or forgery, organisations can be sure that they have reliable evidence that produces actionable results. Authenticating content also strengthens accountability and trust, protecting organisations from legal disputes or compliance violations. Safeguarding digital content “With an increasing amount of disinformation in today’s world, we sought to develop an innovative solution to safeguard the integrity of digital content,” says Crawforth. SWEAR safeguards security content using real-time “digital DNA” encoding. It integrates directly at the video management system level, ensuring it is preserved with a secure chain of custody and maintains integrity for evidentiary purposes. Real-time “digital DNA” encoding The digital DNA is then stored on a blockchain, creating an immutable record The solution integrates with cameras and other recording devices to map this digital DNA of the video data, all in real-time. The digital DNA is then stored on a blockchain, creating an immutable record that tracks the content’s history and integrity. Any attempt to manipulate the media can be instantly detected by comparing the current state of the media to its original, authenticated version. SWEAR is actively collaborating with video management solution providers to integrate the technology into their platforms. Video and security data benefits “We’re still in the early stages of our collaboration in this space, but it is clear that the industry recognises that we have to work together to mitigate this risk proactively before it becomes a significant issue,” says Crawforth. “The feedback we have received from the industry to date has been beyond our expectations, and we expect to have more integration partners to highlight shortly.” “We should approach this as a collaborative effort across the industry, as ensuring the authenticity of video and security data benefits everyone involved,” says Crawforth.
Security professionals are recognising the intelligence value of leveraging publicly and commercially available information. This information can now be accessed more effectively from typically hard-to-reach regions. Also, the technological capabilities have matured in our age of artificial intelligence, machine learning, and data science. Intelligence has historically been based on classified data. However, today’s unclassified data, including open-source intelligence (OSINT), is increasingly being used to provide context and queuing for other types of intelligence. Advanced identity intelligence Babel Street is a technology company providing advanced identity intelligence and risk operations using an AI-enabled data-to-knowledge platform to unlock insights from a flood of data. The company provides advanced data analytics and intelligence for the world’s most trusted government and commercial organisations. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally The sheer volume of data is growing exponentially. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally. Not only are we seeing exponential growth in the volume of data, but there is also disparity in the veracity and the variety of data. This is being compounded by the ‘app economy’ in which data is created in a new format for every app added around the globe. Human language technology “The problem is that the data ‘junk’ and the ‘crown jewels’ are in the same bucket, and government and commercial entities need better and faster ways to extract intelligence from these torrents of data,” says Farid Moussa, VP, Strategy & Public Sector, Babel Street. Prior to joining Babel Street, Farid retired from the National Security Agency (NSA). He has guided video, image, speech, and text analytics (VISTA) and developed an appreciation for human language technology. An elusive source of data is the Dark Web, where every user, by design, is attempting to obfuscate their identity, and bad actors are hiding much better. “This presents a cat and mouse game – the cat must be smarter than the mouse, but the mouse is continually getting smarter,” says Moussa. Intelligence tools for data analysis SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence There are several intelligence tools for analysing data. One of them is signals intelligence (SIGINT), which refers to electronic transmissions collected by ships, planes, ground sites, or satellites. Another is human intelligence (HUMINT), which is collected in a human-to-human fashion. Open-source intelligence (OSINT) is obtained by searching on topics or entities of interest that are publicly available on the Internet at large. Today, these various categories are often done in ‘silos of excellence.’ However, the best practice is using all forms together in a holistic fashion. SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence, while OSINT, which is growing in importance, is most cost-effective. All are vital forms of intelligence; OSINT is complementary and crucial to holistic intelligence practices. Holistic intelligence practices When it comes to physical security of people and places, OSINT has become a critical source of actionable information. Security directors leverage Publicly Available Information (PAI) to safeguard against threats to individuals, property, travel routes, and event sites. By monitoring PAI, security teams can detect and respond to potential dangers, including during and after events where thorough preparation is vital. Online information can contain warning signs of impending threats. It informs security professionals in uncovering digital traces, confirming intentions, and addressing risks across language barriers, ensuring proactive risk management for the protection of people and property. Role of Natural Language Processing (NLP) The Internet and social media were mostly English language by default, but that has changed exponentially Natural Language Processing (NLP) is a crucial capability that has evolved to recognise the richness and variety of words and names in multiple languages and scripts, and their use across cultures. Using machine learning and linguistics algorithms, the technology simultaneously considers numerous types of name variations. At one time, the Internet and social media were mostly English language by default, but that has changed exponentially. Babel Street’s world-class entity matching technology measures over 100 features to calculate the similarity of entities across multiple languages. Despite advances in data management and the cloud, there are still multiple challenges and complexities with integration of these data elements. Challenges include spelling variances/phonetics, language translation issues, criminal evasion, human error upon input, typos, etc. Accessing data from a scattered landscape While there have been advancements in cloud technologies, agencies utilising open-source data are typically working within a highly scattered data landscape and must use a wide array of tools to get at the relevant pieces. This fragmentation makes it difficult to run analytics and apply AI and machine learning at scale in order to derive actionable insights. Unstructured and relationship data are visualised through advanced link analysis As with many disciplines, artificial intelligence (AI) is changing the game when it comes to intelligence. NLP and AI algorithms are employed to enhance datasets for greater quality, usability, and completeness. Unstructured and relationship data are visualised through advanced link analysis, geographic heat maps, influential entity carousels, topic clouds, and patterns by time and day. Geographic heat maps The advanced algorithms accurately score and prioritise critical entities within the relationship network while providing the citations from which an AI/ML-based decision was made. “With the democratisation of AI, the world is becoming flat,” says Moussa. “Just like the most prosperous countries, even the poorest countries have the most advanced capabilities to do damage. Third-world economies often present a scenario where the financial gain of nefarious schemes and low-to-no regulation combine to incentivise bad actors.” The Challenges of Name Matching Identity has been an ongoing challenge for intelligence analysis due to the vast complexity of linguistics, spelling and cultural variances, human error, as well as human evasion. Technology and data science approaches are maturing, however machine translation can still struggle with meaning. The best-of-breed natural language processing capabilities run against the data while it still is in its native language. This minimises the occurrence of analytic errors caused by inaccurate machine translations. This minimises the occurrence of analytic errors caused by inaccurate machine translations It’s tempting to think that name matching is like doing a keyword search. The complexity of language makes it more challenging. New names are constantly created, with multiple spellings and no set of rules to encompass how names are formed. They are variable across languages, scripts, cultures, and ethnicities. Culturally specific nicknames and aliases add to the complexity. Replacing human involvement The investigation of the Boston Marathon Bombing in 2013 spotlighted an example of the significance of intelligence analysis. Even though the FBI had issued a detain alert for Tamerlan Tsarnaev back in 2011, Tsarnaev managed to travel to Russia in January 2012; and in July 2012, he returned to Boston. He was not detained on either occasion because there were too many names on the lists, and Tsarnaev’s last name had been spelled differently from the way it was on travel documents, thus enabling him to get through security. With the Internet, social media, and the dark web, there’s been an exponential increase in public communications in various languages, adding significantly to the amount of analysis required to keep societies safe. Name matching, using AI, analyses multiple contextual data points across languages to arrive at matches. Name matching, using AI, analyzes multiple contextual data points across languages to arrive at matches A common misconception is that this technology will replace human intelligence. “It’s more accurate to recognise its role as a force-multiplier, allowing humans to focus on the on the harder problems and/or vetting the results of AI,” says Moussa. “The technology can efficiently analyse massive volumes of data and distill it into actionable information in a timely manner. It augments human capabilities, enabling analysis at speed and scale beyond human capacity, without replacing human involvement.” Commercial Technology to the rescue “When it comes to threat and identity intelligence, we face a risk-confidence gap, underscored by the challenge of integrating traditional tactics with the modern digital landscape,” adds Moussa. “We cannot ‘hire’ our way out of this problem. Instead, it is imperative that we adopt technology to scale our efforts and free humans to solve the harder problems that machines cannot solve yet.” The public sector loves to build things, but there are time-to-value and return-on-investment considerations to the ‘build or buy’ decision. When commercial technology can be leveraged by government, it frees resources up to work on problems that the commercial world hasn’t yet figured out, says Moussa. “The public and private sectors need to come together – one team, one nation, working together with mutual trust and collaboration,” he says.
Case studies
Thames Valley Police worked with local authorities to improve CCTV coverage, cut costs, and boost efficiency. It’s made public spaces safer and ensured long-term, reliable monitoring across the region. Thames Valley Police is the largest non-metropolitan police force in England and Wales, covering 2,218 square miles and a population of 2.42 million people. Its jurisdiction includes multiple towns, city centres and council areas across the three counties of Berkshire, Buckinghamshire and Oxfordshire. Setting a long-term vision for public space CCTV Public space CCTV is vital in deterring and detecting crime across the Thames Valley Public space CCTV is vital in deterring and detecting crime across the Thames Valley. However, significant pressure on local authority budgets has made it increasingly difficult for councils to provide public space CCTV. There was real jeopardy that financial constraints would result in unmaintained systems, with limited or no real-time monitoring. A fresh approach was needed, so the Thames Valley CCTV partnership between Genetec™ and Hanwha Vision was formed. The first major challenge was securing funding to overhaul several local authorities’ ageing systems, which were proving increasingly expensive to upgrade and maintain. The second was to manage the ongoing costs of staffing control rooms to ensure the long-term sustainability of monitored CCTV across the Thames Valley. Ownership and monitoring of public space CCTV Ambitious plans were devised to pool resources and replace many disparate systems with one police-owned system that could extend across multiple authorities. In effect, the aim was to transfer the ownership and monitoring of public space CCTV from local authorities to dedicated Thames Valley Police control rooms. It would be led by the Thames Valley Police & Crime Commissioner (PCC) Matthew Barber, collaborating with any local authority who chose to participate. It was a feat that had never been attempted in the UK on this scale that held the potential to drive efficiencies and enhance CCTV provision in areas it might otherwise have deteriorated. Ongoing commitment and investment “CCTV is an important part of community safety; benefitting police and local communities in helping to deter crime and antisocial behaviour, identify offenders and support prosecutions." "Ongoing commitment and investment enables high quality, consistent and sustainable CCTV provision now and into the future”, explains Matthew Barber, PCC, Thames Valley. Centralisation creates area-wide visibility and control Several control rooms in the Thames Valley, like Windsor & Maidenhead, had implemented Genetec Security Centre Several control rooms in the Thames Valley, such as Windsor & Maidenhead, had already implemented Genetec Security Centre and were very happy with its operation. Furthermore, as an open platform video management system, it could minimise costs by supporting a phased unification or “takeover” of existing systems across the Thames Valley. Finally, its hybrid cloud architecture provided Thames Valley with maximal flexibility to leverage any combination of cloud or on-premises infrastructure according to Name Thames Valley Police Industries Public Safety Location Thames Valley, United Kingdom Products Genetec Security Centre; Genetec Cloud Services; Federation Technology Partners Hanwha Vision Channel Partners CDS Systems what made sense for each application and location. This made it the obvious choice on which to standardise. Range of multidirectional AI-enabled cameras Following a competitive tender, Thames Valley chose CDS Systems to implement its proposed solution. This would be built on Genetec Security Centre and incorporate a range of multidirectional AI-enabled cameras from Hanwha Vision. A key driver in the decision was the high levels of commitment shown by all three parties to cybersecurity. Another was the recognition that the system design and technology selection could ensure a cost-effective implementation that could continue to evolve in line with the needs of its users. Integration between Genetec and Hanwha Vision technology Legacy cameras were retained and reused to maximise the return on existing investment wherever possible “We urgently needed to improve the quality of CCTV, enhance collaboration, and drive efficiencies for all partners. The respective capabilities and seamless integration between Genetec and Hanwha Vision technology was the optimal way of meeting Thames Valley’s requirements,” says Sam Thomas, CDS Systems. Phase one of the deployment involved CDS taking over an existing control room in Milton Keynes, replacing the legacy analogue infrastructure with a modern IP backbone. It then installed Genetec Security Centre to establish one platform through which officers could smartly interact with all incoming video feeds. Legacy cameras were retained and reused to maximise the return on existing investment wherever possible. A second Genetec workstation was also set up inside Slough Police Station, allowing officers to rapidly review footage for improved community response. Hanwha Vision’s AI-enabled multidirectional cameras CDS then introduced Hanwha Vision’s AI-enabled multidirectional 4k cameras to improve CCTV coverage and quality in public spaces. Each of these cameras incorporates up to five cameras in one device for wide-area surveillance, which would previously have required several separate devices, simplifying installation and resulting in significantly less associated cabling and infrastructure. They also provide powerful AI analytics, including accurate object detection and classification, to enable forensic search and save operators' time when responding to incidents. For example, identifying and establishing the movement of specific people or vehicles based on attributes such as vehicle type. Thames Valley CCTV partnership Phase two will see four additional control rooms in Oxfordshire merged into a single hub Phase two will see four additional control rooms in Oxfordshire merged into a single hub inside Abingdon Police station, also built on the Genetec Security Centre. This and the control room in Milton Keynes will be interlinked, adding further resilience as each site will be able to act as a fallback for the other. At this point, there will be a dedicated team of eighteen staff responsible for monitoring CCTV and enhancing CCTV for all participating communities in the Thames Valley CCTV Partnership. Innovative and cost-effective solutions “The CCTV Command Suite enabled by CDS, Genetec and Hanwha Vision has improved our workflows beyond recognition, enabling staff to quickly review and package evidence for frontline officers or more complex investigations. It has received several plaudits from officers for its ease of use,” says Jason Owen, CCTV Operations Manager, Thames Valley Police. “This collaboration between Thames Valley Police, Genetec, CDS Systems, and Hanwha Vision showcases the power of partnership in driving innovative, cost-effective solutions that improve public safety,” says John Boorman, Head of Product and Marketing at Hanwha Vision Europe. “Our AI-enabled cameras are designed to reduce false alarms and streamline operations, ensuring teams can focus on real incidents and drive efficiency across their monitoring.” Efficiency, at a lower cost All CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers Pooling resources and transferring ownership to the police has brought about significant cost efficiencies for participating authorities, while also enhancing the quality and reliability of public spaces CCTV. Just as importantly, it has dramatically improved the police’s direct access to quality video evidence. Unlike in a traditional council-run control room, all CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers. This means they have full access to Thames Valley’s suite of police databases and reporting software packages. They are better equipped to rapidly report incidents, support front-line officers, and communicate effectively with investigators as a result. On average, it handles between 300 – 500 incidents a month and has substantially increased the number of successful requests for supporting footage. “We’ve immediately seen the benefit of our investment in equipment and CCTV operators, with the police now much better equipped to deter and detect crime across the Thames Valley,” adds Barber. A solid platform for further improvements Control room operators’ intuition will always be the driving force that brings results Looking forward, Thames Valley has plans to use the Genetec platform to connect its people and mobile surveillance assets back to its control rooms for better cross-force interaction. Genetec Federation as a Service is already allowing live and recorded video to be shared with officers in the field. Soon it will also be extended to ensure video from police CCTV vans and drones is immediately available in the control room. In both cases this is achieved without complex network configuration, requiring only an internet connection. It is also at the beginning of its journey of fully realising the value of the AI-equipped Hanwha Vision cameras specified by CDS. Control room operators’ intuition will always be the driving force that brings results, but AI is freeing them up to do what they do best by saving time on routine monitoring and searches. Cost savings, resilience, and efficiencies Finally, talks continue that would see the addition of further control rooms across the Thames Valley to the Thames Valley CCTV Partnership. Having proven the model, would allow it to scale operations further to deliver even greater cost savings, resilience, and efficiencies. “We’re proud of what we’ve achieved to date but have no intention of resting on our laurels. The foundations we’ve established will ensure continued high-quality, consistent, and sustainable CCTV provision for our communities,” concludes Owen.
Modern measurement technologies enable high-precision detection of the movement of liquids and gases - and thus provide valuable data for numerous applications. How does the air flow around an aeroplane? How does the blood move through our veins? And how can pollutant emissions in combustion processes be minimised? For this purpose, speed, direction, pressure and turbulence within a flow are analysed in order to increase efficiency, ensure safety and drive innovation in a wide variety of areas. Innovative sensor technology High-resolution cameras are used to track marked particles within a flow and analyse their movement A range of methods are available to measure these flows, including visual ones such as particle image velocimetry (PIV). High-resolution cameras are used to track marked particles within a flow and analyse their movement. iLA_5150 GmbH from Aachen (Germany) now also relies on EBIV. The abbreviation stands for Event-Based Particle Image Velocimetry and is a new optical method for the qualitative and quantitative visualisation of flows and flow velocities. It combines PIV with event-based cameras, here with a uEye EVS from IDS Imaging Development Systems GmbH. The innovative sensor technology of the industrial camera enables highly dynamic and energy-efficient detection, especially of fast and turbulent movements. Application In the EBIV method, tiny particles are added to a flowing fluid and illuminated in a plane, the so-called light section plane. They generate individual light pulses as they enter and exit the LED light section. This change in local brightness is recorded independently by the camera pixels and transmitted to the PC as a data stream of "change events". In contrast to conventional cameras, event-based models therefore only react to the changes in brightness registered in the image field. Stationary scattered light, such as background or a non-changing illuminated surface, does not generate a measurement signal. This reduces the amount of data considerably. Frame rates of up to 10,000 frames per second The data stream essentially contains information about what happens, when and where The data stream essentially contains information about what happens, when and where. In detail, these are the pixel coordinates on the sensor, microsecond time stamps of the pixel events and the information about the events: ON or OFF. This allows a distinction to be made between increasing intensity (ON event) and decreasing intensity (OFF event). Using suitable software, the stream can be converted into an image matrix in which both the spatial information and the linear time base of the stream are available. The result is comparable to the extremely high frame rate of a high-speed camera. EBIV measurement method "The EBIV measurement method differs fundamentally from conventional imaging methods. They usually generate very large amounts of data and require powerful peripherals that can process them. For exceptional frame rates of 1000 Hertz and more, the image-based cameras required are themselves very complex and expensive." "With the help of event-based camera technology, comparable frame rates of 10,000 frames per second are possible, whereby only standard PC interfaces such as USB with a few gigabits per second are required. The price of the event-based models themselves is significantly lower than that of corresponding high-speed cameras and is therefore also very interesting for smaller teaching and research institutions," explains Dr André Brunn - Head of Development at iLA_5150 GmbH. Further processing The user can optimise the display of the move paths and adapt them to unique study objectives The data stream is converted into image data and displayed in a front end - the so-called EBIV viewer - for direct online flow visualisation. The user can also select the integration time, which corresponds to the exposure time of an image camera, as well as the time increments of the sequence, i.e., the period between two consecutive shots. Classic image filters can also be used. With the help of these settings, the user can optimise the display of the movement paths and adapt them to individual examination objectives. Both fine flow details and large-scale patterns can be made more clearly recognisable. This ability to readjust the measurement results is another advantage of the event-based approach. Numerical analysis of the flow properties In the qualitative visualisation of the flow in the EBIV-View, particles are continuously illuminated so that they are visible as luminous traces. The method is therefore very well suited to visualising the flow. However, it does not provide exact measurements of its speed or direction. For a precise, numerical analysis of the flow properties, individual particles are illuminated for a moment using short, time-defined light pulses. Image sequences of the event-based camera As with classic PIV, the image sequences of the event-based camera can also be statistically analysed This allows their exact position to be recorded and their movement quantified. By comparing the particle positions in successive images, the speed and direction of the flow can be precisely calculated using PIV, for example. The result is a transient 2D vector field that changes over time - in other words, the vectors do not remain constant. As with classic PIV, the image sequences of the event-based camera can also be statistically analysed, for example, to determine mean values and fluctuations in the flow velocity. Camera and software On the camera side, iLA relies on a uEye XCP-E from IDS. The small, lightweight industrial camera offers event-based sensor technology in a robust die-cast zinc housing (29 × 29 × 17 mm) with screw-on USB Micro-B connection. It is compatible with all standard C-mount lens sizes. This makes it ideal for both industrial and non-industrial areas. The integrated event-based vision sensor (EVS) was developed by Sony and Prophesee. It is supported by the Metavision SDK, a seamlessly integrated suite of software tools and models, APIs and other training and development resources from Prophesee for efficient analysis, visualisation and customisation. Building on this, the EBIV viewer from iLA_5150/PIVTec is specially tailored to flow visualisation applications. Outlook The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions. A qualitative flow visualisation is often sufficient to understand effects and develop suitable control mechanisms. Until now, however, imaging fast flows with high temporal resolution was usually only possible with expensive high-speed cameras. Event-based camera technology offers a cost-effective alternative that requires significantly less technical effort. These “simple” methods have been lacking in teaching and research in particular. Thanks to the extreme data reduction, this technology also allows the use of several cameras or large camera arrays without the periphery becoming a limitation for data transfer. The compact design of the uEye EVS models also makes them ideal for mobile applications. This means that real application environments can be analysed directly for the first time - without having to rely on artificial flow models or channels. Established flow measurement methods Event-based cameras enable efficient, cost-effective and high-resolution visualisation and quantification of flows. Due to the small amounts of data generated, many processes can be analysed almost in real time, which also makes them interesting for use in fully automated systems. Established flow measurement methods such as Particle Image Velocimetry (PIV) can be seamlessly integrated and expanded. The technology can be used wherever flow information is captured by changes in scattered light intensity - be it from moving particles or vibrating surfaces.
Growing businesses require flexibility and easy scalability from their access management. Choosing a secure digital solution which easily adapts and grows as needs change, ensures the organisation is prepared not just for now, but for the future. H.R. Owen is a dealership specialising in the sale, service and repair of luxury and sports cars. Its portfolio of high-end brands includes Lamborghini, Bentley, Aston Martin, Rolls Royce and Lotus. Based primarily in London, the company expanded operations with a new facility in Hatfield to accommodate its growing business. As with all of H.R. Owen’s premises, this new showroom required high security due to the nature of its vehicle stock. Access management solution Unified access control solution that could encompass a wide range of openings “Security is paramount as we needed to ensure that we are not just protecting our high-value products, but also our staff and our customers,” explains Sean Nevatte, Group Aftersales Director at H.R. Owen. For the new premises, managers sought a single, unified access management solution which could encompass a wide range of openings including glass doors, fire doors and parking barriers. Investment in digital access H.R. Owen customers expect a degree of refinement in the showroom environment. So, as well as security and reliability, access devices must blend with the high-end interior design. Finally, they needed a solution which offered easy scalability. As a successful, growing company, they have to be confident their investment in digital access would meet evolving requirements for security, flexibility and aesthetics – now and long into the future. SMARTair® brings real-time control and easy scalability “During the planning stages with H.R. Owen and the architects, it was clear that ASSA ABLOY’s SMARTair solution was the only real choice for the site,” says Matthew Taylor, Operations Director at Knightsbridge Security, who installed the dealership’s system. SMARTair, part of a suite of connected digital access solutions from ASSA ABLOY, is an out-of-the-box system ideally suited to medium-sized premises with a broad range of openings to equip. Among more than 100 devices installed throughout the facility, SMARTair Wall Readers and SMARTair i-max Escutcheons were selected for their sleek aesthetics and versatility. Benefits of choosing a wireless solution The facility can manage access remotely, ensuring access rights may be monitored The devices are wireless, and therefore fast and cost-effective to fit. With no need for extensive cabling, they are quickly installed, minimising onsite disruption. Another benefit of choosing wireless, the reach of H.R. Owen’s solution can be easily extended or reconfigured anytime, protecting their investment for the long term. SMARTair is equally convenient to operate. The facility can manage access remotely, ensuring access rights may be monitored or amended in real time in response to any potential threat. SMARTair’s mobile access solution H.R. Owen also chose SMARTair’s mobile access solution Openow®: staff can use their smartphones for access, rather than physical cards or fobs. Access by secure mobile app boosts both security – fewer lost credentials – and sustainability performance by cutting single-use plastics. Particularly well suited to car showrooms and other premises with parking, Openow’s Parking Mode feature allows drivers to unlock barriers from 3m–5m away. They don’t need to get out of the car to open the barrier. This reduces the risk of opportunist theft or unauthorised access, which is a critical benefit for premises like H.R. Owen with high-value goods inside.
Richard Thorp has been fascinated with aviation since childhood. A self-described “aviation geek,” Thorp is now the Chief Technology Officer at Swissport International AG, where he leads IT infrastructure strategy for the world’s largest ground-handling company, ensuring seamless operations across 276 airports in 45 countries, handling approximately 247 million airline passengers per year, as of the end of 2024. “If we were an airline, we’d actually be the biggest airline in the world in terms of a number of passengers we support and handle,” he says. Security challenges Swissport’s goal is to make a tangible impact on people’s lives by enabling smooth air travel Swissport’s goal is to make a tangible impact on people’s lives by enabling smooth air travel. “If the things we do get people to their destinations safely and on time, then magically, we become more successful and profitable as an organisation,” he says. But casting that spell had been challenging for Swissport. Three years ago, legacy IT leadership at Swissport had overcome network challenges with Cato, but more work was needed to address their security challenges, particularly in securing endpoints. Thorp and Swissport CISO, Giles Ashton-Roberts, joined Swissport in the middle of the Cato deployment. Having deep experience with a legacy zero trust provider, they were skeptical that Cato could meet Swissport’s requirements. Cato platform Over the next 10 months of meetings, investigation, and testing Thorp and Ashton-Roberts challenged Cato, ultimately changing their perspective. “IT is no longer seen as a blocker; it just works,” says Thorp. “I relax a bit more with the Cato platform around. It’s given us holistic way of protecting ourselves today, and a secure foundation for everything we want to do in the future.” The challenges of a global, always-on operation Swissport’s network helps millions of passengers, cargo shipments, and lounges worldwide Swissport’s network supports millions of passengers, cargo shipments, and lounges worldwide. Three years ago, scale was an enormous challenge—ensuring reliable connectivity for operations spanning locations and time zones. The company relied on a mix of MPLS and regional SD-WAN solutions across its now 320+ sites and airport locations. But bandwidth limitations and performance variability impacted many applications, including cloud-based, mission-critical applications. As a result of that complicated network, expanding to new locations was resource-intensive, requiring manual setup and multiple vendor dependencies. Differences between networking tools made troubleshooting inconsistent and time-consuming. The IT team in turn had to maintain expertise in multiple networking technologies, increasing operational overhead. What security inspection existed for unencrypted traffic Visibility was an enormous challenge. With multiple network platforms in place, Swissport’s IT team lacked a centralised view of network performance and security threats. “In the past, working with multiple systems meant inconsistency,” says Thorp. “Different platforms required different configurations, which complicated troubleshooting and made security enforcement a challenge.” Swissport relied on a patchwork of security appliances, including firewalls and web gateways. Remote users are connected through different VPN servers deployed across different regions. The complex appliance stack required manual maintenance and lacked centralised visibility and control. Security patching was manual and error-prone and implementing consistent security policies was practically impossible, weakening Swissport’s security posture. What security inspection existed was relegated to unencrypted traffic due to the well-founded concern that inspecting encrypted traffic could break the application experience that in this case were airline partners’ systems. Finally, the lack of consistent, advanced threat detection worldwide limited Swissport’s ability to detect and stop threats. Visibility differentiates the Cato SASE cloud platform Thorp and the IT team had initially leaned away towards deploying that architecture Recognising these inefficiencies, Swissport’s legacy IT team initiated the Cato relationship, connecting many of the now 320+ sites and instances in AWS and Azure to the Cato SASE Cloud Platform. When Thorp and the new IT leadership joined Swissport, about two-thirds of the connections had been deployed. Having been familiar with a legacy cybersecurity provider, Thorp and the IT team had initially leaned away towards deploying that architecture. Hearing about the value of Cato they decided to have a closer look. “What really drew me to Cato is the visibility the platform provides. It’s incredibly easy to pinpoint connectivity issues, analyse traffic patterns, and secure our network from a single interface,” says Thorp. Cato uniquely stores the metadata of all enterprise traffic crossing the Cato SASE Cloud Platform — whether to the Internet or another location — from all endpoints — in the office and outside of it — in a single data store. This incredible resource provides Cato customers with deep, end-to-end insight into their complete network. Much improved security and a better network With a platform that is resilient, secure, and easy to manage, Swissport has been able to take a more proactive approach to security, streamline IT processes, and ensure a seamless digital experience for employees across the globe. Advanced threat prevention now operates globally and protects against malware and ransomware even in encrypted traffic. “Cato’s TLS Inspection gives us the ability to inspect encrypted traffic while avoiding unintended service disruptions,” says Ashton-Roberts. “It’s been a major improvement to our security posture.” Fine-grained access control through the always-on Cato Client connects remote users to Cato, granting access only to permitted resources. The Cato Client fully implements zero trust principles and operates outside and inside the office under one common policy set. “With Cato, every device—whether in a Swissport office or in an airport lounge—operates under the same set of security policies. That level of consistency wasn’t possible before,” says Ashton-Roberts. Deploying new network sites Cato not only delivers optimised network version worldwide but also makes deploying new networks Access is across the Cato Global Private Backbone built into the Cato SASE Cloud Platform, delivering an exceptional, secure user experience anywhere in the world. Cato not only delivers optimised network performance worldwide but also makes deploying new network sites effortless. “Connecting new airlines or contracts now takes just a few clicks,” says Thorp. Thorp’s team has also dramatically reduced network resolution times. “We recently identified and solved a performance issue in a South African location that would have taken us days before Cato,” says Thorp. “Within 15 minutes, our team identified excessive database traffic, blocked the device, and restored normal operations.” Transforming IT by transforming the infrastructure The transformative impact of the Cato SASE Cloud Platform on the IT team has been profound. Previously, managing multiple networking platforms required maintaining expertise in diverse technologies, creating an operational burden. The IT staff was constantly troubleshooting connectivity issues, manually configuring security appliances, and dealing with inconsistent policies across different locations. The shift to Cato not only simplified management but also allowed the IT team to focus on higher-value strategic initiatives. “Before Cato, we had to maintain different skill sets for different platforms, which spread the team thin. Now, we have one standardised system that allows us to be much more efficient,” Thorp says. Newfound network visibility Swissport has been able to optimise resource allocation and improve overall productivity By consolidating security and networking into a single platform, Swissport has been able to optimise resource allocation and improve overall productivity. The newfound network visibility has also brought a shift from reactive to a proactive IT strategy that has helped the company ensure consistent service delivery across its global operations. “For me, Cato future proofs Swissport’s IT infrastructure,” says Thorp. “The platform constantly evolves, adapts to new technologies, and provides the visibility and security we need to support our business today and tomorrow.” Partnership with Cato proved unique The success of Swissport’s IT transformation was built on more than just technology—it was about forming a strong, collaborative relationship with Cato Networks. From the start, Cato worked closely with Swissport to understand its unique challenges and deliver tailored solutions that addressed its global security and networking needs. “We worked directly with Cato’s product team to enhance capabilities—not just for us, but for all customers,” says Thorp. The success of Swissport’s IT transformation was built on more than just technology Features requested by Swissport were implemented on schedule, unlike other vendors who provided only lip service. Thorp says, “Many vendors say they listen, but Cato actually delivers on what they promise.” This close partnership has given Swissport confidence that its evolving needs will continue to be met as Cato refines its platform. “With Cato, we’re not just another customer; we’re part of a continuous innovation cycle that ensures our IT infrastructure remains future-ready,” says Thorp. “It’s rare to find a vendor so responsive and committed to delivering what they promise.” Looking ahead to the future Swissport IT requirements continue to evolve with Cato remaining a key pillar. “With Cato in place, we know that our network is not the limiting factor in our growth,” Thorp explains. The ongoing partnership between Swissport and Cato ensures that as technology continues to evolve, Swissport’s IT infrastructure remains secure, scalable, and adaptable to the demands of a fast-paced aviation industry. On a personal level, Cato has given Thorp peace of mind. “I relax a bit more with the Cato platform around. It’s given us a holistic way of protecting ourselves today and a secure foundation for everything we want to do in the future. Swissport’s IT leadership now can focus on innovation rather than crisis management.”
The Torrance Unified School District is a cornerstone of the Torrance community, dedicated to providing a high-quality education that prepares students for success in college, career, and life. Serving a diverse student population, Torrance USD delivers a comprehensive and enriching educational experience from kindergarten through high school. The school district comprises 17 elementary, eight middle, and five high schools, one continuation high school, and one alternative high school. Vendor solutions Torrance USD had a mashup of different technologies and vendor solutions across its schools Like many school districts, Torrance USD had a mashup of different technologies and vendor solutions across its schools regarding the ability to broadcast announcements and alerts. Each school had separate systems for bells, clocks, and loudspeakers. There was no central management of these systems, and the school district couldn't create pre-recorded messages for emergencies. Many system components were also end-of-life, and maintaining everything was cumbersome at best. Focusing on consolidation for reliability and consistency Torrance USD began planning district-wide communication improvements in 2020, with the overarching goal of deploying one uniform system through all 32 campuses, with one dashboard to manage communications. The school district achieved its goal by deploying Cisco Call Manager coupled with Singlewire’s InformaCast communications software and hundreds of IPX endpoints from AtlasIED. Vetted integration technology partners like Cisco, Singlewire, and AtlasIED ensure that interoperability, reliability, and usability have all been verified and validated through extensive testing. Surveillance cameras for emergency alerting Torrance USD began planning district-wide communication improvements in 2020 “This project was part of a larger strategic plan to secure each campus — improve perimeter security, add surveillance cameras, allow for emergency alerting, consolidate the speaker systems, and standardise the bells,” said Gil Mara, Chief EdTech and Information Services Officer at Torrance USD. “For example, when you went from one campus to another, campuses had different bell sequences for scenarios like lockdowns. So, there was no consistency of the alerting mechanisms, and we wanted to ensure it was consistent across all the schools.” Digital and physical security of K-12 schools District staff contacted Nilkanth Radadia, Senior Account Manager at NIC Partners, to design the desired district-wide communications solution. NIC Partners has over two decades of experience enhancing the digital and physical security of K-12 schools and was well-suited to take on a project of Torrance USD’s scale. Focusing on what’s most important “Many stakeholders were involved in this project,” said Radadia. ”Given the project’s scope and requirements, there were a lot of conversations beforehand to get the district comfortable with understanding how the system would work." "Some key elements were customisability, two-way talk, multicolour visual message capabilities, and ADA compliance for the visual and hearing impaired. When AtlasIED came out with their full LCD screen speaker, that was a game changer.” Feature set and industrial design NIC Partners installed nearly 1700 IP-SDMF speakers throughout the schools to ensure messages AtlasIED was chosen as the vendor for the system upgrades after a thorough evaluation of various vendors. Their feature set and industrial design, particularly the full LCD screen speaker, stood out. NIC Partners installed nearly 1700 IP-SDMF speakers throughout the schools to ensure messages were audible, visible, and intelligible. WAN or LAN network architecture Leveraging standard WAN or LAN network architecture, each speaker is equipped with an integrated talkback microphone, LCD, and LED flasher, supporting both visual text and audio broadcast to enhance physical security while improving day-to-day communications through advanced alerting, bell schedules, and pre-recorded and scheduled announcements. For example, at 8:30 each morning, the Pledge of Allegiance is broadcast to all schools with a patriotic colour palette appearing on the IPX endpoints. LED blinker “We needed to implement a solution that would serve the needs of all the students, including those with visual or audio impairments,” said Mara. “That's why having the LED blinker and the message crawler was essential. That solved the issues regarding accessibility for our students and staff to ensure they got the message(s) every time.” Network-wide communication For campus exteriors, NIC Partners chose the IP-HVP speaker from AtlasIED For campus exteriors, NIC Partners chose the IP-HVP speaker from AtlasIED. The IP-HVP is a vandal-proof, IP45 weather-resistant, wall-mount IP speaker well-suited for environments where network-wide communication is desired, and high output is required to overcome excessive ambient noise or large spaces. Almost 600 IP-HVP speakers were installed district-wide. Additionally, the Power over Ethernet (PoE+)-enabled IPX endpoints connect through the same IT network the school uses to deliver Internet access. InformaCast mass communications software The platform simplifies the installation process for integrators and reduces the need to introduce multiple cable types to a project. The IPX platform also offers scalability benefits, allowing schools the flexibility to expand their systems as the district’s communications evolve. The IPX Series also helped Torrance USD incorporate new and expanded campus safety capabilities with the help of InformaCast mass communications software. IPX LCD screens Torrance USD is trying out various colour combinations on the IPX LCD screens to indicate alerts Using InformaCast, designated school personnel can initiate an alert from a mobile device wherever they are. The software then sends text messages to faculty, students, and parents' mobile devices, alerts law enforcement, and activates attention-grabbing audio alarms and LCD text messages on the installed IPX devices throughout the school or district. Currently, Torrance USD is trying out various colour combinations on the IPX LCD screens to indicate different kinds of alerts, including earthquakes, shelter-in-place, and all-clear messages. Intentional and phased deployment leads to consistent use NIC Partners started with the smallest school to establish best practices for implementation. Once the first school was completed and future implementation methods documented, NIC Partners went full-on with the remaining schools, working second shift during the school year and completing all the upgrades district-wide in less than five months. The communication system is in the final phase of upgrading all the schools to InformaCast Fusion servers and upgrading Cisco Call Manager to Webex calling. These updates will allow select school and district staff members to make emergency announcements or push out notifications directly from their cell phones. NIC Partners and AtlasIED Staff and students appreciate the audio upgrades, albeit for different reasons. Teachers are relieved by the improved audio clarity, as they can finally hear things “loud and clear,” and emergency alerts include visual messaging. Students love the music played at the end of each period to indicate a class transition. “Before the upgrades, you couldn't make a good page,” said Mara. “Now, the audio clarity is way better. We’re delighted with the IPX products and even happier to have NIC Partners and AtlasIED as our partners for such a huge undertaking. We wouldn't have been successful without their help.”
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.
Thames Valley Police worked with local authorities to improve CCTV coverage, cut costs, and boost efficiency. It’s made public spaces safer and ensured long-term, reliable monitoring across the region. Thames Valley Police is the largest non-metropolitan police force in England and Wales, covering 2,218 square miles and a population of 2.42 million people. Its jurisdiction includes multiple towns, city centres and council areas across the three counties of Berkshire, Buckinghamshire and Oxfordshire. Setting a long-term vision for public space CCTV Public space CCTV is vital in deterring and detecting crime across the Thames Valley Public space CCTV is vital in deterring and detecting crime across the Thames Valley. However, significant pressure on local authority budgets has made it increasingly difficult for councils to provide public space CCTV. There was real jeopardy that financial constraints would result in unmaintained systems, with limited or no real-time monitoring. A fresh approach was needed, so the Thames Valley CCTV partnership between Genetec™ and Hanwha Vision was formed. The first major challenge was securing funding to overhaul several local authorities’ ageing systems, which were proving increasingly expensive to upgrade and maintain. The second was to manage the ongoing costs of staffing control rooms to ensure the long-term sustainability of monitored CCTV across the Thames Valley. Ownership and monitoring of public space CCTV Ambitious plans were devised to pool resources and replace many disparate systems with one police-owned system that could extend across multiple authorities. In effect, the aim was to transfer the ownership and monitoring of public space CCTV from local authorities to dedicated Thames Valley Police control rooms. It would be led by the Thames Valley Police & Crime Commissioner (PCC) Matthew Barber, collaborating with any local authority who chose to participate. It was a feat that had never been attempted in the UK on this scale that held the potential to drive efficiencies and enhance CCTV provision in areas it might otherwise have deteriorated. Ongoing commitment and investment “CCTV is an important part of community safety; benefitting police and local communities in helping to deter crime and antisocial behaviour, identify offenders and support prosecutions." "Ongoing commitment and investment enables high quality, consistent and sustainable CCTV provision now and into the future”, explains Matthew Barber, PCC, Thames Valley. Centralisation creates area-wide visibility and control Several control rooms in the Thames Valley, like Windsor & Maidenhead, had implemented Genetec Security Centre Several control rooms in the Thames Valley, such as Windsor & Maidenhead, had already implemented Genetec Security Centre and were very happy with its operation. Furthermore, as an open platform video management system, it could minimise costs by supporting a phased unification or “takeover” of existing systems across the Thames Valley. Finally, its hybrid cloud architecture provided Thames Valley with maximal flexibility to leverage any combination of cloud or on-premises infrastructure according to Name Thames Valley Police Industries Public Safety Location Thames Valley, United Kingdom Products Genetec Security Centre; Genetec Cloud Services; Federation Technology Partners Hanwha Vision Channel Partners CDS Systems what made sense for each application and location. This made it the obvious choice on which to standardise. Range of multidirectional AI-enabled cameras Following a competitive tender, Thames Valley chose CDS Systems to implement its proposed solution. This would be built on Genetec Security Centre and incorporate a range of multidirectional AI-enabled cameras from Hanwha Vision. A key driver in the decision was the high levels of commitment shown by all three parties to cybersecurity. Another was the recognition that the system design and technology selection could ensure a cost-effective implementation that could continue to evolve in line with the needs of its users. Integration between Genetec and Hanwha Vision technology Legacy cameras were retained and reused to maximise the return on existing investment wherever possible “We urgently needed to improve the quality of CCTV, enhance collaboration, and drive efficiencies for all partners. The respective capabilities and seamless integration between Genetec and Hanwha Vision technology was the optimal way of meeting Thames Valley’s requirements,” says Sam Thomas, CDS Systems. Phase one of the deployment involved CDS taking over an existing control room in Milton Keynes, replacing the legacy analogue infrastructure with a modern IP backbone. It then installed Genetec Security Centre to establish one platform through which officers could smartly interact with all incoming video feeds. Legacy cameras were retained and reused to maximise the return on existing investment wherever possible. A second Genetec workstation was also set up inside Slough Police Station, allowing officers to rapidly review footage for improved community response. Hanwha Vision’s AI-enabled multidirectional cameras CDS then introduced Hanwha Vision’s AI-enabled multidirectional 4k cameras to improve CCTV coverage and quality in public spaces. Each of these cameras incorporates up to five cameras in one device for wide-area surveillance, which would previously have required several separate devices, simplifying installation and resulting in significantly less associated cabling and infrastructure. They also provide powerful AI analytics, including accurate object detection and classification, to enable forensic search and save operators' time when responding to incidents. For example, identifying and establishing the movement of specific people or vehicles based on attributes such as vehicle type. Thames Valley CCTV partnership Phase two will see four additional control rooms in Oxfordshire merged into a single hub Phase two will see four additional control rooms in Oxfordshire merged into a single hub inside Abingdon Police station, also built on the Genetec Security Centre. This and the control room in Milton Keynes will be interlinked, adding further resilience as each site will be able to act as a fallback for the other. At this point, there will be a dedicated team of eighteen staff responsible for monitoring CCTV and enhancing CCTV for all participating communities in the Thames Valley CCTV Partnership. Innovative and cost-effective solutions “The CCTV Command Suite enabled by CDS, Genetec and Hanwha Vision has improved our workflows beyond recognition, enabling staff to quickly review and package evidence for frontline officers or more complex investigations. It has received several plaudits from officers for its ease of use,” says Jason Owen, CCTV Operations Manager, Thames Valley Police. “This collaboration between Thames Valley Police, Genetec, CDS Systems, and Hanwha Vision showcases the power of partnership in driving innovative, cost-effective solutions that improve public safety,” says John Boorman, Head of Product and Marketing at Hanwha Vision Europe. “Our AI-enabled cameras are designed to reduce false alarms and streamline operations, ensuring teams can focus on real incidents and drive efficiency across their monitoring.” Efficiency, at a lower cost All CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers Pooling resources and transferring ownership to the police has brought about significant cost efficiencies for participating authorities, while also enhancing the quality and reliability of public spaces CCTV. Just as importantly, it has dramatically improved the police’s direct access to quality video evidence. Unlike in a traditional council-run control room, all CCTV operators are civilian police staff vetted to the same clearance levels as sworn-in officers. This means they have full access to Thames Valley’s suite of police databases and reporting software packages. They are better equipped to rapidly report incidents, support front-line officers, and communicate effectively with investigators as a result. On average, it handles between 300 – 500 incidents a month and has substantially increased the number of successful requests for supporting footage. “We’ve immediately seen the benefit of our investment in equipment and CCTV operators, with the police now much better equipped to deter and detect crime across the Thames Valley,” adds Barber. A solid platform for further improvements Control room operators’ intuition will always be the driving force that brings results Looking forward, Thames Valley has plans to use the Genetec platform to connect its people and mobile surveillance assets back to its control rooms for better cross-force interaction. Genetec Federation as a Service is already allowing live and recorded video to be shared with officers in the field. Soon it will also be extended to ensure video from police CCTV vans and drones is immediately available in the control room. In both cases this is achieved without complex network configuration, requiring only an internet connection. It is also at the beginning of its journey of fully realising the value of the AI-equipped Hanwha Vision cameras specified by CDS. Control room operators’ intuition will always be the driving force that brings results, but AI is freeing them up to do what they do best by saving time on routine monitoring and searches. Cost savings, resilience, and efficiencies Finally, talks continue that would see the addition of further control rooms across the Thames Valley to the Thames Valley CCTV Partnership. Having proven the model, would allow it to scale operations further to deliver even greater cost savings, resilience, and efficiencies. “We’re proud of what we’ve achieved to date but have no intention of resting on our laurels. The foundations we’ve established will ensure continued high-quality, consistent, and sustainable CCTV provision for our communities,” concludes Owen.
Modern measurement technologies enable high-precision detection of the movement of liquids and gases - and thus provide valuable data for numerous applications. How does the air flow around an aeroplane? How does the blood move through our veins? And how can pollutant emissions in combustion processes be minimised? For this purpose, speed, direction, pressure and turbulence within a flow are analysed in order to increase efficiency, ensure safety and drive innovation in a wide variety of areas. Innovative sensor technology High-resolution cameras are used to track marked particles within a flow and analyse their movement A range of methods are available to measure these flows, including visual ones such as particle image velocimetry (PIV). High-resolution cameras are used to track marked particles within a flow and analyse their movement. iLA_5150 GmbH from Aachen (Germany) now also relies on EBIV. The abbreviation stands for Event-Based Particle Image Velocimetry and is a new optical method for the qualitative and quantitative visualisation of flows and flow velocities. It combines PIV with event-based cameras, here with a uEye EVS from IDS Imaging Development Systems GmbH. The innovative sensor technology of the industrial camera enables highly dynamic and energy-efficient detection, especially of fast and turbulent movements. Application In the EBIV method, tiny particles are added to a flowing fluid and illuminated in a plane, the so-called light section plane. They generate individual light pulses as they enter and exit the LED light section. This change in local brightness is recorded independently by the camera pixels and transmitted to the PC as a data stream of "change events". In contrast to conventional cameras, event-based models therefore only react to the changes in brightness registered in the image field. Stationary scattered light, such as background or a non-changing illuminated surface, does not generate a measurement signal. This reduces the amount of data considerably. Frame rates of up to 10,000 frames per second The data stream essentially contains information about what happens, when and where The data stream essentially contains information about what happens, when and where. In detail, these are the pixel coordinates on the sensor, microsecond time stamps of the pixel events and the information about the events: ON or OFF. This allows a distinction to be made between increasing intensity (ON event) and decreasing intensity (OFF event). Using suitable software, the stream can be converted into an image matrix in which both the spatial information and the linear time base of the stream are available. The result is comparable to the extremely high frame rate of a high-speed camera. EBIV measurement method "The EBIV measurement method differs fundamentally from conventional imaging methods. They usually generate very large amounts of data and require powerful peripherals that can process them. For exceptional frame rates of 1000 Hertz and more, the image-based cameras required are themselves very complex and expensive." "With the help of event-based camera technology, comparable frame rates of 10,000 frames per second are possible, whereby only standard PC interfaces such as USB with a few gigabits per second are required. The price of the event-based models themselves is significantly lower than that of corresponding high-speed cameras and is therefore also very interesting for smaller teaching and research institutions," explains Dr André Brunn - Head of Development at iLA_5150 GmbH. Further processing The user can optimise the display of the move paths and adapt them to unique study objectives The data stream is converted into image data and displayed in a front end - the so-called EBIV viewer - for direct online flow visualisation. The user can also select the integration time, which corresponds to the exposure time of an image camera, as well as the time increments of the sequence, i.e., the period between two consecutive shots. Classic image filters can also be used. With the help of these settings, the user can optimise the display of the movement paths and adapt them to individual examination objectives. Both fine flow details and large-scale patterns can be made more clearly recognisable. This ability to readjust the measurement results is another advantage of the event-based approach. Numerical analysis of the flow properties In the qualitative visualisation of the flow in the EBIV-View, particles are continuously illuminated so that they are visible as luminous traces. The method is therefore very well suited to visualising the flow. However, it does not provide exact measurements of its speed or direction. For a precise, numerical analysis of the flow properties, individual particles are illuminated for a moment using short, time-defined light pulses. Image sequences of the event-based camera As with classic PIV, the image sequences of the event-based camera can also be statistically analysed This allows their exact position to be recorded and their movement quantified. By comparing the particle positions in successive images, the speed and direction of the flow can be precisely calculated using PIV, for example. The result is a transient 2D vector field that changes over time - in other words, the vectors do not remain constant. As with classic PIV, the image sequences of the event-based camera can also be statistically analysed, for example, to determine mean values and fluctuations in the flow velocity. Camera and software On the camera side, iLA relies on a uEye XCP-E from IDS. The small, lightweight industrial camera offers event-based sensor technology in a robust die-cast zinc housing (29 × 29 × 17 mm) with screw-on USB Micro-B connection. It is compatible with all standard C-mount lens sizes. This makes it ideal for both industrial and non-industrial areas. The integrated event-based vision sensor (EVS) was developed by Sony and Prophesee. It is supported by the Metavision SDK, a seamlessly integrated suite of software tools and models, APIs and other training and development resources from Prophesee for efficient analysis, visualisation and customisation. Building on this, the EBIV viewer from iLA_5150/PIVTec is specially tailored to flow visualisation applications. Outlook The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions The optimisation of fluidic systems and processes requires detailed knowledge of the flow conditions. A qualitative flow visualisation is often sufficient to understand effects and develop suitable control mechanisms. Until now, however, imaging fast flows with high temporal resolution was usually only possible with expensive high-speed cameras. Event-based camera technology offers a cost-effective alternative that requires significantly less technical effort. These “simple” methods have been lacking in teaching and research in particular. Thanks to the extreme data reduction, this technology also allows the use of several cameras or large camera arrays without the periphery becoming a limitation for data transfer. The compact design of the uEye EVS models also makes them ideal for mobile applications. This means that real application environments can be analysed directly for the first time - without having to rely on artificial flow models or channels. Established flow measurement methods Event-based cameras enable efficient, cost-effective and high-resolution visualisation and quantification of flows. Due to the small amounts of data generated, many processes can be analysed almost in real time, which also makes them interesting for use in fully automated systems. Established flow measurement methods such as Particle Image Velocimetry (PIV) can be seamlessly integrated and expanded. The technology can be used wherever flow information is captured by changes in scattered light intensity - be it from moving particles or vibrating surfaces.
Growing businesses require flexibility and easy scalability from their access management. Choosing a secure digital solution which easily adapts and grows as needs change, ensures the organisation is prepared not just for now, but for the future. H.R. Owen is a dealership specialising in the sale, service and repair of luxury and sports cars. Its portfolio of high-end brands includes Lamborghini, Bentley, Aston Martin, Rolls Royce and Lotus. Based primarily in London, the company expanded operations with a new facility in Hatfield to accommodate its growing business. As with all of H.R. Owen’s premises, this new showroom required high security due to the nature of its vehicle stock. Access management solution Unified access control solution that could encompass a wide range of openings “Security is paramount as we needed to ensure that we are not just protecting our high-value products, but also our staff and our customers,” explains Sean Nevatte, Group Aftersales Director at H.R. Owen. For the new premises, managers sought a single, unified access management solution which could encompass a wide range of openings including glass doors, fire doors and parking barriers. Investment in digital access H.R. Owen customers expect a degree of refinement in the showroom environment. So, as well as security and reliability, access devices must blend with the high-end interior design. Finally, they needed a solution which offered easy scalability. As a successful, growing company, they have to be confident their investment in digital access would meet evolving requirements for security, flexibility and aesthetics – now and long into the future. SMARTair® brings real-time control and easy scalability “During the planning stages with H.R. Owen and the architects, it was clear that ASSA ABLOY’s SMARTair solution was the only real choice for the site,” says Matthew Taylor, Operations Director at Knightsbridge Security, who installed the dealership’s system. SMARTair, part of a suite of connected digital access solutions from ASSA ABLOY, is an out-of-the-box system ideally suited to medium-sized premises with a broad range of openings to equip. Among more than 100 devices installed throughout the facility, SMARTair Wall Readers and SMARTair i-max Escutcheons were selected for their sleek aesthetics and versatility. Benefits of choosing a wireless solution The facility can manage access remotely, ensuring access rights may be monitored The devices are wireless, and therefore fast and cost-effective to fit. With no need for extensive cabling, they are quickly installed, minimising onsite disruption. Another benefit of choosing wireless, the reach of H.R. Owen’s solution can be easily extended or reconfigured anytime, protecting their investment for the long term. SMARTair is equally convenient to operate. The facility can manage access remotely, ensuring access rights may be monitored or amended in real time in response to any potential threat. SMARTair’s mobile access solution H.R. Owen also chose SMARTair’s mobile access solution Openow®: staff can use their smartphones for access, rather than physical cards or fobs. Access by secure mobile app boosts both security – fewer lost credentials – and sustainability performance by cutting single-use plastics. Particularly well suited to car showrooms and other premises with parking, Openow’s Parking Mode feature allows drivers to unlock barriers from 3m–5m away. They don’t need to get out of the car to open the barrier. This reduces the risk of opportunist theft or unauthorised access, which is a critical benefit for premises like H.R. Owen with high-value goods inside.
Richard Thorp has been fascinated with aviation since childhood. A self-described “aviation geek,” Thorp is now the Chief Technology Officer at Swissport International AG, where he leads IT infrastructure strategy for the world’s largest ground-handling company, ensuring seamless operations across 276 airports in 45 countries, handling approximately 247 million airline passengers per year, as of the end of 2024. “If we were an airline, we’d actually be the biggest airline in the world in terms of a number of passengers we support and handle,” he says. Security challenges Swissport’s goal is to make a tangible impact on people’s lives by enabling smooth air travel Swissport’s goal is to make a tangible impact on people’s lives by enabling smooth air travel. “If the things we do get people to their destinations safely and on time, then magically, we become more successful and profitable as an organisation,” he says. But casting that spell had been challenging for Swissport. Three years ago, legacy IT leadership at Swissport had overcome network challenges with Cato, but more work was needed to address their security challenges, particularly in securing endpoints. Thorp and Swissport CISO, Giles Ashton-Roberts, joined Swissport in the middle of the Cato deployment. Having deep experience with a legacy zero trust provider, they were skeptical that Cato could meet Swissport’s requirements. Cato platform Over the next 10 months of meetings, investigation, and testing Thorp and Ashton-Roberts challenged Cato, ultimately changing their perspective. “IT is no longer seen as a blocker; it just works,” says Thorp. “I relax a bit more with the Cato platform around. It’s given us holistic way of protecting ourselves today, and a secure foundation for everything we want to do in the future.” The challenges of a global, always-on operation Swissport’s network helps millions of passengers, cargo shipments, and lounges worldwide Swissport’s network supports millions of passengers, cargo shipments, and lounges worldwide. Three years ago, scale was an enormous challenge—ensuring reliable connectivity for operations spanning locations and time zones. The company relied on a mix of MPLS and regional SD-WAN solutions across its now 320+ sites and airport locations. But bandwidth limitations and performance variability impacted many applications, including cloud-based, mission-critical applications. As a result of that complicated network, expanding to new locations was resource-intensive, requiring manual setup and multiple vendor dependencies. Differences between networking tools made troubleshooting inconsistent and time-consuming. The IT team in turn had to maintain expertise in multiple networking technologies, increasing operational overhead. What security inspection existed for unencrypted traffic Visibility was an enormous challenge. With multiple network platforms in place, Swissport’s IT team lacked a centralised view of network performance and security threats. “In the past, working with multiple systems meant inconsistency,” says Thorp. “Different platforms required different configurations, which complicated troubleshooting and made security enforcement a challenge.” Swissport relied on a patchwork of security appliances, including firewalls and web gateways. Remote users are connected through different VPN servers deployed across different regions. The complex appliance stack required manual maintenance and lacked centralised visibility and control. Security patching was manual and error-prone and implementing consistent security policies was practically impossible, weakening Swissport’s security posture. What security inspection existed was relegated to unencrypted traffic due to the well-founded concern that inspecting encrypted traffic could break the application experience that in this case were airline partners’ systems. Finally, the lack of consistent, advanced threat detection worldwide limited Swissport’s ability to detect and stop threats. Visibility differentiates the Cato SASE cloud platform Thorp and the IT team had initially leaned away towards deploying that architecture Recognising these inefficiencies, Swissport’s legacy IT team initiated the Cato relationship, connecting many of the now 320+ sites and instances in AWS and Azure to the Cato SASE Cloud Platform. When Thorp and the new IT leadership joined Swissport, about two-thirds of the connections had been deployed. Having been familiar with a legacy cybersecurity provider, Thorp and the IT team had initially leaned away towards deploying that architecture. Hearing about the value of Cato they decided to have a closer look. “What really drew me to Cato is the visibility the platform provides. It’s incredibly easy to pinpoint connectivity issues, analyse traffic patterns, and secure our network from a single interface,” says Thorp. Cato uniquely stores the metadata of all enterprise traffic crossing the Cato SASE Cloud Platform — whether to the Internet or another location — from all endpoints — in the office and outside of it — in a single data store. This incredible resource provides Cato customers with deep, end-to-end insight into their complete network. Much improved security and a better network With a platform that is resilient, secure, and easy to manage, Swissport has been able to take a more proactive approach to security, streamline IT processes, and ensure a seamless digital experience for employees across the globe. Advanced threat prevention now operates globally and protects against malware and ransomware even in encrypted traffic. “Cato’s TLS Inspection gives us the ability to inspect encrypted traffic while avoiding unintended service disruptions,” says Ashton-Roberts. “It’s been a major improvement to our security posture.” Fine-grained access control through the always-on Cato Client connects remote users to Cato, granting access only to permitted resources. The Cato Client fully implements zero trust principles and operates outside and inside the office under one common policy set. “With Cato, every device—whether in a Swissport office or in an airport lounge—operates under the same set of security policies. That level of consistency wasn’t possible before,” says Ashton-Roberts. Deploying new network sites Cato not only delivers optimised network version worldwide but also makes deploying new networks Access is across the Cato Global Private Backbone built into the Cato SASE Cloud Platform, delivering an exceptional, secure user experience anywhere in the world. Cato not only delivers optimised network performance worldwide but also makes deploying new network sites effortless. “Connecting new airlines or contracts now takes just a few clicks,” says Thorp. Thorp’s team has also dramatically reduced network resolution times. “We recently identified and solved a performance issue in a South African location that would have taken us days before Cato,” says Thorp. “Within 15 minutes, our team identified excessive database traffic, blocked the device, and restored normal operations.” Transforming IT by transforming the infrastructure The transformative impact of the Cato SASE Cloud Platform on the IT team has been profound. Previously, managing multiple networking platforms required maintaining expertise in diverse technologies, creating an operational burden. The IT staff was constantly troubleshooting connectivity issues, manually configuring security appliances, and dealing with inconsistent policies across different locations. The shift to Cato not only simplified management but also allowed the IT team to focus on higher-value strategic initiatives. “Before Cato, we had to maintain different skill sets for different platforms, which spread the team thin. Now, we have one standardised system that allows us to be much more efficient,” Thorp says. Newfound network visibility Swissport has been able to optimise resource allocation and improve overall productivity By consolidating security and networking into a single platform, Swissport has been able to optimise resource allocation and improve overall productivity. The newfound network visibility has also brought a shift from reactive to a proactive IT strategy that has helped the company ensure consistent service delivery across its global operations. “For me, Cato future proofs Swissport’s IT infrastructure,” says Thorp. “The platform constantly evolves, adapts to new technologies, and provides the visibility and security we need to support our business today and tomorrow.” Partnership with Cato proved unique The success of Swissport’s IT transformation was built on more than just technology—it was about forming a strong, collaborative relationship with Cato Networks. From the start, Cato worked closely with Swissport to understand its unique challenges and deliver tailored solutions that addressed its global security and networking needs. “We worked directly with Cato’s product team to enhance capabilities—not just for us, but for all customers,” says Thorp. The success of Swissport’s IT transformation was built on more than just technology Features requested by Swissport were implemented on schedule, unlike other vendors who provided only lip service. Thorp says, “Many vendors say they listen, but Cato actually delivers on what they promise.” This close partnership has given Swissport confidence that its evolving needs will continue to be met as Cato refines its platform. “With Cato, we’re not just another customer; we’re part of a continuous innovation cycle that ensures our IT infrastructure remains future-ready,” says Thorp. “It’s rare to find a vendor so responsive and committed to delivering what they promise.” Looking ahead to the future Swissport IT requirements continue to evolve with Cato remaining a key pillar. “With Cato in place, we know that our network is not the limiting factor in our growth,” Thorp explains. The ongoing partnership between Swissport and Cato ensures that as technology continues to evolve, Swissport’s IT infrastructure remains secure, scalable, and adaptable to the demands of a fast-paced aviation industry. On a personal level, Cato has given Thorp peace of mind. “I relax a bit more with the Cato platform around. It’s given us a holistic way of protecting ourselves today and a secure foundation for everything we want to do in the future. Swissport’s IT leadership now can focus on innovation rather than crisis management.”
The Torrance Unified School District is a cornerstone of the Torrance community, dedicated to providing a high-quality education that prepares students for success in college, career, and life. Serving a diverse student population, Torrance USD delivers a comprehensive and enriching educational experience from kindergarten through high school. The school district comprises 17 elementary, eight middle, and five high schools, one continuation high school, and one alternative high school. Vendor solutions Torrance USD had a mashup of different technologies and vendor solutions across its schools Like many school districts, Torrance USD had a mashup of different technologies and vendor solutions across its schools regarding the ability to broadcast announcements and alerts. Each school had separate systems for bells, clocks, and loudspeakers. There was no central management of these systems, and the school district couldn't create pre-recorded messages for emergencies. Many system components were also end-of-life, and maintaining everything was cumbersome at best. Focusing on consolidation for reliability and consistency Torrance USD began planning district-wide communication improvements in 2020, with the overarching goal of deploying one uniform system through all 32 campuses, with one dashboard to manage communications. The school district achieved its goal by deploying Cisco Call Manager coupled with Singlewire’s InformaCast communications software and hundreds of IPX endpoints from AtlasIED. Vetted integration technology partners like Cisco, Singlewire, and AtlasIED ensure that interoperability, reliability, and usability have all been verified and validated through extensive testing. Surveillance cameras for emergency alerting Torrance USD began planning district-wide communication improvements in 2020 “This project was part of a larger strategic plan to secure each campus — improve perimeter security, add surveillance cameras, allow for emergency alerting, consolidate the speaker systems, and standardise the bells,” said Gil Mara, Chief EdTech and Information Services Officer at Torrance USD. “For example, when you went from one campus to another, campuses had different bell sequences for scenarios like lockdowns. So, there was no consistency of the alerting mechanisms, and we wanted to ensure it was consistent across all the schools.” Digital and physical security of K-12 schools District staff contacted Nilkanth Radadia, Senior Account Manager at NIC Partners, to design the desired district-wide communications solution. NIC Partners has over two decades of experience enhancing the digital and physical security of K-12 schools and was well-suited to take on a project of Torrance USD’s scale. Focusing on what’s most important “Many stakeholders were involved in this project,” said Radadia. ”Given the project’s scope and requirements, there were a lot of conversations beforehand to get the district comfortable with understanding how the system would work." "Some key elements were customisability, two-way talk, multicolour visual message capabilities, and ADA compliance for the visual and hearing impaired. When AtlasIED came out with their full LCD screen speaker, that was a game changer.” Feature set and industrial design NIC Partners installed nearly 1700 IP-SDMF speakers throughout the schools to ensure messages AtlasIED was chosen as the vendor for the system upgrades after a thorough evaluation of various vendors. Their feature set and industrial design, particularly the full LCD screen speaker, stood out. NIC Partners installed nearly 1700 IP-SDMF speakers throughout the schools to ensure messages were audible, visible, and intelligible. WAN or LAN network architecture Leveraging standard WAN or LAN network architecture, each speaker is equipped with an integrated talkback microphone, LCD, and LED flasher, supporting both visual text and audio broadcast to enhance physical security while improving day-to-day communications through advanced alerting, bell schedules, and pre-recorded and scheduled announcements. For example, at 8:30 each morning, the Pledge of Allegiance is broadcast to all schools with a patriotic colour palette appearing on the IPX endpoints. LED blinker “We needed to implement a solution that would serve the needs of all the students, including those with visual or audio impairments,” said Mara. “That's why having the LED blinker and the message crawler was essential. That solved the issues regarding accessibility for our students and staff to ensure they got the message(s) every time.” Network-wide communication For campus exteriors, NIC Partners chose the IP-HVP speaker from AtlasIED For campus exteriors, NIC Partners chose the IP-HVP speaker from AtlasIED. The IP-HVP is a vandal-proof, IP45 weather-resistant, wall-mount IP speaker well-suited for environments where network-wide communication is desired, and high output is required to overcome excessive ambient noise or large spaces. Almost 600 IP-HVP speakers were installed district-wide. Additionally, the Power over Ethernet (PoE+)-enabled IPX endpoints connect through the same IT network the school uses to deliver Internet access. InformaCast mass communications software The platform simplifies the installation process for integrators and reduces the need to introduce multiple cable types to a project. The IPX platform also offers scalability benefits, allowing schools the flexibility to expand their systems as the district’s communications evolve. The IPX Series also helped Torrance USD incorporate new and expanded campus safety capabilities with the help of InformaCast mass communications software. IPX LCD screens Torrance USD is trying out various colour combinations on the IPX LCD screens to indicate alerts Using InformaCast, designated school personnel can initiate an alert from a mobile device wherever they are. The software then sends text messages to faculty, students, and parents' mobile devices, alerts law enforcement, and activates attention-grabbing audio alarms and LCD text messages on the installed IPX devices throughout the school or district. Currently, Torrance USD is trying out various colour combinations on the IPX LCD screens to indicate different kinds of alerts, including earthquakes, shelter-in-place, and all-clear messages. Intentional and phased deployment leads to consistent use NIC Partners started with the smallest school to establish best practices for implementation. Once the first school was completed and future implementation methods documented, NIC Partners went full-on with the remaining schools, working second shift during the school year and completing all the upgrades district-wide in less than five months. The communication system is in the final phase of upgrading all the schools to InformaCast Fusion servers and upgrading Cisco Call Manager to Webex calling. These updates will allow select school and district staff members to make emergency announcements or push out notifications directly from their cell phones. NIC Partners and AtlasIED Staff and students appreciate the audio upgrades, albeit for different reasons. Teachers are relieved by the improved audio clarity, as they can finally hear things “loud and clear,” and emergency alerts include visual messaging. Students love the music played at the end of each period to indicate a class transition. “Before the upgrades, you couldn't make a good page,” said Mara. “Now, the audio clarity is way better. We’re delighted with the IPX products and even happier to have NIC Partners and AtlasIED as our partners for such a huge undertaking. We wouldn't have been successful without their help.”
In areas such as high-precision metalworking, accuracy is non-negotiable. This includes the automotive industry and its suppliers, which are in crisis in Germany for a variety of reasons. The industry is under enormous pressure to deliver products of impeccable quality and at the same time reduce operating costs, for example by increasing process speeds. The automotive industry's quality assurance standards are strict, the component geometries are complex and the demands on precision and process reliability are enormous. Fluctuations in detection, insufficient traceability to individual serial numbers or batches and changing environmental conditions can lead to costly errors, production downtime and complaints. Innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has set an exemplary, innovative solution for AI quality inspection VIVALDI Digital Solutions GmbH has developed an exemplary, innovative solution for AI quality inspection in real time. In addition to an edge server with an Intel processor, intelligent image processing plays a key role in the so-called SensorBox. Designed for an automotive supplier and its production site in the Czech Republic, up to 70 USB3 uEye+ XC autofocus cameras from IDS Imaging Development Systems perform automatic visual inspection for surface inspection in several inspection cells. AI recognises various surface defects "The IDS cameras integrated into the test cells capture high-resolution images of the surface of aluminium components from German OEMs, in this case an electric motor," says Uwe Siegwart, Managing Director at Vivaldi, explaining the camera's task. The captured images are pre-processed to optimise factors such as exposure, white balance and colour correction. The AI recognises various surface defects such as scratches, pores or dirt. Strict requirements at the plant Up to 2,400 electric motor housings per day are tested 100% automatically with the implemented system "There are strict requirements at the plant in the Czech Republic. According to the defect catalogue, defects from 0.2 millimetres must be reliably detected. The test time per component must not exceed 36 seconds," says Uwe Siegwart, explaining the stringent guidelines. Up to 2,400 electric motor housings per day are tested 100 percent automatically with the successfully implemented system. Why did the AI specialist choose the uEye XC camera from IDS? "The decisive factor was that the autofocus camera can capture several surfaces at different distances from the camera," says Eike Humpert from Vivaldi's Business Development department. This simplifies the testing process enormously and ensures greater efficiency and flexibility. This is a crucial factor when, for example, different component variants need to be tested. With the macro attachment lens, the minimum object distance of the camera can also be shortened very easily. BSI pixel technology "The BSI pixel technology enables the sensor to deliver consistently precise and reliable results, even in changing light conditions," explains Jürgen Hejna, Product Owner 2D cameras at IDS. It is not only the excellent low-light performance and minimal pixel noise that make the sensor particularly suitable for this application. "The 24x digital zoom, combined with auto white balance and precise colour correction, contributes significantly to the success of this demanding test procedure," emphasises Jürgen Hejna. AI-based image processing The simultaneous image processing task is complex and the challenges are diverse The simultaneous image processing task is complex and the challenges are diverse. Aluminium parts often have very shiny surfaces that reflect light and therefore have a strong influence on images. These reflections make it difficult to reliably recognise defects such as scratches, cold runs, chatter marks or surface irregularities, as they are often obscured or distorted by light reflections. This, along with other material and environmental variations, means AI-based image processing must therefore be able to distinguish precisely between the normal material structure and actual raw areas in surfaces to be processed that are considered defects. AI-supported and synchronous camera control via edge server Image processing is carried out via an optimised infrastructure. Up to eight cameras can be connected per USB hub, enabling simultaneous recording of several inspection areas. A maximum of two of these USB hubs are connected to a self-developed 'cam controller', which bundles and processes the image signals. Several cam controllers are networked with the edge server. This server not only calculates the AI-supported analyses, but also communicates directly with the system controller, which coordinates the triggering of the cameras and ensures synchronised recording. Digitised quality data acquisition Up to eight cameras can be linked per USB hub, enabling simultaneous recording of inspection areas "Image processing is a central component for traceability, which is the actual technological centrepiece of the solution, and IDS is the ideal partner for this point”, underlines Uwe Siegwart. "Digitised quality data acquisition in real time and linking with other production parameters not only increases efficiency, but also significantly reduces rejects and rework. Errors are minimised, costs are reduced and production processes are optimised." The system has already paid off in the Czech Republic: The number of complaints per year has been reduced by two-thirds and the number of unrecognised surface defects has even been reduced to zero. Outlook "The market for digital quality control is developing rapidly, particularly due to more favourable camera technology, for example with regard to higher resolutions. Optimised image processing processes and tools also make it possible for real-time analyses to be carried out by end users," states Eike Humpert. "Improved resolution, more compact design and price-optimised cameras are in demand." The portfolio of the industrial camera manufacturer IDS is designed to meet this demand with state-of-the-art technology.


Round table discussion
The most common wearable device deployed by security professionals is the body-worn camera. Traditionally used by law enforcement professionals, these devices are finding more and more uses in the corporate security world, and even impacting issues such as customer service. However, the term “wearables” also encompasses a range of other devices, including many worn by consumers. We asked this week’s Expert Panel Roundtable: How are wearable technologies impacting the security market?
Every day, the physical security industry succeeds in applying technologies that make the world a safer place. Manufacturers, integrators, and end users are eager to share their success stories, and their successes can inspire others to implement the same technology solutions. But, occasionally, technology does not live up to expectations and, in fact, fails to perform as promised. We asked this week’s Expert Panel Roundtable: How has the physical security industry failed to meet customer needs?
For many years, security systems produced their share of "data exhaust." Every access control action and each video image became a data point to be stored in perpetuity, with no practical way to use the data. More recently, systems have been developed to enable organizations to analyze data from sensors and other connected devices to gain valuable insights into how their systems are being used, to identify potential vulnerabilities; and even to provide insights into broader enterprise operations. We asked this week’s Expert Panel Roundtable: How are data analytics changing the course of the security marketplace?
Products


White papers

How to migrate to an IP-based access control system
Download
The inevitability of The Cloud
DownloadMaking sense of today’s security camera options
Download
Smart security cameras: excellence in retail
Download
Access control & intelligent vehicle screening
Download
How to get buy-in from IT departments on IP video installations
Download
Hikvision DarkFighter Technology for high-quality images at night
Download
Enhanced Ethernet Technology (ePoE)
Download
Video technology: making cities safer & improving lives
Download
Integrated access control: reap the benefits of connected security
Download
Securing unmanned infrastructure at the network edge
Download
Connected video technology for safe cities
Download
10 top insights in access, cloud and more
Download
Protecting dormitory residents and assets
Download
11 reasons video surveillance is moving to the cloud
Download
How to migrate to an IP-based access control system
Download
The inevitability of The Cloud
DownloadMaking sense of today’s security camera options
Download
Smart security cameras: excellence in retail
Download
Access control & intelligent vehicle screening
Download
How to get buy-in from IT departments on IP video installations
Download
Hikvision DarkFighter Technology for high-quality images at night
Download
Enhanced Ethernet Technology (ePoE)
Download
Video technology: making cities safer & improving lives
Download
Integrated access control: reap the benefits of connected security
Download
Securing unmanned infrastructure at the network edge
Download
Connected video technology for safe cities
Download
10 top insights in access, cloud and more
Download
Protecting dormitory residents and assets
Download
11 reasons video surveillance is moving to the cloud
Download
How to migrate to an IP-based access control system
Download

Videos
Network cameras: Manufacturers & Suppliers
- Hikvision Network cameras
- Dahua Technology Network cameras
- Axis Communications Network cameras
- exacqVision Network cameras
- Bosch Network cameras
- Hanwha Vision Network cameras
- Honeywell Security Network cameras
- VIVOTEK Network cameras
- AV Costar Network cameras
- LILIN Network cameras
- Messoa Network cameras
- Panasonic Network cameras
- Milesight Network cameras
- eneo Network cameras
- Sony Network cameras
- Vicon Network cameras
- Pelco Network cameras
- FLIR Systems Network cameras
- Surveon Network cameras
- IDIS Network cameras

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download