Fingerprint reader
Anviz, a pioneer in intelligent security solutions, proudly announces the launch of W2 Face, its latest hybrid biometric access control and attendance terminal. Designed to meet the evolving needs of modern enterprises, the W2 Face combines facial recognition, fingerprint authentication, and RFID capabilities in a compact, intelligent device built for dynamic workplaces. Responding to market evolution As the access control landscape shifts toward integrated multi-biometric solutions, business...
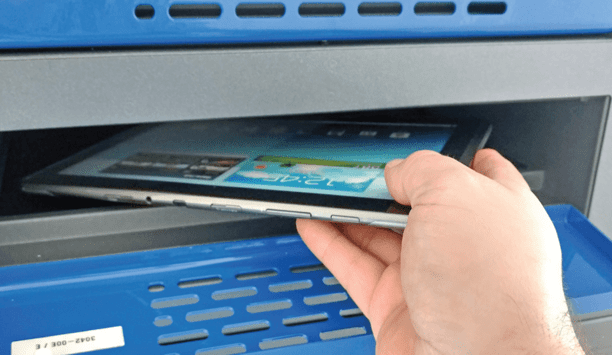
NEXT Biometrics, the world pioneer in advanced high-security fingerprint sensor technology, has received the first major purchase order for its FAP 20 sensor in Nigeria. NEXT has already delivered an initial order of NOK 1.7 million during the first quarter of 2025. The NEXT FAP 20 sensor offers unparalleled performance and reliability, setting a new standard for secure identity verification. Integrated into POS terminals Sensor will be integrated into POS terminals to bring strong authentica...
Blackline Safety Corp., a global pioneer in connected safety technology, announced it has been named to Fast Company’s prestigious list of the World’s Most Innovative Companies of 2025. The annual Fast Company ranking recognises companies making meaningful strides across industries through bold thinking and impactful innovation. Smarter solutions for safety Blackline earned its place on the list for transforming the way organisations protect their peopleThis year’s hon...
Wavelynx Technologies, a pioneer in secure and versatile reader and credential solutions, has expanded its global reach into the United Kingdom and Ireland to support the increasing demand for modern security solutions. This strategic move comes as the company scales its operations to ensure that all customers have access to interoperable solutions that align with the growing need for advanced security across sectors such as commercial real estate, hospitality, education, and healthcare....
In today's rapidly evolving security landscape, facial recognition has become a buzzword that often triggers privacy and data protection concerns. However, many security professionals may not realise that "facial recognition" is an umbrella term encompassing various technologies, each with distinct applications and privacy implications. Let's dive into what these technologies really mean for security system resellers, integrators, and end-users. Facial recognition tech At its core, faci...
Integrated Systems Europe (ISE) is the annual meeting place for the audiovisual and systems integration industry. It will take place for the 21st time in 2025. DoorBird, a manufacturer of smart door communication products, will also be at ISE from February 4 to 7 to present its innovations. At stand 2H300, visitors can get to know the wide range of door communication products and see the features of the latest product developments for themselves. D31TDH and D31TDV With the IP video door...
News
Fime has supported ELAN Microelectronics, a global pioneer in human-machine interfaces, in achieving FIDO Biometric Component Certification for its fingerprint authentication solution. FIDO authenticators can now integrate the sensors to further strengthen customer authentication and support the industry drive to reduce the world’s reliance on passwords. Access to digital services The use of a certified biometric component is optional for level 1 and level 2 FIDO authenticators The FIDO certification program aims to empower organisations to make informed decisions when selecting biometric identity verification solutions and ensure secure, resilient, and equitable access to digital services for everyone. The use of a certified biometric component is optional for level 1 and level 2 FIDO authenticators. At level 3 and higher, authenticators must use a certified biometric component if a biometric modality is used for authentication. FIDO authentication and biometrics “All FIDO authentication is a significant improvement on outdated PINs and passwords,” comments Stephanie El Rhomri, Vice President of Product & Strategy at Fime. “Taking this one step further, we see the combination of FIDO authentication and biometrics as the sweet spot for high security and convenience online, with certification schemes helping to raise the bar for solutions throughout the ecosystem to protect users and their data.” FIDO Biometric Component Level 2 Certification During PAD testing, its IAPAR was less than 1% against a model of 7% over the course of 2,100 trades ELAN’s fingerprint solution achieved FIDO Biometric Component Level 2 Certification with results far exceeding the specified benchmarks. Its solution tested with a False Acceptance Rate (FAR) of 0% against the benchmark of 1%, and a False Rejection Rate (FRR) of 3.6% against a benchmark of 7%. During Presentation Attack Detection (PAD) testing, its Impostor Attack Presentation Accept Rate (IAPAR) was less than 1% against a benchmark of 7% over the course of 2,100 transactions. New markets and opportunities for ELAN “Fime is our long-time partner for biometric testing and certification, and so we knew where to go to achieve a swift and successful certification,” comments Joe Yeh, Executive Vice President at ELAN. “FIDO’s certification program helps drive the ecosystem to adopt higher-quality biometric systems for authentication, and successful certification with Fime is opening up new markets and opportunities for ELAN.” Fime’s EMEA and Taiwan test laboratories are accredited by FIDO to perform biometric evaluations under its Biometric Component Certification Program. Fime is a Sponsor Level Member of the FIDO Alliance. Learn more about how Fime can help maximise new opportunities in the biometrics ecosystem.
Invixium, a global pioneer in biometric access control, workforce, and visitor management along with RTLS-connected worker solutions announces an enhanced integration of their software platform, IXM WEB 3.0 with System Galaxy software v11.8.5. This integration offers a seamless connection between the two systems, enabling seamless data exchange and providing a scalable, unified platform to manage access control information. Range of access control Dealers of Galaxy Control Systems will be able to purchase all Invixium products For ease, dealers of Galaxy Control Systems will be able to purchase all Invixium products, including the all-new Enterprise Series – IXM ROSTO (face + card) and IXM TOUCH 3 (finger + card) directly from Galaxy Control Systems. “Galaxy Control is a valued long-term partner and reseller and we are excited to announce this enhanced integration,” said Shiraz Kapadia, CEO & President at Invixium. “Our longstanding and trusted partnership with Galaxy ensures that integrators and end users can rely on this solution to deliver continual innovation, quality, and value for a wide range of access control needs.” Uncompromised performance and scalability “Demand for high-performance access control solutions is on the rise, and this integration offers our customers with uncompromised performance and scalability,” said Rick Caruthers, President at Galaxy Control Systems. “This collaboration brings together the strengths of both systems, delivering enhanced functionality that supports the growing customer base.” Security management solution System Galaxy software is a complete access control and security management solution System Galaxy software is a complete access control and security management solution. This upgraded integration enables auto-face enrolment, eliminating the need for tedious manual processes. With this feature, users who have a picture on their profile will be automatically enrolled, significantly reducing setup times. This integration also enables efficient identity management, individualised identity-based door access, and the ability to generate specific reports for each screen view or credential holder. Galaxy Control Systems’ cloud software Invixium’s biometric solutions seamlessly integrate with Galaxy Control Systems’ cloud software, delivering a flexible, scalable, and complete solution for customers. Galaxy Control Systems is an authorised value-added distributor of Invixium biometric solutions.
ISC West and its premier sponsor, the Security Industry Association (SIA), are excited to announce the return of the highly anticipated ISC West Concert, set to take place on April 2, 2025, at 5 p.m. at The Venetian Expo in Las Vegas. Headlining the concert will be the iconic rock band Gin Blossoms, bringing their signature hits and unforgettable energy to the ISC West Main Stage. Headline sponsor Wavelynx, the open and secure access platform of readers, Wallet credentials, and physical credential solutions enabling scalable access across the globe, returns as the headline sponsor for the ISC West Concert. As a company committed to advancing security technologies, Wavelynx is excited to support this unique event, combining industry innovation with entertainment. Live musical performance The ISC West Concert debuted in 2024, marking the first time the show introduced a live musical performance The ISC West Concert debuted in 2024, marking the first time the show introduced a live musical performance as part of the event. The success of that inaugural concert has paved the way for the return of this fan-favorite tradition in 2025. “We’re thrilled to bring the ISC West Concert back for a second year, and even more excited to have Gin Blossoms as the headliner,” said Mary Beth Shaughnessy, ISC Event Vice President. “Last year’s event was an incredible experience for attendees and exhibitors, and we expect 2025 to be even bigger and better. It’s the perfect way to unwind and connect with colleagues and peers after a productive day on the show floor.” Gin Blossoms Gin Blossoms is an American alternative rock band formed in 1987 in Tempe, Arizona. The band rose to prominence following the 1992 release of their first major label debut album, New Miserable Experience, and the first single released from that album, "Hey Jealousy” became a top 25 hit and went gold. New Miserable Experience eventually went quadruple platinum and three other charting singles were released from the album including "Allison Road" and "Until I Fall Away". The band's follow-up album, Congratulations I'm Sorry (1996), went platinum including the Grammy-nominated "As Long as It Matters" and the top 10 single “Follow You Down”. Gin Blossoms continues to tour every year and in recent years has shared the stage with Collective Soul, Barenaked Ladies, and Hootie & The Blowfish. Networking and celebration All registered ISC West attendees and exhibitors can look forward to an evening of live music, networking, and celebration, with the Gin Blossoms performing their classic hits. A valid ISC West badge and ticket are required for entry. A limited number of tickets will be distributed on a first-come, first-served basis at key locations on the show floor.
DNAKE, a global pioneer in IP video intercom and smart home solutions, is excited to introduce its latest innovation: the DK360 Wireless Doorbell Kit. This all-in-one security solution, featuring the stylish DC300 wireless doorbell and the upgraded DM60 indoor monitor, is designed to offer effortless installation, enhanced connectivity, and user-friendly features for modern homes. Smart, durable, stylish 1. Innovative Design Meets Functionality The DC300 combines cutting-edge technology with a sleek design. Its compact build, rounded edges, and frosted, fingerprint-resistant finish make it an elegant addition to any entryway. With a 2 MP camera for high-definition video and a smile-shaped white light design crafted by a Red Dot-winning designer, it’s as functional as it is visually appealing. 2. Enhanced Connectivity with Wi-Fi HaLow This innovative connectivity also reduces power consumption, extending the doorbell’s battery life The standout feature? Wi-Fi HaLow technology, operating on the 866 MHz band, delivers up to 500 meters of transmission range in open areas, making it ideal for larger properties. This innovative connectivity also reduces power consumption, extending the doorbell’s battery life. 3. Flexible and Eco-Friendly Power Options The DC300 supports three versatile power solutions: Rechargeable battery. DC 9-24V power supply. Solar power is ideal for eco-conscious homeowners. 4. Built to Last with Security in Mind Designed for security and durability, the DC300 is IP65-rated for water resistance and includes an optional rain cover. It also features a tamper alarm with sound and light alerts to deter intruders. The DM60 Indoor Monitor: More than just a screen 1. Advanced Visual Experience The DM60 indoor monitor boasts a 7-inch IPS touchscreen with vivid colours, sharper image quality, and a wider viewing angle. Whether mounted on the wall or placed on a tabletop using its built-in stand, the DM60 offers versatile placement options. 2. Seamless Connectivity with Wi-Fi 6 Its Wi-Fi 6 compatibility ensures fast and reliable connections, while the ability to integrate Its Wi-Fi 6 compatibility ensures fast and reliable connections, while the ability to integrate with the smartphone allows for remote call answering and door unlocking via the DNAKE app. 3. User-Friendly Features Additional features include two-way communication for seamless interaction, call logs and a Do Not Disturb mode for added privacy, photo and video capture with support for up to 32GB TF card storage, and a digital photo frame mode that adds a warm, personal touch to the living space. Why Choose the DK360? The DK360 is designed with simplicity, performance, and sustainability in mind. With plug-and-play wireless installation, it takes just minutes to set up. It also incorporates eco-friendly materials and solar-powered options for a greener lifestyle. From its long-range transmission to its intuitive operation, the DK360 is the ideal security upgrade for homeowners seeking modern solutions without the hassle of complex wiring. The DK360 Wireless Doorbell Kit is available.
Dotlines UK has announced the upcoming launch of Audra Security, a new suite of hardware and software security products that promise to level up how homes and small businesses in the UK manage their security and internet usage. Audra is designed to make internet security more accessible to a wider audience, by making it simpler, more affordable and user-friendly, while also championing planet-friendly initiatives. Key features of Audra Security The announcement marks a significant step for Dotlines, an international technology company with a presence in 17 countries. While initially focused on South and Southeast Asian markets, such as Malaysia, Singapore and India, where the product gained rapid traction, the company now aims to capture the attention of UK homes and businesses. Audra is designed to protect families and small businesses without the hefty price tag or the need for extensive IT expertise. Key features include its plug-and-play setup and its cloud-based dashboard for managing network settings and reviewing security information remotely. The Audra Security portfolio is split into Home and Business. For homes, there are two products; Audra Safe and AudraVPN. Enhanced security features Audra Safe is a Wi-Fi router that makes it easy for households to manage the security of their smart devices Audra Safe is a Wi-Fi router that makes it easy for households to manage the security of their smart devices and their family’s online safety at their fingertips. It combines the standard capabilities of a typical router with enhanced security features and app-based controls. This allows parents to group devices and set rules, such as blocking certain types of content or setting time limits, helping to protect their families and encourage healthy online habits. AudraVPN is a freemium VPN service designed for individuals who prioritise online security on the go and it enables high-speed streaming across five devices in a single subscription. Cloud-based central dashboard For businesses, there’s Audra Secure. Audra Secure is a straightforward portfolio of business-specific 2-in-1 router and firewall devices that provide a scalable solution, supporting up to 250 concurrent connected devices. Users can manage the devices and rules across multiple locations from a cloud-based central dashboard. With a simple subscription model and pricing plans that span one, three, and five years, Audra Secure is perfect for businesses that are taking the first steps into protecting their business and need reliable protection without an IT department. Implement advanced security systems Jaki Chowdhury, CEO of Dotlines UK, said: “We believe that staying safe online should be a basic right, not a privilege. We’re incredibly excited to bring Audra to the UK, where it can empower anyone – from busy parents to small business owners – to take control of their internet security, even if they have little to no technical knowledge." “Many homes and small businesses are targeted by opportunistic cyber criminals in a scattergun approach because they usually don’t have much or any protection. They also don’t have the time, knowledge or resources to implement advanced security systems, and they perhaps don’t even need such incredibly powerful features in the first place. Audra will protect at a price and simplicity level that anyone can handle and will help to deter the most common of threats.” Benefits of IT budgets Dotlines UK will pledge to plant up to ten trees as part of its planet-positive efforts For every device sold, Dotlines UK will pledge to plant up to ten trees (depending on the device) as part of its planet-positive efforts. Jaki Chowdhury, CEO of Dotlines UK, said: “We’re not just here to sell a product, we’re committed to creating the biggest possible positive impact, both for the planet and for communities that lack the digital tools many of us take for granted." “Our goal is to democratise internet security. We want to make sure that the benefits of staying safe online are available to everyone, not just large corporations with large IT budgets.” Overall economic growth Audra will initially be focused on the home and small business market via the technology reseller, managed service provider and Internet service provider channels. With promising innovations on the horizon, the company is positioning itself as a fresh and approachable player in a field that often overlooks the needs of those with limited technology knowledge, despite their significant role in the overall economic growth of the country. Audra will be available in the UK from early 2025, with plans to expand into other European and North American markets in the coming years.
Alcatraz AI, a pioneer in access control and AI-powered security solutions, announces the launch of its “Switch to Alcatraz AI” promotion. From November 18, 2024, through February 15, 2025, this initiative offers an exclusive discount for new customers seeking to replace outdated biometric readers with Alcatraz AI’s advanced Rock or Rock X solutions–modern, frictionless facial authentication systems that enhance security without compromising user privacy. Physical and cyber security In landscape, increased security and privacy standards are in place to address evolving concerns and challenges for both physical and cyber security. As new industry regulations are implemented to protect against potential threats, companies using legacy systems often struggle to stay compliant. Alcatraz AI’s solutions Alcatraz AI’s Rock and Rock X keys handle these crises with facial authentication Alcatraz AI’s Rock and Rock X solutions address these concerns with touchless facial authentication, real-time tailgating detection, and robust consent management, all fully compliant with BIPA, GDPR, CCPA, and more. Unlike legacy biometric readers, Alcatraz AI’s solutions maintain data integrity by creating a secure digital profile without exposing personally identifiable information (PII). User images, names, and job titles are never displayed or stored, ensuring compliance and peace of mind. Modern security solutions During the “Switch to Alcatraz AI” promotion, eligible new customers can receive a trade-in credit on each Rock or Rock X device when replacing ten or more outdated biometric access points, including fingerprint, palm, or iris readers. Terms and conditions apply. “Yesterday’s technology is no match for today’s challenges,” said Tina D’Agostin, CEO of Alcatraz AI. “With the Rock and Rock X solutions, companies can make the shift from lagging legacy systems to pioneering-edge, privacy-first technology that seamlessly addresses today’s evolving security issues. Now is the perfect time to step confidently into 2025 with modern security solutions that protect both people and privacy.” Alcatraz AI’s Rock solutions Alcatraz AI’s Rock and Rock X keys empower organisations across multiple industries Alcatraz AI’s Rock and Rock X solutions empower organisations across multiple industries, including data centres, critical infrastructure, healthcare facilities, higher education campuses, entertainment venues, and more, to secure their spaces with cutting-edge technology, ensuring operational efficiency and alignment with evolving privacy standards. With an increase in companies enacting return-to-office (RTO) mandates ahead of 2025, it’s more important than ever for enterprises to prioritise workplace safety and ensure their security is well-equipped to handle the influx of additional people back in the office. Data safety This promotion marks a significant opportunity for enterprises to future-ready their access control and compliance needs and put their people's and data safety at the forefront of their business. Ring in the New Year with Alcatraz AI–make the switch and lead the way in access control technology.


Expert commentary
Choosing the appropriate fingerprint technology for a given application is dependent on factors including the required level of security and matching accuracy, the desired capabilities and features, and the usability to achieve adoption and productivity goals. A successful evaluation process will help ensure that this mature and proven user authentication method performs as expected. Fingerprint biometric advantages The speed, simplicity, accuracy, and cost-effectiveness of the fingerprint method have made it among the most widely used for biometric authentication across industry sectors ranging from banking and finance, retail, and healthcare, to government and law enforcement. It performs biometric technology’s “something you are” function while offering unique characteristics that make it particularly valuable for many applications. Unique identifier The fingerprint biometric has the permanency of being reasonably stable and consistent over time Among these characteristics is the pervasiveness and special nature of the fingerprint -- almost everyone has one, and each is a unique identifier. The fingerprint biometric has the permanency of being reasonably stable and consistent over time. It is also easy to acquire, measure, and process. High adoption rate Another key attribute of a fingerprint biometric is its ability to be protected against threats ranging from abuse and misuse to theft, imitation, and substitution. When it is used with recognition techniques the resulting solution performs with a combination of accuracy, speed, scalability, and ease of use. Fingerprint biometric solutions also have the highest adoption rate among biometric authentication solutions according to an industry report published by Payments Journal. Three interrelated components There are three basic components in any fingerprint biometric system as shown in Figure 1: capture (using a sensor that can capture even the most difficult finger types); liveness detection (using the Presentation Attack Detection – or PAD – technique); and matching (including preventing rejection of a legitimate user). Biometric algorithm The sensor captures and pre-processes the fingerprint data. It must be able to successfully capture fingerprint images for a range of skin types and print conditions under diverse temperatures, humidity, light, surface oil, dust, dirt, and other environmental conditions. A biometric algorithm then extracts minutiae data about the fingerprint ridges (endings, bifurcations, islands, etc.) and their orientation and position. PAD technique Implementing a presentation attack detection (PAD) technique at this stage activates the fingerprint biometric system’s second key element: liveness detection. This verifies the fingerprint’s authenticity and that it belongs to a living person. The system’s third element – matching – occurs after the PAD-verified fingerprint dataset has been securely stored as a record, known as a template, inside an enclave with cryptographic protection. Check for liveness The corresponding template of the legitimate user is then retrieved from secure storage When the fingerprint is presented for matching, it is rechecked for liveness. The corresponding template of the legitimate user is then retrieved from secure storage and the process of matching the fingerprint with this template is executed. This must be completed accurately and without rejecting a legitimate user. Types of fingerprint sensing technologies There are four prevailing categories of sensing technologies used with fingerprint readers: optical, capacitive, thin-film transistor (TFT), and multispectral imaging (MSI). Optical and capacitive method Optical is the most mature sensor technology and offers the benefits of a compact size, good capture Optical is the most mature sensor technology, and offers the benefits of a compact size, good capture and matching performance, a small enough size to fit in most desktop environments or shared workstations, and a high level of accuracy at a cost-effective price point across all use cases. The capacitive method, on the other hand, is less prone to fake finger attempts while also offering a thin and compact size for space-limited applications, the power efficiency to support battery-operated devices, and the ability to handle both indoor and outdoor lighting conditions. TFT technology The third technology goes a step further in capture accuracy. TFT technology can accurately recognise the smallest fingerprint features with ultra-high resolution and is used either as a larger-size matrix capacitive proximity detector (capacitive fingerprint sensor) or a larger-area matrix light detector (optical fingerprint sensor). It is ideal for in-the-field mobile identification applications that require a cost-effective, ultra-slim, and lightweight solution with low power consumption. MSI technology MSI technology differs from all three approaches, projecting multiple colors of light into the finger from different angles to collect both surface and subsurface biometrics data. It captures the most difficult fingerprints of diverse demographics, in a wide range of challenging environments. HID has used this patented technology in fingerprint readers that are compliant with ISO 30107-3 PAD Level 2 for advanced anti-spoofing against fraud. The technology also improves matching and offers sophisticated endpoint security that prohibits cyber criminals from gaining unauthorised access to networks by turning fingerprint readers into secure endpoints. Best practices for technology selection Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership. There are three top considerations: security, suitability, and usability. Each is important and the best approach is to strike a balance between all three. Following are the questions to ask during the selection process: Security: What is the regulatory environment? Financial and government services, healthcare, and law enforcement are some examples of highly regulated sectors with elevated security compliance requirements. Are there mandates in place for advanced capturing and biometric authentication specifications? How important is it to ensure anti-spoofing through liveness detection? Will endpoint security be required so that, if the fingerprint device is hacked, no network, system, or data behind the firewall will be impacted? Suitability: Where will the biometric technology be implemented? There will be additional considerations if it is to be embedded in portable, battery-operated devices that require low power consumption. Where will the technology be used? Will it need to fit into small spaces or be used in challenging indoor or outdoor conditions and environments? Will durability be important? Some deployments will face unpredictable weather and difficult lighting conditions for image capture. Will the technology be used for mission-critical border control or a more common – and less demanding -- commercial use? Usability Is it critical that the technology easily and consistently perform capture and matching? Will there be high volumes of fingerprint captures and matches? Is “friction frustration” a concern? If so, the solution must perform matching quickly and accurately to sustain high levels of user productivity. Will the fingerprint device be used by one person exclusively, or multiple people in a shared workstation setting? How diverse is the user population? Some readers are designed to handle all types of fingerprints and diversified demographics. Different applications Fingerprint biometrics is a proven solution to address real-world challenges, each with its requirements The answers to these questions will help determine the best choice of fingerprint technology. Different applications apply fingerprint biometrics to very different use cases but in all cases. It is a proven solution to address real-world challenges, each with its requirements. For instance, in a healthcare clinician’s terminal area or a similar shared environment with limited space, a durable, low-profile capacitive sensor may be the right answer. For an organisation in a highly regulated, mission-critical environment like a bank or border control agency, advanced technologies such as MSI readers may be needed to avoid the serious repercussions of a spoofed identity or the rejection of a legitimate one. Requirements for a biometric solution These are just a few of the requirements to consider when choosing a fingerprint solution. In banking and finance, alone, fingerprint biometrics is used for applications ranging from transacting at the ATM to customer onboarding (eKYC), compliance (AML/KYC), and fraud prevention. The retail sector adds even more, including age verification, loss prevention, point of sale (POS) security, self-service checkout, and secure time and attendance. Law enforcement organisations have their unique requirements, using fingerprint biometrics for background checks, criminal booking, crime investigation, inmate management, mobile identification, and more. For government agencies, typical applications include benefits distribution, border security, citizen ID, employ authentication (SSO/MFA), and voter registration. Each application requires a thorough assessment of the best fingerprint technology for the job. The right touch The right solution will deliver the optimal balance of security, suitability, and usability Fingerprint biometric solutions empower a wide range of use cases with the simple touch of a finger. The right solution will deliver the optimal balance of security, suitability, and usability based on an analysis of criteria including specific application requirements, the characteristics and size of the user population, and challenges posed by environmental conditions. Accuracy, efficiency, and security The world faces increasingly dangerous fraud, account takeover, and impersonation threats. As industries and enterprises work to improve and evolve their identity and access strategies to combat these threats, fingerprint biometrics continue to prove their value through solutions that meet the key selection criteria while delivering the highest levels of accuracy, efficiency, and security.
Along with the growing adoption of cloud, SaaS applications have accounted for more than triple of the account-takeover attacks between 2019 and 2021, alone. Any given breach can potentially bankrupt many small businesses, with average costs reaching USD 4.35 million in 2022, according to a 2022 IBM report. Every business, no matter its size, must minimise these risks by deploying a range of cybersecurity tools and procedures. One of the most important elements is multifactor authentication (MFA). Some cyber insurance companies mandate MFA as a prerequisite for coverage and others will lower their premiums for companies that have deployed it. These insurers know how much more secure the enterprise is when multiple different verification methods are used for logging into accounts and applications. Importance of Cyber Insurance Cyber insurance has become a must-have for organisations that deploy and rely on digital systems. Small businesses are especially vulnerable to cyber threats since few have invested in the necessary security tools to defend against network breaches, scams and other types of cybercrime. Cyber insurance has become a must-have for organisations that deploy and rely on digital systems The good news is that cyber insurance policies are widely available and offer a broad range of coverage options. Some will pay the costs of direct expenses associated with a network attack as well as legal costs, including litigation defense payments, if the business could not meet contractual obligations because of the breach. Cyber insurance premiums Policies may also cover the cost of losing and then restoring access to technology after a breach. Policies may even cover the costs of transfer payment fraud caused by social engineering, as well as profit losses from reputational damage, although this can be restricted to a finite period of time. Depending on the coverage that is selected, cyber insurance premiums can be expensive, and a policy does not replace the solid foundation of an underlying cybersecurity framework. A foundation that includes MFA will help to stop cybercrime before it is committed while also making it easier to acquire and reduce the costs of cyber insurance. In fact, MFA is now one of the most common conditions for obtaining cyber insurance because of its proven ability to help prevent account takeover attacks and stop identity-related data breaches. Multifactor authentication overview The MFA ‘factors’ for confirming identity during login typically include something the user knows The MFA ‘factors’ for confirming identity during login typically include something the user knows (like a pin), something the user has (like a secure device), and something the user ‘is’ (like presenting a fingerprint or face scan to a reader or camera). Using these factors when accessing sensitive applications, systems, and data helps prevent attackers from compromising accounts. This is true even if the attacker has somehow tricked legitimate users into providing usernames and passwords through phishing schemes, in which seemingly legitimate emails are used to harvest this information. Preventing unauthorised access These types of attacks can be launched at scale and put millions of organisations at risk around the world. Some insurance providers simply will not cover them. They know that MFA can help organisations avoid these ‘user error’ attacks through authentication policies that prevent unauthorised access to any of the organisation's networks, applications and devices, wherever they are located. The U.S. government has also required that all federal agencies use MFA Insurers aren't the only ones recommending and even mandating MFA. The U.S. government has also required that all federal agencies use MFA, per the Executive Order On Improving the Nation's Cybersecurity signed by U.S. President Joe Biden in May 2021. A similar recommendation has been made in Europe as part of ENISA guidelines. The barriers to MFA adoption by SMBs One might wonder why over 40% of small and medium size business(SMBs) in the United States don’t have a cybersecurity plan in place and why less than 15% of the ones that do have a plan, consider it to be inadequate. According to the Cyber Readiness Institute, when we dive deeper into the details, there are three key barriers to MFA adoption: Lack of Awareness — 55% of SMBs are reported to remain unprotected because they’re simply unaware of MFA and its benefits to their organisation. Limited Understanding — Beyond a lack of awareness, 30% of business owners said they don’t utilise MFA because they simply don’t know how it works. In addition to the fundamental functionality, there are a variety of MFA options to consider, including a range of form factors that can be utilised to best meet an organisation’s needs. Perceived Inconvenience — 20% of SMBs believe MFA is too inconvenient, when in reality, we’re all more familiar with the concept than we think. How smaller businesses can best implement MFA SMBs should see MFA as a fundamental piece of a larger cybersecurity puzzle SMBs should see MFA as a fundamental piece of a larger cybersecurity puzzle by allowing them to quickly and easily increase security and convenience. MFA isn’t only about security, its also about convenience. Implementing MFA allows organisations to eliminate reliance on passwords, which can significantly improve user experience. So what should decision-makers know about MFA in order to implement it for their SMB? Ease of Use — The right MFA solution should offer a variety of authentication methods, but should also be easy to adopt and use across the organisation. Multiple Methods and Form Factors — Determine the best combination of authentication methods and form factors. Some providers offer only a small selection, which can tie you down to very basic and inflexible options that do not fully meet your users unique needs. Easy Deployment and Management — Time is money, especially for SMBs. Some solutions can take months to deploy, require extensive training and new installation codes, as well as potential overhauls to existing applications. Look for a solution that can be up and running in days. A Complete Solution — Any MFA solution should provide comprehensive security across all of your assets, including your PCs, mobile devices, applications and networks Compliance — Compliance impacts businesses of all sizes. As such, be sure to find a provider that meets evolving industry standards, including data protection such as GDPR and CCPA. Adaptability — As your business grows, your security needs will also evolve, with some users or parts of your business requiring more security than others. Make sure your provider allows you to scale and adjust accordingly to offer the right security for the right users. Blocking cybercriminal attempts Leading and growing a smaller business is a big challenge. Fortunately, adopting MFA provides a safety net to help block cybercriminal attempts, protect your business’ reputation and most importantly, help protect your bottom line. MFA should be the foundation for any robust security strategy and many cyber insurance companies now require it to reduce premiums and even qualify for coverage. For best results, organisations should choose a solution that is easy to deploy, offers a broad range of authentication options and form factors, and gives users a smooth and convenient authentication experience.
A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutions. In the world of access control systems, biometric advancements allow for more secure authentication measures and seamless security processes. As more products and services hit the market, learn our predictions for the 2023 biometric trends in this article. Biometric access control systems What are biometric access control systems? Biometric access control systems include safety measures like facial and fingerprint recognition, as well as multi factor identification terminals. These systems decide who is authorised to enter a specific room, floor or even the entire building, using a database of stored identifiable features, like someone’s fingerprints. If an individual tries to enter and is not in the system, then they are denied access. Biometric Access Control Trends to Look Out For in 2023 - From multifactor authentication to contactless security measures, discover the five biggest upcoming trends in biometrics for access control. Real-time facial recognition The cloud has offered us new and innovative ways to store vast amounts of data Cloud Biometrics - The cloud has offered us new and innovative ways to store vast amounts of data. Combined with biometrics, this trend will allow security professionals to forgo the dedicated server and store their data on the cloud. Cloud biometrics facilitate real-time facial recognition and other processing-intensive security measures. It even allows for remote monitoring, which will be essential in our new era of hybrid working. Multifactor Authentication - In 2023, multifactor authentication will become the norm. It is already widely used by people to secure their accounts, but it will be vital in access control security. Multifactor authentication adds another layer of security by combining a traditional password with facial recognition or fingerprint biometrics. This approach has previously been reserved for highly sensitive data, but with cybercrimes on the rise, it will soon be used to protect everyday accounts. Highly sensitive data Contactless Biometrics - The most recent advancements in biometrics allow people to go about their day without being interrupted by pin codes and touchpads. Contactless biometrics, combined with integrated systems and algorithms, allow people to move seamlessly without sacrificing security. The latest biometrics, for example, can let a pre-authorised individual into a building, inform the appropriate people that they have arrived and call them an elevator, all without needing to touch a keypad. They care about security, but people also want to trust that their provider shares their values Ethical Biometrics - Increasingly, people are valuing ethical biometrics. They care about security, but people also want to trust that their provider shares their values. People want to know that their data will be protected, in line with privacy laws, and that the biometrics system they use will be unbiased. This new standard for the industry has been growing steadily, but 2023 will bring stricter expectations for ethical security. Digital IDs - More people than ever are using digital IDs. From the humble digital wallet, which we all have on our phones, to more complex applications used in access control, physical cards are seemingly a thing of the past. This shift has required (and will continue to require) a complete overhaul of existing infrastructure to allow for new forms of identification. TLDR: 2023 biometric trends in access control The latest biometric trends will see contactless security measures become the norm. With advancements in cloud biometrics and digital IDs, the latest technologies will continue to allow for new and innovative security solutions. However, with stricter expectations for ethical biometrics and data privacy, any new security trends will need to align with these standards. As the founder of Elite Security, Ben McCayna is passionate about security. He started the company in 2004 after identifying a need for high-quality door and security installations and specialised maintenance for commercial businesses. Ben is one of the leading security experts in London and beyond, thanks to his highly successful company and network of happy clients. Elite Security has grown to offer a wide range of security and access control systems, including fire safety, intercoms, alarms and CCTV. With decades of experience in both business management and security, Ben has established himself as a true expert in his field.
Security beat
Acre is a company built on mergers and acquisitions (M&A). Since its founding in 2012, Acre acquired several familiar access control companies, from Vanderbilt to RS2 Technologies, Open Options to Feenics, and several others. Acre itself was acquired in 2021 by UK-based private equity firm Triton, thus launching a new chapter in the company's history. Don Joos was named the new CEO in 2022 and set about transforming Acre from a collection of acquired companies into a coherent whole (representing various brands). A year later, we recently caught up with Don Joos to discuss the "new Acre" and what's ahead. Q: How does your background inform your approach to leading Acre Security? In physical security, there is a shift to more of a software-centric versus hardware approach Joos: This is my fourth company as CEO. What I’ve found along the way is that no matter the size or type of business, there’s a common theme, the business is going through some form of evolution or transformation because the industry they're in is going through an evolution. And today, in physical security, there is a shift to more of a software-centric versus hardware approach, and there’s a shift occurring that’s pulling us to the cloud. I think a key thing here is that while the industry is evolving, we must keep a careful eye on the evolution of the customer because the customer is the one who will dictate the pace of change, and I think that is what a lot of people sometimes lose sight of. Q: It seems Acre is on the path from being a “collection of small companies” to “a collection of brands within a single company.” Joos: I think most people think of Acre as a federation of companies. Acre Security was seen more as a holding company. For me, I think the biggest misconception is just that: “This is just a federation of companies” versus “This is a business.” Acre Security is a business that has a range of portfolios to address key verticals and pivotal business problems for customers. Because of what’s happening now and the market dynamics that are occurring, it ties back to “Who is Acre Security?” We have a clear answer as to where we want to be from cloud access control versus on-premise access control. We have clear answers regarding market segments, visitor management, and intrusion. When you think about it, those are the core areas of our business. Q: What has surprised you the most in your first year or so at Acre? Joos: I think the thing that surprised me the most was how similar the problems are because I was coming into a new industry. It’s surprising how strong a correlation [security has] to other industry transformations that I’ve been a part of. Q: What are the points of differentiation among the various Acre Security brands? Joos: I think if you go back to the history of the company, it was designed to compete. That is, that's how it was set up under the logic of, “If we have three bids in a deal, it increases the odds that we're going to win one of them.” As we evolve, to have sustained scalable growth, it is not just about going shallow and casting a wide net. It’s about creating a concentrated focus. Some of the technology is just inherently older technology. And so for me, it’s about creating migration paths for the customers to move to more modern technology, such as the cloud. I love our installed base. When you think about the cost of acquisition to get a new cloud customer, it costs a lot less when you have an installed base that you can migrate to the more modern solution versus having to spend the money and the sales energy to hunt for that next opportunity. Q: Where has Acre positioned itself in the marketplace? We can take care of your current needs, but we also have a clear migration path to take care of your future needs Joos: If you're ready to go to the cloud, we have an answer for you. If you're not ready to go to the cloud, but you're ready to take more cloud-based applications to continue to evolve, we have an answer for you. If you're not quite ready yet and you're still looking for a market-leading premises solution, we have an answer for you, and we have a migration path when you're ready down the road. So, you have a safe bet with Acre because we can take care of your current needs, but we also have a clear migration path to take care of your future needs. Q: How are you building up your team? Joos: In 2023, we’re getting a lot of core building blocks in place and making investments in people who have experience in this space or aligned industries. It is a balance. I think we need a group that understands the industry and a group that's going to come into it and challenge why we do things the way we do. I think that makes us unique: we have fresh eyes looking at things from a different perspective. With that, you’re naturally going to end up with a better answer to problems because people are comfortable challenging the status quo. Q: How are you seeking to expand your dealer channel and/or transition it from the various dealers “inherited” in previous acquisitions? Joos: The channel invests in Acre Security. Our success is their success, and so what we're proposing to them is a range of solutions that supports their longevity and their financial success. But we also continue to build out our portfolio through organic technology innovation or M&A. We're continuing to make investments in our channel strategy and how our partners interact with us We're continuing to expand their addressable market if they want to make investments with us. We're continuing to make investments in our channel strategy and how our partners interact with us. The design of our upcoming technology right now is built with the channel in mind. We want to ensure that we are not creating any channel conflict or any perceived channel conflict. I think that's usually the worst kind: when it's perceived but not real. You need to be very upfront and clear with communications. Q: What is the biggest challenge in the industry right now? Joos: Companies and customers are looking to embed security into their workflows. What I mean is these are not just standalone solutions anymore. They’re integrating with enterprise resource planning (ERP) and human resource (HR) software systems. In property management, they want it integrated into the fitness center, they want it integrated into the cafeteria areas and the dry cleaners, and so forth. So, this is about an ecosystem, and there are times when we are going to be the core, and there is going to be a lot of technology that is adjacent to us. There are times when we are the adjacency to someone else's core in a smart city or a smart building. This gets to why having an open application programming interface (API) is going to be an important part of the technology evolution. It cannot be a closed environment anymore; that is part of the past. Q: What’s next for Acre? We're constantly evolving our cloud access control as well as our on-premise access control Joos: There is a lot of work going on with integrating the business into a single Acre Security company. This is an investment year for us, we are adding people to our team. We are making a lot of investments from a systems and technology perspective. We have a lot of work right now going into integrating the business from an IT infrastructure perspective and all the tools that we use from an employee perspective. We are making a lot of investment as it relates to the commercial side. You're going to see some next-gen technology coming out from an intrusion perspective. We're constantly evolving our cloud access control as well as our on-premise access control. We're also bringing software applications, too. Q: What is Acre’s “message” going forward? Joos: One of the takeaways for me is this is not the Acre of the past. We are making some bold changes. New things are happening here; you better pay attention because clearly, something is different. I think that's one. I think the second is that as they spend time within us, they're going to realize the wide range of solutions and use cases that we can address, whether you're in access control or cloud, whether you're in intrusion, whether you are in visitor management, or whether you're looking at some network connectivity solutions. The third thing that I think people are going to see is a whole lot of energy as they talk to our people and the passion that you see from the team. If I wrap those three points up in one kind of statement there, I think my goal is that people walk away saying “Something is going on at Acre Security. We better pay attention.”
Large-scale events, including both corporate and sporting events, are coming back strongly in the aftermath of the pandemic. With the increase in activity comes more demand for oversized credentials preferred by many event planners and end users. Pent-up demand due to the pandemic has caused a tremendous uptick in the entire ID card industry in 2022. The return of large-scale events and in-person trade shows will extend the higher demand for cards well into 2023 and beyond, says Andrew Schonzeit, President of Idesco, a provider of ID card solutions. Supply chain concerns Supply chain concerns will continue as companies seek to upgrade and purchase new ID printers and badges An impact of the pandemic was a shortage of supplies related to the ID card industry, says Schonzeit. Like other industries, several leading ID card and printer manufacturers had supply chain issues, and some deliveries were delayed at times for more than six months. Supply chain concerns will continue into 2023 as more companies return to the workplace and others seek to upgrade their current systems and purchase new ID printers and badges. Persistent price increase concerns “The shortage created hardships for end users and often resulted in them purchasing any solution that was readily available even if it was not the preferred one,” says Schonzeit. Another issue during the pandemic was persistent price increases, due both to inflationary pressures and a shortage of products. The industry was used to stable prices with infrequent increases, but the pandemic changed this quickly. Some companies also decided to upgrade their entire system as employees returning to the office increased demand. Oversized credentials advantages Among the advantages of oversized credentials is the ability to print more information on the card, says Schonzeit. For example, a larger credential allows event organisers to preprint the corporate agenda on the back of the card to increase efficiency. In addition, companies can enhance their brand presence by distributing a nice thick plastic badge to attendees. Two categories Standard credit card size These are generally CR100 size, which is around 40% larger than the standard credit card Oversized badges fall into two main categories. One category is for cards that are larger than the standard credit card size (CR80), but smaller than event badges. These are generally CR100 size, which is around 40% larger than the standard credit card. They are generally used by law enforcement or healthcare institutions. It is easier to see an oversized badge more clearly from a distance than a regular-sized badge. Oversized ID badges The other category of oversized ID badges is used for events, these badges are typically 3.5” by 5.5” and are usually worn around the neck. These events include categories such as sporting events, corporate events, music festivals, and trade shows. The badges are generally used only for the duration of the event and are often kept as souvenirs. Anticipating the needs “My advice for event planners is to manage your expectations about badges as it is very hard to order extra badges at the last minute,” says Schonzeit. “It is important to plan well in advance and anticipate your needs upfront to help avoid a shortage.” Idesco often gets requests from customers to include some type of technology on the credentials. The most common technologies are proximity cards, NFC, and/or UHF. “It is a much ‘cleaner’ and safer solution if the chip can be embedded within the credential as opposed to putting a sticker on the outside of the credential,” says Schonzeit. Additional technologies in credentials Customers wanting technology in their credentials should allow additional lead time Generally, these additional technologies are used for gaining entry to a location (access control), or they can be used for gathering valuable information regarding an event, including attendance at seminars, crowd flow, vending, and food services information, among others. Supply chain issues have led to less availability of many of the most common chips, which can impact delivery times. Customers wanting technology in their credentials should allow additional lead time, says Schonzeit. Applications In addition to corporate events, sporting events, and trade shows, other markets can also benefit from oversized ID badges. Industries include healthcare, government, and law enforcement. Oversized badges are becoming more popular in hospitals, for example, where color coding can make it easy to identify doctors, nurses, and hospital personnel from a distance, even in congested hospital spaces. ID card necessity Could there be a negative impact on the ID card industry if more companies allow employees to work from home? It’s always a possibility, says Schonzeit. “However, with many hybrid options out there, most employees are required to come to the office either one or two days a week,” he says. “Employees will still need a way to access their workplace for meetings, conferences, etc., and will require an ID card to do so.” Mobile vs. physical credentials The growing popularity of mobile credentials has created some concerns in the ID card marketplace The growing popularity of mobile credentials has created some concerns in the ID card marketplace about the continuing need for a physical credential. So far it has not been an issue. “[Mobile credentials] have not had any type of meaningful effect on the physical ID card market,” says Schonzeit. Relying on smartphones “Sometimes these disruptive technologies can linger in the background for some time and then suddenly have a massive effect on the market. This is something to be concerned about, but I don’t think there is an imminent threat.” A big issue with using only mobile credentials is the need for a backup plan rather than relying only on a smartphone to enter a facility. Also, for mobile credentials to work, specialised readers are required, which requires a large investment. “In my opinion, ID badges are here to stay for the long haul,” says Schonzeit.
Across the security industry, power supplies are too often an afterthought and the first item in an access control system to be value-engineered. However, when the power supply fails on a high-end access control device, the system becomes a very expensive paperweight. Fortunately, there are now power supply units available that can enhance system reliability by providing remote diagnostics and real-time reporting and analytics. There is also a mistaken perception that all power supplies are the same, says David Corbin, Director of ASSA ABLOY’S Power Management Strategic Business Unit. Access control and security applications Power supplies today are more important than ever for access control and security applications The fact is, a properly designed unit for today’s market must have a wide input range, a myriad of features, interface to network, have adequate transient protection, good surge capability and a demonstrated quality level for mission critical reliability, he says. “Power supplies today are more important than ever for access control and security applications,” says Corbin. “From heavy snowstorms in the Midwest and East Coast to the two million Californians that experienced unprecedented power outages, extreme weather conditions have created chaos for millions over the past few months. These events have resulted in students being locked out of schools, hospitals darkening and electronic keypads or card readers shutting down. With events like these on the rise, and an increased reliance on the technology we use to get in and out of the spaces we occupy, power supplies are critical for keeping systems up and running and people safe and secure.” ASSA ABLOY's LifeSafety Power’s FPO Intelligent Power Supplies and Helix Redundant Power Systems Installing right power supplies ASSA ABLOY has a range of products within the power supplies category, including LifeSafety Power’s FPO Intelligent Power Supplies and Helix Redundant Power Systems. ASSA ABLOY’s acquisition of LifeSafety Power in September expanded the company’s offering of smart integrated access control power solutions for OEMs, integrators and end-users. Other ASSA ABLOY power supply products include Securitron AQ Series Switching Power Supplies, and eco-friendly, linear, plug-in and solar power supplies, as well as Power over Ethernet (PoE). Access control is crucial to security and life safety, says Corbin. And without power, any protective system is useless. When the right power supplies are installed correctly, the system will have built-in backup power that will be triggered during an outage. Dependable power supplies, with regularly replaced and appropriately sized backup batteries, are critical to keeping occupants safe in an emergency event. Other ASSA ABLOY power supply products include Securitron AQ Series Switching Power Supplies Periodic testing of the battery When it comes to extreme weather conditions, the result of a power outage can lead to hazardous situations for employees, patients, residents and students, he says. Buildings that require power to gain access can leave people stranded outside or locked inside. “When access controls are disabled, intruders can easily enter buildings without notice, affording the opportunity for interruptions to power distribution, water supplies and other necessary public utilities,” says Corbin. Preparation for the next big power outage should include the sizing of power supplies to the system requirement with a reasonable safety factor for foreseeable system expansion and a battery set that is sized for operating the system for a period of time greater than the planned requirement, he says. Using a ‘smart’ power supply provides early warning of an impending failure; and consistent, periodic testing of the battery set keeps the system in peak operating condition. Predictive maintenance of access control Predictive analytics and data harvesting can help with predictive maintenance of access control Redundancy ensures that power remains available in the event of a failure, regardless of whether it is a blackout situation or a failure of the power supply itself, says Corbin. “In critical power installations where redundancy is vital, the system must have a properly sized and maintained backup battery,” says Corbin. “Additionally, further redundancy can be achieved via products like our Helix systems that provide for seamless switching between two different power supplies in the event of an electrical failure of one of the power supplies.” Corbin also notes there is a growing want and need for more data and analytics in the access control field. End users increasingly expect access control systems to be able to integrate with building information systems. Predictive analytics and data harvesting can help with predictive maintenance of access control and building systems. For example, intelligent power supplies can identify problems before they happen – such as performing periodic, automated battery tests and then notifying a central monitoring location and/or a facility manager of a battery that needs replacement. Lock operation can also be monitored on a real-time basis for failure or impending failure of a secured door opening, he says.
Case studies
For years, the Civil Police of the State of São Paulo, Brazil’s largest state police force faced significant challenges with criminal bookings and identification, including: A Fragmented Identity System - Each of Brazil’s 27 states has its own siloed programme that does not interconnect. This not only hinders statewide criminal booking but also undermines the community’s confidence in the criminal justice system. Identity Fraud With Multiple IDs - Imagine having 43 identities. This was the case for one unlawful Brazilian. The prevalence of identity fraud is extremely high across the country. If a person wants to hide their identity, it’s common for them to simply move to another state and set up a new profile. Manual Ink-and-Paper Fingerprinting Techniques - Many law enforcement departments across Brazil administered manual fingerprinting techniques, resulting in inaccuracies and low matching rates. Slow, Inefficient Criminal Booking Processes - Inefficiency was another setback for justice. It took numerous steps to confirm one’s identity and, on average, a whole workweek to get matching results returned. Biometric National ID Compliance - The civil police must modernise systems to comply with the Brazilian government’s mandates for all citizens to tie biometrics to their IDs. The Civil Police of the State of São Paulo needed a more reliable and efficient solution to break down identification silos and put the agency on the path toward a unified, national system rooted in the power of biometrics. HID's solution The HID ten-print scanner is designed to quickly capture flat and rolled fingerprints for background checks Working through HID’s partner, Golden Distribuidora, one of Brazil’s largest distributors of IT products, the Civil Police of the State of São Paulo selected a comprehensive biometrics-based identification system called BioKit, featuring HID’s ten-print scanner. The HID ten-print scanner is designed to quickly capture flat and rolled fingerprints for background checks and identity validation programmes. It is also certified for FBI Appendix F (FAP 60) and offers an economical approach to fingerprint acquisition without sacrificing image quality. Automated Biometric Identification System The criminal booking process at São Paulo civil police stations is simplified and can be accomplished in minutes not days. First, agents use HID’s ten-print scanner to capture fingerprints and determine if the individual has a biometric file on record. The fingerprint images are compared against the state-run Automated Biometric Identification System (ABIS). If there is a match, the civil police move forward with their investigation. If there is no match, the officer then creates a new biographic/biometric profile for the individual in question and enrolls them into the ABIS. HID ten-print scanner HID ten-print scanners deliver superior performance and reliability at a competitive price point. Key advantages include: High-Quality Tenprint Capture - The scanner is FBI Appendix F (FAP 60) certified and can quickly capture high-resolution rolled and flat fingerprints. Ease of Use - User-friendly pictographs and LED indicators simplify the process for operators. Automatic Capture - Patented “Auto-Capture” offers fast and error-free image capture. Difficult Fingerprint Capability - An optional silicone membrane improves image quality for dry or damaged skin ensuring consistent results. ABIS Integration - The scanner seamlessly integrates with Brazil’s Automated Biometric Identification System (ABIS) to enable quick and accurate background checks. Results delivered Using the BioKit system, featuring the HID ten-print scanner significantly streamlines the criminal booking Using the BioKit system, featuring the HID ten-print scanner significantly streamlines the criminal booking process and improves matching accuracy for the State of São Paulo Civil Police. “Working with criminals can be difficult and dangerous, and the HID ten-print scanners help us identify and book criminals quickly and simply,” said Dr. Luiz Ortiz, Chief Delegate, Civil Police of the State of São Paulo. Easy to use Dr. Luiz Ortiz adds, “The HID ten-print scanner is easy to use and provides clear direction through pictographs, which is a big differentiator from other offerings.” To date, the BioKit system with HID’s print scanners is deployed in 500 civil police stations throughout São Paulo. This system has transformed criminal booking and identification processes, resulting in an increase in solved criminal cases and a steep reduction in identity fraud. HID fingerprint technology “What used to take 4 to 5 days is now done in minutes using the BioKit system and HID fingerprint technology,” said Dr. Ortiz. Dr. Ortiz adds, “Our agents can accurately identify or onboard suspects, and each new biometric enrollment into the centralised ABIS contributes to strengthening our country’s overall identity system and ability to bring about justice faster and smarter.” Biometric enrollment and verification “Each individual the Civil Police of the State of São Paulo onboards ties to a single set of fingerprints that verifies their true identity,” said Danilo Fernandes, Business Development Manager at Golden Distribuidora. Danilo Fernandes adds, “Utilising biometric enrollment and verification, our nation has the potential to streamline millions of records, while preventing countless cases of fraud. This establishes a fierce force to fight fraud here in Brazil.” A simple, fast, and trusted experience Additional use cases for the BioKit + HID ten-print scanner, beyond criminal bookings, include border control, background checks, correctional centres, courtrooms, voter registration, and national ID programmes. The team at Golden Distribuidora expects to continue distributing these biometric systems throughout the country to support Brazil in combating fraud and making biometric enrollment and identification a simple, fast, and trusted experience for all citizens and stakeholders.
Established in 1997, Dubai-based BMA International operates fashion retail in the Middle East and Asia across the Kingdom of Saudi Arabia (KSA), United Arab Emirates (UAE), Bahrain, Oman, Kuwait and Qatar with more than 250 stores offering two major brands — Redtag and twenty4. BMA’s steady growth is a testament to its focus on building trust with its shoppers, employees, suppliers and stakeholders to create a company that is people-centric, ambitious and results-oriented. Challenge Fraud is a common problem in the retail sector, particularly within large chains with hundreds of locations and tens of thousands of employees. BMA’s retail stores were no exception. Following an internal audit, security of point-of-sale (POS) terminals in retail outlets were identified as a serious concern, particularly the misuse of floor supervisors’ credentials to access terminals and modify or cancel transactions. The problem persisted even after BMA switched from passwords to a smart card-based authentication system The problem persisted even after BMA switched from passwords to a smart card-based authentication system. The most common issues involved supervisors leaving smart cards with cashiers to use in their absence and failing to return the cards when separation from an employer occurs — a frequent occurrence as many of BMA’s retail employees are expatriates who often return to their home countries. Fraudulent use of the smart card was also a common problem. Once a sale was completed and the customer had left the store with their purchased items, the smart card could be used to improperly access the system so the cashier could void the transaction and pocket the “refund,” resulting in both monetary and inventory losses. Biometric-based system “BMA’s internal auditors were concerned with the lack of control over the cards and the potential for fraudulent transactions due to their mishandling. They observed clear gaps in security and authentication practices that led directly to fraud and revenue leakage, resulting in the Internal Audit Committee recommending to the BMA Board of Directors that action be taken to plug the security holes by tightening the authentication process,” said Nainan M. Kurian, CEO of Technowave International LLC. The decision was made to transition authentication to a biometric-based system that would provide the required security at a competitive price that aligned with the aesthetics of the retail stores. The system also needed to be compatible with the Oracle Retail Xstore Office Cloud Service, which BMA International was adopting across its brands. Solution A fingerprint reader from HID is ideal for use by multiple people in a shared environment BMA International and its technology partner, Technowave International LLC, determined that the HID DigitalPersona® 4500 Fingerprint Reader met all their requirements — a decision supported by recommendations from other retailers that had deployed the product, and by the fact that competitive solutions were incompatible with Oracle Retail Xstore, a crucial requirement. A USB peripheral with a compact design to conserve space, this fingerprint reader from HID is ideal for use by multiple people in a shared environment. Its professional, modern design looks elegant in retail settings while offering superior authentication control via biometric functionality that uses optical scanning technology to achieve excellent image quality and reliability. HID DigitalPersona 4500 Fingerprint Reader With this easy-to-use technology, floor supervisors simply place their finger on the reader window, which rapidly captures and encrypts the fingerprint image, and then provides a red flash as a visual cue indicating that it was properly captured. That image is sent to the DigitalPersona FingerJetTM biometric engine for verification, and once the user has been authenticated, access to the POS terminal is granted. “Deploying the HID DigitalPersona 4500 Fingerprint Reader was simple and caused no disruption to retail operations. It paved the way for significant reduction in the malpractice that had been occurring with the smart card system,” said Kurian. Result Since deploying more than 1,100 HID fingerprint readers in retail outlets across KSA, UAE, Oman, Bahrain, Kuwait and Qatar, BMA has eliminated nearly all POS fraud and abuse. The system has also driven tangible improvements in the attendance and punctuality of floor supervisors, who must now be physically present in the store for authentication to take place. The HID authentication system is also capable of multiple types of authentications — providing flexibility that is appreciated by users who work at multiple locations. “Because the HID DigitalPersona 4500 Fingerprint Reader requires proof of presence for authentication, there is greater accountability among supervisors which resulted in immediate cessation of POS fraud and stopped both revenue and inventory leakage. The exceptional support provided by HID Global has also allowed BMA to take full advantage of the system’s functionality and flexibility,” said Kurian.
Cequence announced that the world's largest navigation device manufacturer has chosen the Cequence bot detection and mitigation solution API Spartan, part of the overall Unified API Protection (UAP) platform, to secure its e-commerce experience and deliver a frictionless shopping experience for its customers. The company joins an already elite roster of clients, standing alongside industry giants spanning diverse sectors such as beauty, retail, government, telecommunications, systems integration, international voice traffic carriers, online automotive, motorcycle enthusiasts, and marine classifieds. Boosting online security As the company aimed to boost online security, it faced alarming numbers: about 100 million SSO login requests monthly, with 15 to 20 percent flagged as malicious. They also uncovered significant financial risks, with account takeovers costing anywhere from $50 (£40) to $12,000 (£9,500) each. Ignoring these unsettling numbers might have spelled financial disaster for the business, potentially surpassing the billion-dollar mark. Lack of behavioural analysis The previous solution relied solely on identifying bots based on bad IP addresses, which proved inadequate In light of the company’s previous experience with a prominent internet security provider that utilised rudimentary bot protection methods, it became evident that their efficacy in stopping malicious bots was compromised. The previous solution relied solely on identifying bots based on bad IP addresses, which proved inadequate in detecting many sophisticated malicious bots due to the lack of behavioural analysis. Consequently, the navigation device manufacturer faced challenges in effectively mitigating bot attacks and ensuring business continuity and customer experience. Cequence API Spartan Recognising the limitations of their existing bot protection measures, the customer sought a more proactive and comprehensive bot management solution like Cequence API Spartan to safeguard their business continuity, protect their online assets, and enhance the overall customer experience. Cequence's ability to distinguish genuine users from bots in real-time and adapt to evolving bot tactics resonated with the company, offering a reliable and future-proof solution to their bot problem. Proactive and comprehensive bot management "Bots aren't just a technical nuisance; they're customer experience assassins,” said Ameya Talwalkar, CEO of Cequence. “Imagine loyal customers, eager to purchase your products, locked out by an army of automated bad actors." "The frustration, lost sales, and reputational damage are a nightmare scenario no business can afford. That's why Cequence is dedicated to providing solutions that go beyond simple bot detection. We empower companies to proactively safeguard their legitimate customers and foster a thriving online environment where trust and genuine interactions flourish." Vulnerability due to automated bot attacks The OWASP API Security Top 10 highlights the vulnerability of poorly secured APIs to automated bot attacks. This blurs the line between traditional API and bot attacks, requiring unified security solutions that address both. Key features of Cequence API Spartan As the only API security solution with bot management capabilities, Cequence provides the navigation device manufacturer with: Continuous Behaviour-based API Threat Detection: Cequence leverages the behavioural fingerprint created by a machine learning-based analytics engine to track sophisticated attacks continuously. Supported by the largest API threat database in the world, with millions of behavioural and malicious infrastructure records, the analysis results are translated into policies and models that can be implemented on day one for high-efficacy protection. Integrated Security Ecosystem: While Cequence offers native real-time attack mitigation capabilities, it seamlessly integrates with existing security solutions such as web application firewalls (WAFs). This collaborative approach ensures holistic protection, allowing organisations to leverage the strengths of multiple security tools for enhanced API security and threat mitigation. Protection in Minutes: Cequence can be enabled to protect your APIs and web applications in as little as 15 minutes and can immediately begin reducing the operational burden associated with preventing attacks that can result in fraud, data loss, and business disruption. Advanced AI and machine learning The current e-commerce environment is increasingly vulnerable to bots exploiting loopholes in business logic. Cequence offers a robust solution to protect web and mobile applications, as well as their underlying API infrastructure, from business logic abuse. Leveraging advanced AI and machine learning, Cequence analyses incoming traffic to effectively identify and thwart even subtle attempts at exploitation.
Situated in Vadodara, Gujarat, India, this venerable university stands as one of the oldest in the country, tracing its roots back to 1881. Honouring a forward-thinking ruler, it has evolved into a prominent public institution that provides a diverse array of academic programmes spanning arts, sciences, engineering, and management. Dedicated to delivering top-notch education and cultivating a culture of research and innovation, the university features a sprawling campus and holds a distinguished position for its commitment to excellence in the realm of Indian education. Project overview Confronted with a significant hurdle in the form of a competitor's attendance tracking system for its teaching staff, the university embarked on a quest for a more precise and streamlined method to record daily attendance across its various campuses. The primary goal was to establish a centralised platform dedicated to attendance management, focusing on improving employee access to attendance records and facilitating efficient leave request management. A key consideration was the necessity for a tailored provision to accommodate professors frequently moving A key consideration was the necessity for a tailored provision to accommodate professors frequently moving across campuses for lecture commitments. This case study explores the university's journey in pursuit of a robust attendance management solution catering to 3000 users, addressing specific challenges and optimising operational efficiency. University challenges The university encountered significant challenges in ensuring the smooth operation of its Attendance Management System, including: Inefficiency in the Existing Attendance Management Solution: The university grappled with issues stemming from an ineffective competitor's attendance management system, adding complexity rather than facilitating streamlined operations. This inefficiency extended to the complexities of managing attendance across diverse faculties, further complicating university-level payroll processing. Inconsistencies in Daily Attendance Recording for Teaching Staff: A crucial necessity for the university was the seamless daily recording of professors' attendance. The imperative for a well-organised system became evident to ensure accurate tracking and efficient payroll management. Lack of Proper Attendance Management Across Multiple Campuses: With campuses spread across different locations, the university faced the pressing need to centralise attendance data. This centralisation was crucial for the effective management of attendance records across all campus locations. Delayed Data Transmission from Devices: The existing solution encountered difficulties as punch data from devices experienced delays in reaching the system promptly. This lag resulted in complications, necessitating manual synchronization efforts to rectify the issue. Employee Accessibility Issues for Attendance Data and Leave Management: Staff members encountered limitations in accessing their attendance data through the current system. Furthermore, the absence of support for submitting leave requests contributed to inefficient leave management practices, prompting a demand for more effective solutions. Faced with these operational challenges, the university embarked on a quest for innovative solutions to improve its attendance management processes' overall efficiency and effectiveness. Matrix's solution To address the critical issues faced by the client, Matrix successfully implemented a comprehensive solution that effectively resolved the organisational challenges they were encountering. Matrix executed its Attendance Management System to achieve: Deployment of a Comprehensive Attendance Management System: Matrix effectively implemented an enterprise-grade Time-Attendance Solution, successfully tackling the client's organisational hurdles in attendance management. This solution streamlined the entire attendance process, simplifying complexities across various campuses. Seamless Attendance Recording for Teaching Staff: Matrix introduced biometric devices across different faculties, enabling effortless attendance logging for teaching staff. The widespread availability of devices ensured accurate tracking and efficient payroll management. Centralised Attendance Management Across Multiple Campuses: Matrix established a centralised solution for attendance management, consolidating data from various campuses. This centralised approach facilitated effective control and oversight of attendance across diverse locations. Automated Data Transmission from Devices: Matrix Time-Attendance terminals were equipped with automated data push technology. This feature ensured timely and automated data transfer from devices to the server, eliminating the need for manual synchronisation and enhancing operational efficiency. User-Friendly Employee Self-Service Portal: Matrix provided a comprehensive solution, including an Employee Self-Service portal. This portal enabled users to access attendance data on their devices and submit leave requests. With its hierarchy-based approval system, Matrix streamlined the leave management process. Improved efficiency The innovative solutions offered by Matrix not only resolved the client's challenges but also significantly enhanced attendance operations, promoting improved efficiency throughout the organisation. This case study highlights Matrix's capability to tailor solutions to meet unique client needs, ultimately optimising business processes. Results acheived Matrix successfully streamlined the entire process, introducing clarity in payroll processing and simplifying attendance Matrix's deployment of its Enterprise-grade Time-Attendance Solution brought about a remarkable transformation in the operations of the historic university based in Vadodara. Confronting challenges posed by an inefficient attendance management system, Matrix successfully streamlined the entire process, introducing clarity in payroll processing and simplifying attendance tracking across diverse faculties. The use of Matrix biometric devices facilitated seamless attendance marking for teaching staff, contributing to efficient payroll management. Centralised attendance management The implementation of a centralised attendance management system across multiple campuses significantly improved control and efficiency in handling attendance data. Matrix addressed delays in data transmission by deploying terminals equipped with automated data push technology, eliminating the need for manual synchronisation. Employee Self-Service Portal Matrix's provision of a hierarchy-based approval system streamlined the client’s leave management requirements Furthermore, the implementation included a user-friendly Employee Self-Service Portal, allowing staff to effortlessly view attendance data and submit leave requests. Matrix's provision of a hierarchy-based approval system streamlined the client’s leave management requirements. These tailored solutions markedly enhanced operational efficiency, resulting in a more streamlined, accurate, and transparent organisational operation. Matrix's success in optimising attendance processes underscores its commitment to delivering innovative solutions tailored to the unique requirements of its clients. Products offered COSEC VEGA FOT: Fingerprint and RFID card-based Time-Attendance Terminal COSEC CENTRA PLT: Platform-based User Licence COSEC CENTRA TAM: User Licence for Time-Attendance Management COSEC CENTRA ESS: User Licence for Employee Self-Service Management
On the occasion of INTERPOL’s 91st General Assembly – and 100th anniversary – the world’s largest international police organisation announces the launch of its enhanced BioHUB, powered by IDEMIA’s newest Multibiometric Identification System (MBIS). Multibiometric Identification System This latest version, MBIS 5, integrates new generation algorithms, which provide a higher matching accuracy rate with a shorter response time and a more user-friendly interface. The first phase of its deployment to enhance the identification of potential Persons of Interest (POIs) for police investigations has already been operational since October 2023. The second phase, which will be rolled out over the next two years, will extend this tool to border control points. The system will then be able to perform up to 1 million forensic searches per day, including fingerprints, palm prints and portraits, making it the top performing automated biometric identification system on the market. Cutting-edge technology to help law enforcement IDEMIA still leads the biometric tech race covering iris, fingerprint and face recognition IDEMIA’s commitment to excellence is reflected in its consistently top-ranked identity and security technologies. IDEMIA still leads the biometric tech race covering iris, fingerprint and face recognition. NIST’s (National Institute of Standards and Technology) latest test results underscore IDEMIA’s outstanding expertise and solutions combining efficiency, accuracy and equity. INTERPOL, creating a safer world INTERPOL currently has 196 member countries and enables law enforcement agencies from around the world to work together to make the world a safer place. INTERPOL’s high-tech infrastructure of technical and operational support helps meet the growing challenge of combating crime in the 21st century. Facial recognition is an important and rapidly evolving technology that has opened up many new opportunities to identify individuals and solve crimes. In 2016, INTERPOL opted for IDEMIA’s advanced facial recognition capabilities to create the INTERPOL Face Recognition System (IFRS). INTERPOL Face Recognition System (IFRS) The IFRS contains face images from more than 170 countries, and since its launch, thousands of terrorists, criminals, fugitives, POIs, and missing persons have been identified. In 2019, INTERPOL renewed its contract with IDEMIA to upgrade the current system and transform it into a Multibiometric Identification System (MBIS). IDEMIA and INTERPOL first began their collaboration in 1999, when IDEMIA delivered the original Automated Fingerprint Identification System (AFIS). Automated Fingerprint Identification System (AFIS) AFIS was designed to make cooperation easier between police forces from member countries The Automated Fingerprint Identification System (AFIS) was designed to make cooperation easier between police forces from member countries, by giving them access to global police tools and services, namely forensics, fingerprint evidence and the exchange of forensic data to support international investigations. Through AFIS, authorised users in member countries can view, submit, and cross-check these records using INTERPOL’s secure global police communications network. IDEMIA and INTERPOL share enhanced partnership Cyril Gout, INTERPOL’s Director of Operational Support and Analysis, said “In the same way that criminals use ever more innovative and sophisticated ways to avoid detection, law enforcement must also leverage the latest advances in technology, especially in biometric security, to better combat all forms of transnational crime. INTERPOL’s enhanced partnership with IDEMIA will further help our member countries better protect their borders and communities.” Matt Cole, Group Executive Vice President, Public Security and Identity at IDEMIA, said “IDEMIA is proud to be collaborating with INTERPOL again and to continue making the world a safer place for all. This project reinforces our longstanding partnership with INTERPOL, which has been going strong for over 20 years.” INTERPOL receives delivery of the new MBIS Matt Cole adds, “With the delivery of the new MBIS, developed thanks to our strong dedication to R&D, INTERPOL will have access to cutting-edge fingerprint, palm print and face identification technologies, enabling it and member countries to identify persons of interest faster than ever before.” He continues, “We look forward to many more years of supporting INTERPOL to ensure the safety of potentially billions of citizens around the world.”
Christ’s Hospital School has a long history. It first opened its doors to 380 pupils in November 1552, at that time located in Newgate Street, London. In 2022 the school needed to replace their obsolete security system with a new solution that would be simple to manage while maintaining the security of the site, staff, and pupils. Requirements The school has around 900 students, over 95% of which board. With 18 boarding houses on site, all requiring different access permissions, as well as the school buildings, dining hall, and other common areas. The school’s new security system needed to be able to manage a huge number of doors and users, while still providing a simple, user-friendly experience. Net2 Net2 is Paxton’s flagship, networked access control solution, designed to make the management of any site James Brookes, Operations Manager at Vistec, said, “I’ve been working with Paxton systems for over 12 years, and as soon as I heard the requirements for Christ’s Hospital, I knew that Net2 would be the right solution.” Net2 is Paxton’s flagship, networked access control solution, designed to make the management of any site straightforward. Features and benefits Easy to use and with a range of features, it moves beyond the basics of controlling the flow of people around a building, offering benefits such as building control and system integration. The Net2 system is easily scalable, making it perfectly suited to the school’s needs. Easy installation James Brookes continues, “There were a few challenges to contend with for this installation, including the need to use existing cabling, limited space for hardware storage, and most difficult time!" He adds, "We needed to install over 280 readers and all of the supporting Net2 plus access control units in only six weeks while the students were on their summer holidays. Thanks to the ease of the Net2 system to install, and the occasional help from Paxton’s Technical Support team, we were able to deliver!” Solution I knew Net2 would be a great choice to manage a site of this size, and this time we got to install the Net2 Marine Readers" David, who is responsible for the security decisions made at the school, has experience with Net2 from a previous job and was pleased with the proposal to use it again at Christ’s Hospital. He said, “I knew Net2 would be a great choice to manage a site of this size, and this time we got to install the Net2 Marine Readers. I’d seen them installed when collecting my wife from work, and I just thought I had to have them. They’re visually appealing, but also provide a clear, lit indication of where the door is, and whether access has been granted or denied. I can’t speak more highly of them.” Read-in/read-out access Christ’s Hospital’s new security system provides simple read-in/read-out access on all doors, helping to maintain the security of the site and its staff and students. As every user needs to present their access token to get in and out of a building, the Net2 software can provide exhaustive reporting on how many people are on-site, in any given building, and even pinpoint the location of specific users in an emergency. The school also has an ingenious alert system to ensure the students’ safety; the security team will get a notification if students leave their dorms outside of hours. Keypad readers After a set time, should a student present their Net2 token to a reader to exit the building, an alert will be flagged in the system and the security team will know who is trying to leave the site (and from which building they’ll be trying to exit). To further support the school’s unique requirements, several keypad readers have also been installed on the external doors of relevant buildings, to allow access and egress to temporary students who board over the Easter and Summer holidays. PINs The use of PINs instead of physical tokens in this instance saves time, admin, and money Students will be issued PINs instead of tokens, which may otherwise be lost or not returned. The use of PINs instead of physical tokens in this instance saves time, admin, and money for the school when the students depart at the end of their term. Net2 plus 1 door controller James from Vistec adds, “To overcome the challenge of the limited space, we used the Net2 plus 1 door controller in the PCB-only format and installed a number of them in a single Haydon PSU cabinet to minimise the amount of wall space required for the installation. This is another reason why Net2 was the best option for this site; its flexibility allows us to make it work to our advantage.” Result The Net2 system has been in use since September 2022. All staff, students, and system administrators are pleased with how easy Net2 access control is to use and have fully gotten to grips with all the features. There are plans to further extend the already vast system to secure all of the internal doors on the higher floors of the boarding houses.


Round table discussion
Port forwarding is a networking technique that allows incoming traffic on a specific port number to be redirected to a particular device or application on a local network. Open ports on the network expose an IP video system to the internet. This makes it a potential target for malicious cyberattacks. In the physical security industry, the elimination of port forwarding is seen as a basic and manageable precaution to shore up cybersecurity. We asked this week's Expert Panel Roundtable: What are the risks of port forwarding, and how can manufacturers and/or integrators mitigate those risks?
Technology offers a range of tools to bolster security at public events, including before, during, and after. This year, the 2024 Summer Olympics in Paris will draw the attention of the world, requiring the best protection available for the venues, the athletes, and the attendees. Other happenings such as the FIFA World Cup, the Super Bowl, the Tour de France, and the U.S. NBA Finals are momentous events that challenge security and law enforcement personnel to keep them safe. We asked this week’s Expert Panel Roundtable: How is technology contributing to security in the arena of public events?
Historically, the emphasis of security systems has been on reactivity, whether it’s providing video evidence of an incident or data to support a resulting investigation. Reactivity is core to impactful security, but increasingly, systems are also seeking to be more proactive. A proactive system seeks to prevent events from happening in the first place, thus mitigating the harm to an organisation, and making the need for a reactive response moot. We asked this week’s Expert Panel Roundtable: How can security systems be proactive? Please provide a couple of examples.
Products


Videos
Fingerprint reader: Manufacturers & Suppliers

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download