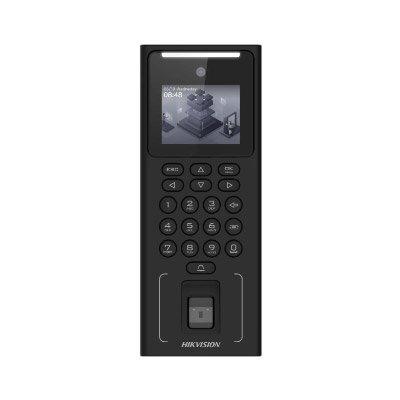
Fingerprint Locks
Camden Door Controls has announced a number of enhancements to its popular CX-DE1200 Series EXIT WATCH™ delayed egress magnetic locks. These include a louder 75 dB voice annunciation, packaging the lock with a 90 dB remote sounder, and adding the option for a cost-effective kit that includes the maglock, remote sounder, and a remote reset key switch. Camden EXIT WATCH™ series Camden EXIT WATCH™ series delayed egress magnetic locks feature a 1200 lb. holding force, rugged al...
Powering digital access with energy-harvesting technology frees organisations from wiring and even batteries. However, to meet the challenges of the future, digital access needs more. It needs technologies and software platforms flexible enough to grow and adapt with the evolving needs of each organisation, protecting their investment in digital access while delivering an ROI every day. Digital access solutions Kinetic energy generated by inserting the intelligent key is harvested to power th...
Managing visitor access efficiently has become a critical component of business operations across industries. With increasing security concerns, regulatory compliance, and the need for seamless visitor experiences, organisations must adopt robust visitor management solutions. Traditional methods such as logbooks and manual tracking are no longer sufficient to meet the security and operational demands of 2025. Digital solutions Modern businesses require digital solutions that not only enhance...
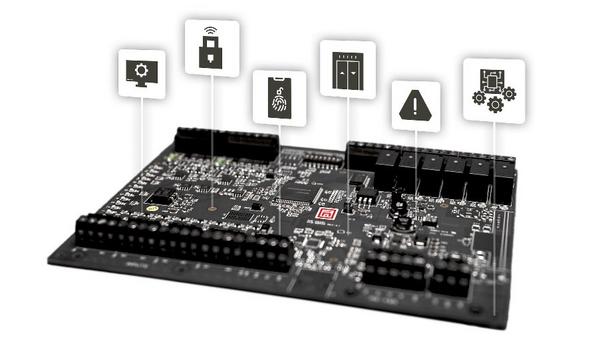
Mercury Security, the pioneer in open architecture access control hardware, is launching a new addition to its industry-defining controller platform—the Mercury embedded application environment, an open platform that enables technology partners and OEMs to develop and deploy custom applications directly on Mercury MP Controllers. “We have a lot of exciting things happening at Mercury,” said Steve Lucas, vice president of sales at Mercury Security. “We are excited to...
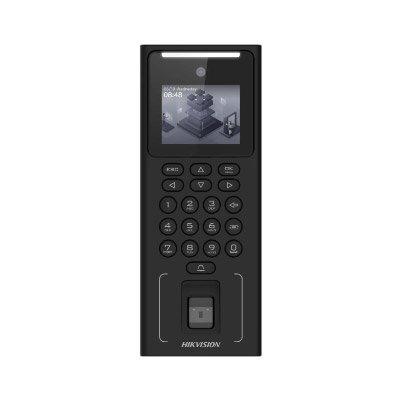
NEXT Biometrics, the world pioneer in advanced high-security fingerprint sensor technology, has received the first major purchase order for its FAP 20 sensor in Nigeria. NEXT has already delivered an initial order of NOK 1.7 million during the first quarter of 2025. The NEXT FAP 20 sensor offers unparalleled performance and reliability, setting a new standard for secure identity verification. Integrated into POS terminals Sensor will be integrated into POS terminals to bring strong authentica...
ASSA ABLOY Opening Solutions will showcase a comprehensive range of access solutions designed to enhance security, convenience, and peace of mind at ISC West, the security industry’s premier international tradeshow. Visit Booth #8061 at ISC West 2025 to explore the latest advancements in comprehensive door security and access control and discuss the real-world challenges with the ASSA ABLOY team of experts. How technologies can transform security “Our mission is to empo...
News
Aiphone, the global pioneer in security communication and access control solutions, will showcase its latest solutions at ISC West 2025, including major updates for AiphoneCloud’s innovative dashboard and Remote Management for commercial applications as well as new AC Series cloud deployment options. Attendees visiting booth #6109 can get first-hand demonstrations of the platform’s remote management capabilities and the complete range of intercom and access control solutions tailored to the unique need of each vertical. Development with remote management The updated Remote Management delivers faster, more secure, and more efficient system deployment The improved AiphoneCloud includes a more intuitive user interface, enhanced efficiency, and comprehensive function updates. These enhancements enable security professionals to streamline every aspect of their relationship with Aiphone, from pre-sales support to product deployment and post-installation account management. The updated Remote Management delivers faster, more secure, and more efficient system deployment. Technicians and integrators can now access the powerful remote capabilities to configure, monitor, and manage Aiphone IP intercom systems from anywhere at any time. Smart, scalable protection “In an increasingly complicated and unpredictable world, simplicity is no longer a luxury, it’s a necessity.” said Sean Peterson, Director of Product, Marketing and Support at Aiphone. "Our enhanced cloud solution represents Aiphone's commitment to delivering flexible, scalable security solutions built for the future." Next-gen access control Building on its cloud momentum, Aiphone is introducing AC Nio cloud hosting option at ISC West, scheduled for release in late April 2025. AC Nio in the cloud makes it a complete, modern access control solution ready to make waves in the industry. The AC Series features a powerful, intuitive dashboard for managing permissions, schedules, and alerts with exceptional scalability and customisation options. Its Nio Scripting Engine enables third-party API integration and event customisation. When combined with intercoms, video management solutions, and wireless locks, the system creates a unified security ecosystem with cloud deployment flexibility to meet evolving security needs. Enhance building access control As the only brand in the industry offering four telephone entry solutions, Aiphone continues to revolutionise access control for multifamily, mixed-use buildings, and commercial properties. Flexible entry options include tenant station door release, mobile app, telephone dialing via SIM, and SIP integration. Each option allows users to see and communicate with visitors before granting entry with the press of a button, enhancing both convenience and security.
Honeywell Building Automation is heading to ISC West 2025, taking place March 31-April 4 at the Venetian Expo in Las Vegas, and this year promises to be a true milestone. For the first time, Honeywell is bringing together two of its powerhouse brands—LenelS2 and Honeywell Commercial Security—in a unified presence. Honeywell's latest offerings Honeywell is displaying a wide variety of the latest offerings that blend LenelS2’s access control Honeywell will be stationed at Booth #18059, showcasing a lineup that is both innovative and time-tested. From AI-powered tools to cloud-based solutions, Honeywell is displaying a wide variety of the latest offerings that blend LenelS2’s access control expertise with top-tier portfolios from Commercial Security. Fire and life safety solutions will also be on display. ISC West attendees—ranging from integrators to end-users—will have a front-row seat to learn how these solutions tackle real-world challenges. Few products and offerings Here’s a sneak peek at a few of the products and offerings that will be featured: Security Management Solutions LenelS2 OnGuard Access Control Solution: Trusted by more than half of the Fortune 100 with extensive breadth and depth of integrations and scalability, it’s powerful, versatile and built to adapt to whatever businesses demand. The latest OnGuard developments focus on enterprise customer experience, extending client capabilities and continued browserisation of clients, expanded FEDGOV and FICAM support and integration with Honeywell’s video solutions. Honeywell Pro-Watch Integrated Security Suite: This enterprise-level solution integrates access control, video surveillance and intrusion detection to help organisations detect and respond to threats sooner, optimise productivity and maintain compliance. The latest features include integrations with BlueDiamond readers and wireless locks, as well as new Mercury MP Series l panels and other installation and deployment improvements. LenelS2 NetBox Access Control Solution: NetBox is a browser-based plug-and-play solution that seamlessly integrates with video surveillance, alarms and third-party products, software or complex configuration for easy scalability as business needs evolve. NetBox continues to enhance ease-of-use and user experience with expanded video capabilities and integrations, improved reporting and visualisations and future LenelS2 HelpBot integration. Integrated Cloud Solutions LenelS2 OnGuard Cloud: Delivering the premier enterprise physical access control muscle of OnGuard now via the cloud—scalable, resilient and updated automatically to meet the needs of various dynamically evolving verticals. LenelS2 Elements cloud-based security management solution: A comprehensive and intuitive access control and video management system, designed specifically for the cloud with a flexible, mobile-first and browser-based interface. Recent releases added support for managing multiple sites and vendor integrations, including additional models of wireless locks, video platforms and hardware manufacturers, while also streamlining badge printing and reducing the number of systems needed to support a company’s overall security ecosystem. Honeywell MAXPRO Cloud: It provides real-time access control and video surveillance on almost any mobile device. It’s perfect for managing one building or an entire campus. Innovation and Emerging Technology BlueDiamond Readers & Mobile Credential Management: Keys? Who needs them? This turns smartphones into touchless access passes with a slick ecosystem that integrates seamlessly with LenelS2 OnGuard, NetBox and Elements platforms and now with Honeywell Pro-Watch to help organisations transition from card-based readers and credentials to mobile-based smartphone credentials as they are ready. One-click credential management is included. Honeywell 35 Series Cameras: Honeywell’s 35 Series of NDAA-compliant cameras offer exceptional picture clarity, flexible system integration, secure data transmission and advanced video analytics with AI insights for everything from small shops to sprawling office, hospitality or enterprise-level facilities. Recent additions include Dual Light Colour cameras that effortlessly switch between infrared and warm light for clear, crisp colour images in extremely low light conditions, pinhole cameras for use in self-checkouts and bank ATMs, 6-12MP Fisheye for monitoring large areas and 5MP Micro Dome with HDMI models for use in retail settings. Honeywell Forge Performance+ for Buildings: This smart solution streamlines visitor management with simplicity, security and compliance at its core. It integrates seamlessly across tools to automate processes, making building operations smoother and more efficient. LenelS2 HelpBot & Honeywell ProWatch HelpBot: AI is part of these proof-of-concept assistants, designed to help make security operations smoother than ever. LenelS2 NetBox ReportBot and ControlBot: Another AI-powered duo in development, working to elevate reporting and system control. Visitors can stop by to see these concepts in action. This is more than just a booth appearance—it’s an opportunity to witness how Honeywell is merging the strengths of its LenelS2 and Commercial Security portfolios to address the security challenges with future technology. How these solutions can elevate security strategies The goal? To spark conversations and show how these tools can fit into any security playbook, from standalone sites to sprawling global networks. The Honeywell team is eager to connect with attendees and demonstrate how these solutions can elevate security strategies for any scale of operation. Attendees are invited to visit Booth #18059 to explore demos, discuss solutions with Honeywell’s experts and catch a glimpse of some future-forward concepts.
System Surveyor has launched its free online System Surveyor Certification Program, available 24/7 for system integrators, security and IoT professionals. The program helps users master the company's site survey and system design software and create accurate survey layouts for proposals, documentation and bill of material reports. Visual collaboration simplified "Our video-based Certification Program helps our software users to become more proficient with site surveys and system design," said Laura Newell, System Surveyor's Director of Operations. "System Surveyor is becoming more broadly adopted across the industry, as it helps users visually collaborate with customers in a professional way.” “Our certified training program is designed to help make the most of these customer engagement opportunities, and our users have seen it as a true differentiation of their expertise and higher productivity.” Certification made simple The program includes online courses with videos, guided tours, and practical assessments. Certified users receive a digital badge for LinkedIn, social profiles, and email signatures, helping them connect with other certified professionals. Key benefits: Hands-on, scenario-based training Increased productivity and time savings Access to updated training materials Who can participate To participate in the Certification Program requires being a registered System Surveyor user. All registered accounts and users will be invited to the program via email. Sign up for a free account. Visit the System Surveyor team in booth #7051 at ISC West 2025 to learn more.
At ISC West, trusted security brands Yale and Master Lock announced their newest lines of smart locks for businesses and multi-family facilities. Part of Fortune Brands Innovations, Inc., Yale and Master Lock are expanding their professional portfolios to offer a new level of security and convenience for multi-family properties, offices, schools, healthcare facilities, small and medium businesses, and more. Product lines under Yale and Master Lock “By launching these new product lines under Yale and Master Lock, we are poised to serve a greater share of the professional market,” said Dave Barry, President of Security & Connected Products at Fortune Brands. “Yale is continuing its legacy of providing flexible solutions for multi-family environments, simplifying access decisions for our partners and operators. Master Lock is delivering solutions to secure access for essential places like schools, healthcare facilities, small and medium businesses, and more.” Key features of Yale’s new multi-family product Yale’s multi-family product line will serve partners and operators with innovative and flexible Yale’s new multi-family product line will serve partners and operators with innovative, flexible, and scalable access control solutions. Designed to enhance security at every entrance, the Yale Pro® 2 Interconnected Lock, Yale Pro® 2 Mortise Lock, and Yale Pro® 2 Cylindrical Lock include key features such as: Flexible Connectivity: With Yale’s range of technology offerings, multi-family properties can choose between: Z-Wave (800 series) module offering long-range support and SmartStart Zigbee module offering app compatibility with top smart home partners Wi-Fi module offering remote access and easy app management Single Action Egress: Meeting all code requirements, multi-family apartment doors can be unlocked in one motion, all with top ANSI/BHMA grading and 90- to 190-minute fire ratings (fire ratings vary by model). Tamper-Proof: Each product is available as a key-free model to provide convenient, keyless access for residence doors—so they can’t be picked, there are no keys to lose, and installers save money by no longer having to address tenant lockouts or rekey apartments after residents move out. Award Winning Design: Modeled after Yale’s award-winning residential product line, Yale Assure Lock® 2, the new multi-family product line features seamless pairing for apartment buildings, no matter what lock style is chosen for apartment or common area doors. Key features of Master Lock Master Lock is also unveiling a new line of locks designed for commercial applications Master Lock is also unveiling a new line of locks designed for commercial applications. The Master Lock Electronic and Connected Mortise Locks and the Master Lock Electronic and Connected Cylindrical Locks offer more advanced access management and tracking, providing commercial owners the confidence that their properties are protected. The introduction of these new products will expand Master Lock’s renowned brand applications to include schools, healthcare facilities, small and medium businesses, and more. Key features include: Flexible Connectivity: With different technology offerings, installers can choose the right technology for their customers, including: Z-Wave (800 series) module offering long-range support and SmartStart Zigbee module offering app compatibility with top smart home partners Non-connected (no module) offering keypad access only Convenient, Key-Free Access: Control access to common areas, exterior doors, residence doors, and stairwells to enhance facility security with access control at every opening. Options for Every Door: Product options are available for standard cylindrical or mortise door prep, and offer top ANSI/BHMA Grade 1 and a 180-minute fire rating. These products will be available for customers to order later this year. Attendees at ISC West can learn more about how Yale and Master Lock are creating safer multi-family housing and businesses at booth #24131.
Altronix, the recognised pioneer in power and data transmission products for the professional security industry, is displaying the company’s latest innovations here at ISC West in booth #11073. Features include integrated power and access control solutions that streamline installation and reduce labour costs, and the latest solutions to deploy IP devices utilising coax, fibre or Ethernet infrastructure. Deployment of advanced IP devices "Altronix continues to deliver new and innovative ways to streamline the deployment of advanced IP devices with greater cost-efficiency, versatility and reliability to ensure heightened security and safety,” said Alan Forman, President of Altronix. “We look forward to demonstrating the numerous advantages and benefits our latest product line-up delivers to our installation partners and customers at ISC West 2025.” New Altronix products on display in booth 11073 Netway Spectrum with EBC48 Integration: The Altronix EBC48 recharges 32AH batteries for NetWay Spectrum models in under eight hours to ensure critical security devices remain operating when there is only intermittent power at the pole. New 277VAC input options now available! Pace™: Advanced technology that extends Ethernet connectivity well beyond traditional limitations, supporting distances up to 1000 metres over a single pair or up to 500 metres over structured cabling, providing an ideal solution for challenging long-distance industrial and IP video applications. Circ™: Advanced multi-path/redundant power solutions ensure seamless transitions between two independent 115VAC or 230VAC inputs, eliminating downtime during power interruptions and power failures, to maintain mission-critical security operations. Trove™ Series: Comprehensive pre-wired, pre-configured access and power kits supporting over 50 pioneering access control brands. including AMAG, AXIS, Azure, Brivo, Hirsch, Mercury, Software House, and TDSi. Easily combine Altronix power with access controllers in scalable wall-mount to extended rack-mount configurations for any installation environment, providing a single point for service and maintenance, minimising wall space. TEMPO724Q: New two-channel network programmable 24/7 timer is designed for diverse applications from security, access control, home automation to lighting control and more. Featuring dual form “C” relay contacts, advanced LINQ™ technology for remote programming and diagnostics, and precise scheduling capabilities, it ensures reliable, synchronised control across complex systems. LINQ™ Network Power Management: Sophisticated remote monitoring platform enabling real-time control and comprehensive reporting of power diagnostics, optimising system performance, preventative maintenance, and overall operational uptime. Altronix Trove™ integration solutions Altronix Trove™ integration solutions will be prominently featured across multiple strategic partner locations throughout the event: Honeywell (LenelS2): Experience Altronix Trove integrated access and power solutions within the comprehensive LenelS2 ecosystem at booth #18059. Inner Range: Discover how Altronix Trove enhances Inner Range's security management systems at booth #25099. Hirsch: Explore access control featuring Altronix Trove access power in wall and rack solutions at booth #13089. PDK: See Altronix's power supply units working with PDK's access control technology at booth #13099. Visit Altronix at ISCW booth #11073 and discover how Altronix power can enhance the security infrastructure.
Gunnebo Safe Storage has strengthened its ModuleGuard range of modular vault doors and strong rooms with ballistic resistance, further enhancing security against physical attacks. Developed through customer insights and research, ModuleGuard from the global security specialist features improved materials and manufacturing processes, reducing its carbon footprint for a more sustainable approach. Its certified bolt assembly allows for easy installation, even in areas with floor load limitations. Fire resistance ratings ModuleGuard Vault Doors (VD T2) and Strong Rooms (SR T2) are now tested and certified to EN 1522 FB2 Alongside burglary resistance certified to EN 1143-1 by ECB•S and fire resistance ratings, the ModuleGuard Vault Doors (VD T2) and Strong Rooms (SR T2) are now tested and certified to EN 1522 FB2 by Banc National d’Épreuve de Saint-Étienne. This classification ensures protection against 9mm pistol attacks, providing an additional layer of defence for high-risk environments. Ballistic resistance to the ModuleGuard range "Security challenges are constantly evolving, and so are our customers’ needs," said Emmanuel Harir-Forouch, Global Business Development Director at Gunnebo Safe Storage. "By introducing ballistic resistance to the ModuleGuard range, we are enhancing both asset protection and personal safety, delivering a more comprehensive and sustainable security solution for high-risk environments." Gunnebo's ModuleGuard range ModuleGuard range now offers a layer of protection for settings where assets and people are at risk Gunnebo's ModuleGuard range features modular, lightweight designs that enable easier installation in locations with space or load constraints. Vault doors are available in T2 grades I, III, and IV, with high-security locking options including key, combination, and electronic locks. By introducing ballistic resistance, the ModuleGuard range now offers an extra layer of protection for environments where both assets and people are at risk. Security concerns Traditionally, vault doors and strong rooms have been designed to protect valuables, but growing security concerns mean there is an increasing need to safeguard individuals as well. Whether in public spaces, high-risk environments, or residential settings, protection against ballistic threats is becoming more relevant. Emmanuel added: "Every security solution we develop is driven by real-world demands. By reinforcing the ModuleGuard range with ballistic resistance, we are ensuring our customers have the confidence that their people and assets are better protected. And from initial design and specification, we can incorporate such bespoke futureproof solutions to achieve targeted security requirements."
Aiphone, the global pioneer in security communication and access control solutions, will showcase its latest solutions at ISC West 2025, including major updates for AiphoneCloud’s innovative dashboard and Remote Management for commercial applications as well as new AC Series cloud deployment options. Attendees visiting booth #6109 can get first-hand demonstrations of the platform’s remote management capabilities and the complete range of intercom and access control solutions tailored to the unique need of each vertical. Development with remote management The updated Remote Management delivers faster, more secure, and more efficient system deployment The improved AiphoneCloud includes a more intuitive user interface, enhanced efficiency, and comprehensive function updates. These enhancements enable security professionals to streamline every aspect of their relationship with Aiphone, from pre-sales support to product deployment and post-installation account management. The updated Remote Management delivers faster, more secure, and more efficient system deployment. Technicians and integrators can now access the powerful remote capabilities to configure, monitor, and manage Aiphone IP intercom systems from anywhere at any time. Smart, scalable protection “In an increasingly complicated and unpredictable world, simplicity is no longer a luxury, it’s a necessity.” said Sean Peterson, Director of Product, Marketing and Support at Aiphone. "Our enhanced cloud solution represents Aiphone's commitment to delivering flexible, scalable security solutions built for the future." Next-gen access control Building on its cloud momentum, Aiphone is introducing AC Nio cloud hosting option at ISC West, scheduled for release in late April 2025. AC Nio in the cloud makes it a complete, modern access control solution ready to make waves in the industry. The AC Series features a powerful, intuitive dashboard for managing permissions, schedules, and alerts with exceptional scalability and customisation options. Its Nio Scripting Engine enables third-party API integration and event customisation. When combined with intercoms, video management solutions, and wireless locks, the system creates a unified security ecosystem with cloud deployment flexibility to meet evolving security needs. Enhance building access control As the only brand in the industry offering four telephone entry solutions, Aiphone continues to revolutionise access control for multifamily, mixed-use buildings, and commercial properties. Flexible entry options include tenant station door release, mobile app, telephone dialing via SIM, and SIP integration. Each option allows users to see and communicate with visitors before granting entry with the press of a button, enhancing both convenience and security.
Honeywell Building Automation is heading to ISC West 2025, taking place March 31-April 4 at the Venetian Expo in Las Vegas, and this year promises to be a true milestone. For the first time, Honeywell is bringing together two of its powerhouse brands—LenelS2 and Honeywell Commercial Security—in a unified presence. Honeywell's latest offerings Honeywell is displaying a wide variety of the latest offerings that blend LenelS2’s access control Honeywell will be stationed at Booth #18059, showcasing a lineup that is both innovative and time-tested. From AI-powered tools to cloud-based solutions, Honeywell is displaying a wide variety of the latest offerings that blend LenelS2’s access control expertise with top-tier portfolios from Commercial Security. Fire and life safety solutions will also be on display. ISC West attendees—ranging from integrators to end-users—will have a front-row seat to learn how these solutions tackle real-world challenges. Few products and offerings Here’s a sneak peek at a few of the products and offerings that will be featured: Security Management Solutions LenelS2 OnGuard Access Control Solution: Trusted by more than half of the Fortune 100 with extensive breadth and depth of integrations and scalability, it’s powerful, versatile and built to adapt to whatever businesses demand. The latest OnGuard developments focus on enterprise customer experience, extending client capabilities and continued browserisation of clients, expanded FEDGOV and FICAM support and integration with Honeywell’s video solutions. Honeywell Pro-Watch Integrated Security Suite: This enterprise-level solution integrates access control, video surveillance and intrusion detection to help organisations detect and respond to threats sooner, optimise productivity and maintain compliance. The latest features include integrations with BlueDiamond readers and wireless locks, as well as new Mercury MP Series l panels and other installation and deployment improvements. LenelS2 NetBox Access Control Solution: NetBox is a browser-based plug-and-play solution that seamlessly integrates with video surveillance, alarms and third-party products, software or complex configuration for easy scalability as business needs evolve. NetBox continues to enhance ease-of-use and user experience with expanded video capabilities and integrations, improved reporting and visualisations and future LenelS2 HelpBot integration. Integrated Cloud Solutions LenelS2 OnGuard Cloud: Delivering the premier enterprise physical access control muscle of OnGuard now via the cloud—scalable, resilient and updated automatically to meet the needs of various dynamically evolving verticals. LenelS2 Elements cloud-based security management solution: A comprehensive and intuitive access control and video management system, designed specifically for the cloud with a flexible, mobile-first and browser-based interface. Recent releases added support for managing multiple sites and vendor integrations, including additional models of wireless locks, video platforms and hardware manufacturers, while also streamlining badge printing and reducing the number of systems needed to support a company’s overall security ecosystem. Honeywell MAXPRO Cloud: It provides real-time access control and video surveillance on almost any mobile device. It’s perfect for managing one building or an entire campus. Innovation and Emerging Technology BlueDiamond Readers & Mobile Credential Management: Keys? Who needs them? This turns smartphones into touchless access passes with a slick ecosystem that integrates seamlessly with LenelS2 OnGuard, NetBox and Elements platforms and now with Honeywell Pro-Watch to help organisations transition from card-based readers and credentials to mobile-based smartphone credentials as they are ready. One-click credential management is included. Honeywell 35 Series Cameras: Honeywell’s 35 Series of NDAA-compliant cameras offer exceptional picture clarity, flexible system integration, secure data transmission and advanced video analytics with AI insights for everything from small shops to sprawling office, hospitality or enterprise-level facilities. Recent additions include Dual Light Colour cameras that effortlessly switch between infrared and warm light for clear, crisp colour images in extremely low light conditions, pinhole cameras for use in self-checkouts and bank ATMs, 6-12MP Fisheye for monitoring large areas and 5MP Micro Dome with HDMI models for use in retail settings. Honeywell Forge Performance+ for Buildings: This smart solution streamlines visitor management with simplicity, security and compliance at its core. It integrates seamlessly across tools to automate processes, making building operations smoother and more efficient. LenelS2 HelpBot & Honeywell ProWatch HelpBot: AI is part of these proof-of-concept assistants, designed to help make security operations smoother than ever. LenelS2 NetBox ReportBot and ControlBot: Another AI-powered duo in development, working to elevate reporting and system control. Visitors can stop by to see these concepts in action. This is more than just a booth appearance—it’s an opportunity to witness how Honeywell is merging the strengths of its LenelS2 and Commercial Security portfolios to address the security challenges with future technology. How these solutions can elevate security strategies The goal? To spark conversations and show how these tools can fit into any security playbook, from standalone sites to sprawling global networks. The Honeywell team is eager to connect with attendees and demonstrate how these solutions can elevate security strategies for any scale of operation. Attendees are invited to visit Booth #18059 to explore demos, discuss solutions with Honeywell’s experts and catch a glimpse of some future-forward concepts.
System Surveyor has launched its free online System Surveyor Certification Program, available 24/7 for system integrators, security and IoT professionals. The program helps users master the company's site survey and system design software and create accurate survey layouts for proposals, documentation and bill of material reports. Visual collaboration simplified "Our video-based Certification Program helps our software users to become more proficient with site surveys and system design," said Laura Newell, System Surveyor's Director of Operations. "System Surveyor is becoming more broadly adopted across the industry, as it helps users visually collaborate with customers in a professional way.” “Our certified training program is designed to help make the most of these customer engagement opportunities, and our users have seen it as a true differentiation of their expertise and higher productivity.” Certification made simple The program includes online courses with videos, guided tours, and practical assessments. Certified users receive a digital badge for LinkedIn, social profiles, and email signatures, helping them connect with other certified professionals. Key benefits: Hands-on, scenario-based training Increased productivity and time savings Access to updated training materials Who can participate To participate in the Certification Program requires being a registered System Surveyor user. All registered accounts and users will be invited to the program via email. Sign up for a free account. Visit the System Surveyor team in booth #7051 at ISC West 2025 to learn more.
At ISC West, trusted security brands Yale and Master Lock announced their newest lines of smart locks for businesses and multi-family facilities. Part of Fortune Brands Innovations, Inc., Yale and Master Lock are expanding their professional portfolios to offer a new level of security and convenience for multi-family properties, offices, schools, healthcare facilities, small and medium businesses, and more. Product lines under Yale and Master Lock “By launching these new product lines under Yale and Master Lock, we are poised to serve a greater share of the professional market,” said Dave Barry, President of Security & Connected Products at Fortune Brands. “Yale is continuing its legacy of providing flexible solutions for multi-family environments, simplifying access decisions for our partners and operators. Master Lock is delivering solutions to secure access for essential places like schools, healthcare facilities, small and medium businesses, and more.” Key features of Yale’s new multi-family product Yale’s multi-family product line will serve partners and operators with innovative and flexible Yale’s new multi-family product line will serve partners and operators with innovative, flexible, and scalable access control solutions. Designed to enhance security at every entrance, the Yale Pro® 2 Interconnected Lock, Yale Pro® 2 Mortise Lock, and Yale Pro® 2 Cylindrical Lock include key features such as: Flexible Connectivity: With Yale’s range of technology offerings, multi-family properties can choose between: Z-Wave (800 series) module offering long-range support and SmartStart Zigbee module offering app compatibility with top smart home partners Wi-Fi module offering remote access and easy app management Single Action Egress: Meeting all code requirements, multi-family apartment doors can be unlocked in one motion, all with top ANSI/BHMA grading and 90- to 190-minute fire ratings (fire ratings vary by model). Tamper-Proof: Each product is available as a key-free model to provide convenient, keyless access for residence doors—so they can’t be picked, there are no keys to lose, and installers save money by no longer having to address tenant lockouts or rekey apartments after residents move out. Award Winning Design: Modeled after Yale’s award-winning residential product line, Yale Assure Lock® 2, the new multi-family product line features seamless pairing for apartment buildings, no matter what lock style is chosen for apartment or common area doors. Key features of Master Lock Master Lock is also unveiling a new line of locks designed for commercial applications Master Lock is also unveiling a new line of locks designed for commercial applications. The Master Lock Electronic and Connected Mortise Locks and the Master Lock Electronic and Connected Cylindrical Locks offer more advanced access management and tracking, providing commercial owners the confidence that their properties are protected. The introduction of these new products will expand Master Lock’s renowned brand applications to include schools, healthcare facilities, small and medium businesses, and more. Key features include: Flexible Connectivity: With different technology offerings, installers can choose the right technology for their customers, including: Z-Wave (800 series) module offering long-range support and SmartStart Zigbee module offering app compatibility with top smart home partners Non-connected (no module) offering keypad access only Convenient, Key-Free Access: Control access to common areas, exterior doors, residence doors, and stairwells to enhance facility security with access control at every opening. Options for Every Door: Product options are available for standard cylindrical or mortise door prep, and offer top ANSI/BHMA Grade 1 and a 180-minute fire rating. These products will be available for customers to order later this year. Attendees at ISC West can learn more about how Yale and Master Lock are creating safer multi-family housing and businesses at booth #24131.
Altronix, the recognised pioneer in power and data transmission products for the professional security industry, is displaying the company’s latest innovations here at ISC West in booth #11073. Features include integrated power and access control solutions that streamline installation and reduce labour costs, and the latest solutions to deploy IP devices utilising coax, fibre or Ethernet infrastructure. Deployment of advanced IP devices "Altronix continues to deliver new and innovative ways to streamline the deployment of advanced IP devices with greater cost-efficiency, versatility and reliability to ensure heightened security and safety,” said Alan Forman, President of Altronix. “We look forward to demonstrating the numerous advantages and benefits our latest product line-up delivers to our installation partners and customers at ISC West 2025.” New Altronix products on display in booth 11073 Netway Spectrum with EBC48 Integration: The Altronix EBC48 recharges 32AH batteries for NetWay Spectrum models in under eight hours to ensure critical security devices remain operating when there is only intermittent power at the pole. New 277VAC input options now available! Pace™: Advanced technology that extends Ethernet connectivity well beyond traditional limitations, supporting distances up to 1000 metres over a single pair or up to 500 metres over structured cabling, providing an ideal solution for challenging long-distance industrial and IP video applications. Circ™: Advanced multi-path/redundant power solutions ensure seamless transitions between two independent 115VAC or 230VAC inputs, eliminating downtime during power interruptions and power failures, to maintain mission-critical security operations. Trove™ Series: Comprehensive pre-wired, pre-configured access and power kits supporting over 50 pioneering access control brands. including AMAG, AXIS, Azure, Brivo, Hirsch, Mercury, Software House, and TDSi. Easily combine Altronix power with access controllers in scalable wall-mount to extended rack-mount configurations for any installation environment, providing a single point for service and maintenance, minimising wall space. TEMPO724Q: New two-channel network programmable 24/7 timer is designed for diverse applications from security, access control, home automation to lighting control and more. Featuring dual form “C” relay contacts, advanced LINQ™ technology for remote programming and diagnostics, and precise scheduling capabilities, it ensures reliable, synchronised control across complex systems. LINQ™ Network Power Management: Sophisticated remote monitoring platform enabling real-time control and comprehensive reporting of power diagnostics, optimising system performance, preventative maintenance, and overall operational uptime. Altronix Trove™ integration solutions Altronix Trove™ integration solutions will be prominently featured across multiple strategic partner locations throughout the event: Honeywell (LenelS2): Experience Altronix Trove integrated access and power solutions within the comprehensive LenelS2 ecosystem at booth #18059. Inner Range: Discover how Altronix Trove enhances Inner Range's security management systems at booth #25099. Hirsch: Explore access control featuring Altronix Trove access power in wall and rack solutions at booth #13089. PDK: See Altronix's power supply units working with PDK's access control technology at booth #13099. Visit Altronix at ISCW booth #11073 and discover how Altronix power can enhance the security infrastructure.
Gunnebo Safe Storage has strengthened its ModuleGuard range of modular vault doors and strong rooms with ballistic resistance, further enhancing security against physical attacks. Developed through customer insights and research, ModuleGuard from the global security specialist features improved materials and manufacturing processes, reducing its carbon footprint for a more sustainable approach. Its certified bolt assembly allows for easy installation, even in areas with floor load limitations. Fire resistance ratings ModuleGuard Vault Doors (VD T2) and Strong Rooms (SR T2) are now tested and certified to EN 1522 FB2 Alongside burglary resistance certified to EN 1143-1 by ECB•S and fire resistance ratings, the ModuleGuard Vault Doors (VD T2) and Strong Rooms (SR T2) are now tested and certified to EN 1522 FB2 by Banc National d’Épreuve de Saint-Étienne. This classification ensures protection against 9mm pistol attacks, providing an additional layer of defence for high-risk environments. Ballistic resistance to the ModuleGuard range "Security challenges are constantly evolving, and so are our customers’ needs," said Emmanuel Harir-Forouch, Global Business Development Director at Gunnebo Safe Storage. "By introducing ballistic resistance to the ModuleGuard range, we are enhancing both asset protection and personal safety, delivering a more comprehensive and sustainable security solution for high-risk environments." Gunnebo's ModuleGuard range ModuleGuard range now offers a layer of protection for settings where assets and people are at risk Gunnebo's ModuleGuard range features modular, lightweight designs that enable easier installation in locations with space or load constraints. Vault doors are available in T2 grades I, III, and IV, with high-security locking options including key, combination, and electronic locks. By introducing ballistic resistance, the ModuleGuard range now offers an extra layer of protection for environments where both assets and people are at risk. Security concerns Traditionally, vault doors and strong rooms have been designed to protect valuables, but growing security concerns mean there is an increasing need to safeguard individuals as well. Whether in public spaces, high-risk environments, or residential settings, protection against ballistic threats is becoming more relevant. Emmanuel added: "Every security solution we develop is driven by real-world demands. By reinforcing the ModuleGuard range with ballistic resistance, we are ensuring our customers have the confidence that their people and assets are better protected. And from initial design and specification, we can incorporate such bespoke futureproof solutions to achieve targeted security requirements."


Expert commentary
Digital access control has well-known benefits over traditional security, of course, but also costs attached to each stage of its lifetime. However, these costs are not fixed. Many factors – including building size, shape, type, location, national regulations and more – impact affordability and efficiency calculations. Crucially, the type of access solution a business selects – wired or wireless – impacts total operating costs, including during installation, running and any potential expansion or reconfiguration stages. Wireless installation Wiring premises can be expensive. So, the potential cost savings from choosing wireless digital access begin at the very start. Installation stage is the largest contributor to potential cost savings when businesses go wireless. In calculations for one report, access experts at ASSA ABLOY examined projected costs for a fictional 100-door installation. Labour savings for those who chose wireless over wired locks were 82.5%. Why? Firstly, because wireless installation is much faster. It is also less intrusive. Most wireless locking devices require little or no drilling of the door, whereas wired security needs cabling through and partly around a door – which means not just door damage, but the contracting of specialist electrical installers who may require multiple site visits. These costs add up. Digital access technology Torus aims for the highest level of LEED certification for all its new properties In Poland, for example, developer Torus aims for the highest level of LEED certification for all their new properties around Gdansk. Where possible, they choose products with Environmental Product Declarations (EPDs) and Green Circle documentation, favouring access solutions which reduce their carbon footprint. Wireless digital access technology is a natural choice. “The lack of wiring significantly reduces materials use, reduces costs, and ensures quick installation,” confirms Torus’ Roman Sokolowski. There’s no cabling, which cuts power consumption. There’s less damage to the building fabric and fitters make fewer journeys to and from the site. Adaptable locking solution By choosing a wireless solution, organisations also upgrade building security with little disruption. A wireless system makes it easier to improve security at an existing building via a retrofit process which does not inconvenience staff or disturb work routines. This was one goal at Plexal, a £15 million flexible work environment for London enterprise and academia. Plexal chose battery powered wireless locks integrated with DoorFlow, NetNodes’ online platform for managing and auditing building access. “Plexal required an adaptable locking solution for a range of different doors and, with no wiring required, it was quick and easy to install ASSA ABLOY Aperio® devices with minimal disruption,” confirms Stewart Johnson, Director at NetNodes. Cost savings with improved energy efficiency Choosing wireless over wired locking can play a vital role in reducing ongoing energy use Choosing wireless over wired locking can play an important role in reducing ongoing energy use – and, therefore, expenditure. Wholesale electricity prices in Europe are approximately double what they were in 2019, according to the IEA’s “Electricity 2024” report. For a variable cost such as energy, where businesses have little control over unit prices, it is critical to control usage, especially if high and/or changeable energy prices become what analysts at ING called “the new normal for business”. Thus, the fact that battery-powered locks consume much less energy than traditional wired solutions is increasingly relevant and important. Additional saving on energy costs Traditional wired door access devices often work via magnets connected permanently to mains electricity. These doors draw power around the clock to remain locked. Wireless locks work differently. They only “wake up” when presented with a credential, to make the access decision. This translates to an additional saving on energy costs during operation: more than 70%, or thousands of euros over a typical access system’s lifetime. Wireless digital access Wireless locks only need a change of their standard battery, which may be rechargeable Related energy and materials costs during in-use stage are also lower. Wireless locks only need a change of their standard battery – which may be rechargeable – typically once every two years. No specialist maintenance is required, saving on specialists and their travel to and from the site(s). By choosing wireless digital access, businesses help protect themselves against these ongoing costs, notably energy price increases and volatility. Cost-efficient flexible working, for staff and facilities managers Perhaps harder to quantify, but equally easy to imagine, the financial benefits of choosing a wireless digital solution are felt in the increased convenience and efficiency of daily operations. In the co-working sector, for example, flexible access to offices is a priority. As “fixed” office space rented by corporations continues to fall, co-working spaces are expected to keep growing, with one estimate suggesting almost 18% CAGR to 2030. To stand out from the competition, the founders of ULab in Alicante sought the latest innovations in access and design to create their 21st-century business centre. Part of the suite of digital access solutions from ASSA ABLOY, a SMARTair® system gave ULab real-time access management via battery-powered locks and Openowä, the Mobile Key solution for SMARTair, without any need to wire doors and other openings. SMARTair TS1000 Web interface With SMARTair and Openow, workspace residents can carry virtual keys on their smartphone With SMARTair and Openow, workspace residents can carry virtual keys on their smartphone; ULab’s security team update their rights over the air. An office manager can perform any operation remotely from the SMARTair TS1000 Web interface. In case of an emergency, they could lock-down the site or open doors remotely, for example. It’s convenient, efficient and boosts ULab’s security, benefiting users and managers. And because of SMARTair’s flexibility, they can comfortably welcome many more than their usual 100 daily users. “In addition to regular daily traffic, weekly traffic can almost multiply by 10 if an event is held,” says Enrique Burgos Pérez, Director at ULab. “We needed an access control system as flexible and convenient as SMARTair.” ASSA ABLOY benchmarking report Choosing wireless locks also adds flexibility – and can reduce costs – when an organisation reconfigures or expands their commercial space. High-quality wireless devices like SMARTair can typically be reinstalled at another opening without impacting reliability. They move to wherever is convenient. If a business is rethinking workspace to encourage flexible or hybrid work patterns, for example, cost efficiencies could be significant. Typical savings on office relocation or expansion are estimated at around 30% with wireless over wired locking, according to the same ASSA ABLOY benchmarking report. Cost efficiency and more control with ASSA ABLOY digital access To refit and improve their student accommodation, managers at the University of St Andrews sought energy- and cost-efficient access control. They chose Aperio, another innovative digital access solution from ASSA ABLOY. Approximately 1,600 doors so far are equipped with battery-powered Aperio escutcheons – without cabling. Aperio devices integrate fully with both the university’s existing central security system and their student ID card. University security managers continue to enjoy the efficiency benefits of monitoring and controlling access from a single point and in real-time, including for doors across multiple buildings. Aperio, another innovative digital access solution from ASSA ABLOY. Benefits of cost-efficiency In comparison to a wired solution, Aperio offers significant cost-efficiency benefits. Devices are wireless, so can be installed with little energy use and no need for wiring to the mains. They consume near-zero energy when idle and run on standard batteries, consuming little power during operation. Through the entire product life-cycle, Aperio combines reliability with cost effectiveness. “Aperio gives us central management and control,” says Pauline Brown, Associate Chief Information Officer at the University of St Andrews, “and contributes to our award-winning track record in energy efficiency.”
As part of ever-evolving technological advancements and the increase in digitisation, home security systems remain a vital piece of equipment for at least 39 million households in the U.S., and as many as 13 million more households may install new security systems in the next 12 months. Global home security market In addition, a recent study found that 60% of burglars are deterred from attempting a burglary when a home has a security system, looking for alternative targets that are easier. Another similar study found homes without security systems are 300% more likely to experience a burglary. It’s estimated the global home security market is expected to grow to $84.4 billion as more and more people install home security systems as a way to ensure their safety. High-tech security devices Home security systems and the technology behind them will continue to expand and integrate further With the ongoing need for home security systems and the introduction of technology such as Artificial Intelligence (AI), home security companies are finding new and innovative ways to improve the home security experience by installing high-tech security devices. These devices are changing how we protect our homes, valuables, families, pets, and more. As we look ahead to the future, home security systems and the technology behind them will continue to expand and integrate further within the home as AI evolves and takes on a more meaningful and deeper role in the home security industry. Features of AI-based home security systems Most home security systems already use AI regularly for features like smart cameras, motion sensors, and alarms. These offerings incorporate AI to detect and respond to potential security threats, differentiating between everyday activities and potential suspicious behaviour and then alerting homeowners based on the activity. As AI expands the capabilities of critical security features such as facial recognition, voice control connectivity, and enhanced video capabilities, it will significantly improve the traditional security systems we use today, providing additional means of not only protecting homes but also streamlining the overall home security system. Future advancements in AI home security systems Increased integration of security devices through AI As AI continues to evolve, we can expect to see increased integration and connectivity of devices included in a home security system and home – all powered by AI. This includes hardware such as cameras, motion detectors, keypads, sensors, and smart locks, as well as software, such as digital apps. This increased connectivity will not only make it easier for homeowners to manage their security system but also to customise their home and home security to meet their evolving needs. Voice control connectivity The new hands-free approach to home security enhances the user experience and opens up new possibilities Voice control connectivity is yet another key feature that is gaining popularity in AI-powered home security systems. Security system users can control and monitor their security systems using voice commands similar to how Amazon’s Alexa works, making security systems more convenient and user-friendly. The new hands-free approach to home security not only enhances the user experience but also opens up new possibilities for seamless integration with other smart home devices and mobile devices. AI will help personalise and individualise security settings Relying more heavily on facial recognition technology, AI algorithms integrated into home security systems will become more personalised and tailored to individual users based on their preferences. Imagine a security system that recognises each member of your family and adjusts its settings and alerts based on each user’s unique preferences and habits. Thanks to facial recognition improvements in recent years, this new level of customisation will enhance security and improve the ease of use, making home security more intuitive and user-friendly. By incorporating personalisation via AI into home security systems, simple tasks like disarming the system when returning home or arming the system before going to bed at night will be much more efficient, and security settings will be saved based on each user’s preferences. AI will analyse threats before they become emergencies AI-powered automation will play a heightened role in the future of home security systems as it learns to proactively analyse and respond to potential threats, security breaches, and emergencies like fires or carbon monoxide leaks. Through real-time monitoring, AI will begin to predict and prevent security breaches before they occur, working efficiently with human counterparts for an effective approach to security monitoring. Security monitoring AI linked to a carbon monoxide detector may notice the levels rising before they reach a dangerous level For example, through camera monitoring, AI will learn how to tell the difference between normal and suspicious activities, automatically adjusting your security settings and alerting you of a potential risk. Similarly, AI linked to a carbon monoxide detector may notice the levels rising before they reach a dangerous level and alert the security system user and monitoring service in advance. The AI evolution of home security The traditional idea of home security systems, with physical locks, keypads, and alarms, is rapidly changing into a more intelligent system powered by AI. Just as the cell phone industry revolutionised communication by making phones constantly accessible to us all, AI is on the cusp of transforming our home security systems into a much safer and more user-friendly experience. Shortly, we’ll see a world where every aspect of home security systems is easily accessible on one or multiple devices within the home or even on mobile devices, boosted by the help of AI. From keyless entry systems that recognise our faces to AI assistants that communicate with us and adjust settings based on our preferences, the possibilities are truly endless. A safer, smarter, and more secure future As AI continues to advance and becomes more integrated into home security systems and life in general, the future will bring enhanced safety, security, convenience, and peace of mind for homeowners. As we move towards a future where AI plays a larger role in our daily lives, we can expect to see a shift in the way we think about and approach home security systems – in fact, it’s already happening. The traditional security setup of the past is being replaced by a new era of intelligent, interconnected, and proactive home security systems that work seamlessly. With AI as our ally and incorporated into our home security systems, we can look forward to a safer, smarter, and more secure future for our communities, homes, and loved ones.
Choosing the appropriate fingerprint technology for a given application is dependent on factors including the required level of security and matching accuracy, the desired capabilities and features, and the usability to achieve adoption and productivity goals. A successful evaluation process will help ensure that this mature and proven user authentication method performs as expected. Fingerprint biometric advantages The speed, simplicity, accuracy, and cost-effectiveness of the fingerprint method have made it among the most widely used for biometric authentication across industry sectors ranging from banking and finance, retail, and healthcare, to government and law enforcement. It performs biometric technology’s “something you are” function while offering unique characteristics that make it particularly valuable for many applications. Unique identifier The fingerprint biometric has the permanency of being reasonably stable and consistent over time Among these characteristics is the pervasiveness and special nature of the fingerprint -- almost everyone has one, and each is a unique identifier. The fingerprint biometric has the permanency of being reasonably stable and consistent over time. It is also easy to acquire, measure, and process. High adoption rate Another key attribute of a fingerprint biometric is its ability to be protected against threats ranging from abuse and misuse to theft, imitation, and substitution. When it is used with recognition techniques the resulting solution performs with a combination of accuracy, speed, scalability, and ease of use. Fingerprint biometric solutions also have the highest adoption rate among biometric authentication solutions according to an industry report published by Payments Journal. Three interrelated components There are three basic components in any fingerprint biometric system as shown in Figure 1: capture (using a sensor that can capture even the most difficult finger types); liveness detection (using the Presentation Attack Detection – or PAD – technique); and matching (including preventing rejection of a legitimate user). Biometric algorithm The sensor captures and pre-processes the fingerprint data. It must be able to successfully capture fingerprint images for a range of skin types and print conditions under diverse temperatures, humidity, light, surface oil, dust, dirt, and other environmental conditions. A biometric algorithm then extracts minutiae data about the fingerprint ridges (endings, bifurcations, islands, etc.) and their orientation and position. PAD technique Implementing a presentation attack detection (PAD) technique at this stage activates the fingerprint biometric system’s second key element: liveness detection. This verifies the fingerprint’s authenticity and that it belongs to a living person. The system’s third element – matching – occurs after the PAD-verified fingerprint dataset has been securely stored as a record, known as a template, inside an enclave with cryptographic protection. Check for liveness The corresponding template of the legitimate user is then retrieved from secure storage When the fingerprint is presented for matching, it is rechecked for liveness. The corresponding template of the legitimate user is then retrieved from secure storage and the process of matching the fingerprint with this template is executed. This must be completed accurately and without rejecting a legitimate user. Types of fingerprint sensing technologies There are four prevailing categories of sensing technologies used with fingerprint readers: optical, capacitive, thin-film transistor (TFT), and multispectral imaging (MSI). Optical and capacitive method Optical is the most mature sensor technology and offers the benefits of a compact size, good capture Optical is the most mature sensor technology, and offers the benefits of a compact size, good capture and matching performance, a small enough size to fit in most desktop environments or shared workstations, and a high level of accuracy at a cost-effective price point across all use cases. The capacitive method, on the other hand, is less prone to fake finger attempts while also offering a thin and compact size for space-limited applications, the power efficiency to support battery-operated devices, and the ability to handle both indoor and outdoor lighting conditions. TFT technology The third technology goes a step further in capture accuracy. TFT technology can accurately recognise the smallest fingerprint features with ultra-high resolution and is used either as a larger-size matrix capacitive proximity detector (capacitive fingerprint sensor) or a larger-area matrix light detector (optical fingerprint sensor). It is ideal for in-the-field mobile identification applications that require a cost-effective, ultra-slim, and lightweight solution with low power consumption. MSI technology MSI technology differs from all three approaches, projecting multiple colors of light into the finger from different angles to collect both surface and subsurface biometrics data. It captures the most difficult fingerprints of diverse demographics, in a wide range of challenging environments. HID has used this patented technology in fingerprint readers that are compliant with ISO 30107-3 PAD Level 2 for advanced anti-spoofing against fraud. The technology also improves matching and offers sophisticated endpoint security that prohibits cyber criminals from gaining unauthorised access to networks by turning fingerprint readers into secure endpoints. Best practices for technology selection Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership. There are three top considerations: security, suitability, and usability. Each is important and the best approach is to strike a balance between all three. Following are the questions to ask during the selection process: Security: What is the regulatory environment? Financial and government services, healthcare, and law enforcement are some examples of highly regulated sectors with elevated security compliance requirements. Are there mandates in place for advanced capturing and biometric authentication specifications? How important is it to ensure anti-spoofing through liveness detection? Will endpoint security be required so that, if the fingerprint device is hacked, no network, system, or data behind the firewall will be impacted? Suitability: Where will the biometric technology be implemented? There will be additional considerations if it is to be embedded in portable, battery-operated devices that require low power consumption. Where will the technology be used? Will it need to fit into small spaces or be used in challenging indoor or outdoor conditions and environments? Will durability be important? Some deployments will face unpredictable weather and difficult lighting conditions for image capture. Will the technology be used for mission-critical border control or a more common – and less demanding -- commercial use? Usability Is it critical that the technology easily and consistently perform capture and matching? Will there be high volumes of fingerprint captures and matches? Is “friction frustration” a concern? If so, the solution must perform matching quickly and accurately to sustain high levels of user productivity. Will the fingerprint device be used by one person exclusively, or multiple people in a shared workstation setting? How diverse is the user population? Some readers are designed to handle all types of fingerprints and diversified demographics. Different applications Fingerprint biometrics is a proven solution to address real-world challenges, each with its requirements The answers to these questions will help determine the best choice of fingerprint technology. Different applications apply fingerprint biometrics to very different use cases but in all cases. It is a proven solution to address real-world challenges, each with its requirements. For instance, in a healthcare clinician’s terminal area or a similar shared environment with limited space, a durable, low-profile capacitive sensor may be the right answer. For an organisation in a highly regulated, mission-critical environment like a bank or border control agency, advanced technologies such as MSI readers may be needed to avoid the serious repercussions of a spoofed identity or the rejection of a legitimate one. Requirements for a biometric solution These are just a few of the requirements to consider when choosing a fingerprint solution. In banking and finance, alone, fingerprint biometrics is used for applications ranging from transacting at the ATM to customer onboarding (eKYC), compliance (AML/KYC), and fraud prevention. The retail sector adds even more, including age verification, loss prevention, point of sale (POS) security, self-service checkout, and secure time and attendance. Law enforcement organisations have their unique requirements, using fingerprint biometrics for background checks, criminal booking, crime investigation, inmate management, mobile identification, and more. For government agencies, typical applications include benefits distribution, border security, citizen ID, employ authentication (SSO/MFA), and voter registration. Each application requires a thorough assessment of the best fingerprint technology for the job. The right touch The right solution will deliver the optimal balance of security, suitability, and usability Fingerprint biometric solutions empower a wide range of use cases with the simple touch of a finger. The right solution will deliver the optimal balance of security, suitability, and usability based on an analysis of criteria including specific application requirements, the characteristics and size of the user population, and challenges posed by environmental conditions. Accuracy, efficiency, and security The world faces increasingly dangerous fraud, account takeover, and impersonation threats. As industries and enterprises work to improve and evolve their identity and access strategies to combat these threats, fingerprint biometrics continue to prove their value through solutions that meet the key selection criteria while delivering the highest levels of accuracy, efficiency, and security.
Security beat
Big news on the mergers and acquisitions (M&A) front is closing out 2024, a year in which several shifts changed the face of the physical security manufacturer community. Announced in December, German giant Bosch Group is selling its Building Technologies division’s product business for security and communications technology to the European investment firm Triton. Bosch division selling to Triton The transaction encompasses three business units – Video, Access and Intrusion, and Communication – and thus the entire product business of Bosch Building Technologies that was offered for sale. All 4,300 associates employed in these units at more than 90 locations worldwide will be taken over. The transaction reflects a growing confidence in the security market among private equity companies such as Triton, Becklar, and Volaris. Sharing best practices Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership Acre Security, previously acquired by Triton, has benefited from Triton’s strategic guidance and expertise, according to the company, which is confident Bosch will experience the same level of support and opportunity to thrive. Acre Security and Bosch will remain independent, standalone companies under Triton’s ownership, but will benefit from the potential to collaborate and share best practices as part of the broader Triton portfolio. Resideo acquires Snap One Earlier in 2024, there were other large M&A transactions. In the spring, Resideo Technologies, Inc., a manufacturer and distributor of technology-driven products and solutions, agreed to acquire Snap One Holdings Corp., a provider of smart-living products, services, and software to professional integrators. The transaction is valued at $1.4 billion, inclusive of net debt. Upon closing, Snap One becomes part of Resideo's ADI Global Distribution business. Honeywell buys Carrier’s Access Solutions In late 2023, Honeywell announced plans to enhance and strengthen its building automation capabilities with the acquisition of Carrier Global Corporation’s Global Access Solutions business for $4.95 billion, in an all-cash transaction. The acquisition, which played out through 2024, includes both hardware and software solutions, adding three respected brands to Honeywell’s portfolio with a focus on life safety and digital access solutions. Acquired brands include LenelS2, commercial and enterprise access solutions; Onity electronic locks; and Supra cloud-based electronic real estate lock boxes. Hirsch reemerges as an iconic brand The Identiv sale was originally announced in April, subject to regulatory approval Identiv announced plans to sell its physical security business and assets to Vitaprotech, the security solutions provider that also acquired British manufacturer, TDSI, in 2019. The Identiv sale was originally announced in April, subject to regulatory approval. As a result of the sale, Hirsch, a global security technology pioneer advancing physical security, video intelligence, cybersecurity, and digital identification solutions, announces the relaunch of its iconic brand and strengthened focus on the industry’s most complete high-security, end-to-end platform. Ease of use security solutions The move seeks to reposition Hirsch as the global pioneer in physical security, video intelligence, and identity solutions, protecting everything from small enterprises to critical national infrastructure. With a 43-year-strong foundation in the industry, Hirsch’s mission has always been empowering a secure, connected world, combining government-grade high security with ease of use. Milestone and Arcules unite Effective July 1, 2024, global video technology company Milestone Systems announced its merger with the cloud-based video surveillance solutions provider, Arcules. Both companies are owned by Japanese multinational Canon Inc. Based in Irvine, Calif., Arcules was spun off from Milestone in 2017. The merger brings together Milestone and Arcules’ best-in-class capabilities within video management software (VMS), video analytics, and video surveillance as a service (VSaaS), providing a complete video technology offering. More M&A stories in 2024 In other M&A moves in 2024, cloud-based workforce management software provider Synerion USA Inc. acquired cloud-based video surveillance and access control solutions platform Qumulex Inc. Also, the global pioneer in airspace awareness and security, Dedrone, became part of the public safety and technology company Axon. The acquisition unites two companies with a shared mission to improve public safety and national security by staying ahead of persistent and escalating threats, enabling faster, more effective responses and ultimately protecting more lives in more places.
The pattern of veins in the hand contains unique information that can be used for identity. Blood flowing through veins in the human body can absorb light waves of specific wavelengths. Irradiating the human palm with near-infrared light waves yields an image of the vascular pattern. A venous distribution map can be processed and compared to pre-registered data to match and confirm identity. Palm vein biometrics The idea of palm vein biometrics goes back to the 1980s when palm vein scanners emerged as commercial products in the 1990s. The devices gained some traction in military-grade and high-security applications, although the technology was too expensive to become popular among mainstream applications such as physical access control. Anviz Global is expanding palm vein technology into mainstream applications, featuring a lower price point that will open new market opportunities. Palm vein technology “Palm vein technology has been viewed as a boutique product because it is costly and has not developed as a mainstream product,” says Mark Vena, Senior Director of Business Strategy and Development for Anviz Global. “With a more compelling price point, the market can see the technology more broadly. We can change the game in terms of how people think about palm vein technology.” FAR and FRR Palm vein technology is more accurate than either fingerprint (0.0001% FAR) or facial recognition (0.001% FAR) Iris recognition is considered the gold standard in biometric identification, but palm vein technology can almost achieve the accuracy of iris. The false accept rate (FAR) for palm vein technology is 0.00008%, compared to 0.00005% for iris recognition systems. The false reject rate (FRR) is comparable at 0.01% for either technology. Palm vein technology is more accurate than either fingerprint (0.0001% FAR) or facial recognition (0.001% FAR). Palm vein identification occurs in less than half a second. M7 Palm “Anviz is seeking to bring a high level of capability to more mainstream commercial applications,” says Vena, specifically providing a lower-cost palm vein unit. The M7 Palm by Anviz can achieve next-generation biometric access control for greater security and intelligence. The door-mounted unit combines palm vein recognition with an RFID card reader and PIN code (using a 17-button keypad), all configurable for multi-factor authentication. Outdoor applications The robust unit, including a narrow metal exterior design, provides strong vandal resistance (IK10) and stability for outdoor applications. To ensure a weatherproof design, the IP66 rating indicates the product is completely protected against dust and can withstand strong jets of water from any direction. Power-over-ethernet (PoE) enables centralised power management and the ability to remotely reboot devices. Wiegand-out interface The unit communicates using RS-485 or TCP/IP and can connect locks, exit buttons, door contacts, doorbells, etc The unit communicates using RS-485 or TCP/IP and can connect locks, exit buttons, door contacts, doorbells, etc. The Wiegand-out interface can connect to standard third-party controllers, or a built-in relay can trigger a lock directly. Capacity is 500 users. Because palm vein recognition originates from the physiological characteristics of the human body, it represents a “credential” that cannot be forged, lost, or left at home. It is not easily counterfeited or worn out. Multi-factor authentication Applications include industries requiring high security such as government, judicial, and banking. Multi-factor authentication eliminates fraud and ensures safety at banks, data centers, airports, prisons, and government. An end user might opt for higher levels of access control for a laboratory or server room. For dealers and integrators, palm vein technology, including multi-factor authentication, provides an additional option for customers seeking to protect high-security areas on a large campus. Card readers Card readers may suffice for most of the doors, but an important laboratory or cash-handling area requires more protection. Palm vein technology can secure a casino cash cage or a room containing corporate secrets. Time of Flight ToF laser-ranging uses a laser to measure the distance to an object by calculating the time Time of Flight (ToF) laser-ranging achieves accurate measurement to ensure the right distance for operation. ToF laser-ranging uses a laser to measure the distance to an object by calculating the time it takes for the laser light to travel to the object and back. Palm vein technology operates in the range of 10 to 30cm (4 to 12 inches). The proprietary BioNANO palm vein recognition algorithm enables accurate and fast scanning speed. Non-contact biometric The non-contact biometric performs in touchless environments and does not contribute to lingering health concerns in the post-COVID world. The technology is accurate across all hand types and skin tones. Users may feel more comfortable scanning their hands than their eyes. Optimal human-machine interaction M7 Palm’s optimal human-machine interaction and user experience include a low-power-consumption OLED screen to deliver clear text notifications to the user. Advantages of M7 Palm include accuracy, stability, security, and privacy. Features include easy installation with standard processes and no special tools, centralised power management, simplified cabling, and less maintenance. Managing the system is expedited by integration with the Anviz CrossChex Standard access control and time management dashboard, used by more than 30,000 enterprises, and the system can be integrated with any access control system. Security for SMBs Anviz Global is a converged intelligent security provider for SMBs and enterprise organisations Anviz Global is a converged intelligent security provider for small- and medium-sized businesses (SMBs) and enterprise organisations. The company’s product line includes biometrics, video surveillance, and security management solutions based on the cloud, Internet of Things (IoT) and artificial intelligence (AI) technologies. Privacy concerns Anviz is part of the Xthings family of companies, which includes Ultraloq (smart locks), Utec (smart home), Bright (smart lighting), Secu365 (SaaS Platform), and Ulticam (smart cameras). Privacy concerns are minimised because palm vein recognition does not directly store the original image but rather extracts feature information through algorithmic models. Personal data is protected through obfuscation and encryption.
ISC West 2024 mirrored a vibrant industry on the precipice of accelerated change. Factors such as the cloud, artificial intelligence (AI), edge computing, and biometrics are shaping the future of the security marketplace, and they were front-and-centre at the industry’s biggest U.S. show in Las Vegas. Foot traffic was steady and impressive, including more than 29,000 security industry professionals viewing 750 exhibitors. A torrent of eager attendees crowded the lobby on the first day and could not wait for the doors to open. When they were admitted, the wealth of technological innovation and business opportunity did not disappoint. Focus on cloud systems Cloud systems were high-profile at ISC West. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference. Meanwhile, Genetec officially launched their Security Centre SaaS platform, which aims at eliminating points of friction to enable integrators to easily embrace cloud systems from quoting and ordering to provisioning and installing. Camera manufacturer Axis, for example, introduced their Axis Cloud Connect at a press conference Cloud provider Eagle Eye Networks promoted their new “Eagle Eye 911 Camera Sharing” technology under which both non-Eagle Eye Cloud VMS customers (via Eagle Eye 911 Public Safety Camera Sharing) and Eagle Eye customers can opt to share their video feeds for use by 911 operators in case of emergency. If users opt-in, 911 operators can have access to live video as an emergency unfolds. Eagle Eye Networks provides the feature by integrating with RapidSOS call centre software. Camera locations are based on geolocation coordinates, and customers can choose if they want to participate and which cameras they want to share. Biometrics in the mainstream Biometrics were well represented at ISC West, including Alcatraz AI, which introduced an outdoor version of their biometric face recognition product. The Rock X works well despite harsh lighting. Alcatraz’s products do not have to be integrated, they communicate just like a card reader using OSDP or Wiegand protocol. “At the show, customers are excited about moving to a frictionless environment and getting rid of existing credentialing,” said Tina D’Agostin, CEO and co-founder of Alcatraz. “We are making access control frictionless, secure and private. The experience can be as passive as possible – people can just walk in.” Multiple types of authentication, and the ability to detect tailgating and stream video SAFR from Real Networks also featured biometric face recognition, emphasising feature sets, convenience, and price/performance. They offer multiple types of authentication, and the ability to detect tailgating and stream video. A new device is a small mullion mount that is “approaching the price of a card reader, factoring in the need to purchase cards,” said Brad Donaldson, Vice President and General Manager. SAFR focuses on convenience: You don’t have to take out your phone to pass through a door. Enrolment is easy by incorporating existing databases, and costs are lower than competitors, said Donaldson. The system analyses multiple points on the face, turns it into data and then encrypts it, providing a “unique signature for each person.” Credentials in Apple Wallet and Google Wallet AMAG Technology announced the compatibility of credentials with the Apple Wallet and Google Wallet. The company is also embracing a new strategic direction under President David Sullivan. They launched a new website in January, are developing dynamic resources and a partner page, and they now integrate with 120 tech partners. AMAG Technology Financial Services now enables their channel partners to offer leasing and financing options to customers. The big new booth at ISC West reflected an effort to “market different and look different,” according to the company. The big new booth at ISC West reflected an effort to “market different and look different" The new Symmetry Control Room, a command-and-control system, is a relaunch of an earlier AMAG product with enhanced features. Suitable for large enterprise customers, the software enables a big video wall to display all the various systems and incorporates all the data into a single “pane of glass.” Operators can “draw a lasso” around cameras they want to display on the video wall and can follow action across multiple camera feeds. Navigating megatrends A breakfast meeting for integrators, sponsored by Assa Abloy Opening Solutions, was built around the theme “Navigating Megatrends for Sustainable Growth." The megatrends are artificial intelligence, sustainability and cybersecurity. Related to cybersecurity, there are 350 common vulnerabilities and exposures (CVE) published per week, reflecting the continuing threat to cybersecurity. Physical security has a “data lake” of information from various physical security systems that can be an attractive target for cybersecurity breaches. Data sets can be exploited and/or poisoned. The security industry needs to apply “defence in depth” to the challenges of protecting data. “The threat landscape is always changing, and security technology is an iterative process,” said Antoinette King, i-PRO’s head of cyber convergence, one of the panellists. Natural language systems Natural language systems are a newer approach making an early appearance at ISC West Natural language systems are a newer approach making an early appearance at ISC West. Brivo, for example, has an early prototype of its “natural language search capabilities” that can answer questions such as “Who is in the office?” or “Where is Bob and what has he done?” Brivo also promoted its all-in-one door station device that combines a card reader and a camera (for facial authentication) and serves as a video intercom, thus eliminating the need for multiple devices at the door. Brivo is also emphasising tailgate prevention, facial authentication, and people counting using AI at the edge. Also promoting natural language systems was Verkada, which unveiled a beta version of its AI Search feature that embraces national language capabilities. With AI Search, users will soon be able to use natural language to search for people or items. For example, a search could be “person climbing over a fence” or “person making phone call” or “person wearing football jersey.” Verkada wants to be thoughtful with the rollout and make sure effective guardrails are implemented to prevent abuse and bias. The release should happen in the coming months. Multi-family applications Allegion is promoting the XE360 hardware lock platform in various formats, including cylindrical lock, mortise lock, deadbolt and exit trim. At the show, Allegion noted an enthusiasm for multi-family applications. “We have been surprised by the people who want to add electronics and to retrofit existing multi-family facilities to compete with newer facilities,” said Henry “Butch” Holland, Allegion’s Regional Director, Channel Sales East Region. Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec Allegion also offers an “indicator” display on its locks, showing at a glance whether a door is locked or unlocked. The “indicator” might also display “occupied” or “vacant.” Allegion works with 60 different physical access control software providers, including familiar players such as LenelS2 and Genetec. Integrator M&A trends Everon looks for acquisitions in areas where they do not currently have support for national accounts A conversation with Everon at ISC West provided insights into the accelerating trend of mergers and acquisitions among the integrator community. Everon, formerly ADT Commercial, has done six acquisitions of local integrators since they changed their name last year. In targeting companies to acquire, they look for a good company with a good reputation, and they consider how the new company’s competencies complement their own. Some M&A strategy is geographic, as Everon looks for acquisitions in areas where they do not currently have support for national accounts. They also consider density, seeking to add new acquisitions in larger markets where they don’t currently have a big market share. “A lot of investment is coming into security because it is seen by investors as recession-proof,” said Michael Kennedy, VP, Mergers and Acquisitions, for Everon. Kennedy met with 95 businesses last year for possible acquisition, and the company only finalised a handful – reflecting that Everon is selective and careful that corporate cultures are aligned. “With an acquisition, the goal is to keep every customer and every employee,” said Kennedy. Voice of the customer ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. “We have every kind of problem come to the booth,” commented Heather Torrey, Honeywell’s General Manager, Commercial Security, Americas. “People are passionate, interested and very specific with their questions and comments,” she said. “We are driving a complete system, but we are flexible, helping our customers to meet their needs and not try to fit every foot into the same shoe. Sometimes meeting customer needs involves working with competitors," Torrey commented. “It truly comes back to listening to the customer, not just ‘this is what we have to offer,’” she adds. ISC West provides an opportunity for manufacturers to listen to the “voice of the customer;” in person, no less. Edge applications are everywhere at ISC West, and one company is promoting a new approach to expand functionality at the edge. Camera company i-PRO advocates the use of the “Docker” platform for app development, an option they offer on their cameras. Docker “containers” package deep-learning algorithms to make it easier to embed software into edge devices. Anyone can run Docker apps on i-PRO cameras that use the powerful Ambarella chip. A Docker “swarm” can combine multiple edge devices to work together and share resources. For example, the approach can increase computing power at the edge to increase the capabilities of instant analytics. It’s faster and provides better redundancies. A “distributed computing platform” ensures less latency than communicating analytics to a central server. Unification of capabilities Johnson Controls (JCI) also promotes the trend of combining multiple systems into a single pane of glass. Their “Open Blue” platform, with a security version unveiled at the show, integrates various security systems into one, combining data and monitoring device health. Basically, the system manages all resources holistically. JCI also notes a trend toward “unification of capabilities,” e.g., combining access control and video. “The scope of security is evolving from a focus on protection to a broader focus on operations,” commented Julie M. Brandt, JCI’s President, Building Solutions North America.
Case studies
As a provider of future-oriented business education, The Camp sought an access control solution as forward-thinking as their courses. Their campus site near Aix-en-Provence is diverse, with offices, event spaces, kitchens and two accommodation blocks totalling 170 units. The Camp must remain open around the clock, all week, while maintaining security for staff and visitors. Aperio wireless locks Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks Aperio provided locking devices tailored to every door type — interior and exterior. So far, The Camp has integrated 221 Aperio Wireless Escutcheons, 42 Aperio Wireless Cylinders and 10 Aperio Wireless Handles within a TIL Technologies security system. Integrated online with the central system and controlled from the same interface, these Aperio devices effortlessly handle daily staff traffic of around 250 people. Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks. Aperio visitor access system Up to 2,000 external visitors arrive on-site when The Camp stages an event — and each must also have credentials issued and access filtered through the site. Aperio makes it straightforward to enable visitor access. “Many credentials get lost and Aperio enables us to handle this efficiently,” says Benjamin Ciotto, Head of Information Technology at The Camp. A few clicks are all it takes to cancel a lost key card and issue a replacement. Real-time and future-proofed Security staff at The Camp ensure only authorised users enter offices where expensive video projectors and screens are stored. Their TIL integration enables real-time management of the whole site, with specific profiles created to segment individuals who need fine-grained access to specific areas. “Online mode is very important because (access) rights are very often updated for the constantly shifting campus population,” explains Benjamin Ciotto, adding “We can also program access to defined time slots, which is essential when we welcome 200 people for an all-day meeting, for example.” Aperio product ecosystem’s performance Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos Aperio technology also met The Camp’s need for an aesthetically pleasing, wireless solution. They did not want to compromise their interior or exterior design. The Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos. Because Aperio devices are wireless and battery-powered, they are much more energy efficient than traditional wired locking systems, which require an “always-on” mains connection. Multiple Aperio devices Multiple Aperio devices have independently assessed Environmental Product Declarations (EPDs). These detail the footprint of each device through its full life cycle, from production to disposal. “Aperio is a real comfort of use,” Benjamin Ciotto concludes. “And we handle the easy maintenance for ourselves.”
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. Modern digital solution Modern digital solution would provide better oversight of movement around the building They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorisations, even at the last minute. Digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. Maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provide security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous tavern,” explains its Security Manager, Robert Graßl, adding “The whole world goes in and out. Security is very important.” Bavarian Duke Wilhelm V commissioned Munich’s original Hofbräuhaus in 1589, initially as a brewery to supply the Wittelsbacher Hof. Moved at the end of the 19th century and severely damaged during World War II, it underwent reconstruction in 1958. It now attracts tourists and city locals, seating up to 3,000 guests indoors and a further 400 in the beer garden. Access rights management Digital devices and low-impact skills were needed to assure compliance with origin protection Although the building is an important heritage monument, it requires 21st-century digital access to keep site users safe and streamline day-to-day operations. They wanted fast, secure access rights management for employees and service providers – including up to 100 waiters working each shift – within a unified system that could authorise access at both the Hofbräuhaus and their food production facility in Brunntal. Of course, inobtrusive digital devices and low-impact installation were a necessity to ensure compliance with heritage preservation regulations. Digital access for a famous heritage building Many electronic access products and technologies are not appropriate for historic buildings. An eCLIQ key-based digital access solution is different: eCLIQ cylinders are compatible with the strict monument preservation requirements at the Hofbräuhaus. They have a flush fit, so don’t even appear to be part of an electronic locking system. With wireless installation at the doors, devices blend with the building interior. “We can exchange a mechanical cylinder 1:1 with an eCLIQ cylinder without having to modify anything on the door or install cables,” confirms Miriem Hammoudi, Business Development Manager at ASSA ABLOY Sicherheitstechnik GmbH. ASSA ABLOY fitted around 100 eCLIQ locking cylinders and supplied 340 eCLIQ programmable keys for Hofbräuhaus managers to issue to relevant staff and service contractors. Easy operation for flexible, cost-efficient management Every eCLIQ key has an integrated chip and is programmable individually for the keyholder Every eCLIQ key has an integrated chip and is programmable individually for the keyholder. The versatility of eCLIQ is demonstrated when a key is lost: Access authorisations are removed rapidly – simply by reprogramming cylinders – ensuring security is maintained. The eCLIQ system also helps manage workflows for service providers, such as cleaners: Their access is enabled on a time-limited basis. A standard battery inside each programmable electronic key powers the cylinder or padlock on insertion – and encrypts data transfer between cylinder, key and system – so no external power source or wiring is needed. Scalable web-based platform The Hofbräuhaus team manages their system via a flexible, scalable web-based platform, CLIQ Web Manager: “I can program keys from anywhere or also block them quickly if a key has been lost or if someone is no longer allowed to enter,” says Robert Graßl. He adds, “And I can install any cylinder in any door by adjusting the length. I don’t have to carry extra stock which is really cost effective.” New master key system With the hosting solution chosen, access data is stored securely at ASSA ABLOY, accessible anytime and from any location, which is an ideal configuration for managing large systems or multiple locations. Their system is easy to expand anytime – future-proofing Hofbräuhaus access. “The situation before the new master key system was installed was problematic,” says Robert Graßl, adding “Keys were distributed and nobody knew who held them. Now, everyone carries only one key programmed with details of where and when they can enter. It’s perfect.”
Artificial Intelligence Technology Solutions, Inc., a pioneer in AI-driven security and productivity solutions for enterprise clients, along with its subsidiary Robotic Assistance Devices (RAD), announced recent successes in St. Louis, Missouri, where the Downtown St. Louis Community Improvement District (CID) has embraced RAD’s solutions as part of its public safety initiatives. The CID has deployed multiple ROSA™ security devices, showcased RAD’s ROAMEO™ and RADDOG™ LE2 during the NCAA Frozen Four Championship, and is actively developing a citywide program that would introduce hundreds of RADCam™ units across St. Louis. RAD’s added layer of security RAD’s ROAMEO and RADDOG LE2 were actively deployed in St. Louis as part of the city’s public safety From April 10 to 12, RAD’s ROAMEO and RADDOG LE2 were actively deployed in downtown St. Louis as part of the city’s public safety and engagement efforts during the NCAA Frozen Four Championship. These high-visibility units provided an added layer of security, engaged with residents and visitors, and generated strong public interest. Steve Reinharz, CEO/CTO of AITX and RAD, was interviewed on-site by KSDK, the St. Louis NBC affiliate, where he discussed how RAD’s technologies enhance urban safety while fostering meaningful community interaction. RAD security solutions During the event, representatives from several local organisations, including casino operators, professional sports teams, and major property management firms, visited with RAD and the Downtown St. Louis CID to see firsthand how ROAMEO, ROSA, RADDOG LE2, and other RAD security solutions could be used to support safety and operational efficiency in real-world environments. Of particular interest to many of these organisations was RAD’s multiple SARA™ (Speaking Autonomous Responsive Agent) and ROSS™ (RAD Operations System Software) platforms. RAD’s analytics and automation capabilities Software solutions allow clients to reimagine the role of their existing security infrastructure These software solutions allow clients to reimagine the role of their existing security infrastructure by adding an intelligent, agentic AI layer to legacy hardware. By leveraging RAD’s analytics and automation capabilities, organisations can unlock powerful new functionality from their current systems, enhancing performance, accelerating incident response, and delivering significant cost savings without the need for full system replacement. RAD’s technology: public safety efforts “RAD’s technology has been an impactful addition to our public safety efforts,” said Kelli McCrary, Executive Director of the Downtown St. Louis CID. “The presence of ROSA, ROAMEO, and RADDOG has not only helped deter unwanted activity, but also brought positive attention and community engagement, especially during the excitement of the Frozen Four Championship. This kind of innovation supports our vision for a safer, more welcoming downtown experience.” RAD over traditional security solutions RAD secured deployments of ROSA and RIO units following a competitive review, with city leadership RAD’s momentum extends beyond St. Louis. In Cleveland, RAD partnered with Downtown Cleveland, Inc. to launch a smart security initiative in Public Square, featuring the RIO™ 360 tower with live video integration into the city’s crime centre. In Nashville, RAD secured deployments of ROSA and RIO units following a competitive review, with city leadership opting for RAD over traditional security solutions to enhance monitoring and deterrence in key public areas. How RAD’s solutions meet the evolving security needs As municipalities and CIDs search for scalable, cost-effective ways to secure public spaces, RAD has emerged as a trusted partner in redefining how cities approach safety. From high-traffic districts to major public events, RAD’s AI-powered devices provide 24/7 monitoring, advanced detection capabilities, and autonomous responses that relieve the burden on human personnel. The recent deployments in St. Louis, Cleveland, and Nashville illustrate how RAD’s solutions meet the evolving security needs of urban centres while reinforcing community confidence. RAD's effective security solutions “We’re seeing growing interest from CIDs and public sector organisations that are eager to rethink how they secure their communities,” said Reinharz. “RAD is executing a nationwide campaign to deliver meaningful, affordable, and effective security solutions to cities, towns, and districts across the country. Our technology gives these organisations the tools to protect public spaces, ease the strain on human resources, and deliver a stronger sense of safety for residents and visitors alike.” Outdated approaches and deployments RAD welcomes inquiries from municipalities, CIDs, BIDs, DDAs, and other organisations “It’s incredibly rewarding to see our devices actively supporting the safety goals of communities like St. Louis, Cleveland, Nashville, and others,” said Troy McCanna, Chief Security Officer at RAD. “These deployments represent a shift away from outdated approaches and a move toward intelligent, responsive technology that delivers results. We’re proud to be working hand-in-hand with local pioneers who are committed to creating safer urban environments through innovation.” How its AI-powered security solutions can support safety goals RAD welcomes inquiries from municipalities, Community Improvement Districts (CIDs), Business Improvement Districts (BIDs), Downtown Development Authorities (DDAs), and other organisations focused on public safety and urban revitalisation. The Company offers personalised consultations to explore how its AI-powered security solutions can support local safety goals, improve operational efficiency, and strengthen community trust. RAD's security guarding and monitoring model RAD solutions are precisely designed to provide cost savings to businesses of between 35%-80% AITX, through its subsidiary, Robotic Assistance Devices, Inc. (RAD), is redefining the nearly $50 billion (US) security and guarding services industry through its broad lineup of innovative, AI-driven Solutions-as-a-Service business model. RAD solutions are specifically designed to provide cost savings to businesses of between 35%-80% when compared to the industry’s existing and costly manned security guarding and monitoring model. RAD AI-based analytics and software platforms RAD delivers these tremendous cost savings via a suite of stationary and mobile robotic solutions that complement, and at times, directly replace the need for human personnel in environments better suited for machines. All RAD technologies, AI-based analytics and software platforms are developed in-house. RAD has a prospective sales pipeline of over 35 Fortune 500 companies and numerous other client opportunities. RAD expects to continue to attract new business as it converts its existing sales opportunities into deployed clients, generating a recurring revenue stream. Each Fortune 500 client has the potential of making numerous reorders over time.
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. Modern digital solution Modern digital solutions would provide better oversight of movement around the building All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management, they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorizations, even at the last minute. ASSA ABLOY’s smart key digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. eCLIQ system maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provides security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.
Silverstein Properties, a pioneering real estate development, investment, and management firm, and its partners SwiftConnect, Allegion, and Kastle, announced they are live with resident keys in Apple Wallet for all apartment units at a multi-family housing location: Silverstein’s Silver Towers residential property at 606 West 42nd Street in New York City. Silverstein’s residential tenants now have an easy and secure way to add a resident key to Apple Wallet to access the apartment building and unlock their homes with a simple tap of an iPhone or Apple Watch—thus eliminating the need to use a traditional, physical key. Resident key in Apple Wallet The rollout of keys in Apple Wallet marks an important milestone for the U.S. real estate industry “We’re excited to make it easy for our residents to use their resident key in Apple Wallet to get into their buildings, homes, and common areas, which builds upon our previous offering to office tenants who use their employee badge in Apple Wallet to access offices and shared spaces including lounges, cafes, conference facilities, and yoga studios,” said Tal Kerret, President of Silverstein Properties. The rollout of keys in Apple Wallet marks an important milestone for the U.S. real estate industry, as property owners and employers reimagine the home and workplace experience for residents, office tenants, and employees. SwiftConnect’s success: Enhance security for residents “The Silver Towers project builds on SwiftConnect’s success in delivering seamless access via NFC wallets across the most iconic commercial real estate properties in New York and beyond,” said Matt Kopel, co-CEO and President of SwiftConnect. “We are excited to once again partner with Silverstein Properties and to extend our leadership into the multi-family housing market. Now, residents can easily access their personal spaces with their iPhone and Apple Watch, and property teams are able to enhance security for their residents—while also automating the process of managing keys and access.” Modern access-control solution SwiftConnect integrates with the Kastle Access Control platform; Schlage® mobile credentials To provide residential tenants with this experience, SwiftConnect integrates with the Kastle Access Control platform; Schlage® mobile credentials; and access control devices from Allegion™, as well as all other necessary business platforms and systems to create a unified digital network for hassle-free mobile access. “Kastle is thrilled to be a partner on the Silver Tower project, leveraging Kastle’s robust and proven access-control products to create a modern access-control solution that delivers an unparalleled experience both property owners and residents can trust,” said Haniel Lynn, CEO of Kastle. Schlage mobile-enabled wireless locks “We are excited to work with SwiftConnect and play an important role in Silver Tower's resident key in Apple Wallet multifamily housing deployment,” said Mark Casey, Vice President of National Electronic Sales of Allegion. “Resident Keys in Apple Wallet—alongside our Schlage mobile credentials and Schlage mobile-enabled wireless locks—not only enhances security and convenience for residents, but also exemplifies our commitment to driving the future of seamless access and smart apartment technology.” How seamless access works at Silver Towers Tenants can add their resident key to Apple Wallet after an initial set-up through Silverstein’s Inspire app, using SwiftConnect’s AccessCloud platform. Once added, tenants can hold their iPhone or Apple Watch near a door reader or smart lock for seamless access to the apartment building, their home, and shared fitness and amenity spaces. With Express Mode, tenants don’t need to wake or unlock their device to use their resident key—they can simply hold their device near a reader and go. If an iPhone needs to be charged, they can still use their device to access their apartment and amenity spaces with Power Reserve. Resident key in Apple Wallet takes full advantage of the privacy and security features already built into iPhone and Apple Watch. Data is encrypted and protected against tampering and theft, and Apple cannot see when and where a resident uses a home key in Wallet. Silverstein’s holistic customer experience program The new offering falls under Inspire, Silverstein’s holistic customer experience program that reshapes how, when, and where the company’s customers live and work. Inspire brings hospitality services, social and wellness programming, data-driven workplace technology, and a flexible workspace solution under one umbrella. Since its inception 67 years ago, Silverstein Properties has been recognised for driving innovative technology adoption to enhance the tenant experience. The company has built a reputation for developing exceptional projects, enhancing local communities, providing outstanding services to customers and partners, and driving innovation within the industry.
As a provider of future-oriented business education, The Camp sought an access control solution as forward-thinking as their courses. Their campus site near Aix-en-Provence is diverse, with offices, event spaces, kitchens and two accommodation blocks totalling 170 units. The Camp must remain open around the clock, all week, while maintaining security for staff and visitors. Aperio wireless locks Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks Aperio provided locking devices tailored to every door type — interior and exterior. So far, The Camp has integrated 221 Aperio Wireless Escutcheons, 42 Aperio Wireless Cylinders and 10 Aperio Wireless Handles within a TIL Technologies security system. Integrated online with the central system and controlled from the same interface, these Aperio devices effortlessly handle daily staff traffic of around 250 people. Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks. Aperio visitor access system Up to 2,000 external visitors arrive on-site when The Camp stages an event — and each must also have credentials issued and access filtered through the site. Aperio makes it straightforward to enable visitor access. “Many credentials get lost and Aperio enables us to handle this efficiently,” says Benjamin Ciotto, Head of Information Technology at The Camp. A few clicks are all it takes to cancel a lost key card and issue a replacement. Real-time and future-proofed Security staff at The Camp ensure only authorised users enter offices where expensive video projectors and screens are stored. Their TIL integration enables real-time management of the whole site, with specific profiles created to segment individuals who need fine-grained access to specific areas. “Online mode is very important because (access) rights are very often updated for the constantly shifting campus population,” explains Benjamin Ciotto, adding “We can also program access to defined time slots, which is essential when we welcome 200 people for an all-day meeting, for example.” Aperio product ecosystem’s performance Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos Aperio technology also met The Camp’s need for an aesthetically pleasing, wireless solution. They did not want to compromise their interior or exterior design. The Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos. Because Aperio devices are wireless and battery-powered, they are much more energy efficient than traditional wired locking systems, which require an “always-on” mains connection. Multiple Aperio devices Multiple Aperio devices have independently assessed Environmental Product Declarations (EPDs). These detail the footprint of each device through its full life cycle, from production to disposal. “Aperio is a real comfort of use,” Benjamin Ciotto concludes. “And we handle the easy maintenance for ourselves.”
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. Modern digital solution Modern digital solution would provide better oversight of movement around the building They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorisations, even at the last minute. Digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. Maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provide security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.
Munich’s Hofbräuhaus enjoys an iconic status, as both a heritage property and a spiritual home for lovers of German beer. “In this historic building is the world’s most famous tavern,” explains its Security Manager, Robert Graßl, adding “The whole world goes in and out. Security is very important.” Bavarian Duke Wilhelm V commissioned Munich’s original Hofbräuhaus in 1589, initially as a brewery to supply the Wittelsbacher Hof. Moved at the end of the 19th century and severely damaged during World War II, it underwent reconstruction in 1958. It now attracts tourists and city locals, seating up to 3,000 guests indoors and a further 400 in the beer garden. Access rights management Digital devices and low-impact skills were needed to assure compliance with origin protection Although the building is an important heritage monument, it requires 21st-century digital access to keep site users safe and streamline day-to-day operations. They wanted fast, secure access rights management for employees and service providers – including up to 100 waiters working each shift – within a unified system that could authorise access at both the Hofbräuhaus and their food production facility in Brunntal. Of course, inobtrusive digital devices and low-impact installation were a necessity to ensure compliance with heritage preservation regulations. Digital access for a famous heritage building Many electronic access products and technologies are not appropriate for historic buildings. An eCLIQ key-based digital access solution is different: eCLIQ cylinders are compatible with the strict monument preservation requirements at the Hofbräuhaus. They have a flush fit, so don’t even appear to be part of an electronic locking system. With wireless installation at the doors, devices blend with the building interior. “We can exchange a mechanical cylinder 1:1 with an eCLIQ cylinder without having to modify anything on the door or install cables,” confirms Miriem Hammoudi, Business Development Manager at ASSA ABLOY Sicherheitstechnik GmbH. ASSA ABLOY fitted around 100 eCLIQ locking cylinders and supplied 340 eCLIQ programmable keys for Hofbräuhaus managers to issue to relevant staff and service contractors. Easy operation for flexible, cost-efficient management Every eCLIQ key has an integrated chip and is programmable individually for the keyholder Every eCLIQ key has an integrated chip and is programmable individually for the keyholder. The versatility of eCLIQ is demonstrated when a key is lost: Access authorisations are removed rapidly – simply by reprogramming cylinders – ensuring security is maintained. The eCLIQ system also helps manage workflows for service providers, such as cleaners: Their access is enabled on a time-limited basis. A standard battery inside each programmable electronic key powers the cylinder or padlock on insertion – and encrypts data transfer between cylinder, key and system – so no external power source or wiring is needed. Scalable web-based platform The Hofbräuhaus team manages their system via a flexible, scalable web-based platform, CLIQ Web Manager: “I can program keys from anywhere or also block them quickly if a key has been lost or if someone is no longer allowed to enter,” says Robert Graßl. He adds, “And I can install any cylinder in any door by adjusting the length. I don’t have to carry extra stock which is really cost effective.” New master key system With the hosting solution chosen, access data is stored securely at ASSA ABLOY, accessible anytime and from any location, which is an ideal configuration for managing large systems or multiple locations. Their system is easy to expand anytime – future-proofing Hofbräuhaus access. “The situation before the new master key system was installed was problematic,” says Robert Graßl, adding “Keys were distributed and nobody knew who held them. Now, everyone carries only one key programmed with details of where and when they can enter. It’s perfect.”
Artificial Intelligence Technology Solutions, Inc., a pioneer in AI-driven security and productivity solutions for enterprise clients, along with its subsidiary Robotic Assistance Devices (RAD), announced recent successes in St. Louis, Missouri, where the Downtown St. Louis Community Improvement District (CID) has embraced RAD’s solutions as part of its public safety initiatives. The CID has deployed multiple ROSA™ security devices, showcased RAD’s ROAMEO™ and RADDOG™ LE2 during the NCAA Frozen Four Championship, and is actively developing a citywide program that would introduce hundreds of RADCam™ units across St. Louis. RAD’s added layer of security RAD’s ROAMEO and RADDOG LE2 were actively deployed in St. Louis as part of the city’s public safety From April 10 to 12, RAD’s ROAMEO and RADDOG LE2 were actively deployed in downtown St. Louis as part of the city’s public safety and engagement efforts during the NCAA Frozen Four Championship. These high-visibility units provided an added layer of security, engaged with residents and visitors, and generated strong public interest. Steve Reinharz, CEO/CTO of AITX and RAD, was interviewed on-site by KSDK, the St. Louis NBC affiliate, where he discussed how RAD’s technologies enhance urban safety while fostering meaningful community interaction. RAD security solutions During the event, representatives from several local organisations, including casino operators, professional sports teams, and major property management firms, visited with RAD and the Downtown St. Louis CID to see firsthand how ROAMEO, ROSA, RADDOG LE2, and other RAD security solutions could be used to support safety and operational efficiency in real-world environments. Of particular interest to many of these organisations was RAD’s multiple SARA™ (Speaking Autonomous Responsive Agent) and ROSS™ (RAD Operations System Software) platforms. RAD’s analytics and automation capabilities Software solutions allow clients to reimagine the role of their existing security infrastructure These software solutions allow clients to reimagine the role of their existing security infrastructure by adding an intelligent, agentic AI layer to legacy hardware. By leveraging RAD’s analytics and automation capabilities, organisations can unlock powerful new functionality from their current systems, enhancing performance, accelerating incident response, and delivering significant cost savings without the need for full system replacement. RAD’s technology: public safety efforts “RAD’s technology has been an impactful addition to our public safety efforts,” said Kelli McCrary, Executive Director of the Downtown St. Louis CID. “The presence of ROSA, ROAMEO, and RADDOG has not only helped deter unwanted activity, but also brought positive attention and community engagement, especially during the excitement of the Frozen Four Championship. This kind of innovation supports our vision for a safer, more welcoming downtown experience.” RAD over traditional security solutions RAD secured deployments of ROSA and RIO units following a competitive review, with city leadership RAD’s momentum extends beyond St. Louis. In Cleveland, RAD partnered with Downtown Cleveland, Inc. to launch a smart security initiative in Public Square, featuring the RIO™ 360 tower with live video integration into the city’s crime centre. In Nashville, RAD secured deployments of ROSA and RIO units following a competitive review, with city leadership opting for RAD over traditional security solutions to enhance monitoring and deterrence in key public areas. How RAD’s solutions meet the evolving security needs As municipalities and CIDs search for scalable, cost-effective ways to secure public spaces, RAD has emerged as a trusted partner in redefining how cities approach safety. From high-traffic districts to major public events, RAD’s AI-powered devices provide 24/7 monitoring, advanced detection capabilities, and autonomous responses that relieve the burden on human personnel. The recent deployments in St. Louis, Cleveland, and Nashville illustrate how RAD’s solutions meet the evolving security needs of urban centres while reinforcing community confidence. RAD's effective security solutions “We’re seeing growing interest from CIDs and public sector organisations that are eager to rethink how they secure their communities,” said Reinharz. “RAD is executing a nationwide campaign to deliver meaningful, affordable, and effective security solutions to cities, towns, and districts across the country. Our technology gives these organisations the tools to protect public spaces, ease the strain on human resources, and deliver a stronger sense of safety for residents and visitors alike.” Outdated approaches and deployments RAD welcomes inquiries from municipalities, CIDs, BIDs, DDAs, and other organisations “It’s incredibly rewarding to see our devices actively supporting the safety goals of communities like St. Louis, Cleveland, Nashville, and others,” said Troy McCanna, Chief Security Officer at RAD. “These deployments represent a shift away from outdated approaches and a move toward intelligent, responsive technology that delivers results. We’re proud to be working hand-in-hand with local pioneers who are committed to creating safer urban environments through innovation.” How its AI-powered security solutions can support safety goals RAD welcomes inquiries from municipalities, Community Improvement Districts (CIDs), Business Improvement Districts (BIDs), Downtown Development Authorities (DDAs), and other organisations focused on public safety and urban revitalisation. The Company offers personalised consultations to explore how its AI-powered security solutions can support local safety goals, improve operational efficiency, and strengthen community trust. RAD's security guarding and monitoring model RAD solutions are precisely designed to provide cost savings to businesses of between 35%-80% AITX, through its subsidiary, Robotic Assistance Devices, Inc. (RAD), is redefining the nearly $50 billion (US) security and guarding services industry through its broad lineup of innovative, AI-driven Solutions-as-a-Service business model. RAD solutions are specifically designed to provide cost savings to businesses of between 35%-80% when compared to the industry’s existing and costly manned security guarding and monitoring model. RAD AI-based analytics and software platforms RAD delivers these tremendous cost savings via a suite of stationary and mobile robotic solutions that complement, and at times, directly replace the need for human personnel in environments better suited for machines. All RAD technologies, AI-based analytics and software platforms are developed in-house. RAD has a prospective sales pipeline of over 35 Fortune 500 companies and numerous other client opportunities. RAD expects to continue to attract new business as it converts its existing sales opportunities into deployed clients, generating a recurring revenue stream. Each Fortune 500 client has the potential of making numerous reorders over time.
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. Modern digital solution Modern digital solutions would provide better oversight of movement around the building All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management, they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorizations, even at the last minute. ASSA ABLOY’s smart key digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. eCLIQ system maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provides security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.
Silverstein Properties, a pioneering real estate development, investment, and management firm, and its partners SwiftConnect, Allegion, and Kastle, announced they are live with resident keys in Apple Wallet for all apartment units at a multi-family housing location: Silverstein’s Silver Towers residential property at 606 West 42nd Street in New York City. Silverstein’s residential tenants now have an easy and secure way to add a resident key to Apple Wallet to access the apartment building and unlock their homes with a simple tap of an iPhone or Apple Watch—thus eliminating the need to use a traditional, physical key. Resident key in Apple Wallet The rollout of keys in Apple Wallet marks an important milestone for the U.S. real estate industry “We’re excited to make it easy for our residents to use their resident key in Apple Wallet to get into their buildings, homes, and common areas, which builds upon our previous offering to office tenants who use their employee badge in Apple Wallet to access offices and shared spaces including lounges, cafes, conference facilities, and yoga studios,” said Tal Kerret, President of Silverstein Properties. The rollout of keys in Apple Wallet marks an important milestone for the U.S. real estate industry, as property owners and employers reimagine the home and workplace experience for residents, office tenants, and employees. SwiftConnect’s success: Enhance security for residents “The Silver Towers project builds on SwiftConnect’s success in delivering seamless access via NFC wallets across the most iconic commercial real estate properties in New York and beyond,” said Matt Kopel, co-CEO and President of SwiftConnect. “We are excited to once again partner with Silverstein Properties and to extend our leadership into the multi-family housing market. Now, residents can easily access their personal spaces with their iPhone and Apple Watch, and property teams are able to enhance security for their residents—while also automating the process of managing keys and access.” Modern access-control solution SwiftConnect integrates with the Kastle Access Control platform; Schlage® mobile credentials To provide residential tenants with this experience, SwiftConnect integrates with the Kastle Access Control platform; Schlage® mobile credentials; and access control devices from Allegion™, as well as all other necessary business platforms and systems to create a unified digital network for hassle-free mobile access. “Kastle is thrilled to be a partner on the Silver Tower project, leveraging Kastle’s robust and proven access-control products to create a modern access-control solution that delivers an unparalleled experience both property owners and residents can trust,” said Haniel Lynn, CEO of Kastle. Schlage mobile-enabled wireless locks “We are excited to work with SwiftConnect and play an important role in Silver Tower's resident key in Apple Wallet multifamily housing deployment,” said Mark Casey, Vice President of National Electronic Sales of Allegion. “Resident Keys in Apple Wallet—alongside our Schlage mobile credentials and Schlage mobile-enabled wireless locks—not only enhances security and convenience for residents, but also exemplifies our commitment to driving the future of seamless access and smart apartment technology.” How seamless access works at Silver Towers Tenants can add their resident key to Apple Wallet after an initial set-up through Silverstein’s Inspire app, using SwiftConnect’s AccessCloud platform. Once added, tenants can hold their iPhone or Apple Watch near a door reader or smart lock for seamless access to the apartment building, their home, and shared fitness and amenity spaces. With Express Mode, tenants don’t need to wake or unlock their device to use their resident key—they can simply hold their device near a reader and go. If an iPhone needs to be charged, they can still use their device to access their apartment and amenity spaces with Power Reserve. Resident key in Apple Wallet takes full advantage of the privacy and security features already built into iPhone and Apple Watch. Data is encrypted and protected against tampering and theft, and Apple cannot see when and where a resident uses a home key in Wallet. Silverstein’s holistic customer experience program The new offering falls under Inspire, Silverstein’s holistic customer experience program that reshapes how, when, and where the company’s customers live and work. Inspire brings hospitality services, social and wellness programming, data-driven workplace technology, and a flexible workspace solution under one umbrella. Since its inception 67 years ago, Silverstein Properties has been recognised for driving innovative technology adoption to enhance the tenant experience. The company has built a reputation for developing exceptional projects, enhancing local communities, providing outstanding services to customers and partners, and driving innovation within the industry.


Round table discussion
Technological leaps in the last several decades have revolutionised biometrics. The technologies are constantly evolving, spanning facial recognition to iris scanning to fingerprints, to provide new levels of security and convenience. Biometrics are everywhere, from smartphones to border control, constantly evolving to meet the needs of our increasingly digital world. They are also more accurate and easier to use than ever. We asked this week's Expert Panel Roundtable: What’s new with biometrics?
Historically, the emphasis of security systems has been on reactivity, whether it’s providing video evidence of an incident or data to support a resulting investigation. Reactivity is core to impactful security, but increasingly, systems are also seeking to be more proactive. A proactive system seeks to prevent events from happening in the first place, thus mitigating the harm to an organisation, and making the need for a reactive response moot. We asked this week’s Expert Panel Roundtable: How can security systems be proactive? Please provide a couple of examples.
Biometrics is both a mature technology in the physical security world and an innovation perpetually on the cutting edge. Biometric technologies received a boost during the COVID pandemic when “touchless” became a buzzword with particular relevancy to the world of biometrics. Higher security needs, such as “two-factor authentication,” are also driving demand for biometric products. We asked this week’s Expert Panel Roundtable: What are the latest technology trends in biometrics?
Products


White papers

Securing unmanned infrastructure at the network edge
Download
Protecting dormitory residents and assets
Download
Wireless Access Control eBook
Download
Palm vein recognition
Download
Securing unmanned infrastructure at the network edge
Download
Protecting dormitory residents and assets
Download
Wireless Access Control eBook
Download
Palm vein recognition
Download
Securing unmanned infrastructure at the network edge
Download
Protecting dormitory residents and assets
Download

Videos
Fingerprint Locks: Manufacturers & Suppliers

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download