Door access control
Camden Door Controls has introduced the industry's first 1/2" RIM Strike with 15 lbs. preload. Camden 1299 Series strikes are Grade 1 rated, with UL 1034/294 and ANSI/BHMA listings. Available in brushed stainless steel or black finish, these 1299 strikes offer 'Universal' performance with selectable 12/24V, AC/DC voltage, and fail-secure/fail-safe operation. Latch monitor included. 1299 Series Preload RIM strikes 1299 Series strikes are packaged with 1/8" and 1/4" spacer plates to accommodat...
ASSA ABLOY has signed an agreement to acquire Door System, a Danish manufacturer of high-quality fire rated doors with particular expertise in the pharmaceutical, food and retail industries. "I am very pleased to welcome Door System to ASSA ABLOY. This acquisition delivers on our strategy to add complementary products and solutions to our core business,” says Nico Delvaux, President and CEO of ASSA ABLOY. ASSA ABLOY acquires Door System Sales for 2024 amounted to about MDKK 125 (ap...
Camden Door Controls is proud to announce the launch of its new 1420 Series Low-Profile Fire-Rated Strike, designed to provide a cost-effective solution for code compliance in UL fire-rated doors and frames with cylindrical locksets. Built to the highest industry standards, the CX-ED1420 strikes are Grade 1 ANSI fire-rated and engineered for 1/2” to 5/8” latch projection. CX-ED1420 Series features They offer exceptional durability with 1,500 lbs static strength and are factory-tes...
Gunnebo Safe Storage has strengthened its ModuleGuard range of modular vault doors and strong rooms with ballistic resistance, further enhancing security against physical attacks. Developed through customer insights and research, ModuleGuard from the global security specialist features improved materials and manufacturing processes, reducing its carbon footprint for a more sustainable approach. Its certified bolt assembly allows for easy installation, even in areas with floor load limitations....
SYSGO, a European pioneer in secure real-time software solutions, has been chosen to supply cutting-edge software technology for the EAGLE-1 project. This innovative mission, led by SES, a provider of global content and connectivity solutions, in collaboration with 20 European partners and supported by the European Space Agency and the European Commission, will enable long-distance Quantum Key Distribution. The mission's goal is to design, launch, and operate EAGLE-1, establishing the first so...
DoorBird, a pioneer in IP access control and intercom technology, excited to announce its participation in ISC West 2025. Taking place from April 2-4 at the Venetian Expo in Las Vegas, Nevada. At booth #7070, DoorBird will unveil its latest advancements in smart door communication and security solutions. Enhancing door security Enhancing safety and convenience for both residential and commercial applications. We are proud to partner with industry pioneers, including ASSA ABLOY Door Security S...
News
dormakaba's upcoming EasyAssist™ low energy swing door operator makes entrances more accessible, convenient, and hygienic – with lower costs and time savings from planning to installation. dormakaba will preview EasyAssist at booth #20007 during the International Security Conference and Exposition (ISC) West 2025 in Las Vegas (March 31 - April 4). Operating modes and functions EasyAssist can be used in offices, medical practice buildings, hotels, retail stores, and schools Thanks to its sleek, compact design, EasyAssist can be used in offices, medical practice buildings, hotels, retail stores, schools, and apartment buildings. The new EasyAssist low-energy operator is easy to plan, install, and operate, reliably ensures accessibility and safety, and is environmentally friendly. With its four different operating modes and additional functions, opening doors becomes considerably easier. EasyAssist low-energy operator “Our new EasyAssist low energy swing door operator, coming soon, perfectly demonstrates how entrances can be made more barrier-free, comfortable, and aesthetically pleasing at great value,” said Bret Holbrook, Senior Vice President of Access Hardware Solutions (AHS) and Access Control Solutions (ACS) Channel Sales for dormakaba North America. “Whether you want to easily automate or add accessibility to an interior door, EasyAssist makes life easier.” Push-N-Go feature Installation, commissioning, and configuration are simplified to save time and effort When EasyAssist is in automatic mode, the door opens automatically using a switch such as a push or wave plate. The Push-N-Go feature requires slight manual door movement, while Power Assist supports manual opening and Power Close ensures safe and silent closing of the door. Both standard doors and fire doors can be equipped with EasyAssist. Installation, commissioning, and configuration are simplified to save time and effort. With EasyAssist, all mounting positions are possible and can retrofit a standard mechanical door closer for consistent aesthetics through a facility. EasyAssist’s SmartArm with integrated cabling Additionally, EasyAssist’s SmartArm with integrated cabling allows for door leaf mounting without exposed wiring, enhancing security by deterring cable tampering and damage. Equipped with an Environmental Product Declaration (EPD) and Health Product Declaration (HPD), EasyAssist's environmental and health-related properties are presented transparently to enable architects, planners, and builders to make informed decisions for sustainable construction projects.
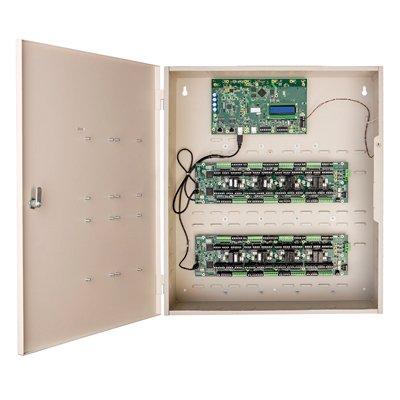
Sielox, the established industry pioneer in layered access control and crisis event management solutions, is demonstrating its latest security innovations at ISC West 2025 at stand 11109. Sielox is showcasing its flagship Pinnacle Access Control Platform that features hundreds of user-selectable filters, enabling security teams to aggregate and manage access data and events with unprecedented insights and visibility. Future of access control Sielox is showcasing its vision Pinnacle's intuitive automated access control features and streamlined workflows"At ISC West we’re highlighting the future of access control with real intelligence. Pinnacle, and our broader portfolio of layered solutions, empower security teams with the proactive insights they need to identify and mitigate evolving threats,” said Karen Evans, President and CEO of Sielox. “We're not just reactive. Sielox delivers proactive data-driven intelligence." Sielox is showcasing this vision with live demonstrations of Pinnacle's intuitive automated access control features and streamlined workflows. Visitors will experience how this comprehensive access control ecosystem creates layered protection that adapts to evolving security challenges while remaining remarkably easy to implement and manage. Next-gen access control solutions Alongside Pinnacle, Sielox is highlighting a variety of powerful security solutions designed to make access control smarter and more efficient, including: Sielox AnyWare A web-based access control platform that lets users monitor and manage security in real time from anywhere. It supports up to 64 doors and 25,000 cardholders and allows authorised personnel to manage security events instantly from any device, anywhere. This plug-and-play system operates via LAN, WAN, WiFi or cellular networks with no monthly fees, configuring in minutes while providing enterprise-grade protection with a lower total cost of ownership. 2700 Controller An intelligent, secure, and fully distributed access controller supporting up to 34 doors with continuous operation even during communication interruptions. This true IP controller features OSDP compatibility, wireless lock integration, and 32GB of memory for redundant configuration—all secured by an embedded Linux OS with AES 256 encryption. CLASS (Crisis Lockdown Alert Status System) Demo An award-winning real-time emergency alert and response system designed to improve communication and safety during critical situations. The solution provides colour-coded status updates on any device, features two-way chat between occupants and responders, and integrates with cameras and access control systems to enable faster, more coordinated emergency responses and real-time lockdown. WaveLynx integration A strategic partnership that enhances Sielox's access control ecosystem with WaveLynx's advanced reader and credential technologies, including secure mobile credentials via Bluetooth. This integration delivers superior security and convenience across financial, commercial, government, and educational environments—giving users flexible credentialing options for migrating from prox credentials. Pinnacle’s UI/UX unveiled “ISC West attendees can get a preview of the Pinnacle new UI and UX,” said Evans, “We encourage attendees to join the end users and CSIs who have guided our development with feedback and direction of their own.”
SAFR from RealNetworks, the world’s foremost AI computer vision platform for access control and security, invites ISC West 2025 attendees to experience its revolutionary suite of AI-powered solutions at booth #25089. SAFR's facial recognition technology delivers unparalleled certainty through industry-pioneer accuracy, enabling organisations to monitor and analyse visual data at speeds far beyond human capabilities—all while maintaining the highest standards of data privacy and personal control. Stronger security and unified solutions "Today's security challenges demand more than isolated point solutions—they require seamlessly integrated systems that work together as a unified whole," said Charisse Jacques, President of SAFR. "Our Unified Facial Recognition Ecosystem represents a fundamental shift in how organisations manage access across their enterprise, bringing unparalleled efficiency, accuracy, and scalability through a single cohesive platform." Unified facial recognition power SAFR unifies identity management, ensures consistent recognition, enables rapid investigationsAt the center of SAFR's Unified Facial Recognition Ecosystem are these core components: One Database to Manage Everything – Eliminating silos with centralised identity management Unified/Shared Watchlist – Ensuring consistent recognition across all deployment points with PACs/VMS integration Forensic Search – Enabling rapid investigation across all connected systems Facial Recognition Analytics – Providing actionable intelligence and operational insights Enterprise Class Solution – Delivering the reliability, security, and scalability demanded by organisations of all sizes Face recognition in action Visitors to booth #25089 will experience firsthand the speed and efficiency of its ecosystem of face-based access control, edge-computing facial recognition cameras and mobile solutions. SAFR will also showcase how its innovative product lineup seamlessly integrates with PACS and VMS systems to provide real-time identity verification at entry points and throughout facilities.
Squire Locks USA will be exhibiting its inigma smart wireless padlock system at ISC West, highlighting the brand’s latest innovation in smart security technology at booth #7056. Inigma allows users to control access to compatible padlocks via Bluetooth, using a smart key programmed through the dedicated app. This provides a smarter, more convenient way for users to manage their security. The smart key can operate multiple padlocks, even in remote locations, and system administrators can grant or revoke access as needed. Next-gen lock technology It eliminates the need for multiple physical keys or expensive replacementsinigma is ideal for utility companies, critical infrastructure, manufacturing facilities, and facility managers, as it eliminates the need for multiple physical keys or expensive replacements if keys are lost. During the three-day event, attendees can see the technology in action alongside Squire’s selection of inigma-compatible padlocks. With end-to-end encryption, inigma builds on Squire USA’s reputation for delivering highly secure, industry-pioneer security solutions. inigma integrates with various Squire padlocks, including the world’s strongest production padlock, the SS100CS, as well as the WS75S, container locks, and other durable Stronghold products. Seamless smart security Show attendees will also get an exclusive look at a new Bluetooth padlock from Squire, which allows authorised users to unlock it using their smartphone. Noel Clarke, Chief Operating Officer at Squire Locks USA, stated: “In recent years, we have seen a major shift in the market. Customers want convenience through smart security, and we are proud to deliver that with inigma." “We are excited to introduce visitors to inigma, demonstrating the power of our technology and how it seamlessly integrates with their existing Squire security solutions. inigma creates a connected network of padlock security, enhancing accessibility for key holders and system administrators. We would love to speak with anyone attending the event about how inigma can provide enhanced security and functionality for various business applications.” Explore inigma tech Visit Squire at booth #7056 during these three days to speak with the team about how this technology can benefit one's business, and learn more about inigma.
Integrated Control Technology a pioneer manufacturer of intelligent access control and security solutions, announced the release of their new TSL access reader series. The new TSL range packs plenty of extras into a slimmed down version of the much-loved ICT readers. Style meets security TSL delivers a dynamic solution for property managers, security professionals, and building operatorsCombining sleek aesthetics with cutting-edge functionality, the TSL delivers a dynamic solution for property managers, security professionals, and building operators seeking a future-proof system for secure and efficient building access. Designed to meet diverse needs, the TSL readers are available in three sizes with a choice of black or white finishes and optional keypads, ensuring it complements any property’s aesthetic while delivering matchless performance. Perfectly tailored for modern buildings. Advanced access control benefits Key benefits include: Hassle-Free Installation: The Quick Connect Plug and app-based configuration enables fast installation. Future-proof: Stay current with live over-the-network firmware updates for future formats, functionality, features, and security enhancements. Customisable Aesthetics: Pick from 3 sizes, 2 finishes, and optional keypads. Visual Feedback at a Glance: Signal access status with 16 configurable LED colours Credential Flexibility: Supports an unmatched number of existing credential types, along with Bluetooth® and NFC capabilities. Unparalleled Security: Advanced encryption-dedicated hardware: Secure Access Module (SAM) handling all credential encryption tasks and key management. Built to Last: IP65-rated for harsh environments and vandal-resistant options for enhanced security. Seamless security innovation Armando Morles, Product Manager at ICT, had the following to say about the product launch, “The new TSL access reader series provides our customers and their end-users with a seamless blend of style, user-friendly customisation, technology and advanced capabilities.”
dormakaba is expanding EntriWorX™ with the North American launch of EntriWorX Planner and the introduction of new technology to advance the EntriWorX Insights platform. dormakaba will demonstrate these updates at booth #20007 during the International Security Conference and Exposition (ISC) West 2025 in Las Vegas (March 31 - April 4). Digital environment “We are continually refining EntriWorX to meet the dynamic needs of our customers today,” said Matt Therrien, Associate Vice President, Architectural Services for dormakaba North America. “Now, our digital environment that is used to address access challenges at every phase of a building’s life cycle is even better at helping anyone involved in building construction and maintenance do their jobs more productively.” Both solutions are designed to optimise the planning, monitoring, and operation of access systems. EntriWorX planner EntriWorX Planner significantly reduces costly omissions or duplications that create delays Available in North America for the first time, the dormakaba EntriWorX Planner is a powerful, user-friendly tool for planning door solutions and access control systems. Introduced in Europe in 2022, this cloud-based planning tool delivers design planning support and expands specification writing services from a team of opening solutions experts for seamless collaboration. The tool generates coordinated elevation drawings during the design phase, eliminating delays and costly rework caused by missed wiring requirements. EntriWorX Planner significantly reduces costly omissions or duplications that create delays in the overall delivery of a project. EntriWorX Insights First introduced at last year’s ISC West, EntriWorX Insights provides transparency and efficiency, making it possible to maintain door systems proactively based on historical data from a single, centralised dashboard. New this year is the introduction of Connector One, a device offering seamless integration for IoT-enabled doors. dormakaba’s automated openings Connector One communicates telemetric data about dormakaba’s automated openings A small but powerful device, Connector One communicates telemetric data about dormakaba’s automated openings to EntriWorX Insights or the customer’s building management system. As a result, customers can take control of their automatic doors individually by knowing exactly what is wrong with them, the moment it happens, and fixing the problem locally or scheduling maintenance before it becomes a problem. Biggest challenges of managing automated doors “Connector One addresses some of the biggest challenges of managing automated doors in buildings: Is there an error at the door? Is a door locked when it should be open? Does it need maintenance? Our customers can now see the status of every door in the building at any time,” said Derek Sarmas, Associate Vice President Sales, Access Automation Solutions. “Both enhancements to our EntriWorX environment were created to drive digitalisation and reflect our commitment to smarter building solutions that simplify access planning and maintenance. We hope you visit us at ISC West 2025 to see them in action.”
dormakaba's upcoming EasyAssist™ low energy swing door operator makes entrances more accessible, convenient, and hygienic – with lower costs and time savings from planning to installation. dormakaba will preview EasyAssist at booth #20007 during the International Security Conference and Exposition (ISC) West 2025 in Las Vegas (March 31 - April 4). Operating modes and functions EasyAssist can be used in offices, medical practice buildings, hotels, retail stores, and schools Thanks to its sleek, compact design, EasyAssist can be used in offices, medical practice buildings, hotels, retail stores, schools, and apartment buildings. The new EasyAssist low-energy operator is easy to plan, install, and operate, reliably ensures accessibility and safety, and is environmentally friendly. With its four different operating modes and additional functions, opening doors becomes considerably easier. EasyAssist low-energy operator “Our new EasyAssist low energy swing door operator, coming soon, perfectly demonstrates how entrances can be made more barrier-free, comfortable, and aesthetically pleasing at great value,” said Bret Holbrook, Senior Vice President of Access Hardware Solutions (AHS) and Access Control Solutions (ACS) Channel Sales for dormakaba North America. “Whether you want to easily automate or add accessibility to an interior door, EasyAssist makes life easier.” Push-N-Go feature Installation, commissioning, and configuration are simplified to save time and effort When EasyAssist is in automatic mode, the door opens automatically using a switch such as a push or wave plate. The Push-N-Go feature requires slight manual door movement, while Power Assist supports manual opening and Power Close ensures safe and silent closing of the door. Both standard doors and fire doors can be equipped with EasyAssist. Installation, commissioning, and configuration are simplified to save time and effort. With EasyAssist, all mounting positions are possible and can retrofit a standard mechanical door closer for consistent aesthetics through a facility. EasyAssist’s SmartArm with integrated cabling Additionally, EasyAssist’s SmartArm with integrated cabling allows for door leaf mounting without exposed wiring, enhancing security by deterring cable tampering and damage. Equipped with an Environmental Product Declaration (EPD) and Health Product Declaration (HPD), EasyAssist's environmental and health-related properties are presented transparently to enable architects, planners, and builders to make informed decisions for sustainable construction projects.
Sielox, the established industry pioneer in layered access control and crisis event management solutions, is demonstrating its latest security innovations at ISC West 2025 at stand 11109. Sielox is showcasing its flagship Pinnacle Access Control Platform that features hundreds of user-selectable filters, enabling security teams to aggregate and manage access data and events with unprecedented insights and visibility. Future of access control Sielox is showcasing its vision Pinnacle's intuitive automated access control features and streamlined workflows"At ISC West we’re highlighting the future of access control with real intelligence. Pinnacle, and our broader portfolio of layered solutions, empower security teams with the proactive insights they need to identify and mitigate evolving threats,” said Karen Evans, President and CEO of Sielox. “We're not just reactive. Sielox delivers proactive data-driven intelligence." Sielox is showcasing this vision with live demonstrations of Pinnacle's intuitive automated access control features and streamlined workflows. Visitors will experience how this comprehensive access control ecosystem creates layered protection that adapts to evolving security challenges while remaining remarkably easy to implement and manage. Next-gen access control solutions Alongside Pinnacle, Sielox is highlighting a variety of powerful security solutions designed to make access control smarter and more efficient, including: Sielox AnyWare A web-based access control platform that lets users monitor and manage security in real time from anywhere. It supports up to 64 doors and 25,000 cardholders and allows authorised personnel to manage security events instantly from any device, anywhere. This plug-and-play system operates via LAN, WAN, WiFi or cellular networks with no monthly fees, configuring in minutes while providing enterprise-grade protection with a lower total cost of ownership. 2700 Controller An intelligent, secure, and fully distributed access controller supporting up to 34 doors with continuous operation even during communication interruptions. This true IP controller features OSDP compatibility, wireless lock integration, and 32GB of memory for redundant configuration—all secured by an embedded Linux OS with AES 256 encryption. CLASS (Crisis Lockdown Alert Status System) Demo An award-winning real-time emergency alert and response system designed to improve communication and safety during critical situations. The solution provides colour-coded status updates on any device, features two-way chat between occupants and responders, and integrates with cameras and access control systems to enable faster, more coordinated emergency responses and real-time lockdown. WaveLynx integration A strategic partnership that enhances Sielox's access control ecosystem with WaveLynx's advanced reader and credential technologies, including secure mobile credentials via Bluetooth. This integration delivers superior security and convenience across financial, commercial, government, and educational environments—giving users flexible credentialing options for migrating from prox credentials. Pinnacle’s UI/UX unveiled “ISC West attendees can get a preview of the Pinnacle new UI and UX,” said Evans, “We encourage attendees to join the end users and CSIs who have guided our development with feedback and direction of their own.”
SAFR from RealNetworks, the world’s foremost AI computer vision platform for access control and security, invites ISC West 2025 attendees to experience its revolutionary suite of AI-powered solutions at booth #25089. SAFR's facial recognition technology delivers unparalleled certainty through industry-pioneer accuracy, enabling organisations to monitor and analyse visual data at speeds far beyond human capabilities—all while maintaining the highest standards of data privacy and personal control. Stronger security and unified solutions "Today's security challenges demand more than isolated point solutions—they require seamlessly integrated systems that work together as a unified whole," said Charisse Jacques, President of SAFR. "Our Unified Facial Recognition Ecosystem represents a fundamental shift in how organisations manage access across their enterprise, bringing unparalleled efficiency, accuracy, and scalability through a single cohesive platform." Unified facial recognition power SAFR unifies identity management, ensures consistent recognition, enables rapid investigationsAt the center of SAFR's Unified Facial Recognition Ecosystem are these core components: One Database to Manage Everything – Eliminating silos with centralised identity management Unified/Shared Watchlist – Ensuring consistent recognition across all deployment points with PACs/VMS integration Forensic Search – Enabling rapid investigation across all connected systems Facial Recognition Analytics – Providing actionable intelligence and operational insights Enterprise Class Solution – Delivering the reliability, security, and scalability demanded by organisations of all sizes Face recognition in action Visitors to booth #25089 will experience firsthand the speed and efficiency of its ecosystem of face-based access control, edge-computing facial recognition cameras and mobile solutions. SAFR will also showcase how its innovative product lineup seamlessly integrates with PACS and VMS systems to provide real-time identity verification at entry points and throughout facilities.
Squire Locks USA will be exhibiting its inigma smart wireless padlock system at ISC West, highlighting the brand’s latest innovation in smart security technology at booth #7056. Inigma allows users to control access to compatible padlocks via Bluetooth, using a smart key programmed through the dedicated app. This provides a smarter, more convenient way for users to manage their security. The smart key can operate multiple padlocks, even in remote locations, and system administrators can grant or revoke access as needed. Next-gen lock technology It eliminates the need for multiple physical keys or expensive replacementsinigma is ideal for utility companies, critical infrastructure, manufacturing facilities, and facility managers, as it eliminates the need for multiple physical keys or expensive replacements if keys are lost. During the three-day event, attendees can see the technology in action alongside Squire’s selection of inigma-compatible padlocks. With end-to-end encryption, inigma builds on Squire USA’s reputation for delivering highly secure, industry-pioneer security solutions. inigma integrates with various Squire padlocks, including the world’s strongest production padlock, the SS100CS, as well as the WS75S, container locks, and other durable Stronghold products. Seamless smart security Show attendees will also get an exclusive look at a new Bluetooth padlock from Squire, which allows authorised users to unlock it using their smartphone. Noel Clarke, Chief Operating Officer at Squire Locks USA, stated: “In recent years, we have seen a major shift in the market. Customers want convenience through smart security, and we are proud to deliver that with inigma." “We are excited to introduce visitors to inigma, demonstrating the power of our technology and how it seamlessly integrates with their existing Squire security solutions. inigma creates a connected network of padlock security, enhancing accessibility for key holders and system administrators. We would love to speak with anyone attending the event about how inigma can provide enhanced security and functionality for various business applications.” Explore inigma tech Visit Squire at booth #7056 during these three days to speak with the team about how this technology can benefit one's business, and learn more about inigma.
Integrated Control Technology a pioneer manufacturer of intelligent access control and security solutions, announced the release of their new TSL access reader series. The new TSL range packs plenty of extras into a slimmed down version of the much-loved ICT readers. Style meets security TSL delivers a dynamic solution for property managers, security professionals, and building operatorsCombining sleek aesthetics with cutting-edge functionality, the TSL delivers a dynamic solution for property managers, security professionals, and building operators seeking a future-proof system for secure and efficient building access. Designed to meet diverse needs, the TSL readers are available in three sizes with a choice of black or white finishes and optional keypads, ensuring it complements any property’s aesthetic while delivering matchless performance. Perfectly tailored for modern buildings. Advanced access control benefits Key benefits include: Hassle-Free Installation: The Quick Connect Plug and app-based configuration enables fast installation. Future-proof: Stay current with live over-the-network firmware updates for future formats, functionality, features, and security enhancements. Customisable Aesthetics: Pick from 3 sizes, 2 finishes, and optional keypads. Visual Feedback at a Glance: Signal access status with 16 configurable LED colours Credential Flexibility: Supports an unmatched number of existing credential types, along with Bluetooth® and NFC capabilities. Unparalleled Security: Advanced encryption-dedicated hardware: Secure Access Module (SAM) handling all credential encryption tasks and key management. Built to Last: IP65-rated for harsh environments and vandal-resistant options for enhanced security. Seamless security innovation Armando Morles, Product Manager at ICT, had the following to say about the product launch, “The new TSL access reader series provides our customers and their end-users with a seamless blend of style, user-friendly customisation, technology and advanced capabilities.”
dormakaba is expanding EntriWorX™ with the North American launch of EntriWorX Planner and the introduction of new technology to advance the EntriWorX Insights platform. dormakaba will demonstrate these updates at booth #20007 during the International Security Conference and Exposition (ISC) West 2025 in Las Vegas (March 31 - April 4). Digital environment “We are continually refining EntriWorX to meet the dynamic needs of our customers today,” said Matt Therrien, Associate Vice President, Architectural Services for dormakaba North America. “Now, our digital environment that is used to address access challenges at every phase of a building’s life cycle is even better at helping anyone involved in building construction and maintenance do their jobs more productively.” Both solutions are designed to optimise the planning, monitoring, and operation of access systems. EntriWorX planner EntriWorX Planner significantly reduces costly omissions or duplications that create delays Available in North America for the first time, the dormakaba EntriWorX Planner is a powerful, user-friendly tool for planning door solutions and access control systems. Introduced in Europe in 2022, this cloud-based planning tool delivers design planning support and expands specification writing services from a team of opening solutions experts for seamless collaboration. The tool generates coordinated elevation drawings during the design phase, eliminating delays and costly rework caused by missed wiring requirements. EntriWorX Planner significantly reduces costly omissions or duplications that create delays in the overall delivery of a project. EntriWorX Insights First introduced at last year’s ISC West, EntriWorX Insights provides transparency and efficiency, making it possible to maintain door systems proactively based on historical data from a single, centralised dashboard. New this year is the introduction of Connector One, a device offering seamless integration for IoT-enabled doors. dormakaba’s automated openings Connector One communicates telemetric data about dormakaba’s automated openings A small but powerful device, Connector One communicates telemetric data about dormakaba’s automated openings to EntriWorX Insights or the customer’s building management system. As a result, customers can take control of their automatic doors individually by knowing exactly what is wrong with them, the moment it happens, and fixing the problem locally or scheduling maintenance before it becomes a problem. Biggest challenges of managing automated doors “Connector One addresses some of the biggest challenges of managing automated doors in buildings: Is there an error at the door? Is a door locked when it should be open? Does it need maintenance? Our customers can now see the status of every door in the building at any time,” said Derek Sarmas, Associate Vice President Sales, Access Automation Solutions. “Both enhancements to our EntriWorX environment were created to drive digitalisation and reflect our commitment to smarter building solutions that simplify access planning and maintenance. We hope you visit us at ISC West 2025 to see them in action.”


Expert commentary
Amidst the challenges of a prevailing economic downturn, the retail sector finds itself grappling with an unparalleled rise in incidents of shoplifting, theft, and burglaries. The disconcerting scenes witnessed on London’s Oxford Street in August 2023, where crowds gathered, looting as many stores as possible, sent shockwaves across the nation’s retailers. This alarming surge in retail crime has put retailers on high alert, as they contend with a rising tide of security concerns. Shoplifting concerns Recent data from the Union of Shop Distributive and Allied Workers (USDAW), has raised alarming concerns: shoplifting rates have surged by an unprecedented 24%. In the first half of 2023 alone, there were approximately 8 million reported shoplifting incidents. With the ongoing burden of the cost of living crisis and the approaching festive season, it is expected that these figures will keep surging. Implementing robust security measures Theft and prevention strategies cost retailers approximately £2 billion in 2021/2022 While more help from the Government to support retail workers and the businesses shoplifters target is certainly needed, the implementation of robust security measures will significantly contribute to deterring these crimes from occurring in the first place. British retailers spend millions on tools to deter and catch shoplifters inside stores, from CCTV and security guards to electronic tagging and alarms. The Grocer reported that theft and prevention strategies cost retailers approximately £2 billion in 2021/2022. Despite these initial costs, other threats are at play beyond the shop floor. Break-ins by criminal gangs For many large town centre stores and supermarkets, and units in retail parks, the rear doors and delivery areas are commonly targeted by criminal gangs. It’s not uncommon for thefts to occur from pallets or cages that have been unloaded from lorries and sit waiting to be moved into the building. After-hours break-ins are a risk for all store owners too, particularly over the festive season when a lot of high-value stock has been delivered to shops and supermarkets. Addressing anti-social behaviour The additional fencing was deemed an essential measure to safeguard the community Anti-social behaviour also poses a challenge for retailers. In 2022, an Aldi based in Derby invested in security fencing to protect staff and deter loitering groups. The additional fencing was deemed an essential measure to safeguard the community, as dangerous items were frequently found outside the store, including weapons and hypodermic needles. So how do physical security solutions such as fencing and gates help better protect retail establishments such as supermarkets and edge-of-town retail park shops? Fencing and gates: a critical component of retail security 1. Risk assessment and target hardening A thorough risk assessment will identify potential weak spots that require protection. ‘Target hardening’ involves implementing physical security measures that become more robust as they approach the target. This helps deter intruders while ensuring ease of access for customers and staff. 2. Effective perimeter security Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders Selecting fencing solutions according to the potential threats, site characteristics, and topography is crucial. It is important to specify fencing that strikes a balance and maintains a welcoming appearance while safeguarding external areas of the store or warehouse from potential harm and unauthorised access. Solid fencing which provides concealment can help to conceal expensive goods and remove them as a target for opportunistic theft. Opt for difficult-to-climb security fencing that provides a robust obstacle against thieves, vandals, and intruders. I recommend selecting a sufficiently tall and robust fence such as an acoustic barrier. Its noise-reducing properties are often beneficial for these types of sites too. 3. Controlling vehicular speeds and access To enhance security, consider controlling vehicular speeds and access. One effective approach is the installation of bollards at the ends of traditional high streets. This practice is already commonplace as a means of safeguarding against hostile vehicle attacks, but it can also play a pivotal role in preventing quick getaways of vehicles involved in potential heists. Additionally, employing road blockers and sliding gates at the rear entrances of delivery areas would serve to fortify security further. These measures can help in delaying vehicles, allowing for necessary checks to be conducted. 4. Balancing security with aesthetics The presence of high-security fencing can also make a site more of a target for vandals and burglars Another challenge is avoiding creating an imposing presence, especially important for areas situated near residential communities. The presence of high-security fencing can also make a site more of a target for vandals and burglars. To minimise this risk consider specifying timber fencing and traffic barriers to secure car parks, providing both security and a welcoming atmosphere for shoppers. Taking an integrated approach Combine secure perimeter fencing with effective lighting in places with shaded areas and at doors, gates, and shop windows, alongside Perimeter Intrusion Detection Systems (PIDS), and strategically placed CCTV. These measures will hinder unauthorised entry and escape, increasing the likelihood of detection and apprehension. Prioritising employee wellbeing Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment Installing robust security fencing, complemented by CCTV, good lighting, and guarding, creates a safe environment for employees. This not only safeguards their well-being but also provides peace of mind that they are protected effectively in the case of a burglary or crime. When selecting security products for retail sites, it is advisable to opt for items that have undergone rigorous testing and carry relevant certifications for their security level. Each component should meet industry-specific standards for its intended purpose and originate from manufacturers accredited under ISO 9001:2015. This ensures a high standard of quality and reliability in safeguarding the premises. High-quality security fencing As the cost-of-living crisis continues, crime rates increase, and the festive season approaches, the time to act and implement on-site security is now. By investing in comprehensive security measures, retailers can protect their assets, employees, and customers, ensuring a safer and more secure shopping environment for all. High-quality security fencing is also a sound investment, that requires little or no maintenance once installed. The best fencing solutions are extremely weather-resistant, and won’t suffer from rust or corrosion. With all sectors preparing to ride the rapids of recession in the coming year, improving on-site security while selecting cost-effective measures, is one surefire way to protect your people, your property, and your profits from harm.
The autumn equinox, which marks the start of autumn, occurs this weekend on Saturday, September 23. With darker evenings ahead, the experts at ADT have shared five ways to maximise your home's security. Author's quote Michele Bennett, General Manager at ADT UK&I comments: “Opportunistic thieves use darkness to their advantage, so it’s no surprise that the number of burglaries committed increases when the darker nights draw in." He adds, "Our 2022 burglary report found that burglaries are most common at night, with 58% of burglaries occurring between 6 p.m. and 6 a.m. Taking steps to optimise your home’s security before the clocks go back this year will provide reassurance that your property is as secure as possible.” Five ways to secure your property: Get a monitored alarm installed: A visible alarm system is a strong deterrent to potential burglars, as criminals are less likely to target a home that is protected. In the event of a break-in, a monitored alarm will alert you, your keyholders and depending on the package you take out, the police, ensuring a swift response to an alarm activation. Light up the dark: Well-lit exteriors make your home less appealing to potential intruders. Install motion-activated lights around any entry points, particularly porches and gardens, which alert you to movement on your property. This will also prevent burglars from operating under the cloak of darkness and increase the chance of a passerby spotting suspicious activity. Trim your garden landscape: Thieves look for escape routes and hiding spots when deciding which homes to break into, making gardens with high, overgrown hedges more likely to be targeted. This is especially true in the darker evenings, so be sure to give your garden a thorough tidy-up to make your property less likely to be targeted. It’s also advisable to ensure any tools are locked away in sheds and garages that could assist a burglar such as ladders, or a garden spade to force entry. Be smart with your lights: Using smart plugs allows you to turn on a few well-appointed lights and radios or televisions from any location from your phone. Used in conjunction with an outdoor camera or video doorbell, you can have lamps plugged into smart plugs come on when motion is detected. Programming lights to come on at different times throughout the night will help to deter burglars by making your property look occupied. Purchase a smart doorbell or outdoor camera: Smart doorbells are an effective way to deter burglars as they provide evidence in the event of a break-in, package theft, or other suspicious activity around your home. They also notify you when someone is at your door reducing the chance of you being caught out by a late evening or early morning robbery. Further encroachment Smart doorbells also act as a deterrent to unscrupulous door-to-door sellers and con artists, as video footage is recorded. In the event of a late-night door knock, you can see and speak to whoever is at your front door, without having to open the door. ADT’s new outdoor camera also has two-way audio and a high-pitch deterrent siren so you can warn off anyone from your property to deter any further encroachment.
It’s no secret that the data security sector is constantly changing. It has an annual CGR of about 12.3%. Future trends in data security Much of this has to do with the rise of cybercrime in recent years, with reports showing that cyberattacks happen as often as every 39 seconds. To combat the growing rate of cybercrime, data security has been on the rise. As we journey further into this era, it becomes evident that a spectrum of significant trends is molding the future of data security. This exploration delves into a selection of these trends, unraveling their importance and the potential implications they carry 1. AI security tools will increase Artificial Intelligence is also being used in the development of smart attacks and malware The introduction of Artificial Intelligence in the data security industry brought significant changes, especially in cybersecurity. AI has been the golden standard for face detection, natural language processing, automated threat detection, and automated security systems. Additionally, Artificial Intelligence is also being used in the development of smart attacks and malware, bypassing even the latest security protocols in data control. And as time progresses, AI security tools will flourish and dominate the scene. Let’s take a more in-depth look at three of the top AI security tools. Targeted attack analysis tool Manufacturers utilise targeted attack analysis tools to uncover targeted and stealthy attacks. Artificial Intelligence can be applied to the program’s capabilities, processes, and knowledge. For instance, Symantec launched this tool to combat the Dragon 2.0 attack in 2022. The phishing attack reprimanded multiple energy companies while trying to gain access to their operational networks. Targeted Attack Analysis Tools can analyse incidents and look for similarities from previous situations. They also help detect suspicious activities and collect all the necessary data to determine whether a specific action is malicious. Intercept X tool Results from the Intercept X Tool feature high accuracy and a low false positive rate Sophos, a British security hardware and software company, launched the Intercept X Tool. It engages a neural network that records and analyses data like a human brain. Sophos’ Intercept X Tool can extract features from a single file and perform a deep analysis. It detects malicious activities within 20 milliseconds. Plus, it’s also trained to work on bi-directional sharing and real-world feedback of threat intelligence. Results from the Intercept X Tool feature high accuracy and a low false positive rate. IBM Watson Technology IBM’s QRadar Advisor uses IBM Watson Technology, a unique AI tool for fighting cyber attacks. Artificial Intelligence can auto-investigate activities and indicators for potential exploitation or compromise. With cognitive reasoning, IBM Watson Technology can present critical insights to accelerate the response cycle. Security analysts can utilise this technology to search for threat incidents, reducing the risk of letting them fly under the radar. 2. Blockchain as a security solution It guarantees no points of failure or hackable entrances that can expose datasets inside the system Blockchain is a type of distributed ledger technology (DLT) that aims to establish trust within an untrusting ecosystem. Today it’s one of the most robust cybersecurity technologies in the industry. Blockchain utilises a decentralised ledger system, but your team members can still gain access to transparent information in the cloud. Members can also record, pass along, and view necessary transactional data in the blockchain. The entire blockchain process maintains data integrity within the system while establishing trust among team members. It guarantees no points of failure or hackable entrances that can expose datasets inside the system. Cybersecurity, biometrics Cybersecurity primarily benefits from these features because blockchain can create a secure and robust wall between data and hackers. On top of that, blockchain ledgers can include biometrics like fingerprints and retina scans. These prevent hackers from accessing any private data. Because blockchain is decentralised, it also limits hackable data. Together with the technology’s record-keeping system, each node is provided insight into data manipulation exposing real-time cybercrime attempts. 3. Increased and widened access control Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data Access control is critical in data security. More than a valuable security tool, business leaders can use access control to regulate people accessing any given resource. A company with an IT security setting can control who has the liberty to edit certain files. One of the primary goals of access control is to minimise threats or attacks to organisations and businesses to keep people and data secure. Without access control, expect your company to be open to security issues, including theft, data loss, and breach of data protection laws. Benefits The benefits of increased and widened access control include: Identifying who can access and control your data at specific time intervals. Protecting data from overwriting, accidental deletion, and malicious intent. User permissions that can be readily changed. Compliance and regulation with data privacy laws. Central management of access to data through a reporting portal or a dashboard. Multi-factor authentication Access control comes in various types and systems, so it’s critical to know the features of what you’re looking for. The most common type is multi-factor authentication or MFA. It involves multiple steps before logging in, requiring the user to enter other relevant information besides the password. Some other examples of information include biometrics, answering a security question, or entering a code sent to the user’s email address. Two-factor authentication, role-based access control Two-factor authentication further prevents unauthorised entries that can result in unnecessary data possession Two-factor authentication further prevents unauthorised entries that can result in unnecessary data possession. Another type of access control is role-based access control. In this setup, only one individual can set up access guidelines and grant permissions to specific team members within an organisation. 4. Greater use of the zero-trust security model The zero-trust security model is a framework that requires every user within and outside the organisation to undergo authentication, authorisation, and validation. These are all essential to ensure proper security configuration before access is granted to the company’s applications and data. A zero-trust model assumes that anyone can cause data breaches and that a traditional network edge is not taken into effect. Moreover, it addresses the following modern-day challenges: Hybrid cloud environments. Security of remote workers. Ransomware threats. This framework utilises the combination of multiple advanced technologies, including: A risk-based multi-factor authentication. Endpoint security. Identity protection. Cloud workload technology. The zero-trust model uses all these innovative tools for system identification, user verification, access consideration, and system security maintenance. Constant validation and monitoring Enforcing strict policies and compliance with data privacy laws are also essential Additionally, it also considers data encryption, email security, and asset verification before establishing connections with applications. The architecture of a zero-trust framework requires constant validation and monitoring of the users and the devices they are using. Enforcing strict policies and compliance with data privacy laws are also essential. More importantly, the zero trust architecture requires all organisations to be aware of all their available services and accounts to gain complete control of data handling and manipulation. 5. Increased privacy regulations Privacy regulations and policies guide organisations in proper data control, handling, and security. These policies guide organisations in proper data control, handling, and security. As a responsible business owner, you must comply with these regulations to avoid legal issues. With cybersecurity attacks becoming common, expect increased and stricter privacy regulations to be released in the next few years. While current policies are still taken into effect, various modifications and adjustments will occur to compete with the rising numbers of data breaches, thefts, data loss, and more. California Privacy Rights Act (CPRA) Currently, the California Privacy Rights Act (CPRA) is the most comprehensive legislation on state data privacy. It only started to take effect on January 1, 2023. The CPRA introduces the following principles: Broad individual consumer rights. Significant duties of people who need to collect sensitive and personal information. Additional definitions of data privacy and security. An individual’s duties include releasing information about data collection to concerned data subjects and proper access, correction, and deletion of information. Final thoughts 2023 is a big year for data security. Trends such as increased adoption of zero-trust policies, a greater reliance on AI security tools, and the implementation of blockchain as a security solution are all things we expect to see shortly. Staying up-to-date with these trends is important for keeping your business current and ensuring that you’re adhering to new and changing regulations. Doing so can give you an edge over the competition and keep you out of legal hot water.
Security beat
In the competitive world of physical access control, Big Tech companies are seeking to play a larger role. Physical access competition Apple Wallet continues to stake its claim on mobile credentialing. Amazon One Enterprise is pushing a palm-based identity service. Google/Nest offers smart locks for home access control, with identity and access management provided in the Google Cloud. The entry of these big companies in the historically fragmented physical access control market is causing disruption and foreboding new levels of competition. Apple Wallet impacting credentialing trends The popularity of mobile wallets and contactless technologies in general has grown, creating more demand At Apple’s Worldwide Developer Conference in June 2021, the company announced support for home, office and hotel keys, including corporate badges and student ID cards, in Apple Wallet. Later, the company announced Hyatt as the first hotel partner to support the technology. Since then, the popularity of mobile wallets and contactless technologies in general has grown, creating more demand for a seamless solution such as Apple Wallet. Easy access In 2023, HID Global announced the availability of their employee badge in Apple Wallet, allowing staff and guests to easily access corporate spaces with their iPhone or Apple Watch, including doors, elevators, turnstiles, etc. Employees just need to hold their iPhone or Apple Watch near the reader to unlock. Factors affecting the rate of adoption However, implementing and maintaining an Apple Wallet-based access control system can incur costs for hardware updates, software licencing, and ongoing maintenance. Factors affecting the rate of adoption include the need to upgrade existing infrastructures to accommodate the technology, and the necessity for access control manufacturers to develop and implement integrations with Apple Wallet. Benefits of adoption Keys in Apple Wallet take full advantage of the privacy and security built into the iPhone and Apple Watch With larger companies leading the way, some smaller ones might take longer to catch up. There is also a need to educate building owners and administrators to see the value and benefits of switching to Apple Wallet-based access control. Convenience and greater security can accelerate adoption. Keys in Apple Wallet take full advantage of the privacy and security built into iPhone and Apple Watch. Sensitive data protection A compatible app, specific to the building’s access control system, is needed. Once added, credentials are securely stored in the iPhone's Secure Enclave, a dedicated hardware chip designed for sensitive data protection. Holding an iPhone near an NFC-enabled reader enables transmission of encrypted credentials. In addition to Near Field Communication (NFC), some systems also utilise Bluetooth Low Energy (BLE) for added security, longer read range, and hands-free unlocking. Phones need sufficient battery charge to function. Amazon One Enterprise Enables Palm-Based Biometrics In November 2023, Amazon Web Services Inc. (AWS) announced an identity service providing comprehensive and easy-to-use authentication for physical and digital access control. The system enables users to employ their palm as an access control credential, allowing organisations to provide a fast and contactless experience for employees and others to gain access to physical locations as well as digital assets. Physical and digital locations Physical locations include data centres, office and residential buildings, airports, hotels, resorts Physical locations include data centres, office and residential buildings, airports, hotels, resorts, and educational institutions. IT and security administrators can easily install Amazon One devices and manage users, devices, and software updates using AWS’s Management Console. Elimination of physical credentials An advantage of the Amazon approach is the elimination of physical credentials such as fobs and badges, and digital elements such as personal identification numbers (PINs) and passwords. AWS says security is built into every stage of the service, from multi-layered security controls in the Amazon One device, which is the same technology used in the Amazon Go retail stores, where shoppers can pay for purchases by scanning the palm of their hands. The devices combine palm and vein imagery for biometric matching and deliver an accuracy rate of 99.9999%, which exceeds the accuracy of other biometric alternatives, says the company. AI and ML The palm-recognition technology uses artificial intelligence and machine learning to create a “palm signature” that is associated with identification credentials such as a badge, employee ID or PIN. Boon Edam, a revolving door and turnstile manufacturer, offers Amazon’s palm biometric technology on its equipment, and IHG Hotels & Resorts uses the technology to provide employees a convenient way to identify themselves and gain access to software systems. Google and Nest Devices in Access Control When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone Google’s Nest devices include smart locks for home access control. The Google Nest × Yale Lock allows access control via both physical keys and passcodes accessible through the Google Home app. When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone. Passcodes can be created for family, guests, and other trusted persons. Alerts can be provided whenever someone unlocks and locks the door. When Nest “knows” a resident is away, the door can lock automatically. Voice control, Google Home app Voice control, using Google Assistant integrated with various Nest devices, enables use of voice commands to lock and unlock doors, thus adding another level of convenience. Smart home devices from various manufacturers can be controlled through the Google Home app. SMART Monitoring ADT’s Self Setup smart home security systems integrate Google Nest smart home products with ADT security and life safety technology, including SMART Monitoring technology. Microsoft Azure is another company that could impact access control. The Microsoft Azure Active Directory is an identity and access management platform that could be extended to physical access control, leveraging existing user credentials. Long-Range Impact on the Security Marketplace Big Tech companies are creating platforms for managing access control data, integrating with other security systems Increasingly, Big Tech companies are creating platforms for managing access control data, integrating with other security systems, and offering analytics for optimising security and building operations. Big Tech is also actively researching and developing new technologies for access control, such as facial recognition, voice authentication, and AI-powered anomaly detection. Access control communication and integration As their involvement in physical access control grows, Big Tech companies could potentially gain more influence in setting industry standards for access control communication and integration, similar to how they have become dominant in other areas such as mobile platforms. Given their expertise in user interface design and data analysis, Big Tech companies could help to direct how future access control systems are managed and how users interact with them, including more intuitive and user-friendly operations. Future of physical access control Existing concerns about privacy, security, and potential dominance by a few Big Tech companies could spill over into physical access control. However, traditional security companies, startups, and industry consortiums are also actively developing innovative solutions. Ultimately, the future of physical access control will likely be shaped by a combination of many different players and technologies – large and small.
Companies at GSX 2023 emphasised new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasises ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the mid-market to the cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for the pure cloud, but there are benefits to be realised from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realise the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘soft’ features for integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organisation more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organisation more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centres around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasising performance, protection (cybersecurity), and price, their data centres are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring centre where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
Large-scale events, including both corporate and sporting events, are coming back strongly in the aftermath of the pandemic. With the increase in activity comes more demand for oversized credentials preferred by many event planners and end users. Pent-up demand due to the pandemic has caused a tremendous uptick in the entire ID card industry in 2022. The return of large-scale events and in-person trade shows will extend the higher demand for cards well into 2023 and beyond, says Andrew Schonzeit, President of Idesco, a provider of ID card solutions. Supply chain concerns Supply chain concerns will continue as companies seek to upgrade and purchase new ID printers and badges An impact of the pandemic was a shortage of supplies related to the ID card industry, says Schonzeit. Like other industries, several leading ID card and printer manufacturers had supply chain issues, and some deliveries were delayed at times for more than six months. Supply chain concerns will continue into 2023 as more companies return to the workplace and others seek to upgrade their current systems and purchase new ID printers and badges. Persistent price increase concerns “The shortage created hardships for end users and often resulted in them purchasing any solution that was readily available even if it was not the preferred one,” says Schonzeit. Another issue during the pandemic was persistent price increases, due both to inflationary pressures and a shortage of products. The industry was used to stable prices with infrequent increases, but the pandemic changed this quickly. Some companies also decided to upgrade their entire system as employees returning to the office increased demand. Oversized credentials advantages Among the advantages of oversized credentials is the ability to print more information on the card, says Schonzeit. For example, a larger credential allows event organisers to preprint the corporate agenda on the back of the card to increase efficiency. In addition, companies can enhance their brand presence by distributing a nice thick plastic badge to attendees. Two categories Standard credit card size These are generally CR100 size, which is around 40% larger than the standard credit card Oversized badges fall into two main categories. One category is for cards that are larger than the standard credit card size (CR80), but smaller than event badges. These are generally CR100 size, which is around 40% larger than the standard credit card. They are generally used by law enforcement or healthcare institutions. It is easier to see an oversized badge more clearly from a distance than a regular-sized badge. Oversized ID badges The other category of oversized ID badges is used for events, these badges are typically 3.5” by 5.5” and are usually worn around the neck. These events include categories such as sporting events, corporate events, music festivals, and trade shows. The badges are generally used only for the duration of the event and are often kept as souvenirs. Anticipating the needs “My advice for event planners is to manage your expectations about badges as it is very hard to order extra badges at the last minute,” says Schonzeit. “It is important to plan well in advance and anticipate your needs upfront to help avoid a shortage.” Idesco often gets requests from customers to include some type of technology on the credentials. The most common technologies are proximity cards, NFC, and/or UHF. “It is a much ‘cleaner’ and safer solution if the chip can be embedded within the credential as opposed to putting a sticker on the outside of the credential,” says Schonzeit. Additional technologies in credentials Customers wanting technology in their credentials should allow additional lead time Generally, these additional technologies are used for gaining entry to a location (access control), or they can be used for gathering valuable information regarding an event, including attendance at seminars, crowd flow, vending, and food services information, among others. Supply chain issues have led to less availability of many of the most common chips, which can impact delivery times. Customers wanting technology in their credentials should allow additional lead time, says Schonzeit. Applications In addition to corporate events, sporting events, and trade shows, other markets can also benefit from oversized ID badges. Industries include healthcare, government, and law enforcement. Oversized badges are becoming more popular in hospitals, for example, where color coding can make it easy to identify doctors, nurses, and hospital personnel from a distance, even in congested hospital spaces. ID card necessity Could there be a negative impact on the ID card industry if more companies allow employees to work from home? It’s always a possibility, says Schonzeit. “However, with many hybrid options out there, most employees are required to come to the office either one or two days a week,” he says. “Employees will still need a way to access their workplace for meetings, conferences, etc., and will require an ID card to do so.” Mobile vs. physical credentials The growing popularity of mobile credentials has created some concerns in the ID card marketplace The growing popularity of mobile credentials has created some concerns in the ID card marketplace about the continuing need for a physical credential. So far it has not been an issue. “[Mobile credentials] have not had any type of meaningful effect on the physical ID card market,” says Schonzeit. Relying on smartphones “Sometimes these disruptive technologies can linger in the background for some time and then suddenly have a massive effect on the market. This is something to be concerned about, but I don’t think there is an imminent threat.” A big issue with using only mobile credentials is the need for a backup plan rather than relying only on a smartphone to enter a facility. Also, for mobile credentials to work, specialised readers are required, which requires a large investment. “In my opinion, ID badges are here to stay for the long haul,” says Schonzeit.
Case studies
Soyak Olympiakent in Turkey comprises thousands of apartments that prioritise 'Quality in Life.' It offers a quality and safe living experience, featuring a natural environment, sports facilities, swimming pools, ample parking areas, and a 24-hour private security system supported by an IP video intercom system. The Solution Solution Highlights: Great scalability in large residential apartments Remote and easy mobile access Real-time video and audio communication Emergency alerts Solution Benefits: DNAKE smart intercoms have been installed in 4 Blocks, covering a total of 1,948 apartments. Each entry point features DNAKE S215 4.3” SIP video door stations for secure access. Residents can open doors for visitors not only through the 280M-S8 indoor monitor, typically installed in every apartment, but also via the Smart Pro mobile application, accessible anywhere and anytime. The master station 902C-A in the guard room facilitates real-time communication, enabling guards to receive updates about security events or emergencies immediately. It can connect multiple zones, allowing for better monitoring and response across the premises, thereby enhancing overall safety and security.
The building, constructed in 2005, consists of three 12-storey towers with a total of 309 residential units. Residents have been experiencing issues with noise and unclear sound, which hinder effective communication and lead to frustration. Additionally, there is an increased need for remote unlocking capabilities. The existing 2-wire system, which supports only basic intercom functions, fails to meet the current needs of the residents. The Solution Solution highlights Easy Intercom Retrofitting with Existing Cables Tenant’s Own Choice on Answering Units Solution benefits For installer: DNAKE 2-wire IP intercom solution leverages existing wiring, which allows for a quicker and more efficient installation process. This solution helps avoid the costs associated with new cabling and extensive rewiring, keeping project costs down and making the retrofit more economically attractive. For property manager: The Central Management System (CMS) is an on-premises software solution for managing video intercom systems via the LAN, which has greatly improved the efficiency of property managers. Additionally, with the 902C-A master station, property managers can receive security alarms to take immediate action, and remotely unlock doors for visitors. For resident: Residents can choose their preferred answering unit based on their needs. Options include Linux-based or Android-based indoor monitors, audio-only indoor monitors, or even app-based services without a physical indoor monitor. With DNAKE's cloud service, residents can unlock doors from anywhere, at any time.
As a provider of future-oriented business education, The Camp sought an access control solution as forward-thinking as their courses. Their campus site near Aix-en-Provence is diverse, with offices, event spaces, kitchens and two accommodation blocks totalling 170 units. The Camp must remain open around the clock, all week, while maintaining security for staff and visitors. Aperio wireless locks Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks Aperio provided locking devices tailored to every door type — interior and exterior. So far, The Camp has integrated 221 Aperio Wireless Escutcheons, 42 Aperio Wireless Cylinders and 10 Aperio Wireless Handles within a TIL Technologies security system. Integrated online with the central system and controlled from the same interface, these Aperio devices effortlessly handle daily staff traffic of around 250 people. Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks. Aperio visitor access system Up to 2,000 external visitors arrive on-site when The Camp stages an event — and each must also have credentials issued and access filtered through the site. Aperio makes it straightforward to enable visitor access. “Many credentials get lost and Aperio enables us to handle this efficiently,” says Benjamin Ciotto, Head of Information Technology at The Camp. A few clicks are all it takes to cancel a lost key card and issue a replacement. Real-time and future-proofed Security staff at The Camp ensure only authorised users enter offices where expensive video projectors and screens are stored. Their TIL integration enables real-time management of the whole site, with specific profiles created to segment individuals who need fine-grained access to specific areas. “Online mode is very important because (access) rights are very often updated for the constantly shifting campus population,” explains Benjamin Ciotto, adding “We can also program access to defined time slots, which is essential when we welcome 200 people for an all-day meeting, for example.” Aperio product ecosystem’s performance Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos Aperio technology also met The Camp’s need for an aesthetically pleasing, wireless solution. They did not want to compromise their interior or exterior design. The Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos. Because Aperio devices are wireless and battery-powered, they are much more energy efficient than traditional wired locking systems, which require an “always-on” mains connection. Multiple Aperio devices Multiple Aperio devices have independently assessed Environmental Product Declarations (EPDs). These detail the footprint of each device through its full life cycle, from production to disposal. “Aperio is a real comfort of use,” Benjamin Ciotto concludes. “And we handle the easy maintenance for ourselves.”
Managing access to and around Helsinki Airport is a complex task. Around 15,000 people work there daily pre-pandemic passenger numbers hovered around 60,000 to 70,000. Challenges faced Only authorised people should have access to many areas at an airport. The management of movement — by passengers, staff, and contractors— is critical to Finavia’s mission to deliver an efficient service. They sought new access solutions to help. Finavia staff and customer safety is paramount. In addition, every new access control device must: Facilitate the move to keyless security at the airport, which aims to enhance user convenience. Offer compatibility so Finavia can secure all types of openings, from doors and cabinets to fences and cargo. Integrate seamlessly with the existing access control system and software used at Helsinki Airport. Meet essential requirements for securing such a sensitive site: safety, functionality, durability and usability. Solution With Aperio H100 battery-powered handles, all types of airport doors are connected Partnering with ASSA ABLOY gave Finavia a vast choice of solutions to meet its complex security needs. With Aperio H100 battery-powered handles, all types of airport doors are connected to their access control system. This Aperio solution with inbuilt RFID capability was easy to install without the cabling that traditional devices require. “We see in real-time who will open the lock and when, and we can modify and grant access rights, remotely,” explains Kari Mäkinen. Programmable, secure ID cards Authorised building users come and go with programmable, secure ID cards. It’s much more convenient than a mechanical key, “The access cards of both Finavia personnel and staff of other companies are easily programmed with necessary access rights,” he adds. “When employees change, their access is disabled. Or if the card gets lost, it can be completely removed from the system. With mechanical keys, that process is much harder.” Durability, security of supply, and usability Multiple compatible ASSA ABLOY solutions are deployed alongside wireless Aperio and CLIQ door devices. Keyless, mobile-operated padlocks secure fencing and cargo. An antimicrobial coating on door handles helps to prevent germ spread and reassures staff. The availability of all these solutions from a single manufacturer helped Finavia to create a unified, integrated system at Helsinki Airport. “Safety, functionality, durability, security of supply, and usability were the reasons we chose the ASSA ABLOY solution,” said Kari Mäkinen, Senior Access Control Specialist at Helsinki Airport.
Opened to mark the 100th anniversary of Bauhaus’ founding, the Bauhaus Museum Dessau is a comprehensive public presentation of the Bauhaus Dessau Foundation collection. On show for the very first time, this valuable collection includes around 49,000 catalogued exhibits and is the second-largest Bauhaus collection in the world. Transparency and simplicity Located in the centre of the city, the museum is a building within a building – a suspended concrete structure inside a glass shell. Its architecture is characterised by transparency and simplicity in both concept and aesthetics. The glass façade reflects the surroundings to different degrees or can be transparent, depending on lighting conditions. An intelligent digital key system It should fit unobtrusively within the building's sophisticated architectural concept Requirements for an intelligent digital key system in the museum were set out in advance. The chosen solution must enable the simplest possible management of access authorisations. It should also fit unobtrusively within the building's sophisticated architectural concept. eCLIQ programmable digital key As in the Bauhaus main building and master houses, the Bauhaus Foundation chose a proven system: ASSA ABLOY’s eCLIQ programmable digital key solution. “The building has an increasingly digital future,” says David Moser, SVP and Head of Digital Access Solutions at ASSA ABLOY Opening Solutions EMEIA. “Choosing a digital solution like eCLIQ, rather than mechanical access, can help organisations to work smarter and collaborate better.” Benefits of digital access: security, convenience, reliability An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry “The electromechanical CLIQ master key system has already proven itself extremely well in the Bauhaus main building and the master houses in Dessau,” explains Uwe Becker, Managing Director of Becker Sicherheitstechnik GmbH, the museum’s security partner on the project. The eCLIQ system is a fully digital version of the CLIQ electromechanical key-operated solution. An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry through doors and much more. Convenient and robust solution Robust, durable cylinders and padlocks with eCLIQ technology can protect lifts, server racks, furniture, gates, mailboxes, cabinets, and more with the same level of control as sensitive doors. Every key has an integrated chip, which makes it unique. As a result, keys may be programmed individually to meet specific needs and access permissions. For keyholders, it’s a convenient solution. Versatility and security benefits The versatility and security benefits of eCLIQ are demonstrated whenever a key is lost. Each key’s access authorisations can be removed individually by reprogramming the cylinders. For greater flexibility, eCLIQ also enables access authorisations to be issued on a time-limited basis, which simplifies the management of external service providers such as maintenance contractors and cleaners. “Digitalisation helps all kinds of organisations to boost their site security and makes everyday access more convenient for everyone – employees, visitors, and contractors,” adds David Moser. Aesthetics and the switch to digital All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design. They blend seamlessly with the varied installation situations of different doors and with the overall building concept in Dessau. A standard battery inside each key powers the eCLIQ cylinder and encrypts the data transfer between the lock, key, and system. With eCLIQ, there is no need to wire cylinders or doors, which leaves building designs intact. Digital transition “ASSA ABLOY’s innovative access solutions can help you digitalise and truly future-proof access at almost any kind of site or building,” says David Moser. “Our vast range of reliable, convenient solutions showcase the value of the digital transition and can be tailored to meet any organisation’s needs or goals.”
There is an older housing estate located in Nagodziców 6-18, Poland with 3 entrance gates and 105 apartments. The investor wants to retrofit the property to improve the community safety and elevate residents’ smart living experience. One of the main challenges in this retrofit is managing the wiring. How can the project minimise disruption to the building’s occupants and reduce the impact on residents’ daily activities? Additionally, how can the costs be kept down to make the retrofit more economically attractive? The Solution Solution Highlights: No Wiring No Indoor Units Fast, Cost-Saving Retrofits Future-Proof Intercom Solution Solution Benefits: No Indoor Units, Cost-effectiveness: DNAKE cloud-based intercom services eliminate the need for expensive hardware infrastructure and maintenance costs associated with traditional intercom systems. There is no need to invest in indoor units or wiring installations. Instead, residents can pay for a subscription-based service, which is often more affordable and predictable. No Wiring, Ease of Deployment: Setting up DNAKE cloud-based intercom service is relatively easier and quicker, when compared to traditional systems. There’s no need for extensive wiring or complicated installations. Residents can connect to the intercom service using their smartphones, making it more convenient and accessible. Easy and Multiple Access Ways: In addition to facial recognition, PIN code, and IC/ID card, there are also multiple app-based access methods available, including calling & app unlocking, QR code, temp key and Bluetooth. Residence can manage access from anywhere at any time.
Soyak Olympiakent in Turkey comprises thousands of apartments that prioritise 'Quality in Life.' It offers a quality and safe living experience, featuring a natural environment, sports facilities, swimming pools, ample parking areas, and a 24-hour private security system supported by an IP video intercom system. The Solution Solution Highlights: Great scalability in large residential apartments Remote and easy mobile access Real-time video and audio communication Emergency alerts Solution Benefits: DNAKE smart intercoms have been installed in 4 Blocks, covering a total of 1,948 apartments. Each entry point features DNAKE S215 4.3” SIP video door stations for secure access. Residents can open doors for visitors not only through the 280M-S8 indoor monitor, typically installed in every apartment, but also via the Smart Pro mobile application, accessible anywhere and anytime. The master station 902C-A in the guard room facilitates real-time communication, enabling guards to receive updates about security events or emergencies immediately. It can connect multiple zones, allowing for better monitoring and response across the premises, thereby enhancing overall safety and security.
The building, constructed in 2005, consists of three 12-storey towers with a total of 309 residential units. Residents have been experiencing issues with noise and unclear sound, which hinder effective communication and lead to frustration. Additionally, there is an increased need for remote unlocking capabilities. The existing 2-wire system, which supports only basic intercom functions, fails to meet the current needs of the residents. The Solution Solution highlights Easy Intercom Retrofitting with Existing Cables Tenant’s Own Choice on Answering Units Solution benefits For installer: DNAKE 2-wire IP intercom solution leverages existing wiring, which allows for a quicker and more efficient installation process. This solution helps avoid the costs associated with new cabling and extensive rewiring, keeping project costs down and making the retrofit more economically attractive. For property manager: The Central Management System (CMS) is an on-premises software solution for managing video intercom systems via the LAN, which has greatly improved the efficiency of property managers. Additionally, with the 902C-A master station, property managers can receive security alarms to take immediate action, and remotely unlock doors for visitors. For resident: Residents can choose their preferred answering unit based on their needs. Options include Linux-based or Android-based indoor monitors, audio-only indoor monitors, or even app-based services without a physical indoor monitor. With DNAKE's cloud service, residents can unlock doors from anywhere, at any time.
As a provider of future-oriented business education, The Camp sought an access control solution as forward-thinking as their courses. Their campus site near Aix-en-Provence is diverse, with offices, event spaces, kitchens and two accommodation blocks totalling 170 units. The Camp must remain open around the clock, all week, while maintaining security for staff and visitors. Aperio wireless locks Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks Aperio provided locking devices tailored to every door type — interior and exterior. So far, The Camp has integrated 221 Aperio Wireless Escutcheons, 42 Aperio Wireless Cylinders and 10 Aperio Wireless Handles within a TIL Technologies security system. Integrated online with the central system and controlled from the same interface, these Aperio devices effortlessly handle daily staff traffic of around 250 people. Meeting rooms, server rooms, living spaces and kitchens are secured with Aperio wireless locks. Aperio visitor access system Up to 2,000 external visitors arrive on-site when The Camp stages an event — and each must also have credentials issued and access filtered through the site. Aperio makes it straightforward to enable visitor access. “Many credentials get lost and Aperio enables us to handle this efficiently,” says Benjamin Ciotto, Head of Information Technology at The Camp. A few clicks are all it takes to cancel a lost key card and issue a replacement. Real-time and future-proofed Security staff at The Camp ensure only authorised users enter offices where expensive video projectors and screens are stored. Their TIL integration enables real-time management of the whole site, with specific profiles created to segment individuals who need fine-grained access to specific areas. “Online mode is very important because (access) rights are very often updated for the constantly shifting campus population,” explains Benjamin Ciotto, adding “We can also program access to defined time slots, which is essential when we welcome 200 people for an all-day meeting, for example.” Aperio product ecosystem’s performance Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos Aperio technology also met The Camp’s need for an aesthetically pleasing, wireless solution. They did not want to compromise their interior or exterior design. The Aperio product ecosystem’s sustainability performance also fits The Camp’s ethos. Because Aperio devices are wireless and battery-powered, they are much more energy efficient than traditional wired locking systems, which require an “always-on” mains connection. Multiple Aperio devices Multiple Aperio devices have independently assessed Environmental Product Declarations (EPDs). These detail the footprint of each device through its full life cycle, from production to disposal. “Aperio is a real comfort of use,” Benjamin Ciotto concludes. “And we handle the easy maintenance for ourselves.”
Managing access to and around Helsinki Airport is a complex task. Around 15,000 people work there daily pre-pandemic passenger numbers hovered around 60,000 to 70,000. Challenges faced Only authorised people should have access to many areas at an airport. The management of movement — by passengers, staff, and contractors— is critical to Finavia’s mission to deliver an efficient service. They sought new access solutions to help. Finavia staff and customer safety is paramount. In addition, every new access control device must: Facilitate the move to keyless security at the airport, which aims to enhance user convenience. Offer compatibility so Finavia can secure all types of openings, from doors and cabinets to fences and cargo. Integrate seamlessly with the existing access control system and software used at Helsinki Airport. Meet essential requirements for securing such a sensitive site: safety, functionality, durability and usability. Solution With Aperio H100 battery-powered handles, all types of airport doors are connected Partnering with ASSA ABLOY gave Finavia a vast choice of solutions to meet its complex security needs. With Aperio H100 battery-powered handles, all types of airport doors are connected to their access control system. This Aperio solution with inbuilt RFID capability was easy to install without the cabling that traditional devices require. “We see in real-time who will open the lock and when, and we can modify and grant access rights, remotely,” explains Kari Mäkinen. Programmable, secure ID cards Authorised building users come and go with programmable, secure ID cards. It’s much more convenient than a mechanical key, “The access cards of both Finavia personnel and staff of other companies are easily programmed with necessary access rights,” he adds. “When employees change, their access is disabled. Or if the card gets lost, it can be completely removed from the system. With mechanical keys, that process is much harder.” Durability, security of supply, and usability Multiple compatible ASSA ABLOY solutions are deployed alongside wireless Aperio and CLIQ door devices. Keyless, mobile-operated padlocks secure fencing and cargo. An antimicrobial coating on door handles helps to prevent germ spread and reassures staff. The availability of all these solutions from a single manufacturer helped Finavia to create a unified, integrated system at Helsinki Airport. “Safety, functionality, durability, security of supply, and usability were the reasons we chose the ASSA ABLOY solution,” said Kari Mäkinen, Senior Access Control Specialist at Helsinki Airport.
Opened to mark the 100th anniversary of Bauhaus’ founding, the Bauhaus Museum Dessau is a comprehensive public presentation of the Bauhaus Dessau Foundation collection. On show for the very first time, this valuable collection includes around 49,000 catalogued exhibits and is the second-largest Bauhaus collection in the world. Transparency and simplicity Located in the centre of the city, the museum is a building within a building – a suspended concrete structure inside a glass shell. Its architecture is characterised by transparency and simplicity in both concept and aesthetics. The glass façade reflects the surroundings to different degrees or can be transparent, depending on lighting conditions. An intelligent digital key system It should fit unobtrusively within the building's sophisticated architectural concept Requirements for an intelligent digital key system in the museum were set out in advance. The chosen solution must enable the simplest possible management of access authorisations. It should also fit unobtrusively within the building's sophisticated architectural concept. eCLIQ programmable digital key As in the Bauhaus main building and master houses, the Bauhaus Foundation chose a proven system: ASSA ABLOY’s eCLIQ programmable digital key solution. “The building has an increasingly digital future,” says David Moser, SVP and Head of Digital Access Solutions at ASSA ABLOY Opening Solutions EMEIA. “Choosing a digital solution like eCLIQ, rather than mechanical access, can help organisations to work smarter and collaborate better.” Benefits of digital access: security, convenience, reliability An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry “The electromechanical CLIQ master key system has already proven itself extremely well in the Bauhaus main building and the master houses in Dessau,” explains Uwe Becker, Managing Director of Becker Sicherheitstechnik GmbH, the museum’s security partner on the project. The eCLIQ system is a fully digital version of the CLIQ electromechanical key-operated solution. An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry through doors and much more. Convenient and robust solution Robust, durable cylinders and padlocks with eCLIQ technology can protect lifts, server racks, furniture, gates, mailboxes, cabinets, and more with the same level of control as sensitive doors. Every key has an integrated chip, which makes it unique. As a result, keys may be programmed individually to meet specific needs and access permissions. For keyholders, it’s a convenient solution. Versatility and security benefits The versatility and security benefits of eCLIQ are demonstrated whenever a key is lost. Each key’s access authorisations can be removed individually by reprogramming the cylinders. For greater flexibility, eCLIQ also enables access authorisations to be issued on a time-limited basis, which simplifies the management of external service providers such as maintenance contractors and cleaners. “Digitalisation helps all kinds of organisations to boost their site security and makes everyday access more convenient for everyone – employees, visitors, and contractors,” adds David Moser. Aesthetics and the switch to digital All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design. They blend seamlessly with the varied installation situations of different doors and with the overall building concept in Dessau. A standard battery inside each key powers the eCLIQ cylinder and encrypts the data transfer between the lock, key, and system. With eCLIQ, there is no need to wire cylinders or doors, which leaves building designs intact. Digital transition “ASSA ABLOY’s innovative access solutions can help you digitalise and truly future-proof access at almost any kind of site or building,” says David Moser. “Our vast range of reliable, convenient solutions showcase the value of the digital transition and can be tailored to meet any organisation’s needs or goals.”
There is an older housing estate located in Nagodziców 6-18, Poland with 3 entrance gates and 105 apartments. The investor wants to retrofit the property to improve the community safety and elevate residents’ smart living experience. One of the main challenges in this retrofit is managing the wiring. How can the project minimise disruption to the building’s occupants and reduce the impact on residents’ daily activities? Additionally, how can the costs be kept down to make the retrofit more economically attractive? The Solution Solution Highlights: No Wiring No Indoor Units Fast, Cost-Saving Retrofits Future-Proof Intercom Solution Solution Benefits: No Indoor Units, Cost-effectiveness: DNAKE cloud-based intercom services eliminate the need for expensive hardware infrastructure and maintenance costs associated with traditional intercom systems. There is no need to invest in indoor units or wiring installations. Instead, residents can pay for a subscription-based service, which is often more affordable and predictable. No Wiring, Ease of Deployment: Setting up DNAKE cloud-based intercom service is relatively easier and quicker, when compared to traditional systems. There’s no need for extensive wiring or complicated installations. Residents can connect to the intercom service using their smartphones, making it more convenient and accessible. Easy and Multiple Access Ways: In addition to facial recognition, PIN code, and IC/ID card, there are also multiple app-based access methods available, including calling & app unlocking, QR code, temp key and Bluetooth. Residence can manage access from anywhere at any time.


Products


Round table discussion
The design of buildings encompasses many elements, from the practical to the aesthetic. Well-designed buildings should be functional, and they can also be beautiful and inspiring. But can security systems and building design coexist and complement each other? We asked this week’s Expert Panel Roundtable: How does building design impact physical security systems -- and vice versa?
Frictionless systems provide access to a building without interfering at all with a user’s entry experience. Frictionless access means you can automatically pass through a gate without showing a credential or otherwise engaging, and with the system recognising who you are and allowing you to pass. In true frictionless access, everything works seamlessly, with unauthorised people obviously barred. But how close are we to realising frictionless access control? We asked this week’s Expert Panel Roundtable: Is frictionless access control a reality or an empty promise?
There is safety in numbers, or so the expression goes. Generally speaking, several employees working together tend to be safer than a single employee working alone. Even so, some environments require that workers complete their jobs alone, thus presenting a unique combination of security vulnerabilities. The U.S. Occupational Safety and Health Administration (OSHA) defines a lone worker as “an employee working alone, such as in a confined space or isolated location.” We asked this week’s Expert Panel Roundtable: How can security technologies help to protect "lone workers?"
White papers

The truth behind 9 mobile access myths
Download
Multi-residential access management and security
Download
Boost efficiency and streamline security with integrated access control
Download
AI in security solution
Download
Managing security in the age of boundaryless working
Download
The top 4 reasons to upgrade physical security with the Cloud
Download
Access control: The enterprise buyer's guide
Download
Effectively branding a multifamily property
Download
The ultimate guide to mastering key control
Download
Physical access control
Download
The key to unlocking K12 school safety grants
Download
The 2024 state of physical access trend report
Download
The security challenges of data centers
Download
Access control system planning phase 2
Download
Access control system planning phase 1
Download
The truth behind 9 mobile access myths
Download
Multi-residential access management and security
Download
Boost efficiency and streamline security with integrated access control
Download
AI in security solution
Download
Managing security in the age of boundaryless working
Download
The top 4 reasons to upgrade physical security with the Cloud
Download
Access control: The enterprise buyer's guide
Download
Effectively branding a multifamily property
Download
The ultimate guide to mastering key control
Download
Physical access control
Download
The key to unlocking K12 school safety grants
Download
The 2024 state of physical access trend report
Download
The security challenges of data centers
Download
Access control system planning phase 2
Download
Access control system planning phase 1
Download
The truth behind 9 mobile access myths
Download

Videos
Door access control: Manufacturers & Suppliers
- Aiphone Door access control
- Trimec Door access control
- Alpro Door access control
- Software House Door access control
- Vanderbilt Door access control
- ASSA ABLOY - Aperio® Door access control
- HID Door access control
- Bosch Door access control
- Honeywell Security Door access control
- CyberLock Door access control
- CDVI UK Door access control
- Paxton Access Door access control
- TESA Door access control
- Adams Rite Door access control
- Magnetic Solutions Door access control
- CLIQ - ASSA ABLOY Door access control
- SALTO Door access control
- Codelocks Door access control
- CEM Door access control
- Deedlock Door access control

The ultimate guide to mastering key control
Download
Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download