Digital video surveillance
Digitalising access brings many benefits, but greater knowledge is needed when it comes to making the right long-term decision. As a pioneer in access solutions, ASSA ABLOY and its over 60 thousand employees worldwide work every day towards a safer and more open world. ASSA ABLOY series of videos In a new series of videos, experts in various specialisms within ASSA ABLOY share their expertise on digital access, including the complexities to overcome and the range of benefits for those who get...
System Surveyor has launched its free online System Surveyor Certification Program, available 24/7 for system integrators, security and IoT professionals. The program helps users master the company's site survey and system design software and create accurate survey layouts for proposals, documentation and bill of material reports. Visual collaboration simplified "Our video-based Certification Program helps our software users to become more proficient with site surveys and system design," said...
HID, pioneer in trusted identity and access management solutions, announced the launch of HID Integration Service, a platform that integrates physical security, cybersecurity and digital identity management. This integration platform-as-a-service (IPaaS) was designed to empower application developers, solution integrators and software vendors to seamlessly and rapidly integrate essential physical security solutions, streamlining processes and enhancing system interoperability. Physical securit...
Everon, a pioneer security integrator and premier provider of commercial security, fire and life safety solutions in the U.S. Announced that David Charney has joined the team as Sr. Vice President, Video Command Center. Expert in security tech With nearly 20 years of industry experience, Charney has established himself as a pioneer of innovation in cutting edge spaces. He has held key executive roles, including President, Chief Operating Officer, and most recently Chief Customer Officer for...
Effective collaboration between security operators, teams, and other departments is essential for the smooth functioning of any organisation. However, as organisations grow in complexity, it becomes increasingly challenging for teams to coordinate. Factors such as staffing shortages, high turnover rates, and outdated collaboration tools exacerbate these challenges. Streamlining security operations These solutions enhance communication, boosts productivity, and improves overall operation...
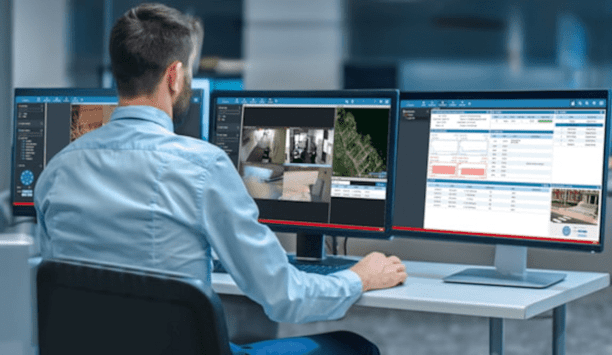
AMAG Technology announces Symmetry CompleteView Video Management 7.5, the latest software update to its video management system (VMS) platform. This version enhances operator experiences and introduces significant new enterprise capabilities including the integration of Iron Yun’s Vaidio® AI Video Analytics. Optimised monitoring The integration of Vaidio® AI Video Analytics supports both real-time monitoring and forensic investigationsThe integration of Vaidio® A...
News
Hosted America, a pioneering fibre network operator, has announced a groundbreaking partnership with KelTech IoE to implement the innovative LOC platform, making Hosted America the first fiber provider in the United States to utilise this advanced smart network technology. The LOC platform, with its AI-driven capabilities, will enable Hosted America to optimise network performance, streamline operations and future-proof infrastructure for long-term scalability. KelTech IoE's LOC platform Hosted America will gain unparalleled precision in managing fiber assets via NFC-enabled smart tagging Through KelTech IoE's LOC platform, Hosted America will gain unparalleled precision in managing fiber assets via NFC-enabled smart tagging. The platform provides real-time data on network assets, ensuring enhanced visibility, operational efficiency and seamless network maintenance. This strategic move positions Hosted America as the most intelligent, operationally efficient and sustainable fiber-to-the-home (FTTH) network in the country. Partnership with KelTech IoE "This partnership with KelTech IoE marks a transformative step for Hosted America," said Philip Watkins, chief executive officer of Hosted America. "Our commitment to building a state-of-the-art fiber network goes beyond connectivity – we are creating an infrastructure that is sustainable, intelligent and designed for the future. With KelTech IoE's LOC platform, we are ensuring that our network is managed with unparalleled precision, security and operational efficiency." Next-generation FTTH technology LOC agreement represents a significant milestone for KelTech IoE, valued at $21 million over the five years As part of this collaboration, Hosted America is set to connect 1 million homes across underserved communities in the U.S. with next-generation FTTH technology. Additionally, the LOC agreement represents a significant milestone for KelTech IoE, valued at $21 million over the next five years. "We are proud to partner with Hosted America in their mission to connect communities and create a more inclusive digital future," said Mark Kellett, chief executive officer of KelTech IoE. "The adoption of our LOC platform will empower Hosted America to build a fiber network that sets the benchmark for intelligence, sustainability and operational excellence." Industry standards for broadband infrastructure By integrating the LOC platform, Hosted America is not only reducing inefficiencies but also minimising environmental impact while maximising network uptime. This ensures a seamless and resilient broadband experience for households and businesses across the country. With this strategic partnership, Hosted America is poised to set new industry standards for broadband infrastructure, reinforcing its commitment to delivering strong, reliable and future-ready fiber networks nationwide.
Seamless connectivity between CLIQ Web Manager (CWM) and the braXos Steward platform gives organisations’ access management even greater security, flexibility and functionality. This innovative integration helps security managers work smarter, save time, and seamlessly extend the reach of their existing access system with wire-free CLIQ digital and electromechanical cylinders. CLIQ digital access with HR The CLIQ Connector feeds a secure bi-directional link between CWM and access systems The CLIQ Connector, now part of the braXos Steward connector library, provides a secure bi-directional link between CWM and almost 100 different access management systems. It can also connect CLIQ digital access with HR and building management solutions, to help businesses enjoy an even greater ROI from digitalising their internal systems and software. New CLIQ Connector The new CLIQ Connector enables creation and deletion of users within CWM, based on actions performed in the access management system. Users unlock CLIQ-secured openings thanks to access profile mapping between the system and CWM. Administrators can transfer audit trails from CWM directly to braXos Steward and, where supported, on to the access control system. Enhance security with CLIQ and braXos Steward The powerful new integration puts access at the heart of an organisation’s digital future This powerful new integration puts access at the heart of an organisation’s digital future. The connector helps facility managers consult and control a range of complementary systems from one place. They handle daily tasks directly in their familiar system interface – adding and removing users, as well as assigning existing users with new or revised access profiles. Security administrators save time and reduce manual errors because actions performed in the main access control system are mirrored in CLIQ Web Manager. They can quickly view individual audit trails within braXos Steward or their system, in real time if required. CLIQ key-based digital access solution This integration enables businesses currently running almost 100 different systems to enhance or extend their security with the CLIQ key-based digital access solution, which offers a wide range of cable-free cylinders. It is easy to integrate management of these smart keys with other digital and mobile credentials, further reducing the need for manual user data entry and re-entry. CLIQ, convenient smart key digital access CLIQ digital and electromechanical intelligent locking is relied upon to secure all kinds of sites CLIQ digital and electromechanical intelligent locking is relied upon to secure all kinds of locations, all over the world. Deploying CLIQ programmable smart keys and battery-free cylinders minimises risks from lost or stolen mechanical credentials – and saves businesses the hassle and expense of changing locks. Both electromechanical PROTEC² CLIQ and fully electronic eCLIQ devices offer a choice of more than 60 cylinder and padlock types to secure doors, cabinets, drawers, gates and much more. CLIQ Connect Bluetooth-enabled smart keys These reliable, durable devices enhance physical security and resistance against attack at almost any access point. CLIQ keys are convenient to update via wall, desk or portable programmers – or, with CLIQ Connect Bluetooth-enabled smart keys, via the CLIQ Connect mobile app.
Colt Technology Services (Colt), the digital infrastructure company, published a white paper entitled ‘Supporting AI in the UK: a White Paper to government’ which outlines key steps to unlock AI’s potential as a growth driver. The paper, authored by Colt’s CEO Keri Gilder in conjunction with EY, highlights the transformative opportunities presented by AI and offers actionable steps for the UK to harness AI’s power and potential. AI ecosystem The UK Government can bear outcomes that will gird the AI ecosystem, promote adoption across sectors The document also outlines the risks presented by a failure to act fast, suggesting the UK could be relegated to a ‘secondary player in the global economy’. By facilitating critical infrastructure upgrades, fostering a supportive regulatory environment, leveraging regional strengths and cultivating a highly skilled workforce, the UK Government can deliver outcomes that will strengthen the AI ecosystem, promote adoption across sectors and position the UK as a global innovation pioneer without the need to negatively impact public funding, Colt believes. Fundamental to the AI economy As a trusted digital infrastructure pioneer, Colt’s vantage point across the global technology industry - alongside its track-record in building secure, sustainable, next-generation fibre networks which are fundamental to the AI economy - leaves it well positioned to share experience and insight. Author and CEO Keri Gilder has an engineering background and is one of the most recognised and respected pioneers in the international telecoms world. Colt paper outlines four ways The Colt paper outlines four ways it believes the government should act to help reposition the UK as an AI superpower: Shape a supportive environment: establish robust, pro-innovation regulation and a streamlined planning processes to create a stable policy environment for AI Facilitate cross-sector coordination: act as a unifying force by harmonising policies, identifying synergies and addressing varying sectoral requirements Maximise strategic leadership and vision: champion AI adoption, identify sectoral opportunities, and showcase public sector best practices to build confidence in AI Enable flexible funding support: leverage fiscal tools, targeted R&D funding, and flexible mechanisms to unlock private investment and drive innovation UK’s socioeconomic growth Commenting on the paper, Keri said, “AI has the potential to transform the UK’s socioeconomic growth – to drive lasting change which brings together public and private investment, talent and insight to improve lives and protect the environment." "The UK government’s AI Opportunities Plan is a significant step forward in reaching this potential with clear and decisive measures, but we need to see this plan prioritised and accelerated. We need to keep the question of sustainability and power consumption high on the agenda and we must make sure the plan solves rather than reinforces digital exclusion.” Five of the 50 recommendations Keri continued, “Our goal behind this paper is to share the deep insights and experience we’ve gained as a vital part of the UK’s digital ecosystem, and to encourage conversations which explore ways the UK can capitalise on the AI revolution and drive remarkable, lasting change.” The paper responds directly to five of the 50 recommendations presented to the UK government by the Prime Minister’s AI Opportunities Advisor, Matt Clifford, which have been integrated into the AI Opportunities Action Plan announced in January. These recommendations include: A response to Recommendation 1: Set out, within 6 months, a long-term plan for the UK’s AI infrastructure needs, backed by a 10-year investment commitment. As the largest business-to-business fibre infrastructure provider in Europe, Colt has unrivalled experience building the kinds of digital infrastructure required to unlock AI’s potential in the UK. To turbocharge this, Colt calls for a streamlined planning process for critical AI infrastructure, while offering the Government its knowledge and expertise to advise on the digital connectivity deployment and data centre modernisation needed to safeguard the UK’s competitive advantage in the global AI race. A response to Recommendation 4: Establish AI Growth Zones (AIGZs) to accelerate the buildout of AI data centres. With a footprint of connected data centres across Europe and Asia, Colt has a comprehensive view of the optimal sites and conditions for digital infrastructure installation. Colt strongly advocates for strategically locating the AIGZs in regions rich in renewable energy, robust communications infrastructure and with a strong potential for regional economic growth. Leveraging its expertise, Colt can play a pivotal role in helping identify and develop AIGZs in places that will attract further private investment into the UK. A response to Recommendation 5: Mitigate the sustainability and security risks of AI infrastructure, while positioning the UK to take advantage of opportunities to provide solutions. Colt is on a journey to build a leaner, more energy-efficient global network. With its expertise in modernising digital infrastructure and commitment to net-zero emissions, Colt is ideally positioned to help the Government explore a wide range of sustainability solutions for AI infrastructure, from reforming power-purchase agreements (PPAs), to identifying key energy efficiency investments, or capturing waste heat from data centres to serve district heating networks. A response to Recommendation 6: Agree international compute partnerships with like-minded countries to increase the types of compute capability available to researchers and catalyse research collaborations. Through its partnership with Lumen Technologies, Colt offers unmatched global connectivity via the world’s No.1 Autonomous System (AS). This advanced infrastructure, including high-capacity IP transit ports in the major European hubs, enables faster, more reliable access to the global networks needed to forge international compute partnerships and drive AI innovation through strengthened cross-border research collaborations.
Sumsub, a full-cycle verification platform, is launching its Reusable Digital Identity product suite. It will effectively mitigate repetitive verification and redundant Know Your Customer (KYC) checks that negatively impact user experience and conversion rates for businesses. The new offerings are set to reduce applicant onboarding times by 50% and boost conversion rates by 30%, on average. Identity multiple services All of the checks required for ensuring a compliant verification must still take place KYC is essential for security, fraud prevention and compliance. However, when users need to verify their identity repeatedly across multiple services – especially when seeking critical access to financial or transportation apps – it creates friction and frustration. This repetitive process often leads to high drop-off rates and less user interest, impacting both user experience and business conversion rates. At the same time, all of the checks required for ensuring a compliant verification must still take place. Sumsub compliance and security Sumsub is processing millions of identity checks weekly, and aggregated data analysis reveals that one in three applicants have verified previously with Sumsub, highlighting the recurring KYC issue. To address this, Sumsub has launched a combined product to help both individuals and firms alike avoid repetitive verification steps while ensuring full compliance and security. Reusable Digital Identity product Reusable Digital Identity product suite includes two products, Sumsub ID and Reusable KYC The Reusable Digital Identity product suite includes two products, Sumsub ID and Reusable KYC. Both of them enable end-users to skip cumbersome verification steps such as document uploads, while at the same time ensuring that all checks required for regulatory adherence for businesses still take place. Sumsub ID enables end-users to securely store and re-use their verified documents for multiple verifications across Sumsub client platforms, whereas Reusable KYC allows companies in the Sumsub ecosystem to agree to share applicants’ data upon receiving their consent. Reusable Digital Identity While each product has a unique approach to the same challenge, both of them further enhance customer experience while ensuring full compliance and adding an extra layer of security. By offering faster and more efficient ways to verify identities, Reusable Digital Identity is designed to help users avoid unnecessary document uploads and repetitive data input procedures–while, at the same time, speeding up applicant onboarding and enhancing conversion rates for companies. Redefining digital ID verification Reusable Digital Identity is designed to help users avoid unnecessary document uploads “With a decade of experience in the market, our vision remains clear – to provide global businesses digital identity checks with the speed and convenience of payments, without sacrificing on compliance and security”, comments Vyacheslav Zholudev, CTO and co-founder of Sumsub. “With Sumsub ID and Reusable KYC, we are redefining digital ID verification by helping businesses improve onboarding efficiency and also giving users full control over their documents and data, respectively. This marks a significant milestone in our mission to make identity verification faster, safer, and more reliable for everyone.” Key benefits of Sumsub Identity products Key benefits of Sumsub Reusable Digital Identity products for businesses are: Higher pass rates: businesses see up to 30% improvement in successful user verifications. Faster KYC processes: Sumsub ID reduces onboarding time by 50%, improving conversion rates. Full Compliance & Security: Both Reusable KYC and Sumsub ID are GDPR-compliant and built to enhance fraud prevention. Main benefits for users are: Seamless verification: individuals can breeze through KYC by re-using their documents from previous verifications with Sumsub. Full privacy and security of personal data stored or shared by third parties for verification purposes. Less time spent on getting access to the platforms and services people use, as both Sumsub ID and Reusable KYC make the onboarding process faster by eliminating redundant document uploads. How Sumsub reusable digital identity product suite works Sumsub ID allows applicants to onboard onto a platform within the Sumsub ecosystem, securely store their verified documents, and reuse them for future verifications across 4000+ companies which also use Sumsub; Reusable KYC enables companies to share users’ personal data with their explicit consent, ensuring quicker onboarding, which benefits companies and individuals alike. Sumsub ID is now available for anyone to sign up and benefit from seamless verification and onboarding across crypto, fintech, banking, e-commerce, traditional finance, security, regtech, and fraud prevention industries.
Blackline Safety Corp., a global pioneer in connected safety technology, announced it has been named to Fast Company’s prestigious list of the World’s Most Innovative Companies of 2025. The annual Fast Company ranking recognises companies making meaningful strides across industries through bold thinking and impactful innovation. Smarter solutions for safety Blackline earned its place on the list for transforming the way organisations protect their peopleThis year’s honourees include Waymo, Nvidia, and Kraft Heinz. Blackline earned its place on the list for transforming the way organisations protect their people—helping teams respond faster, prevent incidents, and make informed decisions through real-time safety data. “We’re proud to be recognised by Fast Company for leading the transformation of workplace safety, helping organisations protect their people with smarter, more reliable solutions,” said Blackline Safety CEO and Chair, Cody Slater. “Every day, there are over 160,000 families around the world whose family member goes to work in a hazardous environment and comes home safe at the end of the day – thanks to their employer choosing Blackline.” Safety redefined Blackline’s portfolio includes connected wearable devices, portable area monitors, and cloud-based software that work together to enable live monitoring, automatic incident alerts, and location-based insights. In 2024, the company expanded its offering with the launch of the EXO 8 area monitor, designed to provide rapid deployment and advanced gas and gamma detection in industrial and emergency response settings. Innovation trailblazers Fast Company’s World’s Most Innovative Companies list highlights organisations that are shaping the future of business through creativity, technology, and impact. The 2025 honourees include trailblazers redefining industries and setting new standards for progress and performance.
Delta, a pioneer in power management and a provider of IoT-based smart green solutions, is ushering a new era of smart manufacturing at NVIDIA GTC 2025 by showcasing its superior cyber-physical integration capabilities and its close collaboration with NVIDIA through an AI-based Smart Manufacturing Demo Line. The demonstration illustrates high-fidelity cyber-physical integration for essential processes in next-generation smart factories. Advanced digital twin technology Andy Liu, General Manager of Delta’s Industrial Automation Business Group, said, “At Delta, we have worked with NVIDIA to accelerate the development of smart manufacturing through seamless cyber-physical integration and advanced digital twin technology." "By leveraging NVIDIA Omniverse™, our interactive automated PC board assembly demo line shows how manufacturers can enhance flexibility, efficiency, and intelligence in their production lines. With Delta’s hardware and software industrial automation solutions, we are empowering businesses to embrace autonomous and data-driven manufacturing.” Key cyber-physical integration scenarios The demo presents five key high-fidelity cyber-physical integration scenarios The AI-based Smart Manufacturing Demo Line features Delta’s Collaborative Robot D-Bot Series, Omni® Inserter, and Integra® Modular Glue Dispensing machine, combined with Delta’s proprietary Line Manager platform and DIATwin digital twin system. By integrating the NVIDIA Omniverse™ simulation development platform, the demo presents five key high-fidelity cyber-physical integration scenarios: virtual new product introduction, automated recipe generation, automated line changeover and parameter adjustment, automatic collision avoidance, and synchronised cyber-physical operations. Key exhibits in Delta’s AI-based Smart Manufacturing Demo Line IIoT-based Line Manager Platform: Delta’s Line Manager is a comprehensive IIoT-based solution that enables equipment remote control, autonomous production, and data analytics, helping factories embrace distributed manufacturing and centralised management. Upon product recipe uploading, manufacturers can seamlessly switch between different processes while optimising parameters like route and speed to achieve automated mixed-model production. DIATwin Virtual Machine Development Platform: DIATwin is a smart design tool for machine makers, delivering advanced machine-level and line-level digital twin solutions, which integrates machine prototyping, process simulation, virtual commissioning, and parameter optimisation into one robust platform. With DIATwin, machine makers can accelerate time-to-market, cut down on machine downtime to optimise efficiency. Collaborative Robot D-Bot Series: Delta’s D-Bot Series supports high payloads up to 30 kg, featuring an IP66 rating and easy setup in less than one hour. It is integrated with NVIDIA Omniverse™ and Isaac Sim to bring enhanced simulation capabilities, which allow users to create high-fidelity digital twins, enabling virtual testing and optimisation of robot functions before deployment. The result is faster, more efficient design and operation, improving performance across various applications. Omni® Inserter: With a linear motor positioning system, the Omni Inserter delivers accurate, high-speed insertion of odd-form components, supporting a wide range of feeder types. It also comes with a host of smart AI-based features to boost insertion quality, such as applying best-fit algorithm to increase insertion success rate to >99.5%, and utilising AI+AOI vision algorithm to enhance image and improve pin positioning, reducing reject rate to <1%. Integra® Modular Glue Dispensing Machine: Delta’s advanced Integra® Modular Glue Dispensing Machine enhances production efficiency with DIATwin, which simulates scenarios for development evaluation. Boasting a modular design, it enables fast and flexible production line changeovers. With one-click auto-calibration and diverse valves for various glue dispensing applications, Integra® ensures precision, adaptability, and seamless automation. Future of smart manufacturing With a deep-rooted commitment to innovation, Delta continues to push the boundaries of smart manufacturing by integrating automation, AI, and digital twin technologies. Join them at NVIDIA GTC 2025 at booth #1023 or in the sessions, to witness how the innovations are shaping the future of smart manufacturing. The new power, cooling, and infrastructure solutions to enhance the performance and energy conservation of AI data centres will also be an integral part of the showcase.
Hosted America, a pioneering fibre network operator, has announced a groundbreaking partnership with KelTech IoE to implement the innovative LOC platform, making Hosted America the first fiber provider in the United States to utilise this advanced smart network technology. The LOC platform, with its AI-driven capabilities, will enable Hosted America to optimise network performance, streamline operations and future-proof infrastructure for long-term scalability. KelTech IoE's LOC platform Hosted America will gain unparalleled precision in managing fiber assets via NFC-enabled smart tagging Through KelTech IoE's LOC platform, Hosted America will gain unparalleled precision in managing fiber assets via NFC-enabled smart tagging. The platform provides real-time data on network assets, ensuring enhanced visibility, operational efficiency and seamless network maintenance. This strategic move positions Hosted America as the most intelligent, operationally efficient and sustainable fiber-to-the-home (FTTH) network in the country. Partnership with KelTech IoE "This partnership with KelTech IoE marks a transformative step for Hosted America," said Philip Watkins, chief executive officer of Hosted America. "Our commitment to building a state-of-the-art fiber network goes beyond connectivity – we are creating an infrastructure that is sustainable, intelligent and designed for the future. With KelTech IoE's LOC platform, we are ensuring that our network is managed with unparalleled precision, security and operational efficiency." Next-generation FTTH technology LOC agreement represents a significant milestone for KelTech IoE, valued at $21 million over the five years As part of this collaboration, Hosted America is set to connect 1 million homes across underserved communities in the U.S. with next-generation FTTH technology. Additionally, the LOC agreement represents a significant milestone for KelTech IoE, valued at $21 million over the next five years. "We are proud to partner with Hosted America in their mission to connect communities and create a more inclusive digital future," said Mark Kellett, chief executive officer of KelTech IoE. "The adoption of our LOC platform will empower Hosted America to build a fiber network that sets the benchmark for intelligence, sustainability and operational excellence." Industry standards for broadband infrastructure By integrating the LOC platform, Hosted America is not only reducing inefficiencies but also minimising environmental impact while maximising network uptime. This ensures a seamless and resilient broadband experience for households and businesses across the country. With this strategic partnership, Hosted America is poised to set new industry standards for broadband infrastructure, reinforcing its commitment to delivering strong, reliable and future-ready fiber networks nationwide.
Seamless connectivity between CLIQ Web Manager (CWM) and the braXos Steward platform gives organisations’ access management even greater security, flexibility and functionality. This innovative integration helps security managers work smarter, save time, and seamlessly extend the reach of their existing access system with wire-free CLIQ digital and electromechanical cylinders. CLIQ digital access with HR The CLIQ Connector feeds a secure bi-directional link between CWM and access systems The CLIQ Connector, now part of the braXos Steward connector library, provides a secure bi-directional link between CWM and almost 100 different access management systems. It can also connect CLIQ digital access with HR and building management solutions, to help businesses enjoy an even greater ROI from digitalising their internal systems and software. New CLIQ Connector The new CLIQ Connector enables creation and deletion of users within CWM, based on actions performed in the access management system. Users unlock CLIQ-secured openings thanks to access profile mapping between the system and CWM. Administrators can transfer audit trails from CWM directly to braXos Steward and, where supported, on to the access control system. Enhance security with CLIQ and braXos Steward The powerful new integration puts access at the heart of an organisation’s digital future This powerful new integration puts access at the heart of an organisation’s digital future. The connector helps facility managers consult and control a range of complementary systems from one place. They handle daily tasks directly in their familiar system interface – adding and removing users, as well as assigning existing users with new or revised access profiles. Security administrators save time and reduce manual errors because actions performed in the main access control system are mirrored in CLIQ Web Manager. They can quickly view individual audit trails within braXos Steward or their system, in real time if required. CLIQ key-based digital access solution This integration enables businesses currently running almost 100 different systems to enhance or extend their security with the CLIQ key-based digital access solution, which offers a wide range of cable-free cylinders. It is easy to integrate management of these smart keys with other digital and mobile credentials, further reducing the need for manual user data entry and re-entry. CLIQ, convenient smart key digital access CLIQ digital and electromechanical intelligent locking is relied upon to secure all kinds of sites CLIQ digital and electromechanical intelligent locking is relied upon to secure all kinds of locations, all over the world. Deploying CLIQ programmable smart keys and battery-free cylinders minimises risks from lost or stolen mechanical credentials – and saves businesses the hassle and expense of changing locks. Both electromechanical PROTEC² CLIQ and fully electronic eCLIQ devices offer a choice of more than 60 cylinder and padlock types to secure doors, cabinets, drawers, gates and much more. CLIQ Connect Bluetooth-enabled smart keys These reliable, durable devices enhance physical security and resistance against attack at almost any access point. CLIQ keys are convenient to update via wall, desk or portable programmers – or, with CLIQ Connect Bluetooth-enabled smart keys, via the CLIQ Connect mobile app.
Colt Technology Services (Colt), the digital infrastructure company, published a white paper entitled ‘Supporting AI in the UK: a White Paper to government’ which outlines key steps to unlock AI’s potential as a growth driver. The paper, authored by Colt’s CEO Keri Gilder in conjunction with EY, highlights the transformative opportunities presented by AI and offers actionable steps for the UK to harness AI’s power and potential. AI ecosystem The UK Government can bear outcomes that will gird the AI ecosystem, promote adoption across sectors The document also outlines the risks presented by a failure to act fast, suggesting the UK could be relegated to a ‘secondary player in the global economy’. By facilitating critical infrastructure upgrades, fostering a supportive regulatory environment, leveraging regional strengths and cultivating a highly skilled workforce, the UK Government can deliver outcomes that will strengthen the AI ecosystem, promote adoption across sectors and position the UK as a global innovation pioneer without the need to negatively impact public funding, Colt believes. Fundamental to the AI economy As a trusted digital infrastructure pioneer, Colt’s vantage point across the global technology industry - alongside its track-record in building secure, sustainable, next-generation fibre networks which are fundamental to the AI economy - leaves it well positioned to share experience and insight. Author and CEO Keri Gilder has an engineering background and is one of the most recognised and respected pioneers in the international telecoms world. Colt paper outlines four ways The Colt paper outlines four ways it believes the government should act to help reposition the UK as an AI superpower: Shape a supportive environment: establish robust, pro-innovation regulation and a streamlined planning processes to create a stable policy environment for AI Facilitate cross-sector coordination: act as a unifying force by harmonising policies, identifying synergies and addressing varying sectoral requirements Maximise strategic leadership and vision: champion AI adoption, identify sectoral opportunities, and showcase public sector best practices to build confidence in AI Enable flexible funding support: leverage fiscal tools, targeted R&D funding, and flexible mechanisms to unlock private investment and drive innovation UK’s socioeconomic growth Commenting on the paper, Keri said, “AI has the potential to transform the UK’s socioeconomic growth – to drive lasting change which brings together public and private investment, talent and insight to improve lives and protect the environment." "The UK government’s AI Opportunities Plan is a significant step forward in reaching this potential with clear and decisive measures, but we need to see this plan prioritised and accelerated. We need to keep the question of sustainability and power consumption high on the agenda and we must make sure the plan solves rather than reinforces digital exclusion.” Five of the 50 recommendations Keri continued, “Our goal behind this paper is to share the deep insights and experience we’ve gained as a vital part of the UK’s digital ecosystem, and to encourage conversations which explore ways the UK can capitalise on the AI revolution and drive remarkable, lasting change.” The paper responds directly to five of the 50 recommendations presented to the UK government by the Prime Minister’s AI Opportunities Advisor, Matt Clifford, which have been integrated into the AI Opportunities Action Plan announced in January. These recommendations include: A response to Recommendation 1: Set out, within 6 months, a long-term plan for the UK’s AI infrastructure needs, backed by a 10-year investment commitment. As the largest business-to-business fibre infrastructure provider in Europe, Colt has unrivalled experience building the kinds of digital infrastructure required to unlock AI’s potential in the UK. To turbocharge this, Colt calls for a streamlined planning process for critical AI infrastructure, while offering the Government its knowledge and expertise to advise on the digital connectivity deployment and data centre modernisation needed to safeguard the UK’s competitive advantage in the global AI race. A response to Recommendation 4: Establish AI Growth Zones (AIGZs) to accelerate the buildout of AI data centres. With a footprint of connected data centres across Europe and Asia, Colt has a comprehensive view of the optimal sites and conditions for digital infrastructure installation. Colt strongly advocates for strategically locating the AIGZs in regions rich in renewable energy, robust communications infrastructure and with a strong potential for regional economic growth. Leveraging its expertise, Colt can play a pivotal role in helping identify and develop AIGZs in places that will attract further private investment into the UK. A response to Recommendation 5: Mitigate the sustainability and security risks of AI infrastructure, while positioning the UK to take advantage of opportunities to provide solutions. Colt is on a journey to build a leaner, more energy-efficient global network. With its expertise in modernising digital infrastructure and commitment to net-zero emissions, Colt is ideally positioned to help the Government explore a wide range of sustainability solutions for AI infrastructure, from reforming power-purchase agreements (PPAs), to identifying key energy efficiency investments, or capturing waste heat from data centres to serve district heating networks. A response to Recommendation 6: Agree international compute partnerships with like-minded countries to increase the types of compute capability available to researchers and catalyse research collaborations. Through its partnership with Lumen Technologies, Colt offers unmatched global connectivity via the world’s No.1 Autonomous System (AS). This advanced infrastructure, including high-capacity IP transit ports in the major European hubs, enables faster, more reliable access to the global networks needed to forge international compute partnerships and drive AI innovation through strengthened cross-border research collaborations.
Sumsub, a full-cycle verification platform, is launching its Reusable Digital Identity product suite. It will effectively mitigate repetitive verification and redundant Know Your Customer (KYC) checks that negatively impact user experience and conversion rates for businesses. The new offerings are set to reduce applicant onboarding times by 50% and boost conversion rates by 30%, on average. Identity multiple services All of the checks required for ensuring a compliant verification must still take place KYC is essential for security, fraud prevention and compliance. However, when users need to verify their identity repeatedly across multiple services – especially when seeking critical access to financial or transportation apps – it creates friction and frustration. This repetitive process often leads to high drop-off rates and less user interest, impacting both user experience and business conversion rates. At the same time, all of the checks required for ensuring a compliant verification must still take place. Sumsub compliance and security Sumsub is processing millions of identity checks weekly, and aggregated data analysis reveals that one in three applicants have verified previously with Sumsub, highlighting the recurring KYC issue. To address this, Sumsub has launched a combined product to help both individuals and firms alike avoid repetitive verification steps while ensuring full compliance and security. Reusable Digital Identity product Reusable Digital Identity product suite includes two products, Sumsub ID and Reusable KYC The Reusable Digital Identity product suite includes two products, Sumsub ID and Reusable KYC. Both of them enable end-users to skip cumbersome verification steps such as document uploads, while at the same time ensuring that all checks required for regulatory adherence for businesses still take place. Sumsub ID enables end-users to securely store and re-use their verified documents for multiple verifications across Sumsub client platforms, whereas Reusable KYC allows companies in the Sumsub ecosystem to agree to share applicants’ data upon receiving their consent. Reusable Digital Identity While each product has a unique approach to the same challenge, both of them further enhance customer experience while ensuring full compliance and adding an extra layer of security. By offering faster and more efficient ways to verify identities, Reusable Digital Identity is designed to help users avoid unnecessary document uploads and repetitive data input procedures–while, at the same time, speeding up applicant onboarding and enhancing conversion rates for companies. Redefining digital ID verification Reusable Digital Identity is designed to help users avoid unnecessary document uploads “With a decade of experience in the market, our vision remains clear – to provide global businesses digital identity checks with the speed and convenience of payments, without sacrificing on compliance and security”, comments Vyacheslav Zholudev, CTO and co-founder of Sumsub. “With Sumsub ID and Reusable KYC, we are redefining digital ID verification by helping businesses improve onboarding efficiency and also giving users full control over their documents and data, respectively. This marks a significant milestone in our mission to make identity verification faster, safer, and more reliable for everyone.” Key benefits of Sumsub Identity products Key benefits of Sumsub Reusable Digital Identity products for businesses are: Higher pass rates: businesses see up to 30% improvement in successful user verifications. Faster KYC processes: Sumsub ID reduces onboarding time by 50%, improving conversion rates. Full Compliance & Security: Both Reusable KYC and Sumsub ID are GDPR-compliant and built to enhance fraud prevention. Main benefits for users are: Seamless verification: individuals can breeze through KYC by re-using their documents from previous verifications with Sumsub. Full privacy and security of personal data stored or shared by third parties for verification purposes. Less time spent on getting access to the platforms and services people use, as both Sumsub ID and Reusable KYC make the onboarding process faster by eliminating redundant document uploads. How Sumsub reusable digital identity product suite works Sumsub ID allows applicants to onboard onto a platform within the Sumsub ecosystem, securely store their verified documents, and reuse them for future verifications across 4000+ companies which also use Sumsub; Reusable KYC enables companies to share users’ personal data with their explicit consent, ensuring quicker onboarding, which benefits companies and individuals alike. Sumsub ID is now available for anyone to sign up and benefit from seamless verification and onboarding across crypto, fintech, banking, e-commerce, traditional finance, security, regtech, and fraud prevention industries.
Blackline Safety Corp., a global pioneer in connected safety technology, announced it has been named to Fast Company’s prestigious list of the World’s Most Innovative Companies of 2025. The annual Fast Company ranking recognises companies making meaningful strides across industries through bold thinking and impactful innovation. Smarter solutions for safety Blackline earned its place on the list for transforming the way organisations protect their peopleThis year’s honourees include Waymo, Nvidia, and Kraft Heinz. Blackline earned its place on the list for transforming the way organisations protect their people—helping teams respond faster, prevent incidents, and make informed decisions through real-time safety data. “We’re proud to be recognised by Fast Company for leading the transformation of workplace safety, helping organisations protect their people with smarter, more reliable solutions,” said Blackline Safety CEO and Chair, Cody Slater. “Every day, there are over 160,000 families around the world whose family member goes to work in a hazardous environment and comes home safe at the end of the day – thanks to their employer choosing Blackline.” Safety redefined Blackline’s portfolio includes connected wearable devices, portable area monitors, and cloud-based software that work together to enable live monitoring, automatic incident alerts, and location-based insights. In 2024, the company expanded its offering with the launch of the EXO 8 area monitor, designed to provide rapid deployment and advanced gas and gamma detection in industrial and emergency response settings. Innovation trailblazers Fast Company’s World’s Most Innovative Companies list highlights organisations that are shaping the future of business through creativity, technology, and impact. The 2025 honourees include trailblazers redefining industries and setting new standards for progress and performance.
Delta, a pioneer in power management and a provider of IoT-based smart green solutions, is ushering a new era of smart manufacturing at NVIDIA GTC 2025 by showcasing its superior cyber-physical integration capabilities and its close collaboration with NVIDIA through an AI-based Smart Manufacturing Demo Line. The demonstration illustrates high-fidelity cyber-physical integration for essential processes in next-generation smart factories. Advanced digital twin technology Andy Liu, General Manager of Delta’s Industrial Automation Business Group, said, “At Delta, we have worked with NVIDIA to accelerate the development of smart manufacturing through seamless cyber-physical integration and advanced digital twin technology." "By leveraging NVIDIA Omniverse™, our interactive automated PC board assembly demo line shows how manufacturers can enhance flexibility, efficiency, and intelligence in their production lines. With Delta’s hardware and software industrial automation solutions, we are empowering businesses to embrace autonomous and data-driven manufacturing.” Key cyber-physical integration scenarios The demo presents five key high-fidelity cyber-physical integration scenarios The AI-based Smart Manufacturing Demo Line features Delta’s Collaborative Robot D-Bot Series, Omni® Inserter, and Integra® Modular Glue Dispensing machine, combined with Delta’s proprietary Line Manager platform and DIATwin digital twin system. By integrating the NVIDIA Omniverse™ simulation development platform, the demo presents five key high-fidelity cyber-physical integration scenarios: virtual new product introduction, automated recipe generation, automated line changeover and parameter adjustment, automatic collision avoidance, and synchronised cyber-physical operations. Key exhibits in Delta’s AI-based Smart Manufacturing Demo Line IIoT-based Line Manager Platform: Delta’s Line Manager is a comprehensive IIoT-based solution that enables equipment remote control, autonomous production, and data analytics, helping factories embrace distributed manufacturing and centralised management. Upon product recipe uploading, manufacturers can seamlessly switch between different processes while optimising parameters like route and speed to achieve automated mixed-model production. DIATwin Virtual Machine Development Platform: DIATwin is a smart design tool for machine makers, delivering advanced machine-level and line-level digital twin solutions, which integrates machine prototyping, process simulation, virtual commissioning, and parameter optimisation into one robust platform. With DIATwin, machine makers can accelerate time-to-market, cut down on machine downtime to optimise efficiency. Collaborative Robot D-Bot Series: Delta’s D-Bot Series supports high payloads up to 30 kg, featuring an IP66 rating and easy setup in less than one hour. It is integrated with NVIDIA Omniverse™ and Isaac Sim to bring enhanced simulation capabilities, which allow users to create high-fidelity digital twins, enabling virtual testing and optimisation of robot functions before deployment. The result is faster, more efficient design and operation, improving performance across various applications. Omni® Inserter: With a linear motor positioning system, the Omni Inserter delivers accurate, high-speed insertion of odd-form components, supporting a wide range of feeder types. It also comes with a host of smart AI-based features to boost insertion quality, such as applying best-fit algorithm to increase insertion success rate to >99.5%, and utilising AI+AOI vision algorithm to enhance image and improve pin positioning, reducing reject rate to <1%. Integra® Modular Glue Dispensing Machine: Delta’s advanced Integra® Modular Glue Dispensing Machine enhances production efficiency with DIATwin, which simulates scenarios for development evaluation. Boasting a modular design, it enables fast and flexible production line changeovers. With one-click auto-calibration and diverse valves for various glue dispensing applications, Integra® ensures precision, adaptability, and seamless automation. Future of smart manufacturing With a deep-rooted commitment to innovation, Delta continues to push the boundaries of smart manufacturing by integrating automation, AI, and digital twin technologies. Join them at NVIDIA GTC 2025 at booth #1023 or in the sessions, to witness how the innovations are shaping the future of smart manufacturing. The new power, cooling, and infrastructure solutions to enhance the performance and energy conservation of AI data centres will also be an integral part of the showcase.


Expert commentary
Access control solutions will continue their evolution in 2025 as organisations assess and adapt to dynamic and increasingly dangerous threats. Trends to watch include the growing adoption of mobile access credentials and digital IDs, and the integration of digital and physical security and other technologies. Other ongoing trends include the integration of AI into access control solutions and the increasing adoption of contactless biometrics for enhanced convenience. New access control innovations As these trends gather momentum, they highlight the pivotal role access control systems play in combining security and convenience, every hour of every day. Organisations must strike the ideal balance between a secure environment and satisfying user experience if they are to meet increasingly vocal demands for both. Achieving this balance not only delivers the expected user experience but also delivers multi-layered threat protection while introducing exciting new access control innovations. Digital technologies and open standards Modern access control solutions deliver a faster pace of innovation and dramatically improved capabilities Modern access control solutions deliver a faster pace of innovation and dramatically improved capabilities as compared to what was possible in the past. The primary objective is no longer simply to secure places and assets so they are beyond the reach of the wrong people. Now it also must be as easy as possible for authorised individuals to enter a building or access digital assets. Mobile access credentials and digital IDs are increasingly a preferred solution for achieving this seamless and convenient access experience. Technology convergence is happening at a rapid pace and this convergence makes it possible to integrate digital and physical security with real-time location systems and other technologies. Together, these converged technologies provide multi-layered protection against both cyber and physical threats while also enabling valuable new capabilities. 2024 State of Physical Access Control Report As AI is increasingly incorporated into access-control solutions, we will see even more powerful ways to leverage access control data for analytics use cases. Almost 40% of respondents to our 2024 State of Physical Access Control Report said they were looking to do this. Equally consequential is the rise of fast, frictionless and easy contactless biometrics solutions in a wide range of applications including healthcare, where 32% of respondents to our recent 2024 State of Healthcare Security Report said their facilities have already implemented this technology for authentication. Looking at the broader marketplace, nearly one in four (23%) respondents to our 2024 State of Physical Access Control Report cited biometrics when asked to “name the top three trends shaping the wider access control industry in the near future.” Evolution of access control solutions As access control solutions become increasingly central to secure and convenient daily life, these and other trends will have an ongoing impact on all market sectors from healthcare and banking to the corporate real estate enterprise and business and college campuses. At the same time, those responsible for a facility’s digital and physical assets know that these trends – and security in general – will never be a static proposition. The only constant is change. Threats will never stop evolving, and those tasked with protecting organisations against these threats must never stand still. The evolution of access control solutions that we saw during 2024 will continue through 2025 and beyond, and organisations will need to remain thorough and vigilant as they address today’s ever-expanding attack surfaces and ever-evolving attack schemes.
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realise, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionising the overnight security business. Minimising criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilises a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimise the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is remote guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilises a combination of methods to effectively analyse potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyse the situation in real-time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command centre, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customised remote guarding When properly deployed, remote guarding systems are also customised to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional security shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A bounty of benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physical security systems Hospitals in particular have developed into multi-faceted spaces that house hundreds to thousands of patients, staff and visitors at any one time. In England for example, research has found in the three months leading to June 2023, an average of 44,626 people visited major hospital A&E departments each day, with over 16 million attendances typically recorded over the course of a year-not to mention an additional nine million logged at other minor units. For any building, this level of sustained footfall can request severe security difficulties For any building, this level of sustained footfall can invite severe security tests. With that, the need to deploy effective physical security systems in healthcare is clear. And so, as access control continues to become more readily adopted and new products enter the market, decision-makers are reminded to consider the requirements of their building, ensuring they select the solutions most suited to their settings and budget. Security controlled Patient safety will always remain the top priority in healthcare settings, and where matters of health and social care come into question, a diverse set of professional regulatory bodies are tasked with setting and maintaining high standards. When it comes to healthcare premises specifically, patient security and perimeter security often come hand in hand and are amongst the most pressing of challenges that decision-makers must face. To help address operational planning and potential design concerns in the NHS, the Health Building Note (HBN), provides general design guidance for healthcare buildings under HBN 00-01-citing the use of access control measures as a way of maintaining security and protecting the safety of patients, staff and visitors. Use of access control Hospital buildings control varied levels of access for a number of security purposes Hospital buildings, for example, must control varied levels of access for a number of operational and security purposes. Routine scenarios exist where vulnerable patients are under monitoring and thus refrained from exiting the premises for their own safety, while at the same time, permitted staff must be able to reach their patients and medicines when required. For this, the use of access control is key. Equally, access credentials can also help management teams keep track of those who may be entering or exiting rooms with equipment and pharmaceutical supplies, deterring any unwanted visitors and opportunists in the process. Incorporation of access control systems On a similar note, regulations have set a minimum standard for how personal data should be stored and managed in healthcare environments, giving decision-makers an added responsibility to regulate staff-controlled areas with patient medical records. While instances of personal data breaches are rare, healthcare facilities and professionals are at legal risk should confidential data be found misused or missing. As such, the incorporation of access control systems has become essential in keeping data storage areas secure, with intuitive online systems capable of permitting access to staff with the correct credentials while simultaneously tracking who has requested clearance at digital entry points. HBN guidance Healthcare experts are better fitted to control the sheer volume of people entering and exiting To function effectively, healthcare facilities must always be perceived as safe places by the people who reside within them, and as HBN guidance implies, a unified physical security system can help address key safety and security concerns while enhancing patient and staff experience. Opportunely, access control systems are more accessible and adaptable than ever and combine several technologies such as mechanical locks and automatic doors with electronic access credentials in the form of smartphone apps, badge readers and biometric scanners. By integrating these systems into the building’s existing infrastructure, healthcare professionals are better equipped to control the sheer volume of people entering and exiting the premises without impairing the general flow of movement and coordination around the facility. Better by design Despite the clear benefits offered to healthcare facilities, there are a number of considerations to be mindful of when choosing an access control solution. Poorly implemented systems can have an adverse effect on security and functionality - quickly costing healthcare organisations time and budget to rectify and replace the inadequate products that don’t meet the building’s requirements. For that reason, decision-makers and design teams are reminded that there is no single solution that fits all healthcare buildings. As such, it’s crucial for decision-makers to understand the systems that are being put in place throughout each of the touchpoints in their facility. Clear collaboration is required during periods of specification, where together, teams can ensure the selected product works on all angles, from meeting fire safety and sustainability standards to aesthetics and scalability. Modern access control products Scalability is a key area that decision-makers must review when selecting access control systemsFrequently overlooked, scalability is a key area that decision-makers must review when selecting access control systems. Such is their diverse nature; healthcare facilities can often change and develop as years go by, and by selecting a system that facilitates growth, such as a cloud-based solution-security and efficiency is long-established. While modern access control products are known for seamless integration, there are some systems that may restrict the ability to use different vendors throughout the remainder of the building’s infrastructure. This, in effect, causes a monopolisation of products throughout the estate, which can have an adverse effect on growth by increasing costs and reducing the levels of service associated with the security system already in place. Improve security and safety A scalable and reliable access control system will continue to improve security and safety by adapting to a building’s new requirements-and all while having minimal impact on its operational network. And so, while technology will no doubt continue to influence and transform the access control market, healthcare facilities and their professionals must continue to remain educated on their own systems, ensuring they have the best options in place to keep their patients, staff and visitors safe and secure for years to come.
Security beat
Companies at GSX 2023 emphasised new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasises ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the mid-market to the cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for the pure cloud, but there are benefits to be realised from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realise the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘soft’ features for integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organisation more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organisation more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centres around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasising performance, protection (cybersecurity), and price, their data centres are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring centre where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organisations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customised questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
New buzzwords were abundant in the articles that generated the most clicks on our website in 2022. From the metaverse to the Internet of Things, from frictionless access control to artificial intelligence (AI), the topics most popular among our site’s visitors were at the cutting edge of change and innovation in the physical security marketplace. Here is a review of the Top 10 Articles of 2022, based on reader clicks, including links to the original content: Metaverse will promote collaboration and enable more efficiencies for security Metaverse is a familiar buzzword currently, but few people grasp what it means. In the simplest terms, the metaverse is an online “place” where physical, virtual, and augmented realities are shared. The term, Metaverse, suggests a more immersive online environment that combines elements of augmented reality (AR) and virtual reality (VR). For the physical security industry, the looming creation of a complex online environment offers possibilities and challenges. Establishing identity will be a central principle of the metaverse, and various biometrics are at the core of ensuring the identity of someone interacting in the virtual world. Cybersecurity elements are also key. On the benefits side, the security market is already taking advantage of technologies related to the eventual evolution of the metaverse. For example, the industry has deployed AR to provide information about a door lock’s status on a screen, headset, or smart glasses as a patrolling guard walks by. What are the security challenges of the transportation industry? Because transit agencies rely on several IoT devices, they get exposed to higher cybersecurity risks Rapid technological advancement, increasing urbanisation, and the growing expectations of commuters and governments are pressuring transit industry players to modernise. Commuters, urban planners, first responders, and other stakeholders want to use transit data to support their decision-making. Transit agencies’ security and operations teams need closer collaboration to stay ahead. However, for many years, most transit agencies have relied on siloed, proprietary systems. Because transit agencies rely on an ever-growing number of Internet of Things (IoT) devices, they also get exposed to higher cybersecurity risks as there are more network access points to manage. The future is here: ADT’s innovation lab evaluating robots and indoor drones New robots and indoor drones for security applications are on the horizon, based on the work of ADT Commercials’ Innovation Lab, which is evaluating the latest technologies’ value to customers and some typical use cases. The ideal use of humanoid robots is to perform jobs that are considered repetitive, dirty, dangerous, and/or mundane. In security, that describes most security guard positions. As the name implies, autonomous indoor drones are focused on flying indoors versus the outdoor environment, which is heavily regulated by the U.S. Federal Aviation Administration (FAA). Flying autonomously indoors not only eliminates FAA oversight but also will enable ADT Commercial to offer another choice to customers to further reduce their dependencies on and costs of human guards. Innovative security: the key to business efficiency, cost savings, and more Organisations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend. More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organisations looking to drive higher productivity and profitability margins should consider security upgrades that prioritise integrated analytics and automation. Shoplifting today is more sophisticated, and so are the tools to fight it One tool to fight shoplifting is analytics, which can be used to determine where shrink is occurring Shoplifting is often viewed as petty theft by individuals, but that is not always the case. Overall, shoplifting is becoming more sophisticated and coordinated. Traditional “shoplifting” has two major differences when compared to organised retail crime (ORC). The differences are numbers and motivation. ORC consists of groups working together to monetise theft, very different than an individual taking an item they need. One tool to fight to shoplift is analytics, which can be used to determine where shrink is occurring. Understanding where crimes take place helps retailers make strategic decisions about where to place their loss prevention efforts. Oosto offers 10 reasons to switch to frictionless access control in commercial buildings Access control for buildings is nothing new. It’s only in recent years that the urgency to implement smarter, more efficient, and more convenient forms of access control has increased, in the context of public and private sector digital transformation. Upheavals from the COVID-19 pandemic have forced organisations to re-think, pivot, and invest in new technology solutions that will incorporate Artificial Intelligence (AI) and Machine Learning, to gain speed in their operations, glean actionable insights from their video analytics, and enhance productivity with their teams. Which security trend is here to stay? Technologies and trends in the security marketplace come and go with some regularity. But how can you tell which trends are gaining traction and which amount to “the flavor of the month.” For example, while many physical security departments were hesitant to consider cloud-connected solutions in the past, they now better understand the benefits these solutions bring and how they can help them utilize their resources to achieve business goals while minimising overall operational complexity. Other technologies mentioned in the article include mobile credentials, AI-based analytics, video management systems, cybersecurity, and a new emphasis on data. What do these technology trends have in common? They are opening new possibilities for greater system efficiency and functionality. In short, they are playing a role in transforming our industry. GSX 2022 reflects changing technologies and evolving role of security The role of the security director increasingly will encompass facets of cybersecurity and physical security GSX 2022 in Atlanta highlighted the changing role of security in the enterprise. The role of the security director increasingly will encompass facets of cybersecurity as well as physical security. Transitioning to an operation that incorporates both disciplines requires a workforce that embraces education and building new skills. Education and the opportunity to build new skills are evident everywhere at GSX, including in the hundreds of education sessions and also in the knowledge shared on the show floor in the exhibit hall. Consolidation changing the face of the security market Consolidation is a dominant trend in the security marketplace. Large companies typically swallow up smaller companies as a means of expanding both their technology portfolios and their geographic reach. Sometimes a big fish is swallowed up by an even bigger fish. Despite the pandemic and resulting economic challenges, the security market has continued to be a desirable environment for both big players and startups, which then provide abundant acquisition targets for larger companies. This article highlighted recent mergers and acquisition news. Six trends at the intersection of video and AI Video has evolved beyond the capabilities of advanced imaging and performance to include another level: Artificial Intelligence. Video imaging technology combines with AI, delivers a wealth of new data, not just for traditional physical security applications, but for a much deeper analysis of past, present, and even future events across the enterprise. This is more than a big development for the physical security industry; it is a monumental paradigm shift that is changing how security system models are envisioned, designed, and deployed. Much of the heightened demand for advanced video analytics is being driven by six prevalent industry trends.
Case studies
Located in the French suburb of Talence near Bordeaux, within a 15-hectare estate, the Centre for Resources, Expertise, and Sports Performance (CREPS) of Bordeaux is a local public training institution specialising in sports and youth training. The institution, which hosts nearly 450 athletes across 25 training areas, chose Hanwha Vision and its cameras to assist coaches in the training and preparation of athletes. The objective Enhancing athlete performance with video analysis The CREPS of Bordeaux regularly welcomes delegations of French and international athletes who come to prepare for major events, such as the Olympic and Paralympic Games, World Championships, and European Championships. To improve athletes' performance, video intelligence is used by the institution, offering athletes the ability to review their training sessions, playback actions, and complete recordings of their sessions for later analysis. The challenge was to find cameras with a performance level that met the different requirements of various sports disciplines. Challenges at Bordeaux's Fencing Hall This camera is needed to ensure image quality without distortion and with precision, particularly for sabre fencing In the CREPS of Bordeaux's fencing hall, which hosts Olympic and world medalists for training, the most challenging task was finding a camera capable of capturing the entire combat area, including 14-metre-long pistes with little space for positioning. This camera is needed to ensure image quality without distortion and with precision, particularly for sabre fencing where bouts often occur at the ends of the piste. The solution Implementation of high-resolution 180° panoramic multi-sensor cameras E-Novon, a company specialising in sports video and a long-time partner of Hanwha Vision, tested different types of cameras in real situations to meet coaches' needs. "After analysing with the coaches, the PNM-9022V camera was the most suitable due to its angle with minimal guaranteed distortion," according to Romain Briffa, Director at E-Novon. Offering a 180° view reconstructed from four high-resolution video sensors, this camera provides a highly detailed image across its entire field of view, without distortion. Additionally, it requires very little space behind the filmed scene. Conclusion and results CREPS enhances its cutting-edge video tools for greater efficiency After evaluating several solutions, Cyril Faucher, Coordinator of the Performance Support Mission within the high-level department of CREPS, concludes, "Due to the quality and fluidity of the images, the solution provided by E-Novon and Hanwha Vision fully satisfies CREPS in optimising training in the fencing hall." Currently being deployed for fencing and modern pentathlon training, this solution opens up promising perspectives due to the insights being made available, including tracking fencers on the piste, providing statistics, and more.
Revader Security was selected by safety & security specialists North to provide over 75 re-deployable CCTV cameras to the London Borough of Hammersmith and Fulham as part of their contract to upgrade the council’s public space CCTV network. Revader’s re-deployable CCTV cameras are all-in-one professional surveillance solutions that combine an HD camera, recording, onboard storage and wireless transmission in a single compact unit. Fleet of re-deployable cameras They can operate from a wide range of power sources, including mains, battery and solar The cameras can be installed in virtually any location and can be easily moved to target crime hotspots and other areas of interest, enabling police and local authorities to deter offenders, respond to developing incidents and secure prosecutions. They can operate from a wide range of power sources, including mains, battery and solar. The fleet of re-deployable cameras is used by the council’s CCTV operators to tackle street crime, anti-social behaviour and fly-tipping, protect property, prevent trespass, improve public safety and monitor traffic flow. Delivered over a three-year period, this purchase was part of the London Borough of Hammersmith and Fulham’s £5.4 million investment into its CCTV network. The borough has a surveillance network of over 1,900 cameras in total, representing the highest-density network of CCTV cameras in the UK. Longstanding partnership with North Stuart Caldecourt, Managing Director at Revader Security, said: “We are delighted that the investment being made by Hammersmith & Fulham Council into its surveillance network is delivering results, with more police arrests enabled by high-quality CCTV footage and more prosecutions supported by video evidence. We are proud to continue our longstanding partnership with North to deliver cutting-edge solutions that make our communities safer and more secure.” Revader Security continues to work alongside the partners to support Hammersmith & Fulham Council and a wide range of other local authorities, police forces and industrial users across the UK.
A renowned global pioneer in international education services provides various programs and comprehensive support to students pursuing their educational goals abroad. Originating from Australia in 1969, its primary objective has been facilitating educational opportunities worldwide. The company is closely associated with IELTS (International English Language Testing System), and it assists students in studying in English-speaking nations like Australia, New Zealand, Canada, Ireland, the UK, and the US. Company profile In India alone, it has over 70 offices across 61 cities and grew its operations in Southeast Asian nations Situated in Delhi, India, the company’s Indian headquarters serves as a central operational hub, addressing the diverse needs of Indian students aspiring for overseas education. With a team of dedicated experts, the centre offers students personalised guidance, counselling, and support nationwide. In India alone, it has over 70 offices across 61 cities and expanded its operations in Southeast Asian countries. Motivated by a commitment to excellence, integrity, and student success, the company continues to empower individuals, fostering global connections and promoting cultural understanding through international education. Challenges Ensuring the integrity of its assessment process Needed a standard procedure that could be replicated across 61 locations Evidence capturing to confirm the identity of the student appearing for the exam Needed a surveillance solution that ensured compliance at the centre Need to capture footage locally and centralised monitoring The surveillance solution should be dependable, scalable, and interoperable Business scenario The institute sought a wide surveillance solution that captured the details of every student As the co-owner of the IELTS, the institute faced significant challenges in ensuring the integrity of its assessment process for students studying in English-speaking countries. With centres spread across India and other Southeast Asian countries like Sri Lanka, Bangladesh, and Bhutan, they needed a reliable surveillance solution to verify the identity of candidates at their assessment centres. It was crucial for the assessment process to be standardised across 61 locations and easily replicable in new centres. With 11 assessment centres and 49 centres where students arrived for assessment, the institute sought a comprehensive surveillance solution that captured the details of every student entering their premises and cross-referenced them with their system centrally. Additionally, they required a robust recording architecture to store video evidence for future reference as needed securely. In essence, the company faced the distressing challenge of establishing a surveillance solution that was dependable, scalable, capable of capturing essential details, and interoperable. They needed a distributed architecture with centralised control to meet their surveillance requirements effectively. Solution The surveillance solution comprised of: The challenges faced by the institute were swiftly assessed by Matrix experts, who devised a robust surveillance structure to ensure compliance across multiple centres in India and abroad. In all 61 centres, Matrix 2MP PTZ cameras with 25x optical zoom were strategically installed to capture the faces of candidates arriving for tests and match them with their recorded details in the system. The movement of each candidate was meticulously recorded in the system to maintain accurate identity records. The action of each candidate was meticulously recorded in the system to keep real identity records Further, the accuracy was enhanced by adding a secondary layer of surveillance to monitor compliance with the SOP. Matrix PTZ cameras with 25x optical zoom adeptly captured intricate event details recorded in the computer. To meet the needs of each centre, NVRs (Network Video Recorders) with different capacities were installed. This enabled the local recording of details at each centre. Following the client's specifications, the NVRs were configured to store recorded details for three months. Additionally, cameras were installed at the 11 OSM sites to ensure compliance at the places where the papers were assessed. Products offered SATATYA MIBR20FL36CWP: 543 2MP IR Bullet Camera with 3.6mm Lens with Audio SATATYA MIDR20FL36CWP: 264 2MP IR Dome Camera with 3.6mm Lens with Audio SATATYA PZCR20ML25CWP: 76 2MP Pan-Tilt-Zoom Camera with 25x Optical Zoom SATATYA NVR1601X - 8 Nos 16 Channel NVR with 1 SATA Port SATATYA NVR1602X - 8Nos 16 Channel NVR with 2 SATA Port - 8 Nos SATATYA NVR3202X - 1Nos 32 Channel NVR with 2 SATA Port SATATYA NVR3204X - 31Nos 32 Channel NVR with 4 SATA Port SATATYA NVR6404X - 2Nos 64 Channel NVR with 4 SATA Port SATATYA NVR6408X - 7Nos 64 Channel NVR with 8 SATA Port MATRIX LICENCE DONGLE 200 Enterprise VMS: USB Dongle to Run Licence Application SATATYA SAMAS PLT Enterprise VMS: Software for up to 65,535 Cameras SATATYA SAMAS CAM100 - 5Nos Enterprise VMS: 100 Camera Licence SATATYA SAMAS USER3 - 5Nos Enterprise VMS: 3 Concurrent User Licence Benefits Enhanced Assessment Integrity: By implementing Matrix 2MP PTZ cameras with 25x optical zoom across all 61 assessment centres, the company ensured the integrity of the assessment process. These cameras meticulously capture the faces of candidates arriving for tests, allowing them to verify their identities and maintain accurate records. Standardised and Replicable Procedure: The Education Centre needed a standard procedure that could be replicated across the extensive network of centres. The Matrix surveillance solution provided it with a standardised approach that could be easily implemented in new locations, ensuring consistency in its assessment process. Compliance Assurance: The addition of Matrix PTZ cameras with 25x optical zoom and a secondary layer of surveillance helped them monitor and ensure compliance with the Standard Operating Procedures (SOP) at all times. Dependable and Scalable Surveillance: Matrix's NVRs with different capacities allowed the Institute to locally store recorded details at each centre while ensuring reliability and scalability for future expansion. Centralised Monitoring: To streamline the operations, they needed a surveillance solution that allowed seamless central monitoring. Matrix's solution facilitated the cross-referencing of student details with their system centrally and, enhancing efficiency and data accuracy. Interoperability: Matrix's surveillance solution is designed to be interoperable, ensuring seamless integration with the existing infrastructure. This interoperability enables them to adapt to evolving technological requirements while maintaining the integrity of the assessment process. In summary, Matrix's comprehensive surveillance solution not only addressed the immediate challenges but also provided a robust foundation for the assessment process, enabling them to uphold the highest standards of integrity, compliance, and efficiency across all assessment centres.
Genetec Inc., the pioneer in enterprise physical security software, announced that it has been selected by the City of Brampton in Ontario to support a new public safety initiative. Genetec solutions will be used to help Brampton provide regional law enforcement agencies with critical data to expedite crime investigations and improve community safety. Genetec AutoVu™ SharpV LPR Brampton’s project will see the deployment of 200 Genetec AutoVu™ SharpV LPR cameras As the first project of its kind in Canada, Brampton’s project will see the deployment of 200 Genetec AutoVu™ SharpV Licence Plate Recognition (LPR) cameras at major intersections. These cameras will not be used for issuing speeding tickets; instead, they will function exclusively as an investigative tool to support Peel Regional Police in solving crimes and monitoring vehicle-related incidents. 360-Degree street cameras By capturing key vehicle details—such as licence plate numbers, make, colour, and type—they will assist law enforcement in investigating offences and enhancing public safety. Data from AutoVu SharpV and 360-degree street cameras from Axis Communications will be managed through Genetec™ Security Centre. The platform will enable investigators to correlate vehicle information with corresponding video footage to enhance situational awareness and enable faster incident response. Clearance digital evidence management system System will operate in full compliance with municipal, provincial, and federal privacy laws In the event of a reported incident, the City of Brampton will be able to quickly and securely share video evidence and ALPR data with law enforcement using the Genetec Clearance digital evidence management system. This will help expedite investigations by ensuring critical evidence is readily accessible when needed. Security and data privacy remain paramount with this initiative, and the system will operate in full compliance with municipal, provincial, and federal privacy laws. New innovations and technologies All captured information will be securely managed and used solely for law enforcement investigations. Only authorised personnel will have access to the data, with all user activities and case-related actions being logged to maintain the integrity of the chain of custody. “Peel Regional Police is committed to utilising new innovations and technologies to better support the critical work of our officers and enhance public safety," said Deputy Chief Anthony Odoardi, Peel Regional Police. All captured data will be securely managed and used solely for law enforcement studiesOdoardi added: "This welcomed investment by the City of Brampton will provide our service with increased access to data, improving our ability to investigate and respond to traffic-related crimes and safety concerns. By working together, we will continue to strengthen our efforts in keeping our communities safe.” “Too many victims and families have suffered heartbreak at the hands of criminals and enough is enough. Residents made it clear through the 2025 budget process that they want to see action from the City to address community safety, and we are delivering," said Patrick Brown, Mayor, City of Brampton. Expansion of investigative tools Brown added: "By investing in cutting-edge technology, we are giving law enforcement the tools they need to track down offenders and hold them accountable." "This is a major expansion of police investigative tools making Brampton the worst place in Canada to commit a crime. It is a game changer in protecting our community and sends a message to criminals that if you commit a crime in Brampton, you will be caught.” Video surveillance and digital management solutions “The City of Brampton is demonstrating exceptional leadership in using technology to enhance public safety in a responsible and effective way,” said Alain Bissada, Area Vice President - North America at Genetec Inc. “The deployment of our licence plate recognition cameras, alongside our video surveillance and digital evidence management solutions, will provide law enforcement with high-quality, real-time data to support their investigations while ensuring that privacy remains a top priority.”
Yanmar Holdings Co., Ltd. is one of Japan's largest manufacturing companies, founded in 1912, and now has more than 25,000 employees worldwide. Yanmar has positioned itself in the international market as a pioneer in diesel engine technology and has developed a wide range of industrial equipment, including engines, agricultural machinery, installations, construction equipment, power systems, marine and other components. With over a century of manufacturing experience, Yanmar is actively promoting digital transformation across the company. As part of this initiative, VIVOTEK implemented advanced surveillance solutions to enhance traffic management and operational efficiency for Yanmar Construction Equipment Co., Ltd. in Fukuoka, Japan. Challenges Before implementing VIVOTEK’s surveillance solutions, Yanmar Construction Equipment Co., Ltd. faced several challenges in ensuring the safety of the factory area. These challenges included: Automated Guided Vehicles (AGVs) were prone to accidents at intersections with truck routes and walking zones. Additionally, AGVs sometimes derailed or stopped due to issues like sunlight reflecting off QR code covers, affecting navigation and requiring better monitoring for diagnosis and resolution. Difficulty in identifying the root causes of quality issues on the assembly line due to high daily production volume and operators' inability to recall specific incidents. Inefficient manual inspections were needed to monitor paint sludge on stored paint containers, along with the need to understand the true causes of productivity issues and detect abnormalities in painting equipment early. These challenges underscored the need for a comprehensive security solution to enhance the efficiency and safety of factory operations. A surveillance system can not only track accidents on traffic routes and improve route planning but also boost overall factory operational efficiency. Solutions After identifying the client’s pain points, VIVOTEK, in collaboration with its partner Takebishi, tailored advanced surveillance solutions to meet their needs by installing various types of cameras and a video receiver in the construction equipment assembly facility of Yanmar Construction Equipment Co., Ltd. AGVs Monitoring: Cameras are focused on monitoring AGVs, enabling supervisors to respond immediately to accidents and identify areas for improvement in safety protocols. Assembly Line Monitoring: Camera footage captures images of the assembly line, helping to pinpoint the causes of quality issues and streamline production processes. By utilising this "looking-back" analysis, management can improve both productivity and safety, pinpoint areas needing improvement, and significantly reduce unwanted accidents, resulting in more effective and efficient operations. Sludge Monitoring: Cameras can monitor the accumulated sludge on stored paint containers, which can cause unpleasant odours in the facility. This monitoring helps maintain a cleaner and odor-free environment. Previously, staff had to physically inspect the site every hour, often discovering that no cleaning was necessary. With the cameras providing continuous real-time images, management can now remotely monitor the condition of the equipment, significantly reducing unnecessary site visits. Staff only need to visit the site when cleaning is actually required. Smart Analysis through Integration of VIVOTEK’s Cameras and BI Tool: By integrating VIVOTEK’s cameras with the BI tool MotionBoard, camera footage is now being used for work analysis and status monitoring in the factory, enabling more intelligent analysis. Results and customer feedback Yanmar Construction Equipment Co., Ltd. expressed a high level of satisfaction with VIVOTEK’s advanced surveillance solutions, including performance, price, and reliability. "Not only did they meet our requirements, but VIVOTEK also provided more detailed proposals based on their expertise. They were flexible in handling tight deadlines and challenging installation demands," said Yanmar Construction Equipment Co., Ltd. "While this project was implemented at one of Yanmar Construction Equipment Co., Ltd.'s locations, due to the customer's high satisfaction, we aim to expand the solution across their nationwide facilities and throughout the entire Yanmar Group," commented from partner company Takebishi Co., Ltd.
LATINA Construction and Drilling needs to maximise staff safety and site security on the La Santa Maria oil drilling platform in the Gulf of Mexico. To achieve this, they have implemented a Hikvision solution featuring explosion-proof cameras equipped with deep learning algorithms for perimeter protection and fire detection. This system provides real-time alerts to the security team for swift incident response. Challenge: Maximising security and safety High value of hydrocarbon products makes perimeter security crucial for safeguarding staff and assets Oil and gas sites face unique security and health and safety challenges. The extraction, refining, and transport of hydrocarbons present significant fire and explosion risks that require all equipment and installations to operate at safe working temperatures. Additionally, the high value of hydrocarbon products makes perimeter security crucial for safeguarding staff and assets. These are some of the well-known challenges facing Constructora y Perforadora LATINA (LATINA Construction and Drilling), a major geothermal drilling company in Latin America with more than 60 years of experience. ‘La Santa Maria’ drilling platform The organisation is responsible for operating the ‘La Santa Maria’ drilling platform in the Gulf of Mexico, while also ensuring protection of the local maritime environment and wildlife based on responsible operations. The platform, built in 2013, is relatively close to land, making it more vulnerable to security breaches and property damage from trespassers. To address these risks, and to ensure that environmental risks are mitigated, the platform needed a new, improved, security solution. 24x7 perimeter security This needed to provide 24x7 perimeter security, excellent fire prevention capabilities, and the ability to minimise health and safety risks for employees. In addition, the system needed to be highly corrosion-resistant to withstand the harsh maritime environment, where the platform is located. Solution: Hikvision explosion-proof thermal imaging cameras with on-board deep learning for fire detection and perimeter security To overcome these challenges, LATINA Construction and Drilling, in collaboration with the renowned System Integrator - STC Global System, has deployed a Hikvision solution, which incorporates Thermal & Optical Bi-spectrum Network Bullet Cameras (DS-2TD2637-35/P) and Explosion-Proof Thermographic Network Bullet Cameras (DS-2TD2466T-25X). Hikvision explosion-proof thermal imaging cameras The explosion-proof cameras are housed in 316L stainless-steel casings The explosion-proof cameras are housed in 316L stainless-steel casings, preventing sparks or heat from coming into contact with potentially flammable fumes. The casings meet the NEMA-4X anti-corrosion standard, ensuring durability in the salty sea environment. The cameras’ thermal imaging capabilities, along with the sensitive fire-detection algorithm, ensure that any overheating equipment is reported immediately, even in low-visibility conditions such as fog and rain. Cameras feature powerful analytics functions Both Hikvision camera models use an on-board deep learning algorithm to provide powerful analytics functions. This means the cameras can generate alerts immediately for certain types of incidents, including perimeter invasions (line crossing) and entry of unauthorised people. The algorithm also distinguishes false alarms caused by moving objects like seabirds, high waves or storms from genuine threats, such as people invading the platform perimeter. This helps to minimise false alarms. The cameras also feature light and strobe alarms to alert intruders, deterring them from further actions. Benefits: Increased staff health and safety, optimised operational efficiency, and durable performance Enclosed in heavy-duty casings, the Hikvision explosion-proof cameras help to maximise staff health and safety by ensuring that the risk of camera-related sparks and resulting fires and explosions is minimised. Additionally, the cameras' thermal imaging helps the platform respond quickly to temperature increases or fires, ensuring the safety of personnel and assets, while adhering to environmental regulations. False alarm reduction deep learning algorithm The company can mitigate security risks associated with the platform’s location close to land The false alarm reduction deep learning algorithm ensures that members of the security team can focus 100% of their effort on genuine security threats, speeding up responses, saving time, and increasing operating efficiency and performance. With automated alerts for security incidents, such as ‘line crossing’, the company can mitigate security risks associated with the platform’s location close to land and ensure the safety of everyone working on the platform. Corrosion-resistant cameras offer chemical resistance Finally, but equally importantly, the corrosion-resistant cameras offer exceptional chemical resistance and durability, making them well-suited to withstand the harsh maritime conditions of the Gulf of Mexico. This reliability ensures that LATINA Construction and Drilling continues to benefit from the system for years, despite constant exposure to saltwater. Additionally, the reduced need for repairs and maintenance results in significant cost savings.
Located in the French suburb of Talence near Bordeaux, within a 15-hectare estate, the Centre for Resources, Expertise, and Sports Performance (CREPS) of Bordeaux is a local public training institution specialising in sports and youth training. The institution, which hosts nearly 450 athletes across 25 training areas, chose Hanwha Vision and its cameras to assist coaches in the training and preparation of athletes. The objective Enhancing athlete performance with video analysis The CREPS of Bordeaux regularly welcomes delegations of French and international athletes who come to prepare for major events, such as the Olympic and Paralympic Games, World Championships, and European Championships. To improve athletes' performance, video intelligence is used by the institution, offering athletes the ability to review their training sessions, playback actions, and complete recordings of their sessions for later analysis. The challenge was to find cameras with a performance level that met the different requirements of various sports disciplines. Challenges at Bordeaux's Fencing Hall This camera is needed to ensure image quality without distortion and with precision, particularly for sabre fencing In the CREPS of Bordeaux's fencing hall, which hosts Olympic and world medalists for training, the most challenging task was finding a camera capable of capturing the entire combat area, including 14-metre-long pistes with little space for positioning. This camera is needed to ensure image quality without distortion and with precision, particularly for sabre fencing where bouts often occur at the ends of the piste. The solution Implementation of high-resolution 180° panoramic multi-sensor cameras E-Novon, a company specialising in sports video and a long-time partner of Hanwha Vision, tested different types of cameras in real situations to meet coaches' needs. "After analysing with the coaches, the PNM-9022V camera was the most suitable due to its angle with minimal guaranteed distortion," according to Romain Briffa, Director at E-Novon. Offering a 180° view reconstructed from four high-resolution video sensors, this camera provides a highly detailed image across its entire field of view, without distortion. Additionally, it requires very little space behind the filmed scene. Conclusion and results CREPS enhances its cutting-edge video tools for greater efficiency After evaluating several solutions, Cyril Faucher, Coordinator of the Performance Support Mission within the high-level department of CREPS, concludes, "Due to the quality and fluidity of the images, the solution provided by E-Novon and Hanwha Vision fully satisfies CREPS in optimising training in the fencing hall." Currently being deployed for fencing and modern pentathlon training, this solution opens up promising perspectives due to the insights being made available, including tracking fencers on the piste, providing statistics, and more.
Revader Security was selected by safety & security specialists North to provide over 75 re-deployable CCTV cameras to the London Borough of Hammersmith and Fulham as part of their contract to upgrade the council’s public space CCTV network. Revader’s re-deployable CCTV cameras are all-in-one professional surveillance solutions that combine an HD camera, recording, onboard storage and wireless transmission in a single compact unit. Fleet of re-deployable cameras They can operate from a wide range of power sources, including mains, battery and solar The cameras can be installed in virtually any location and can be easily moved to target crime hotspots and other areas of interest, enabling police and local authorities to deter offenders, respond to developing incidents and secure prosecutions. They can operate from a wide range of power sources, including mains, battery and solar. The fleet of re-deployable cameras is used by the council’s CCTV operators to tackle street crime, anti-social behaviour and fly-tipping, protect property, prevent trespass, improve public safety and monitor traffic flow. Delivered over a three-year period, this purchase was part of the London Borough of Hammersmith and Fulham’s £5.4 million investment into its CCTV network. The borough has a surveillance network of over 1,900 cameras in total, representing the highest-density network of CCTV cameras in the UK. Longstanding partnership with North Stuart Caldecourt, Managing Director at Revader Security, said: “We are delighted that the investment being made by Hammersmith & Fulham Council into its surveillance network is delivering results, with more police arrests enabled by high-quality CCTV footage and more prosecutions supported by video evidence. We are proud to continue our longstanding partnership with North to deliver cutting-edge solutions that make our communities safer and more secure.” Revader Security continues to work alongside the partners to support Hammersmith & Fulham Council and a wide range of other local authorities, police forces and industrial users across the UK.
A renowned global pioneer in international education services provides various programs and comprehensive support to students pursuing their educational goals abroad. Originating from Australia in 1969, its primary objective has been facilitating educational opportunities worldwide. The company is closely associated with IELTS (International English Language Testing System), and it assists students in studying in English-speaking nations like Australia, New Zealand, Canada, Ireland, the UK, and the US. Company profile In India alone, it has over 70 offices across 61 cities and grew its operations in Southeast Asian nations Situated in Delhi, India, the company’s Indian headquarters serves as a central operational hub, addressing the diverse needs of Indian students aspiring for overseas education. With a team of dedicated experts, the centre offers students personalised guidance, counselling, and support nationwide. In India alone, it has over 70 offices across 61 cities and expanded its operations in Southeast Asian countries. Motivated by a commitment to excellence, integrity, and student success, the company continues to empower individuals, fostering global connections and promoting cultural understanding through international education. Challenges Ensuring the integrity of its assessment process Needed a standard procedure that could be replicated across 61 locations Evidence capturing to confirm the identity of the student appearing for the exam Needed a surveillance solution that ensured compliance at the centre Need to capture footage locally and centralised monitoring The surveillance solution should be dependable, scalable, and interoperable Business scenario The institute sought a wide surveillance solution that captured the details of every student As the co-owner of the IELTS, the institute faced significant challenges in ensuring the integrity of its assessment process for students studying in English-speaking countries. With centres spread across India and other Southeast Asian countries like Sri Lanka, Bangladesh, and Bhutan, they needed a reliable surveillance solution to verify the identity of candidates at their assessment centres. It was crucial for the assessment process to be standardised across 61 locations and easily replicable in new centres. With 11 assessment centres and 49 centres where students arrived for assessment, the institute sought a comprehensive surveillance solution that captured the details of every student entering their premises and cross-referenced them with their system centrally. Additionally, they required a robust recording architecture to store video evidence for future reference as needed securely. In essence, the company faced the distressing challenge of establishing a surveillance solution that was dependable, scalable, capable of capturing essential details, and interoperable. They needed a distributed architecture with centralised control to meet their surveillance requirements effectively. Solution The surveillance solution comprised of: The challenges faced by the institute were swiftly assessed by Matrix experts, who devised a robust surveillance structure to ensure compliance across multiple centres in India and abroad. In all 61 centres, Matrix 2MP PTZ cameras with 25x optical zoom were strategically installed to capture the faces of candidates arriving for tests and match them with their recorded details in the system. The movement of each candidate was meticulously recorded in the system to maintain accurate identity records. The action of each candidate was meticulously recorded in the system to keep real identity records Further, the accuracy was enhanced by adding a secondary layer of surveillance to monitor compliance with the SOP. Matrix PTZ cameras with 25x optical zoom adeptly captured intricate event details recorded in the computer. To meet the needs of each centre, NVRs (Network Video Recorders) with different capacities were installed. This enabled the local recording of details at each centre. Following the client's specifications, the NVRs were configured to store recorded details for three months. Additionally, cameras were installed at the 11 OSM sites to ensure compliance at the places where the papers were assessed. Products offered SATATYA MIBR20FL36CWP: 543 2MP IR Bullet Camera with 3.6mm Lens with Audio SATATYA MIDR20FL36CWP: 264 2MP IR Dome Camera with 3.6mm Lens with Audio SATATYA PZCR20ML25CWP: 76 2MP Pan-Tilt-Zoom Camera with 25x Optical Zoom SATATYA NVR1601X - 8 Nos 16 Channel NVR with 1 SATA Port SATATYA NVR1602X - 8Nos 16 Channel NVR with 2 SATA Port - 8 Nos SATATYA NVR3202X - 1Nos 32 Channel NVR with 2 SATA Port SATATYA NVR3204X - 31Nos 32 Channel NVR with 4 SATA Port SATATYA NVR6404X - 2Nos 64 Channel NVR with 4 SATA Port SATATYA NVR6408X - 7Nos 64 Channel NVR with 8 SATA Port MATRIX LICENCE DONGLE 200 Enterprise VMS: USB Dongle to Run Licence Application SATATYA SAMAS PLT Enterprise VMS: Software for up to 65,535 Cameras SATATYA SAMAS CAM100 - 5Nos Enterprise VMS: 100 Camera Licence SATATYA SAMAS USER3 - 5Nos Enterprise VMS: 3 Concurrent User Licence Benefits Enhanced Assessment Integrity: By implementing Matrix 2MP PTZ cameras with 25x optical zoom across all 61 assessment centres, the company ensured the integrity of the assessment process. These cameras meticulously capture the faces of candidates arriving for tests, allowing them to verify their identities and maintain accurate records. Standardised and Replicable Procedure: The Education Centre needed a standard procedure that could be replicated across the extensive network of centres. The Matrix surveillance solution provided it with a standardised approach that could be easily implemented in new locations, ensuring consistency in its assessment process. Compliance Assurance: The addition of Matrix PTZ cameras with 25x optical zoom and a secondary layer of surveillance helped them monitor and ensure compliance with the Standard Operating Procedures (SOP) at all times. Dependable and Scalable Surveillance: Matrix's NVRs with different capacities allowed the Institute to locally store recorded details at each centre while ensuring reliability and scalability for future expansion. Centralised Monitoring: To streamline the operations, they needed a surveillance solution that allowed seamless central monitoring. Matrix's solution facilitated the cross-referencing of student details with their system centrally and, enhancing efficiency and data accuracy. Interoperability: Matrix's surveillance solution is designed to be interoperable, ensuring seamless integration with the existing infrastructure. This interoperability enables them to adapt to evolving technological requirements while maintaining the integrity of the assessment process. In summary, Matrix's comprehensive surveillance solution not only addressed the immediate challenges but also provided a robust foundation for the assessment process, enabling them to uphold the highest standards of integrity, compliance, and efficiency across all assessment centres.
Genetec Inc., the pioneer in enterprise physical security software, announced that it has been selected by the City of Brampton in Ontario to support a new public safety initiative. Genetec solutions will be used to help Brampton provide regional law enforcement agencies with critical data to expedite crime investigations and improve community safety. Genetec AutoVu™ SharpV LPR Brampton’s project will see the deployment of 200 Genetec AutoVu™ SharpV LPR cameras As the first project of its kind in Canada, Brampton’s project will see the deployment of 200 Genetec AutoVu™ SharpV Licence Plate Recognition (LPR) cameras at major intersections. These cameras will not be used for issuing speeding tickets; instead, they will function exclusively as an investigative tool to support Peel Regional Police in solving crimes and monitoring vehicle-related incidents. 360-Degree street cameras By capturing key vehicle details—such as licence plate numbers, make, colour, and type—they will assist law enforcement in investigating offences and enhancing public safety. Data from AutoVu SharpV and 360-degree street cameras from Axis Communications will be managed through Genetec™ Security Centre. The platform will enable investigators to correlate vehicle information with corresponding video footage to enhance situational awareness and enable faster incident response. Clearance digital evidence management system System will operate in full compliance with municipal, provincial, and federal privacy laws In the event of a reported incident, the City of Brampton will be able to quickly and securely share video evidence and ALPR data with law enforcement using the Genetec Clearance digital evidence management system. This will help expedite investigations by ensuring critical evidence is readily accessible when needed. Security and data privacy remain paramount with this initiative, and the system will operate in full compliance with municipal, provincial, and federal privacy laws. New innovations and technologies All captured information will be securely managed and used solely for law enforcement investigations. Only authorised personnel will have access to the data, with all user activities and case-related actions being logged to maintain the integrity of the chain of custody. “Peel Regional Police is committed to utilising new innovations and technologies to better support the critical work of our officers and enhance public safety," said Deputy Chief Anthony Odoardi, Peel Regional Police. All captured data will be securely managed and used solely for law enforcement studiesOdoardi added: "This welcomed investment by the City of Brampton will provide our service with increased access to data, improving our ability to investigate and respond to traffic-related crimes and safety concerns. By working together, we will continue to strengthen our efforts in keeping our communities safe.” “Too many victims and families have suffered heartbreak at the hands of criminals and enough is enough. Residents made it clear through the 2025 budget process that they want to see action from the City to address community safety, and we are delivering," said Patrick Brown, Mayor, City of Brampton. Expansion of investigative tools Brown added: "By investing in cutting-edge technology, we are giving law enforcement the tools they need to track down offenders and hold them accountable." "This is a major expansion of police investigative tools making Brampton the worst place in Canada to commit a crime. It is a game changer in protecting our community and sends a message to criminals that if you commit a crime in Brampton, you will be caught.” Video surveillance and digital management solutions “The City of Brampton is demonstrating exceptional leadership in using technology to enhance public safety in a responsible and effective way,” said Alain Bissada, Area Vice President - North America at Genetec Inc. “The deployment of our licence plate recognition cameras, alongside our video surveillance and digital evidence management solutions, will provide law enforcement with high-quality, real-time data to support their investigations while ensuring that privacy remains a top priority.”
Yanmar Holdings Co., Ltd. is one of Japan's largest manufacturing companies, founded in 1912, and now has more than 25,000 employees worldwide. Yanmar has positioned itself in the international market as a pioneer in diesel engine technology and has developed a wide range of industrial equipment, including engines, agricultural machinery, installations, construction equipment, power systems, marine and other components. With over a century of manufacturing experience, Yanmar is actively promoting digital transformation across the company. As part of this initiative, VIVOTEK implemented advanced surveillance solutions to enhance traffic management and operational efficiency for Yanmar Construction Equipment Co., Ltd. in Fukuoka, Japan. Challenges Before implementing VIVOTEK’s surveillance solutions, Yanmar Construction Equipment Co., Ltd. faced several challenges in ensuring the safety of the factory area. These challenges included: Automated Guided Vehicles (AGVs) were prone to accidents at intersections with truck routes and walking zones. Additionally, AGVs sometimes derailed or stopped due to issues like sunlight reflecting off QR code covers, affecting navigation and requiring better monitoring for diagnosis and resolution. Difficulty in identifying the root causes of quality issues on the assembly line due to high daily production volume and operators' inability to recall specific incidents. Inefficient manual inspections were needed to monitor paint sludge on stored paint containers, along with the need to understand the true causes of productivity issues and detect abnormalities in painting equipment early. These challenges underscored the need for a comprehensive security solution to enhance the efficiency and safety of factory operations. A surveillance system can not only track accidents on traffic routes and improve route planning but also boost overall factory operational efficiency. Solutions After identifying the client’s pain points, VIVOTEK, in collaboration with its partner Takebishi, tailored advanced surveillance solutions to meet their needs by installing various types of cameras and a video receiver in the construction equipment assembly facility of Yanmar Construction Equipment Co., Ltd. AGVs Monitoring: Cameras are focused on monitoring AGVs, enabling supervisors to respond immediately to accidents and identify areas for improvement in safety protocols. Assembly Line Monitoring: Camera footage captures images of the assembly line, helping to pinpoint the causes of quality issues and streamline production processes. By utilising this "looking-back" analysis, management can improve both productivity and safety, pinpoint areas needing improvement, and significantly reduce unwanted accidents, resulting in more effective and efficient operations. Sludge Monitoring: Cameras can monitor the accumulated sludge on stored paint containers, which can cause unpleasant odours in the facility. This monitoring helps maintain a cleaner and odor-free environment. Previously, staff had to physically inspect the site every hour, often discovering that no cleaning was necessary. With the cameras providing continuous real-time images, management can now remotely monitor the condition of the equipment, significantly reducing unnecessary site visits. Staff only need to visit the site when cleaning is actually required. Smart Analysis through Integration of VIVOTEK’s Cameras and BI Tool: By integrating VIVOTEK’s cameras with the BI tool MotionBoard, camera footage is now being used for work analysis and status monitoring in the factory, enabling more intelligent analysis. Results and customer feedback Yanmar Construction Equipment Co., Ltd. expressed a high level of satisfaction with VIVOTEK’s advanced surveillance solutions, including performance, price, and reliability. "Not only did they meet our requirements, but VIVOTEK also provided more detailed proposals based on their expertise. They were flexible in handling tight deadlines and challenging installation demands," said Yanmar Construction Equipment Co., Ltd. "While this project was implemented at one of Yanmar Construction Equipment Co., Ltd.'s locations, due to the customer's high satisfaction, we aim to expand the solution across their nationwide facilities and throughout the entire Yanmar Group," commented from partner company Takebishi Co., Ltd.
LATINA Construction and Drilling needs to maximise staff safety and site security on the La Santa Maria oil drilling platform in the Gulf of Mexico. To achieve this, they have implemented a Hikvision solution featuring explosion-proof cameras equipped with deep learning algorithms for perimeter protection and fire detection. This system provides real-time alerts to the security team for swift incident response. Challenge: Maximising security and safety High value of hydrocarbon products makes perimeter security crucial for safeguarding staff and assets Oil and gas sites face unique security and health and safety challenges. The extraction, refining, and transport of hydrocarbons present significant fire and explosion risks that require all equipment and installations to operate at safe working temperatures. Additionally, the high value of hydrocarbon products makes perimeter security crucial for safeguarding staff and assets. These are some of the well-known challenges facing Constructora y Perforadora LATINA (LATINA Construction and Drilling), a major geothermal drilling company in Latin America with more than 60 years of experience. ‘La Santa Maria’ drilling platform The organisation is responsible for operating the ‘La Santa Maria’ drilling platform in the Gulf of Mexico, while also ensuring protection of the local maritime environment and wildlife based on responsible operations. The platform, built in 2013, is relatively close to land, making it more vulnerable to security breaches and property damage from trespassers. To address these risks, and to ensure that environmental risks are mitigated, the platform needed a new, improved, security solution. 24x7 perimeter security This needed to provide 24x7 perimeter security, excellent fire prevention capabilities, and the ability to minimise health and safety risks for employees. In addition, the system needed to be highly corrosion-resistant to withstand the harsh maritime environment, where the platform is located. Solution: Hikvision explosion-proof thermal imaging cameras with on-board deep learning for fire detection and perimeter security To overcome these challenges, LATINA Construction and Drilling, in collaboration with the renowned System Integrator - STC Global System, has deployed a Hikvision solution, which incorporates Thermal & Optical Bi-spectrum Network Bullet Cameras (DS-2TD2637-35/P) and Explosion-Proof Thermographic Network Bullet Cameras (DS-2TD2466T-25X). Hikvision explosion-proof thermal imaging cameras The explosion-proof cameras are housed in 316L stainless-steel casings The explosion-proof cameras are housed in 316L stainless-steel casings, preventing sparks or heat from coming into contact with potentially flammable fumes. The casings meet the NEMA-4X anti-corrosion standard, ensuring durability in the salty sea environment. The cameras’ thermal imaging capabilities, along with the sensitive fire-detection algorithm, ensure that any overheating equipment is reported immediately, even in low-visibility conditions such as fog and rain. Cameras feature powerful analytics functions Both Hikvision camera models use an on-board deep learning algorithm to provide powerful analytics functions. This means the cameras can generate alerts immediately for certain types of incidents, including perimeter invasions (line crossing) and entry of unauthorised people. The algorithm also distinguishes false alarms caused by moving objects like seabirds, high waves or storms from genuine threats, such as people invading the platform perimeter. This helps to minimise false alarms. The cameras also feature light and strobe alarms to alert intruders, deterring them from further actions. Benefits: Increased staff health and safety, optimised operational efficiency, and durable performance Enclosed in heavy-duty casings, the Hikvision explosion-proof cameras help to maximise staff health and safety by ensuring that the risk of camera-related sparks and resulting fires and explosions is minimised. Additionally, the cameras' thermal imaging helps the platform respond quickly to temperature increases or fires, ensuring the safety of personnel and assets, while adhering to environmental regulations. False alarm reduction deep learning algorithm The company can mitigate security risks associated with the platform’s location close to land The false alarm reduction deep learning algorithm ensures that members of the security team can focus 100% of their effort on genuine security threats, speeding up responses, saving time, and increasing operating efficiency and performance. With automated alerts for security incidents, such as ‘line crossing’, the company can mitigate security risks associated with the platform’s location close to land and ensure the safety of everyone working on the platform. Corrosion-resistant cameras offer chemical resistance Finally, but equally importantly, the corrosion-resistant cameras offer exceptional chemical resistance and durability, making them well-suited to withstand the harsh maritime conditions of the Gulf of Mexico. This reliability ensures that LATINA Construction and Drilling continues to benefit from the system for years, despite constant exposure to saltwater. Additionally, the reduced need for repairs and maintenance results in significant cost savings.


Round table discussion
Technological leaps in the last several decades have revolutionised biometrics. The technologies are constantly evolving, spanning facial recognition to iris scanning to fingerprints, to provide new levels of security and convenience. Biometrics are everywhere, from smartphones to border control, constantly evolving to meet the needs of our increasingly digital world. They are also more accurate and easier to use than ever. We asked this week's Expert Panel Roundtable: What’s new with biometrics?
There is safety in numbers, or so the expression goes. Generally speaking, several employees working together tend to be safer than a single employee working alone. Even so, some environments require that workers complete their jobs alone, thus presenting a unique combination of security vulnerabilities. The U.S. Occupational Safety and Health Administration (OSHA) defines a lone worker as “an employee working alone, such as in a confined space or isolated location.” We asked this week’s Expert Panel Roundtable: How can security technologies help to protect "lone workers?"
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
Products


White papers

3 ways AI can improve safety and reduce compliance costs
Download
Healthcare Surveillance: Finding efficiencies from OR to ER and beyond
Download
Intelligent video security solutions
Download
Assessing safety readiness for education campuses
Download
5 must-haves for seamless VMS connectivity
Download
The future of healthcare security is connectivity
Download
Improving city mobility using connected video technology
Download
Charting the path to safe cities
Download
Maximising security and performance
Download
The security challenges of data centers
Download
How to lower labour costs when installing video surveillance
Download
Total cost of ownership for video surveillance
Download
Integrating IT & physical security teams
Download
Securing your growth with video surveillance
Download
Identity and access management
Download
3 ways AI can improve safety and reduce compliance costs
Download
Healthcare Surveillance: Finding efficiencies from OR to ER and beyond
Download
Intelligent video security solutions
Download
Assessing safety readiness for education campuses
Download
5 must-haves for seamless VMS connectivity
Download
The future of healthcare security is connectivity
Download
Improving city mobility using connected video technology
Download
Charting the path to safe cities
Download
Maximising security and performance
Download
The security challenges of data centers
Download
How to lower labour costs when installing video surveillance
Download
Total cost of ownership for video surveillance
Download
Integrating IT & physical security teams
Download
Securing your growth with video surveillance
Download
Identity and access management
Download
3 ways AI can improve safety and reduce compliance costs
Download

Videos
Digital video surveillance: Manufacturers & Suppliers
- Dahua Technology Digital video surveillance
- Hikvision Digital video surveillance
- Dedicated Micros Digital video surveillance
- LILIN Digital video surveillance
- ADPRO Digital video surveillance
- eneo Digital video surveillance
- Hanwha Vision Digital video surveillance
- Vicon Digital video surveillance
- Bosch Digital video surveillance
- Pelco Digital video surveillance
- Messoa Digital video surveillance
- March Networks Digital video surveillance
- Vanderbilt Digital video surveillance
- TruVision Digital video surveillance
- Geutebruck Digital video surveillance
- Axis Communications Digital video surveillance
- Digital Express Digital video surveillance
- AV Costar Digital video surveillance
- Everfocus Digital video surveillance
- artec Digital video surveillance

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download