Digital Video Recorders
Powering digital access with energy-harvesting technology frees organisations from wiring and even batteries. However, to meet the challenges of the future, digital access needs more. It needs technologies and software platforms flexible enough to grow and adapt with the evolving needs of each organisation, protecting their investment in digital access while delivering an ROI every day. Digital access solutions Kinetic energy generated by inserting the intelligent key is harvested to power th...
Umazi, a pioneer in digital identity verification solutions, has welcomed the latest report from CFIT, Fighting Economic Crime Through Digital Verification: The Case for Adopting a Digital Company ID in the UK. The report highlights the potential to revolutionise business operations in the UK by improving efficiency, security, and trust. Innovating business verification CFIT has convened over 70 pioneer organisations to design and develop the Digital Company ID—a unique digital represen...
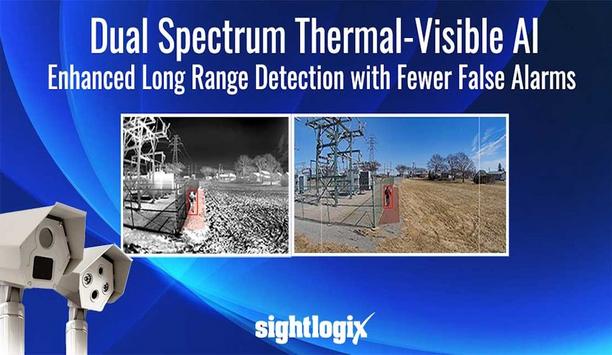
SightLogix, a pioneer in intelligent outdoor security solutions, has announced dual-spectrum AI for its dual-sensor SightSensor product series. This new capability integrates thermal and visible AI validation, providing unmatched, real-time intrusion detection that minimises false alarms. Reliable and immediate awareness is mandatory for high-performing perimeter security solutions in critical infrastructure and commercial remote video monitoring applications. Edge-based intelligence Th...
Konica Minolta has announced the sale of its entire 65% stake in MOBOTIX AG, along with all associated shareholder loans, to CERTINA Software Investments AG, a 100% subsidiary of the Munich-based family equity investor CERTINA Group. The CERTINA Software Division of CERTINA Group specialises in the development and expansion of technology-driven businesses worldwide. CERTINA expands portfolio KONICA MINOLTA's medium plan to divest non-focus business and concentrate on core business areas globa...
Effective collaboration between security operators, teams, and other departments is essential for the smooth functioning of any organisation. However, as organisations grow in complexity, it becomes increasingly challenging for teams to coordinate. Factors such as staffing shortages, high turnover rates, and outdated collaboration tools exacerbate these challenges. Streamlining security operations These solutions enhance communication, boosts productivity, and improves overall operation...
AMAG Technology announces Symmetry CompleteView Video Management 7.5, the latest software update to its video management system (VMS) platform. This version enhances operator experiences and introduces significant new enterprise capabilities including the integration of Iron Yun’s Vaidio® AI Video Analytics. Optimised monitoring The integration of Vaidio® AI Video Analytics supports both real-time monitoring and forensic investigationsThe integration of Vaidio® A...
News
Indonesia is set to host the highly anticipated BIGBOX INDONESIA 2025, a Global Retail & e-commerce Series, an exclusive event bringing together thought pioneers, innovators, and stakeholders shaping the future of retail and e-commerce in Indonesia. Scheduled to take place on the 18th of February 2025 in Jakarta Indonesia. This landmark conference will provide a platform to explore transformative trends, cutting-edge technologies, and strategies driving growth in the digital marketplace. Retail & e-Commerce hub Indonesia is spearheading the change in the region with the retail market expected to grow rapidly, projected to surpass USD 49.56 billion in revenue and 4.73% from 2024 to 2028. Also, Indonesia is anticipated to dominate more than 45% of the Southeast Asian e-commerce sector by 2025. The market's revenue is poised for consistent annual growth, with a projected CAGR of 10.41% from 2023 to 2027. Fuelled by an aspiring middle-class population, burgeoning tech-savvy with ambitious shopping behaviours, the region is a flourishing hub for global retail & e-Commerce trade. Actionable insights and strategies Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions The event underscores the commitment to nurturing the growth of the Retail & e-commerce industry, a key driver of Indonesia’s economic transformation. Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions on topics such as omnichannel strategies, digital marketing trends, customer experience enhancement, and supply chain innovation. The conference aims to provide actionable insights and strategies to help businesses thrive in the competitive Southeast Asia market. Best practices and innovation "We're thrilled to create a platform where retail and e-commerce professionals from South East Asia can exchange insights, build connections, explore global best practices, and drive innovation in the retail & e-commerce sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving retail and e-commerce landscape." Some of the key topics of discussion Reconciling the Physical-Digital Paradox for Brands Leveraging Product Data for Competitive Edge in eCommerce Learning from the Tech Pioneers: Stories on Successful Turnarounds and Transformations From Bricks to Clicks: Mastering the art of Omnichannel Journeys for seamless customer experience Crafting powerful and differentiated CX
Teledyne FLIR OEM, part of Teledyne Technologies Incorporated announced the release of Prism™ Supervisor, the latest addition to its Prism-embedded software ecosystem. Prism Supervisor integrates drone autopilot flight control systems with real-time, AI-based observations at the edge to improve mission safety, efficiency, and performance, enhancing the capabilities of unmanned aircraft systems (UAS). Prism Supervisor software Prism Supervisor software empowers mission planners with a flexible programming framework and software development kit (SDK) to facilitate custom, intricate mission scenarios. During flight, Prism Supervisor adapts its autopilot functionality in real-time, dynamically generating mission segments and flight plans on the fly, minimising operator impact while improving mission success. For example, a Prism Supervisor-controlled UAV flying a search mission pattern can autonomously circle and alert the operator upon the detection of a human or threat. Operational performance "From behaviour and mission planning to dynamically adjust in-flight operations, Prism Supervisor represents a significant advancement for drone autonomy through AI," said Dan Walker, Vice President of Product Management, at Teledyne FLIR. "It improves operational performance via single-click missions, opening up new possibilities for UAS operation from commercial to military use cases." User-friendly GUI It can facilitate collaborative behaviours and synchronised mission execution among multiple UAVs Prism Supervisor simplifies the operator experience with a user-friendly graphic user interface (GUI) for mission planning, real-time mission visualisation, and execution. Available for desktop or mobile deployment supporting Windows, Linux, macOS, iOS, and Android, the supervised mission management application streams and records detailed, full-frame-rate video, path visualisation, and metadata. It can facilitate collaborative behaviours and synchronised mission execution among multiple unmanned aerial vehicles (UAVs). Advanced AI and image processing Prism Supervisor expands Teledyne FLIR's Prism digital ecosystem of advanced AI and image processing. It provides a platform for deploying object detection, tracking, and computational imaging on low-power processors, enhancing UAS mission performance and reducing development costs.
Cequence Security, a pioneer in API security and bot management announced significant momentum in the Middle East and Africa (MEA) region, driven by rapid customer adoption, strategic partnerships, and a strengthened leadership team. This expansion further solidifies Cequence’s position as the go-to API security and bot management provider in the region, addressing the growing demand for advanced threat protection and digital risk mitigation. Modern digital transformation “APIs are the backbone of modern digital transformation, but they are also the most exploited attack surface,” said Ameya Talwalkar, CEO of Cequence Security. “We are not just expanding—we are transforming how businesses defend their digital assets. As the only solution that provides data sovereignty in the region, we empower enterprises with AI-driven security tailored to their unique regulatory and threat landscapes. By combining innovative threat intelligence with proactive defence, we enable organisations to anticipate and mitigate attacks before they impact operations.” MEA expansion Cequence’s expansion in MEA has been marked by: 1) New customer acquisitions across financial services, telecommunications, oil and gas, and technology, securing organisations such as: A top Islamic bank in the UAE. One of the largest financial institutions in the Middle East and Africa. A major telecom provider in Turkey. A digital transformation pioneer in the energy sector. 2) A 193% increase in ARR in the MEA region year-over-year. 3) A 68% increase in partner deal registrations, demonstrating strong market demand for Cequence’s Unified API Protection (UAP) platform. 4) An 83% increase in reseller partnerships, spanning KSA, UAE, Qatar, Jordan, Kuwait, Bahrain, and Egypt. 5) The planned signing of a strategic Memorandum of Understanding (MOU) at LEAP 2025 with a strategic GTM partner, underscores Cequence’s commitment to regional cybersecurity initiatives. 6) Hiring for multiple positions across various departments in the region reinforces Cequence’s investment in local talent and its commitment to long-term growth in the MEA. Strategic leadership appointment Ismail brings a proven track record of driving business growth and forging strategic alliances To drive Cequence’s expansion in MEA, the company has appointed Mohammad Ismail as its new Head of Go-to-Market (GTM) & Sales for EMEA, strategically based in Dubai to accelerate regional growth and customer success. With over 25 years of experience in cybersecurity and enterprise IT across the Middle East, Africa, and Southeast Asia, Ismail brings a proven track record of driving business growth and forging strategic alliances. Reliance on APIs “My focus at Cequence is to strengthen our presence in the EMEA region by deepening relationships with customers and partners,” said Mohammad Ismail, Head of GTM & Sales for EMEA. “With the increasing adoption of the growing reliance on APIs to power digital services, organisations need robust API security and bot management solutions. I look forward to leveraging my experience to expand our footprint, provide strategic guidance, and help customers stay ahead of evolving cyber threats.” Customer success and industry validation Cequence’s platform has helped organisations across MEA overcome critical API security and bot management challenges. Customers have leveraged Cequence to: Secure APIs during open banking transitions, ensuring compliance and real-time protection for sensitive financial data. Enhance API governance and security testing, integrating seamlessly with CI/CD pipelines to enforce OWASP Top 10 protections. Detect and stop sophisticated API attacks with AI-driven threat detection and real-time behavioral analysis, mitigating risks from shadow APIs and automated threats. Improve visibility and response times with comprehensive API activity monitoring, automated security enforcement, and automated enforcement with no human intervention. Meet stringent data sovereignty requirements, ensuring security policies remain within customer-controlled environments. These capabilities combined with Cequence’s unified approach, continue to drive strong adoption among MEA enterprises seeking to protect their digital environments. Investor confidence and market leadership Cequence’s expansion in MEA has garnered continued support from investors Cequence’s expansion in MEA has garnered continued support from investors, including Prosperity7 Ventures and Sanabil Investments. “The Middle East presents a unique and fast-growing opportunity for cybersecurity innovation, and Cequence is pioneering the charge with its best-in-class API security solutions,” said Abhishek Shukla, managing director and head of North America at Prosperity7 Ventures. “With an experienced leadership team, strong regional partnerships, and a relentless focus on innovation, Cequence is well-positioned to drive continued success in the MEA market.” Commitment to innovation As part of its ongoing commitment to innovation, Cequence has introduced new capabilities tailored to the MEA market, including: Expanded cloud and on-premises deployment options, ensuring compliance with regional data sovereignty requirements. Enhanced partner enablement programs, equipping resellers and service providers with advanced API security expertise. Protecting digital assets “With API threats growing more sophisticated, we remain focused on delivering cutting-edge security solutions that empower organisations to stay ahead of attackers,” added Talwalkar. “Our investment in MEA reflects our dedication to supporting businesses with the tools they need to protect their digital assets and maintain trust with their customers.” LEAP 2025 Cequence will be at Stand H1.D30 during LEAP 2025. Stop by to meet the team and learn more about how the industry-pioneering API security and bot management solutions can help protect the digital ecosystem. Join Ameya Talwalkar, CEO of Cequence, as he discusses the evolving API security and bot management landscape. His session will cover emerging threats, regional trends, and strategies for mitigating cyber risks. When: 7:30 PM - 7:50 PM Where: Stand H1.D30
Indonesia is set to host the most anticipated 10th NXT CX-DX Summit & Awards which will explore the intersection of Customer Experience (CX) and Digital Transformation, bringing together industry pioneers, innovators, and decision-makers to discuss strategies for driving business growth in the digital age. Scheduled on the 11th of February 2025 at JW Marriott in Jakarta, Indonesia the summit will feature insights from global thought pioneers, successful case studies, and practical strategies for organisations to navigate and excel in an increasingly digital world. AI, big data, and automation As Indonesia accelerates its digital transformation, businesses face an urgent need to align customer experiences with rapidly evolving technological developments. The conference will feature insightful keynote speeches, interactive panel discussions, and effective networking sessions led by global and regional experts. Attendees will gain actionable insights into leveraging artificial intelligence, data analytics, and emerging technologies to drive customer satisfaction, loyalty, and business growth. Seamless, personalised experiences The summit will spotlight how digital tools and emerging technologies like AI, big data, and automation This one-day event aims to address the urgent need for businesses to enhance customer engagement and deliver seamless, personalised experiences in a highly competitive market. With Indonesia's digital economy poised to reach USD 130 billion by 2025, the summit will spotlight how digital tools and emerging technologies like AI, big data, and automation are reshaping customer interactions across industries. CX & DX landscape This summit will bring together 150+ key decision makers and will discuss the key areas of interest in Customer Experience and Digital transformation across different industry verticals to showcase how technological deployment has transformed the overall CX & DX landscape in Indonesia. "We are excited to create a platform where CX & DX Professionals from Indonesia and South East Asia on the whole, discuss the global best practices when it comes to the effective deployment of innovative strategies," shared by Mr. Jordan Abraham and Mr. Pradish Gireesan Co-Founders of Scribe Minds & Media. Digital transformation "In our upcoming initiative, we wish to deep dive into specific areas of customer experience and Digital Transformation." "Customer expectations are evolving faster than ever, and businesses must embrace digital transformation to not only meet these expectations but to anticipate and exceed them." 10th NXT CX-DX Summit and Awards Goutama Bachtiar, Director of IT Advisory, Grant Thornton Indonesia, mentioned, “The 10th NXT CX-DX Summit and Awards will stand as a beacon of innovation and excellence, where visionary ideas shape the future of customer and digital experiences." "It’s inspiring to witness how organisations continue to push the boundaries of engagement, leveraging technology and creativity to redefine possibilities. Look forward to celebrating these groundbreaking achievements and the brilliant minds driving them.” Sustainable and efficient digital government Kamal Farag, Digital Services Director from Human Resources Development Fund - HRDF – KSA said, “It is a pleasure to be part of the NextGen e-Governance Summit 2024." "Engaging with industry pioneers and sharing insights on the digital transformation journey in Saudi Arabia was truly inspiring. I look forward to contributing further to this vital initiative that supports our nation's vision for a sustainable and efficient digital government.” Valuable takeaways The event is open to professionals across industries including financial services, technology, retail, e-commerce, healthcare, and telecommunications. Whether visitors are C-level executives, marketing professionals, or tech enthusiasts, this conference offers valuable takeaways to elevate strategies and drive measurable results.
Saudi Arabia is set to host the highly anticipated BIGBOX KSA 2025, a Global retail & e-commerce series, an exclusive event bringing together thought pioneers, innovators, and stakeholders shaping the future of retail and e-commerce in the Kingdom and beyond. Scheduled to take place on the 18th of February 2025 in Riyadh, KSA, this landmark conference will provide a platform to explore transformative trends, cutting-edge technologies, and strategies driving growth in the digital marketplace. A global hub As Saudi Arabia continues to advance its Vision 2030 objectives, the conference aligns with the Kingdom's ambitions to diversify its economy and establish itself as a global hub for innovation. The retail and e-commerce sectors have experienced unprecedented growth, spurred by increased internet penetration, mobile usage, and a rapidly evolving consumer landscape. This event will spotlight the key opportunities and challenges shaping these dynamic sectors. Keynote speeches and panel discussions The conference aims to provide actionable insights and strategies to help businesses thrive The event underscores its commitment to nurturing the growth of the Retail & e-commerce industry, a key driver of the Kingdom’s economic transformation. Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions on topics such as omnichannel strategies, digital marketing trends, customer experience enhancement, and supply chain innovation. The conference aims to provide actionable insights and strategies to help businesses thrive in the competitive Middle Eastern market. Global best practices "We're thrilled to create a platform where retail and e-commerce professionals from the Middle East can exchange insights, build connections, explore global best practices, and drive innovation in the retail & e-commerce sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving retail and e-commerce landscape."
In Indonesia, cybersecurity stands as a critical concern, despite its relative insulation from global advanced persistent threats. Nevertheless, cyber-attacks persist, impacting citizens and government institutions alike. As businesses transition to digital platforms, the increased implementation of transformative technologies introduces a slew of security risks, endangering critical infrastructure and sensitive data. The Indonesia Cybersecurity market is projected to grow from US$ 2.05 billion in 2023 to US$ 3.39 billion by 2028. Indonesian Cybersecurity market The Indonesian Cybersecurity market is segmented into three areas: Offering (Security Type and Services), Deployment (Cloud, On-premises), and End User (BFSI, Healthcare, Manufacturing, Government & Defence, IT, and Telecommunication). Indonesia has the potential to boost its economic growth by $150 billion, equivalent to 10% of its Gross Domestic Product (GDP) by 2025 through the adoption of digital technology. Leadership approach This creates an immediate necessity for a new breed of experts, tasked with devising proactive security This surge in threats demands a reimagined leadership approach. With the expanding threat landscape and the growing complexity of safeguarding systems, there arises a pressing need for enhanced tools and highly skilled professionals to handle the same. This creates an immediate necessity of a new breed of experts, tasked with devising proactive security strategies to counter evolving threats. Adopting policies and strategies The summit will explore the imperative of adopting policies and strategies to foster a proactive cybersecurity stance. It will delve into the disruptive technologies reshaping cybersecurity, empowering enterprises to confront the novel risks inherent in digital ventures. Furthermore, the Summit will advocate for instilling a culture of information security across all institutions and organizations. At Secure Indonesia cybersecurity professionals will share insights and best practices for cultivating resilient and risk-averse digital enterprises. Some of the key topics Encouraging global cooperation in cyber governance. Connecting the Dots: Turning Threat Feeds into Actionable Intelligence. Securing the future: Integrating AI into information security. Navigating the cyber battlefield in Smart Cities: Challenges and Safeguards. CISO Safeguarding data security risks in today's digital era. Cybersecurity "We're thrilled to create a platform where Cyber security professionals across Southeast Asia can exchange insights, build connections, explore global best practices, and drive innovation in the cybersecurity sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving cybersecurity landscape."
Indonesia is set to host the highly anticipated BIGBOX INDONESIA 2025, a Global Retail & e-commerce Series, an exclusive event bringing together thought pioneers, innovators, and stakeholders shaping the future of retail and e-commerce in Indonesia. Scheduled to take place on the 18th of February 2025 in Jakarta Indonesia. This landmark conference will provide a platform to explore transformative trends, cutting-edge technologies, and strategies driving growth in the digital marketplace. Retail & e-Commerce hub Indonesia is spearheading the change in the region with the retail market expected to grow rapidly, projected to surpass USD 49.56 billion in revenue and 4.73% from 2024 to 2028. Also, Indonesia is anticipated to dominate more than 45% of the Southeast Asian e-commerce sector by 2025. The market's revenue is poised for consistent annual growth, with a projected CAGR of 10.41% from 2023 to 2027. Fuelled by an aspiring middle-class population, burgeoning tech-savvy with ambitious shopping behaviours, the region is a flourishing hub for global retail & e-Commerce trade. Actionable insights and strategies Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions The event underscores the commitment to nurturing the growth of the Retail & e-commerce industry, a key driver of Indonesia’s economic transformation. Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions on topics such as omnichannel strategies, digital marketing trends, customer experience enhancement, and supply chain innovation. The conference aims to provide actionable insights and strategies to help businesses thrive in the competitive Southeast Asia market. Best practices and innovation "We're thrilled to create a platform where retail and e-commerce professionals from South East Asia can exchange insights, build connections, explore global best practices, and drive innovation in the retail & e-commerce sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving retail and e-commerce landscape." Some of the key topics of discussion Reconciling the Physical-Digital Paradox for Brands Leveraging Product Data for Competitive Edge in eCommerce Learning from the Tech Pioneers: Stories on Successful Turnarounds and Transformations From Bricks to Clicks: Mastering the art of Omnichannel Journeys for seamless customer experience Crafting powerful and differentiated CX
Teledyne FLIR OEM, part of Teledyne Technologies Incorporated announced the release of Prism™ Supervisor, the latest addition to its Prism-embedded software ecosystem. Prism Supervisor integrates drone autopilot flight control systems with real-time, AI-based observations at the edge to improve mission safety, efficiency, and performance, enhancing the capabilities of unmanned aircraft systems (UAS). Prism Supervisor software Prism Supervisor software empowers mission planners with a flexible programming framework and software development kit (SDK) to facilitate custom, intricate mission scenarios. During flight, Prism Supervisor adapts its autopilot functionality in real-time, dynamically generating mission segments and flight plans on the fly, minimising operator impact while improving mission success. For example, a Prism Supervisor-controlled UAV flying a search mission pattern can autonomously circle and alert the operator upon the detection of a human or threat. Operational performance "From behaviour and mission planning to dynamically adjust in-flight operations, Prism Supervisor represents a significant advancement for drone autonomy through AI," said Dan Walker, Vice President of Product Management, at Teledyne FLIR. "It improves operational performance via single-click missions, opening up new possibilities for UAS operation from commercial to military use cases." User-friendly GUI It can facilitate collaborative behaviours and synchronised mission execution among multiple UAVs Prism Supervisor simplifies the operator experience with a user-friendly graphic user interface (GUI) for mission planning, real-time mission visualisation, and execution. Available for desktop or mobile deployment supporting Windows, Linux, macOS, iOS, and Android, the supervised mission management application streams and records detailed, full-frame-rate video, path visualisation, and metadata. It can facilitate collaborative behaviours and synchronised mission execution among multiple unmanned aerial vehicles (UAVs). Advanced AI and image processing Prism Supervisor expands Teledyne FLIR's Prism digital ecosystem of advanced AI and image processing. It provides a platform for deploying object detection, tracking, and computational imaging on low-power processors, enhancing UAS mission performance and reducing development costs.
Cequence Security, a pioneer in API security and bot management announced significant momentum in the Middle East and Africa (MEA) region, driven by rapid customer adoption, strategic partnerships, and a strengthened leadership team. This expansion further solidifies Cequence’s position as the go-to API security and bot management provider in the region, addressing the growing demand for advanced threat protection and digital risk mitigation. Modern digital transformation “APIs are the backbone of modern digital transformation, but they are also the most exploited attack surface,” said Ameya Talwalkar, CEO of Cequence Security. “We are not just expanding—we are transforming how businesses defend their digital assets. As the only solution that provides data sovereignty in the region, we empower enterprises with AI-driven security tailored to their unique regulatory and threat landscapes. By combining innovative threat intelligence with proactive defence, we enable organisations to anticipate and mitigate attacks before they impact operations.” MEA expansion Cequence’s expansion in MEA has been marked by: 1) New customer acquisitions across financial services, telecommunications, oil and gas, and technology, securing organisations such as: A top Islamic bank in the UAE. One of the largest financial institutions in the Middle East and Africa. A major telecom provider in Turkey. A digital transformation pioneer in the energy sector. 2) A 193% increase in ARR in the MEA region year-over-year. 3) A 68% increase in partner deal registrations, demonstrating strong market demand for Cequence’s Unified API Protection (UAP) platform. 4) An 83% increase in reseller partnerships, spanning KSA, UAE, Qatar, Jordan, Kuwait, Bahrain, and Egypt. 5) The planned signing of a strategic Memorandum of Understanding (MOU) at LEAP 2025 with a strategic GTM partner, underscores Cequence’s commitment to regional cybersecurity initiatives. 6) Hiring for multiple positions across various departments in the region reinforces Cequence’s investment in local talent and its commitment to long-term growth in the MEA. Strategic leadership appointment Ismail brings a proven track record of driving business growth and forging strategic alliances To drive Cequence’s expansion in MEA, the company has appointed Mohammad Ismail as its new Head of Go-to-Market (GTM) & Sales for EMEA, strategically based in Dubai to accelerate regional growth and customer success. With over 25 years of experience in cybersecurity and enterprise IT across the Middle East, Africa, and Southeast Asia, Ismail brings a proven track record of driving business growth and forging strategic alliances. Reliance on APIs “My focus at Cequence is to strengthen our presence in the EMEA region by deepening relationships with customers and partners,” said Mohammad Ismail, Head of GTM & Sales for EMEA. “With the increasing adoption of the growing reliance on APIs to power digital services, organisations need robust API security and bot management solutions. I look forward to leveraging my experience to expand our footprint, provide strategic guidance, and help customers stay ahead of evolving cyber threats.” Customer success and industry validation Cequence’s platform has helped organisations across MEA overcome critical API security and bot management challenges. Customers have leveraged Cequence to: Secure APIs during open banking transitions, ensuring compliance and real-time protection for sensitive financial data. Enhance API governance and security testing, integrating seamlessly with CI/CD pipelines to enforce OWASP Top 10 protections. Detect and stop sophisticated API attacks with AI-driven threat detection and real-time behavioral analysis, mitigating risks from shadow APIs and automated threats. Improve visibility and response times with comprehensive API activity monitoring, automated security enforcement, and automated enforcement with no human intervention. Meet stringent data sovereignty requirements, ensuring security policies remain within customer-controlled environments. These capabilities combined with Cequence’s unified approach, continue to drive strong adoption among MEA enterprises seeking to protect their digital environments. Investor confidence and market leadership Cequence’s expansion in MEA has garnered continued support from investors Cequence’s expansion in MEA has garnered continued support from investors, including Prosperity7 Ventures and Sanabil Investments. “The Middle East presents a unique and fast-growing opportunity for cybersecurity innovation, and Cequence is pioneering the charge with its best-in-class API security solutions,” said Abhishek Shukla, managing director and head of North America at Prosperity7 Ventures. “With an experienced leadership team, strong regional partnerships, and a relentless focus on innovation, Cequence is well-positioned to drive continued success in the MEA market.” Commitment to innovation As part of its ongoing commitment to innovation, Cequence has introduced new capabilities tailored to the MEA market, including: Expanded cloud and on-premises deployment options, ensuring compliance with regional data sovereignty requirements. Enhanced partner enablement programs, equipping resellers and service providers with advanced API security expertise. Protecting digital assets “With API threats growing more sophisticated, we remain focused on delivering cutting-edge security solutions that empower organisations to stay ahead of attackers,” added Talwalkar. “Our investment in MEA reflects our dedication to supporting businesses with the tools they need to protect their digital assets and maintain trust with their customers.” LEAP 2025 Cequence will be at Stand H1.D30 during LEAP 2025. Stop by to meet the team and learn more about how the industry-pioneering API security and bot management solutions can help protect the digital ecosystem. Join Ameya Talwalkar, CEO of Cequence, as he discusses the evolving API security and bot management landscape. His session will cover emerging threats, regional trends, and strategies for mitigating cyber risks. When: 7:30 PM - 7:50 PM Where: Stand H1.D30
Indonesia is set to host the most anticipated 10th NXT CX-DX Summit & Awards which will explore the intersection of Customer Experience (CX) and Digital Transformation, bringing together industry pioneers, innovators, and decision-makers to discuss strategies for driving business growth in the digital age. Scheduled on the 11th of February 2025 at JW Marriott in Jakarta, Indonesia the summit will feature insights from global thought pioneers, successful case studies, and practical strategies for organisations to navigate and excel in an increasingly digital world. AI, big data, and automation As Indonesia accelerates its digital transformation, businesses face an urgent need to align customer experiences with rapidly evolving technological developments. The conference will feature insightful keynote speeches, interactive panel discussions, and effective networking sessions led by global and regional experts. Attendees will gain actionable insights into leveraging artificial intelligence, data analytics, and emerging technologies to drive customer satisfaction, loyalty, and business growth. Seamless, personalised experiences The summit will spotlight how digital tools and emerging technologies like AI, big data, and automation This one-day event aims to address the urgent need for businesses to enhance customer engagement and deliver seamless, personalised experiences in a highly competitive market. With Indonesia's digital economy poised to reach USD 130 billion by 2025, the summit will spotlight how digital tools and emerging technologies like AI, big data, and automation are reshaping customer interactions across industries. CX & DX landscape This summit will bring together 150+ key decision makers and will discuss the key areas of interest in Customer Experience and Digital transformation across different industry verticals to showcase how technological deployment has transformed the overall CX & DX landscape in Indonesia. "We are excited to create a platform where CX & DX Professionals from Indonesia and South East Asia on the whole, discuss the global best practices when it comes to the effective deployment of innovative strategies," shared by Mr. Jordan Abraham and Mr. Pradish Gireesan Co-Founders of Scribe Minds & Media. Digital transformation "In our upcoming initiative, we wish to deep dive into specific areas of customer experience and Digital Transformation." "Customer expectations are evolving faster than ever, and businesses must embrace digital transformation to not only meet these expectations but to anticipate and exceed them." 10th NXT CX-DX Summit and Awards Goutama Bachtiar, Director of IT Advisory, Grant Thornton Indonesia, mentioned, “The 10th NXT CX-DX Summit and Awards will stand as a beacon of innovation and excellence, where visionary ideas shape the future of customer and digital experiences." "It’s inspiring to witness how organisations continue to push the boundaries of engagement, leveraging technology and creativity to redefine possibilities. Look forward to celebrating these groundbreaking achievements and the brilliant minds driving them.” Sustainable and efficient digital government Kamal Farag, Digital Services Director from Human Resources Development Fund - HRDF – KSA said, “It is a pleasure to be part of the NextGen e-Governance Summit 2024." "Engaging with industry pioneers and sharing insights on the digital transformation journey in Saudi Arabia was truly inspiring. I look forward to contributing further to this vital initiative that supports our nation's vision for a sustainable and efficient digital government.” Valuable takeaways The event is open to professionals across industries including financial services, technology, retail, e-commerce, healthcare, and telecommunications. Whether visitors are C-level executives, marketing professionals, or tech enthusiasts, this conference offers valuable takeaways to elevate strategies and drive measurable results.
Saudi Arabia is set to host the highly anticipated BIGBOX KSA 2025, a Global retail & e-commerce series, an exclusive event bringing together thought pioneers, innovators, and stakeholders shaping the future of retail and e-commerce in the Kingdom and beyond. Scheduled to take place on the 18th of February 2025 in Riyadh, KSA, this landmark conference will provide a platform to explore transformative trends, cutting-edge technologies, and strategies driving growth in the digital marketplace. A global hub As Saudi Arabia continues to advance its Vision 2030 objectives, the conference aligns with the Kingdom's ambitions to diversify its economy and establish itself as a global hub for innovation. The retail and e-commerce sectors have experienced unprecedented growth, spurred by increased internet penetration, mobile usage, and a rapidly evolving consumer landscape. This event will spotlight the key opportunities and challenges shaping these dynamic sectors. Keynote speeches and panel discussions The conference aims to provide actionable insights and strategies to help businesses thrive The event underscores its commitment to nurturing the growth of the Retail & e-commerce industry, a key driver of the Kingdom’s economic transformation. Attendees can look forward to a dynamic agenda, featuring keynote speeches and panel discussions on topics such as omnichannel strategies, digital marketing trends, customer experience enhancement, and supply chain innovation. The conference aims to provide actionable insights and strategies to help businesses thrive in the competitive Middle Eastern market. Global best practices "We're thrilled to create a platform where retail and e-commerce professionals from the Middle East can exchange insights, build connections, explore global best practices, and drive innovation in the retail & e-commerce sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving retail and e-commerce landscape."
In Indonesia, cybersecurity stands as a critical concern, despite its relative insulation from global advanced persistent threats. Nevertheless, cyber-attacks persist, impacting citizens and government institutions alike. As businesses transition to digital platforms, the increased implementation of transformative technologies introduces a slew of security risks, endangering critical infrastructure and sensitive data. The Indonesia Cybersecurity market is projected to grow from US$ 2.05 billion in 2023 to US$ 3.39 billion by 2028. Indonesian Cybersecurity market The Indonesian Cybersecurity market is segmented into three areas: Offering (Security Type and Services), Deployment (Cloud, On-premises), and End User (BFSI, Healthcare, Manufacturing, Government & Defence, IT, and Telecommunication). Indonesia has the potential to boost its economic growth by $150 billion, equivalent to 10% of its Gross Domestic Product (GDP) by 2025 through the adoption of digital technology. Leadership approach This creates an immediate necessity for a new breed of experts, tasked with devising proactive security This surge in threats demands a reimagined leadership approach. With the expanding threat landscape and the growing complexity of safeguarding systems, there arises a pressing need for enhanced tools and highly skilled professionals to handle the same. This creates an immediate necessity of a new breed of experts, tasked with devising proactive security strategies to counter evolving threats. Adopting policies and strategies The summit will explore the imperative of adopting policies and strategies to foster a proactive cybersecurity stance. It will delve into the disruptive technologies reshaping cybersecurity, empowering enterprises to confront the novel risks inherent in digital ventures. Furthermore, the Summit will advocate for instilling a culture of information security across all institutions and organizations. At Secure Indonesia cybersecurity professionals will share insights and best practices for cultivating resilient and risk-averse digital enterprises. Some of the key topics Encouraging global cooperation in cyber governance. Connecting the Dots: Turning Threat Feeds into Actionable Intelligence. Securing the future: Integrating AI into information security. Navigating the cyber battlefield in Smart Cities: Challenges and Safeguards. CISO Safeguarding data security risks in today's digital era. Cybersecurity "We're thrilled to create a platform where Cyber security professionals across Southeast Asia can exchange insights, build connections, explore global best practices, and drive innovation in the cybersecurity sector," said Mr. Jordan Abraham and Mr. Pradish Gireesan, Co-Founders of Scribe Minds & Media. "This conference is essential for anyone aiming to stay ahead in the rapidly evolving cybersecurity landscape."


Expert commentary
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realise, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionising the overnight security business. Minimising criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilises a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimise the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is remote guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilises a combination of methods to effectively analyse potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyse the situation in real-time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command centre, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customised remote guarding When properly deployed, remote guarding systems are also customised to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional security shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A bounty of benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
Daniel May of Consort reviews the integration of access control systems in healthcare settings, outlining the benefits and key considerations decision-makers must make throughout product specifications. From patient safety and traversal to the protection of sensitive data and pharmaceuticals, healthcare environments are faced with several operational challenges. And where security remains at the forefront of decision-making, modern access control systems may often hold the answers. Physical security systems Hospitals in particular have developed into multi-faceted spaces that house hundreds to thousands of patients, staff and visitors at any one time. In England for example, research has found in the three months leading to June 2023, an average of 44,626 people visited major hospital A&E departments each day, with over 16 million attendances typically recorded over the course of a year-not to mention an additional nine million logged at other minor units. For any building, this level of sustained footfall can request severe security difficulties For any building, this level of sustained footfall can invite severe security tests. With that, the need to deploy effective physical security systems in healthcare is clear. And so, as access control continues to become more readily adopted and new products enter the market, decision-makers are reminded to consider the requirements of their building, ensuring they select the solutions most suited to their settings and budget. Security controlled Patient safety will always remain the top priority in healthcare settings, and where matters of health and social care come into question, a diverse set of professional regulatory bodies are tasked with setting and maintaining high standards. When it comes to healthcare premises specifically, patient security and perimeter security often come hand in hand and are amongst the most pressing of challenges that decision-makers must face. To help address operational planning and potential design concerns in the NHS, the Health Building Note (HBN), provides general design guidance for healthcare buildings under HBN 00-01-citing the use of access control measures as a way of maintaining security and protecting the safety of patients, staff and visitors. Use of access control Hospital buildings control varied levels of access for a number of security purposes Hospital buildings, for example, must control varied levels of access for a number of operational and security purposes. Routine scenarios exist where vulnerable patients are under monitoring and thus refrained from exiting the premises for their own safety, while at the same time, permitted staff must be able to reach their patients and medicines when required. For this, the use of access control is key. Equally, access credentials can also help management teams keep track of those who may be entering or exiting rooms with equipment and pharmaceutical supplies, deterring any unwanted visitors and opportunists in the process. Incorporation of access control systems On a similar note, regulations have set a minimum standard for how personal data should be stored and managed in healthcare environments, giving decision-makers an added responsibility to regulate staff-controlled areas with patient medical records. While instances of personal data breaches are rare, healthcare facilities and professionals are at legal risk should confidential data be found misused or missing. As such, the incorporation of access control systems has become essential in keeping data storage areas secure, with intuitive online systems capable of permitting access to staff with the correct credentials while simultaneously tracking who has requested clearance at digital entry points. HBN guidance Healthcare experts are better fitted to control the sheer volume of people entering and exiting To function effectively, healthcare facilities must always be perceived as safe places by the people who reside within them, and as HBN guidance implies, a unified physical security system can help address key safety and security concerns while enhancing patient and staff experience. Opportunely, access control systems are more accessible and adaptable than ever and combine several technologies such as mechanical locks and automatic doors with electronic access credentials in the form of smartphone apps, badge readers and biometric scanners. By integrating these systems into the building’s existing infrastructure, healthcare professionals are better equipped to control the sheer volume of people entering and exiting the premises without impairing the general flow of movement and coordination around the facility. Better by design Despite the clear benefits offered to healthcare facilities, there are a number of considerations to be mindful of when choosing an access control solution. Poorly implemented systems can have an adverse effect on security and functionality - quickly costing healthcare organisations time and budget to rectify and replace the inadequate products that don’t meet the building’s requirements. For that reason, decision-makers and design teams are reminded that there is no single solution that fits all healthcare buildings. As such, it’s crucial for decision-makers to understand the systems that are being put in place throughout each of the touchpoints in their facility. Clear collaboration is required during periods of specification, where together, teams can ensure the selected product works on all angles, from meeting fire safety and sustainability standards to aesthetics and scalability. Modern access control products Scalability is a key area that decision-makers must review when selecting access control systemsFrequently overlooked, scalability is a key area that decision-makers must review when selecting access control systems. Such is their diverse nature; healthcare facilities can often change and develop as years go by, and by selecting a system that facilitates growth, such as a cloud-based solution-security and efficiency is long-established. While modern access control products are known for seamless integration, there are some systems that may restrict the ability to use different vendors throughout the remainder of the building’s infrastructure. This, in effect, causes a monopolisation of products throughout the estate, which can have an adverse effect on growth by increasing costs and reducing the levels of service associated with the security system already in place. Improve security and safety A scalable and reliable access control system will continue to improve security and safety by adapting to a building’s new requirements-and all while having minimal impact on its operational network. And so, while technology will no doubt continue to influence and transform the access control market, healthcare facilities and their professionals must continue to remain educated on their own systems, ensuring they have the best options in place to keep their patients, staff and visitors safe and secure for years to come.
Global transportation networks are becoming increasingly interconnected, with digital systems playing a crucial role in ensuring the smooth operation of ports and supply chains. However, this reliance on technology can also create vulnerabilities, as demonstrated by the recent ransomware attack on Nagoya Port. As Japan's busiest shipping hub, the port's operations were brought to a standstill for two days, highlighting the potential for significant disruption to national economies and supply chains. Transportation sector The attack began with the port's legacy computer system, which handles shipping containers, being knocked offline. This forced the port to halt the handling of shipping containers that arrived at the terminal, effectively disrupting the flow of goods. The incident was a stark reminder of the risks associated with the convergence of information technology (IT) and operational technology (OT) in ports and other critical infrastructures. This is not an isolated incident, but part of a broader trend of escalating cyber threats targeting critical infrastructure. The transportation sector must respond by bolstering its defences, enhancing its cyber resilience, and proactively countering these threats. The safety and efficiency of our transportation infrastructure, and by extension our global economy, depend on it. Rising threat to port security and supply chains XIoT, from sensors on shipping containers to automatic cranes, are vital to trendy port functions OT, once isolated from networked systems, is now increasingly interconnected. This integration has expanded the attack surface for threat actors. A single breach in a port's OT systems can cause significant disruption, halting the movement of containers and impacting the flow of goods. This is not a hypothetical scenario, but a reality that has been demonstrated in recent cyberattacks on major ports. Adding another layer of complexity is the extended Internet of Things (XIoT), an umbrella term for all cyber-physical systems. XIoT devices, from sensors on shipping containers to automated cranes, are now integral to modern port operations. These devices are delivering safer, more efficient automated vehicles, facilitating geo-fencing for improved logistics, and providing vehicle health data for predictive maintenance. XIoT ecosystem However, the XIoT ecosystem also presents new cybersecurity risks. Each connected device is a potential entry point for cybercriminals, and the interconnected nature of these devices means that an attack on one, which can move laterally and can have a ripple effect throughout the system. The threat landscape is evolving, with cybercriminals becoming more sophisticated and their attacks more damaging with a business continuity focus. The growing interconnectivity between OT and XIoT in port operations and supply chains is also presenting these threat actors with a greater attack surface. Many older OT systems were never designed to be connected in this way and are unlikely to be equipped to deal with modern cyber threats. Furthermore, the increasing digitisation of ports and supply chains has led to a surge in the volume of data being generated and processed. This data, if not properly secured, can be a goldmine for cybercriminals. The potential for data breaches adds another dimension to the cybersecurity challenges facing the transportation sector. Role of cyber resilience in protecting service availability Cyber resilience refers to organisation's ability to prepare for, respond to, and recover from threats As the threats to port security and supply chains become increasingly complex, the concept of cyber resilience takes on a new level of importance. Cyber resilience refers to an organisation's ability to prepare for, respond to, and recover from cyber threats. It goes beyond traditional cybersecurity measures, focusing not just on preventing attacks, but also on minimising the impact of attacks that do occur and ensuring a quick recovery. In the context of port operations and supply chains, cyber resilience is crucial. The interconnected nature of these systems means that a cyberattack can have far-reaching effects, disrupting operations not just at the targeted port, but also at other ports and throughout the supply chain. A resilient system is one that can withstand such an attack and quickly restore normal operations. Port operations and supply chains The growing reliance on OT and the XIoT in port operations and supply chains presents unique challenges for cyber resilience. OT systems control physical processes and are often critical to safety and service availability. A breach in an OT system can have immediate and potentially catastrophic physical consequences. Similarly, XIoT devices are often embedded in critical infrastructure and can be difficult to patch or update, making them vulnerable to attacks. Building cyber resilience in these systems requires a multi-faceted approach. It involves implementing robust security measures, such as strong access controls and network segmentation, to prevent attacks. It also involves continuous monitoring and detection to identify and respond to threats as they occur. But perhaps most importantly, it involves planning and preparation for the inevitable breaches that will occur, ensuring that when they do, the impact is minimised, and normal operations can be quickly restored. Building resilience across port security and supply chains In the face of cyber threats, the transport sector must adopt a complete method of cybersecurity In the face of escalating cyber threats, the transportation sector must adopt a comprehensive approach to cybersecurity. This involves not just implementing robust security measures, but also fostering a culture of cybersecurity awareness and compliance throughout the organisation. A key component of a comprehensive cybersecurity strategy is strong access controls. This involves ensuring that only authorised individuals have access to sensitive data and systems. It also involves implementing multi-factor authentication and regularly reviewing and updating access permissions. Strong access controls can prevent unauthorised access to systems and data, reducing the risk of both internal and external threats. Network segmentation Network segmentation is another crucial measure. By dividing a network into separate segments, organisations can limit the spread of a cyberattack within their network. This can prevent an attack on one part of the network from affecting the entire system. Network segmentation also makes it easier to monitor and control the flow of data within the network, further enhancing security. Regular vulnerability assessments and patch management are also essential. Vulnerability assessments involve identifying and evaluating potential security weaknesses in the system, while patch management involves regularly updating and patching software to fix these vulnerabilities. These measures can help organisations stay ahead of cybercriminals and reduce the risk of exploitation. EU’s NIS2 Directive EU’s NIS2 Directive came into effect, and member states have until October 2024 to put it into law The transportation sector must also be prepared for greater legislative responsibility in the near future. The EU’s NIS2 Directive recently came into effect, and member states have until October 2024 to put it into law. The Directive aims to increase the overall level of cyber preparedness by mandating capabilities such as Computer Security Incident Response Teams (CSIRTs). Transport is among the sectors labelled as essential by the bill, meaning it will face a high level of scrutiny. Getting to grips with the complexities of XIoT and OT integration will be essential for organisations to achieve compliance and avoid fines. Global transportation infrastructure Finally, organisations must prepare for the inevitable breaches that will occur. This involves developing an incident response plan that outlines the steps to be taken in the event of a breach. It also involves regularly testing and updating this plan to ensure its effectiveness. A well-prepared organisation can respond quickly and effectively to a breach, minimising its impact and ensuring a quick recovery. In conclusion, mastering transportation cybersecurity requires a comprehensive, proactive approach. It involves implementing robust technical measures, fostering a culture of cybersecurity awareness, and preparing for the inevitable breaches that will occur. By taking these steps, organisations can enhance their cyber resilience, protect their critical operations, and ensure the security of our global transportation infrastructure.
Security beat
Companies at GSX 2023 emphasised new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasises ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the mid-market to the cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for the pure cloud, but there are benefits to be realised from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realise the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘soft’ features for integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organisation more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organisation more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centres around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasising performance, protection (cybersecurity), and price, their data centres are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring centre where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
A pioneer in the access control sector since 1971, AMAG Technology is looking to the future and the next generation of products that will expand its services to customers. “In our vision, we have advanced approaches that will not only provide our partners with advanced technologies but also ones that are easier to install with tools to expand their services,” says David Sullivan, who was appointed President of the venerable access control company in September 2022. New challenges at AMAG Sullivan brings a new outlook to the AMAG business, a part of Allied Universal, and a new vision to lead the company into the future. We caught up with David Sullivan to discuss his new challenges at AMAG and the journey ahead as the company looks to the future. Q: How does your background inform your approach to leading AMAG? I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry David Sullivan: With the exception of only a few short years, my career has been in access control. I have experience with several systems and have had the privilege to manage several successful access control companies. As a result, I bring a great deal of experience into my role at AMAG. I believe that it helps me to define a vision for AMAG that will be unique and on the leading edge of our industry. Q: How would you describe AMAG’s journey over the last several years and how do you see the future? Sullivan: Prior presidents of AMAG always shared their leadership vision and direction with senior leaders located in the United Kingdom. This had an impact on the full direction of the business, sometimes limiting its ultimate success. Before I became a part of AMAG, these senior leaders that were located in the UK retired, placing for the first time the full management responsibilities of the president. This has allowed me to integrate the business into a single team, with single objectives, and a single vision. We expect to begin to reveal this new vision in the coming weeks. We are excited about the future of AMAG and believe we will surprise the industry with our new products and approach in the coming months and years. Q: How important is it that a manufacturer provides both hardware and software solutions? How does AMAG’s approach (in general) differentiate it in the market? We can design the complete solution, providing functionality that others may find more difficult to accomplish Sullivan: Regardless of the manufacturer, we all provide hardware and software. An access control solution is not complete without both. Some of us choose to make our panels, and others do not. Those who are dependent on third-party suppliers are restricted to the developments and direction of that company, and while it might be perceived to be an open technology, it still is proprietary to the hardware manufacturer. AMAG has controlled its manufacturing of panels from day one. The result means that we can design the complete solution, providing functionality that others may find more difficult to accomplish. Q: How does the breadth of AMAG’s product suite provide advantages to customers and/or integrators? Sullivan: AMAG’s product portfolio is unique and provides the end user with an end-to-end identity management solution from one company. Our Control Room PSIM, Symmetry CONNECT Identity Management Solution, Symmetry Access Control, and Symmetry GUEST solutions all integrate to provide the user with a broad set of features and capabilities from a single provider. There is no finger-pointing when we come to support your system. We hold full responsibility for making it work and can quickly provide a resolution to any application difficulties the user may be experiencing. Q: How does AMAG address the divide between on-prem and cloud systems? How do you help customers make the transition and/or plan for the future? We are in the early stages of developing our next generation of access control in which we intend to provide on-prem Sullivan: In our current product portfolio, we have three products that are cloud-based. Our mobile credential platform (Symmetry Mobile), our visitor management solution (Symmetry GUEST), and our physical identity and access management solution (Symmetry CONNECT) are all offerings that operate in the cloud. We are in the early stages of developing our next generation of access control in which we intend to provide on-prem, web client, and cloud-based offerings. One of the primary objectives is to ensure that the large installed base of systems that are out there today will be able to migrate not only to our next generation but as well to the cloud if the client so desires. Q: What is AMAG’s approach to mobile credentialing? Sullivan: As an access control provider, adding Symmetry Mobile credentialing to our portfolio just made sense. We want our customers to have a forward-thinking solution with the opportunity to save money not only on the physical badges but the cost of printing and distributing badges. Mobile credentials can be easily issued and revoked remotely, reducing administrative overhead, and eliminating the need for physical inventory management. Organisations can centrally configure what devices are used and the read range for each type of device and operating system, thus providing flexibility. Symmetry Mobile offers a customised questionnaire that controls access and reduces liabilities. Q: What has surprised you the most in your first year or so leading AMAG? Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company Sullivan: I wouldn’t say I was surprised by this as much as happy to see, but I would say that the quality of our people was a pleasant surprise. As well, the AMAG product offering is broad and has some unique elements. When coupled with the depth of the resources that we have in AMAG, I know that we are second to none. Not many companies are blessed with such a broad portfolio that is supported by a resource-rich company that has so many talented people. Q: Please describe your dealer channel, and how you are seeking to expand it. Sullivan: The AMAG products are sophisticated and typically are installed for higher-end applications. With this sophistication comes a need to be well able to install such a solution. We have a strong group of certified and loyal partners who help us to deliver these enterprise solutions. We desire to provide our existing partners with updated and competitive systems to offer to their end users. Q: What is the security industry’s (and/or AMAG’s) biggest challenge in the next five years? We need to find ways to provide both our channel partners and the customers with solutions that are easily integrated Sullivan: I believe that the advancements that we are seeing in technology provide our industry with the opportunity to truly change how security is provided to our collective customers. As we advance these solutions, we will need to do so responsibly and in a way that helps the channel’s abilities. We need to find ways to train our partners to both install and support these more complex solutions. At the same time, we need to find ways to provide both our channel partners and the customers with solutions that are easily integrated, moving away from proprietary closed systems to open and cohesive solutions. This will ensure that the users get the best, and most complete solutions. Q: What does the industry as a whole misunderstand about AMAG -- time to set the record straight! Sullivan: Well, I am not ready to openly share where we are heading. We are in the process of putting together some advanced approaches to how we will do business with our partners. We are focused on providing tools that will enhance their services to their customers, and with products that are leading edge. I can only state that all should keep their eyes on AMAG, because over the next few years, we are going to surprise some people, and more importantly make our loyal partners quite powerful.
New buzzwords were abundant in the articles that generated the most clicks on our website in 2022. From the metaverse to the Internet of Things, from frictionless access control to artificial intelligence (AI), the topics most popular among our site’s visitors were at the cutting edge of change and innovation in the physical security marketplace. Here is a review of the Top 10 Articles of 2022, based on reader clicks, including links to the original content: Metaverse will promote collaboration and enable more efficiencies for security Metaverse is a familiar buzzword currently, but few people grasp what it means. In the simplest terms, the metaverse is an online “place” where physical, virtual, and augmented realities are shared. The term, Metaverse, suggests a more immersive online environment that combines elements of augmented reality (AR) and virtual reality (VR). For the physical security industry, the looming creation of a complex online environment offers possibilities and challenges. Establishing identity will be a central principle of the metaverse, and various biometrics are at the core of ensuring the identity of someone interacting in the virtual world. Cybersecurity elements are also key. On the benefits side, the security market is already taking advantage of technologies related to the eventual evolution of the metaverse. For example, the industry has deployed AR to provide information about a door lock’s status on a screen, headset, or smart glasses as a patrolling guard walks by. What are the security challenges of the transportation industry? Because transit agencies rely on several IoT devices, they get exposed to higher cybersecurity risks Rapid technological advancement, increasing urbanisation, and the growing expectations of commuters and governments are pressuring transit industry players to modernise. Commuters, urban planners, first responders, and other stakeholders want to use transit data to support their decision-making. Transit agencies’ security and operations teams need closer collaboration to stay ahead. However, for many years, most transit agencies have relied on siloed, proprietary systems. Because transit agencies rely on an ever-growing number of Internet of Things (IoT) devices, they also get exposed to higher cybersecurity risks as there are more network access points to manage. The future is here: ADT’s innovation lab evaluating robots and indoor drones New robots and indoor drones for security applications are on the horizon, based on the work of ADT Commercials’ Innovation Lab, which is evaluating the latest technologies’ value to customers and some typical use cases. The ideal use of humanoid robots is to perform jobs that are considered repetitive, dirty, dangerous, and/or mundane. In security, that describes most security guard positions. As the name implies, autonomous indoor drones are focused on flying indoors versus the outdoor environment, which is heavily regulated by the U.S. Federal Aviation Administration (FAA). Flying autonomously indoors not only eliminates FAA oversight but also will enable ADT Commercial to offer another choice to customers to further reduce their dependencies on and costs of human guards. Innovative security: the key to business efficiency, cost savings, and more Organisations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend. More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organisations looking to drive higher productivity and profitability margins should consider security upgrades that prioritise integrated analytics and automation. Shoplifting today is more sophisticated, and so are the tools to fight it One tool to fight shoplifting is analytics, which can be used to determine where shrink is occurring Shoplifting is often viewed as petty theft by individuals, but that is not always the case. Overall, shoplifting is becoming more sophisticated and coordinated. Traditional “shoplifting” has two major differences when compared to organised retail crime (ORC). The differences are numbers and motivation. ORC consists of groups working together to monetise theft, very different than an individual taking an item they need. One tool to fight to shoplift is analytics, which can be used to determine where shrink is occurring. Understanding where crimes take place helps retailers make strategic decisions about where to place their loss prevention efforts. Oosto offers 10 reasons to switch to frictionless access control in commercial buildings Access control for buildings is nothing new. It’s only in recent years that the urgency to implement smarter, more efficient, and more convenient forms of access control has increased, in the context of public and private sector digital transformation. Upheavals from the COVID-19 pandemic have forced organisations to re-think, pivot, and invest in new technology solutions that will incorporate Artificial Intelligence (AI) and Machine Learning, to gain speed in their operations, glean actionable insights from their video analytics, and enhance productivity with their teams. Which security trend is here to stay? Technologies and trends in the security marketplace come and go with some regularity. But how can you tell which trends are gaining traction and which amount to “the flavor of the month.” For example, while many physical security departments were hesitant to consider cloud-connected solutions in the past, they now better understand the benefits these solutions bring and how they can help them utilize their resources to achieve business goals while minimising overall operational complexity. Other technologies mentioned in the article include mobile credentials, AI-based analytics, video management systems, cybersecurity, and a new emphasis on data. What do these technology trends have in common? They are opening new possibilities for greater system efficiency and functionality. In short, they are playing a role in transforming our industry. GSX 2022 reflects changing technologies and evolving role of security The role of the security director increasingly will encompass facets of cybersecurity and physical security GSX 2022 in Atlanta highlighted the changing role of security in the enterprise. The role of the security director increasingly will encompass facets of cybersecurity as well as physical security. Transitioning to an operation that incorporates both disciplines requires a workforce that embraces education and building new skills. Education and the opportunity to build new skills are evident everywhere at GSX, including in the hundreds of education sessions and also in the knowledge shared on the show floor in the exhibit hall. Consolidation changing the face of the security market Consolidation is a dominant trend in the security marketplace. Large companies typically swallow up smaller companies as a means of expanding both their technology portfolios and their geographic reach. Sometimes a big fish is swallowed up by an even bigger fish. Despite the pandemic and resulting economic challenges, the security market has continued to be a desirable environment for both big players and startups, which then provide abundant acquisition targets for larger companies. This article highlighted recent mergers and acquisition news. Six trends at the intersection of video and AI Video has evolved beyond the capabilities of advanced imaging and performance to include another level: Artificial Intelligence. Video imaging technology combines with AI, delivers a wealth of new data, not just for traditional physical security applications, but for a much deeper analysis of past, present, and even future events across the enterprise. This is more than a big development for the physical security industry; it is a monumental paradigm shift that is changing how security system models are envisioned, designed, and deployed. Much of the heightened demand for advanced video analytics is being driven by six prevalent industry trends.
Case studies
In any construction project, meticulous recording and management of door hardware is critical —although often prone to human error. What if there was a way to harness digital technology to fulfil this crucial requirement in a dependable, efficient, agile way? Located in several cities around India, Edifice Consultants Pvt Ltd. specialises in designing climate-responsive architectural structures that harmonise with their surroundings. Complex standards and regulations Each project undertaken reflects Edifice’s collaborative ethos and dedication to enhance the immediate environment, while fostering the well-being of building users, local residents, and the landscape. Edifice’s work across commercial, residential, industrial and public service sectors has received multiple prestigious awards. Designing buildings for so many segments and industries requires broad and deep knowledge of complex standards and regulations. The experience and expertise of ASSA ABLOY have proved invaluable. Specification with Openings Studio™ ASSA ABLOY has provided Edifice with solutions for more than 750 fire-rated and non-fire doors To streamline door specification, Edifice requires digital software that can cut manual mistakes and maintain the process’s accuracy, which is essential to efficient building design. Their chosen solution — Openings Studio™ — takes a rigorous approach, speeding up specification iterations to condense the revision cycle, improve time management and help hit Edifice’s ambitious project timelines. To date, ASSA ABLOY has provided Edifice with solutions for more than 750 fire-rated and non-fire doors, via the Openings Studio plugin for Autodesk® Revit®. These include doors and door hardware suited to data centre deployment, among them mechanical mortise locks, exit devices, door closers and master-keying solutions from ASSA ABLOYs portfolio of trusted brands such as Yale and Sargent. Collaborating for transparency and project efficiency An industry-leading specification software tool and BIM plugin, Openings Studio integrates with design software to create and visualise openings for complete door, frame and hardware schedules and specifications. Its flexibility — and availability on multiple types of devices — means all specification changes are incorporated quickly and transparently, helping project delivery dates to remain on target. The Openings Studio environment also simplifies collaboration and data sharing among all project stakeholders. It helps manage openings over the full project lifecycle, from planning and estimation to installation and beyond. Door solution specifications Openings Studio maintains a unified digital thread that connects all project partners to eliminate confusion For these reasons, Openings Studio is deployed all over the world as a specification and ordering tool for building projects. It can deliver detailed door solution specifications directly to popular packages such as Revit® and ARCHICAD®, drawing on a detailed database with colour, size, thickness and certifications for every product; as well as installation and compliance information, Environmental Product Declarations (EPDs) and more. With ongoing use throughout a building’s lifetime, Openings Studio maintains a unified digital thread that connects all project partners to eliminate the confusion that comes with stakeholders having to juggle multiple versions of documents. Management of door hardware “Openings Studio has always been helpful in projects,” explains Gaurav Nirmalkar, Designer at Edifice. “Personally, I have used it in three of the data centres and it never disappoints. The simple and crisp interface is a plus point.” “Recording and management of door hardware is the most important thing in the construction industry. Openings Studio is a good choice for it.”
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure, and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. Mobile-ready HID Signo readers The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over two years by a specialist security installer, Scottish Communications Group. In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. Safe and secure modern system “We wanted a modern system which is safe, secure, and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. “Complying with forthcoming legislation was also another important project requirement." "With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we must protect to ensure everyone is safe. The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” University of Dundee A thriving institution with ambitious development plans, it is currently building a new £40 million facility The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering, and life sciences. Based in the heart of the city, it is home to over 16,000 students, and 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting, and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. Touchless smartphone entry The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP [Open Supervised Device Protocol] and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers thereby speeding up the rollout. University's challenges Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week when some 2,500 – 3,000 undergraduate and postgraduate students enrolled. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Mobile Access Shifting to HID Mobile Access completely changes this and delivers wireless credentialling Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, and validating or revoking of IDs – all of which are done virtually and remotely. Mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Dual system approach While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO DTC4500e printers FARGO range integrates easily with the AEOS software so that Student Services staff can issue physical IDs Given RFID cards are still required, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. “HID Signo readers are going in now across the main buildings including the Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. Encryption, communications, and authentication standards “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications, and authentication standards." "Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” Motorola MOTORTRBO Ion smart radios In addition, the Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems, and CriticalArc Safezone® App, security staff need to carry only a single device to fulfill their duties.
When students come to study at the prestigious Les Roches Marbella campus in Spain, they are not just attending one of the world’s major hospitality business schools, they are also enveloped in extraordinary innovation and sophisticated living to mirror the exceptional experiences they are being prepared to facilitate in their future careers. Real-life training site The institution aims to serve up “academic rigor with a twist of innovation and entrepreneurship” to its 1,000+ students from all corners of the planet who collectively represent more than 80 nationalities. This real-life training site for elite hospitality professionals must offer an authentic, hands-on experience to its students — one that reflects the luxurious living and progressive comforts expected from high-end hospitality properties and their employees. Digital badge One particular aspect they sought to enrich was integrating “digital badge” access across the coastal Mediterranean To ensure Les Roches is always ahead of the curve and a model campus when it comes to exemplary learning based on cutting-edge technologies, administrators wanted to evolve its mobile ecosystem. One particular aspect they sought to enrich was integrating “digital badge” access across their coastal Mediterranean property in Spain. Project objective The project’s objective was to migrate to a mobile credentials-based system where a student’s plastic access card is replaced by a digital ID on a smartphone. This would serve as the verification for daily physical access and digital touchpoints (e.g., building access, vending machines, restaurant reservations, etc.). This effort would also allow the school to steer digital transformation and student efficiencies throughout its security and administrative functions. Catering to student experience “Everything here is about the student experience,” said Mano Soler, Director of Student Services and Operations at Les Roches Marbella. “It is our main driver and the reason we embrace and foster innovation because innovation makes our students’ lives easier and supports their well-being through secure technology. The students will eventually leave this campus and, in turn, take that know-how and excellence into the world with them.” Case study challenge The team wanted a mobile solution to fit specific campus requirements such as swift access For 10 years, Les Roches Marbella relied on an RFID (radio frequency identification) card-based system to identify and grant access to students. This was a fundamental tool that nearly 1,000 individuals needed to have with them at all times to validate themselves day in and day out. Supporting their quest for digital transformation, as part of the school’s Spark incubator programme, the leadership team wanted a mobile solution to fit specific campus requirements such as swiftly granting/removing accesses, avoiding disruption when students lose/forget cards, and accommodating a multi-system environment. Need for a mobile credentials-based system Management also wanted to drive improvements through back-office processes and procedures to save time and resources and enhance everyday life on campus through modern technology. One of the most pressing factors for this particular mobile initiative was to achieve higher efficiency around the school’s new student intake registration/check-in process each semester. Loading ID credentials individually onto RFID cards, then printing each of the 1,000+ cards, meant corrections along the way were inevitable. System re-adaptation Yet, the transition to mobile didn’t come without a series of obstacles and serious considerations. Each touchpoint where a card was to be replaced with smartphone technology required deep analysis and complex integration work, specifically involving seven to eight different brands whose products were already deployed throughout the premises (e.g., printers, vending machines, security technologies, door access, laundry facilities, parking garages and more). Les Roches required an access partner with solutions compatible with the many other products already in play within its existing infrastructure, and an ability to successfully address former system re-adaptation. iOS and Android support The mobile technology needed to support both Android and iOS phones, as well as physical card technology In addition, the mobile technology needed to support both Android and iOS phones, as well as physical card technology (the RFID ecosystem would remain intact for non-student purposes and serve as a migration path for other areas not yet mobile). The school wanted a single company to supply both the hardware and software elements. And, as a higher education establishment with upscale expectations and an outstanding reputation, the Les Roches decision-makers required a proven partner of this same ilk. HID solution To transform technologies and reach new degrees of onsite productivity and novel amenities, Les Roches Marbella selected HID for its unmatched mobile access portfolio. As a market pioneer in trusted identification and authentication, and with a network of partnerships that spans the globe, HID’s experts designed a system to meet each requirement from the school resulting in a tremendous collection of 40+ access points featuring mobile identification, app, portal, and reader technologies. Mobile components from HID The integration project was completed within an accelerated time frame to ensure it was in place before students set foot onto campus that fall. HID components that comprise this robust mobile ecosystem include HID OMNIKEY® readers and reader modules (OMNIKEY 5427, OMNIKEY 5127CK Mini, OMNIKEY 5127 Reader Core), HID Signo™ access control readers, HID Seos® mobile credentials, Aperio® locks from ASSA ABLOY and Aero™ X100 door modules. HID access technologies With a slight tap or wave of their smartphone, students interact easily with the mobile ecosystem and via the digital Seos credential to authenticate themselves as they move throughout the property each day. HID access technologies are embedded in: Parking garage systems Building entrances Vending machines Laundry facilities Printers Point-of-sale at restaurants/on-campus eateries Restaurant access control Class attendance tracking Dorm room door locks Mobile-first world “You cannot discount the value of mobile when it comes to today’s student populations,” said Soler. “It is their way of life. They were ‘born digital’ and they have an expectation when it comes to smart living, for them, it’s a mobile-first world. We get it. We embrace it. And, we intend to attract and retain students by offering them an unparalleled educational experience while here in Marbella.” Efficiencies and integration “We not only transformed our campus with epic mobile access technology but also drove important efficiencies and integration into everything we touched." "The value and inventiveness HIDexperts contributed to constructing this complicated mobile ecosystem is completely in line with our ongoing quest to ensure that innovation is at the heart of the Les RochesWay of Life," said Carlos Diez de la LastraGeneral Manager Les Roches Marbella. Results achieved HID credentials available via a smartphone make scaling individual access up and down significantly easier Tying back to one of the original reasons for this mobile initiative, registration check-ins are streamlined, and Les Roches Marbella has gained immediate improvements around this important event that takes place each semester. 100% of students use the mobile access system on campus. Students register digitally with the option to do so in-person, ahead of time, or remotely with no human interaction. HID credentials available via a smartphone make scaling individual access up and down significantly easier for IT, faculty, and students. A unique, homegrown handheld tool On a case-by-case basis, Les Roches Marbella is already finding ways to apply its in-house ingenuity to foster disruptive thinking. The school used 3D printers to design a customised case to house phones/tablets alongside HID access modules creating a unique, homegrown handheld tool that easily allows campus security personnel to check IDs as required. This safety support tool came about when there was no suitable offering available on the market to meet the school’s specific needs for security checkpoints. Automated student attendance tracking The flexibility and power of HID components enabled the team to re-imagine and invent an original Les Roches security product to, as always, improve the student experience. Many new use cases are in the works to fuel future “wins” across the premises. Automated student attendance tracking is already at the beginning of each class period and serves as another way to further support and protect students. Mini computers and readers were installed in each classroom so students could use their mobile ID (via their smartphone) to mark attendance. API-based interfaces, Aero door module When students go back to their dorm rooms any time, each door loc is integrated with the Aero door module All is handled by a web application running on the mini-computer that pushes and pulls data to/from the Les Roches Absences application in real time through API-based interfaces. And, when students go back to their dorm rooms any time, each door loc is integrated with the Aero door module, providing them with a seamless experience across the entire campus. Mobile authentication and verification “Our eyes are wide open to all the possibilities afforded by the marvelous world of mobile authentication and verification, and each week we come up with new ideas for the continued transformation we have in motion on our campus,” said Juan Luis Velasco, IT Manager at Les Roches Marbella. “Our students love this newfound convenience, and our staff members are reaping the benefits of this technology overhaul.” Best-in-class mobile access system Les Roches Marbella has a best-in-class mobile access system that squarely aligns with the school’s wider objective to be an example of innovation and excellence in global hospitality training both within its own brand family, as well as within the broader realm of higher education. Beyond elevating the student experience through the convenience of mobile IDs and strengthening security when it comes to student safety and mobile ID verification, Les Roches Marbella has an extremely efficient, flexible, and scalable solution that can grow with them as technologies evolve and digital trends continue to transform and connect us all to an international degree. Benefits of digital transformation “This is a story about the value of mobile and any size campus in any sector of education can benefit from the digital transformation angles when it comes to campus business,” said Velasco. “But the most rewarding aspect truly is connecting to our students in a way that’s important, convenient, and meaningful to them keeping them connected and secure via a device that’s already an extension of their existence.”
Opened to mark the 100th anniversary of Bauhaus’ founding, the Bauhaus Museum Dessau is a comprehensive public presentation of the Bauhaus Dessau Foundation collection. On show for the very first time, this valuable collection includes around 49,000 catalogued exhibits and is the second-largest Bauhaus collection in the world. Transparency and simplicity Located in the centre of the city, the museum is a building within a building – a suspended concrete structure inside a glass shell. Its architecture is characterised by transparency and simplicity in both concept and aesthetics. The glass façade reflects the surroundings to different degrees or can be transparent, depending on lighting conditions. An intelligent digital key system It should fit unobtrusively within the building's sophisticated architectural concept Requirements for an intelligent digital key system in the museum were set out in advance. The chosen solution must enable the simplest possible management of access authorisations. It should also fit unobtrusively within the building's sophisticated architectural concept. eCLIQ programmable digital key As in the Bauhaus main building and master houses, the Bauhaus Foundation chose a proven system: ASSA ABLOY’s eCLIQ programmable digital key solution. “The building has an increasingly digital future,” says David Moser, SVP and Head of Digital Access Solutions at ASSA ABLOY Opening Solutions EMEIA. “Choosing a digital solution like eCLIQ, rather than mechanical access, can help organisations to work smarter and collaborate better.” Benefits of digital access: security, convenience, reliability An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry “The electromechanical CLIQ master key system has already proven itself extremely well in the Bauhaus main building and the master houses in Dessau,” explains Uwe Becker, Managing Director of Becker Sicherheitstechnik GmbH, the museum’s security partner on the project. The eCLIQ system is a fully digital version of the CLIQ electromechanical key-operated solution. An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry through doors and much more. Convenient and robust solution Robust, durable cylinders and padlocks with eCLIQ technology can protect lifts, server racks, furniture, gates, mailboxes, cabinets, and more with the same level of control as sensitive doors. Every key has an integrated chip, which makes it unique. As a result, keys may be programmed individually to meet specific needs and access permissions. For keyholders, it’s a convenient solution. Versatility and security benefits The versatility and security benefits of eCLIQ are demonstrated whenever a key is lost. Each key’s access authorisations can be removed individually by reprogramming the cylinders. For greater flexibility, eCLIQ also enables access authorisations to be issued on a time-limited basis, which simplifies the management of external service providers such as maintenance contractors and cleaners. “Digitalisation helps all kinds of organisations to boost their site security and makes everyday access more convenient for everyone – employees, visitors, and contractors,” adds David Moser. Aesthetics and the switch to digital All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design. They blend seamlessly with the varied installation situations of different doors and with the overall building concept in Dessau. A standard battery inside each key powers the eCLIQ cylinder and encrypts the data transfer between the lock, key, and system. With eCLIQ, there is no need to wire cylinders or doors, which leaves building designs intact. Digital transition “ASSA ABLOY’s innovative access solutions can help you digitalise and truly future-proof access at almost any kind of site or building,” says David Moser. “Our vast range of reliable, convenient solutions showcase the value of the digital transition and can be tailored to meet any organisation’s needs or goals.”
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the full US Department of Homeland Security SAFETY Act Designation announced that its proactive gun detection and intelligent situational awareness solution is deployed at the University of New Haven. This integration marks the first time a Connecticut university has adopted ZeroEyes, enhancing the safety and security measures across the campus and surrounding areas. University of New Haven The University of New Haven, located on a suburban campus near New Haven, Connecticut, serves a community of over 10,000 students, faculty, and staff. Its comprehensive, multilayered safety and security strategy ensures protection 24/7/365 with features such as electronic card access gates, CCTV cameras, emergency phones, and the LiveSafe app, which facilitates real-time communication with the University Police Department that patrols the entire campus. Threat identify, assess, and respond With the deployment of ZeroEyes, the campus's security infrastructure is even better equipped to identify With the deployment of ZeroEyes, the campus's security infrastructure is even better equipped to identify, assess, and respond to potential gun-related threats. “The security of our campus and the safety of our students, faculty, staff, and visitors are our paramount priority,” said Adam Brown, chief of the University of New Haven Police Department. AI-based gun-detection system “From our first conversations with ZeroEyes, it was clear they could help enrich the safety and security of our community by offering an AI-based gun-detection system that uses the most advanced technology – supported by a specially trained operations center – to identify and analyze the presence of a firearm." "Testing, implementing, and integrating ZeroEyes into our safety and security systems and protocols has been seamless. ZeroEyes’ expertise in this critical area of public safety provides an important tool that enhances the safety and security of our community.” Situational awareness software If a gun is identified, images are instantly shared with the ZOC which is staffed 24/7/365 ZeroEyes’ AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence including visual description, gun type, and last known location, to local law enforcement and university security as quickly as 3 to 5 seconds from detection. Campus safety “Our collaboration with the University of New Haven underscores their unwavering dedication to campus safety in Connecticut,” said Mike Lahiff, CEO, and co-founder of ZeroEyes. “By integrating our AI gun detection solution, the university is taking a significant step forward in safeguarding its students, faculty, and staff. We are honored to support their mission to create a secure educational environment.”
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. Modern digital solution Modern digital solution would provide better oversight of movement around the building They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorisations, even at the last minute. Digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. Maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provide security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.
In any construction project, meticulous recording and management of door hardware is critical —although often prone to human error. What if there was a way to harness digital technology to fulfil this crucial requirement in a dependable, efficient, agile way? Located in several cities around India, Edifice Consultants Pvt Ltd. specialises in designing climate-responsive architectural structures that harmonise with their surroundings. Complex standards and regulations Each project undertaken reflects Edifice’s collaborative ethos and dedication to enhance the immediate environment, while fostering the well-being of building users, local residents, and the landscape. Edifice’s work across commercial, residential, industrial and public service sectors has received multiple prestigious awards. Designing buildings for so many segments and industries requires broad and deep knowledge of complex standards and regulations. The experience and expertise of ASSA ABLOY have proved invaluable. Specification with Openings Studio™ ASSA ABLOY has provided Edifice with solutions for more than 750 fire-rated and non-fire doors To streamline door specification, Edifice requires digital software that can cut manual mistakes and maintain the process’s accuracy, which is essential to efficient building design. Their chosen solution — Openings Studio™ — takes a rigorous approach, speeding up specification iterations to condense the revision cycle, improve time management and help hit Edifice’s ambitious project timelines. To date, ASSA ABLOY has provided Edifice with solutions for more than 750 fire-rated and non-fire doors, via the Openings Studio plugin for Autodesk® Revit®. These include doors and door hardware suited to data centre deployment, among them mechanical mortise locks, exit devices, door closers and master-keying solutions from ASSA ABLOYs portfolio of trusted brands such as Yale and Sargent. Collaborating for transparency and project efficiency An industry-leading specification software tool and BIM plugin, Openings Studio integrates with design software to create and visualise openings for complete door, frame and hardware schedules and specifications. Its flexibility — and availability on multiple types of devices — means all specification changes are incorporated quickly and transparently, helping project delivery dates to remain on target. The Openings Studio environment also simplifies collaboration and data sharing among all project stakeholders. It helps manage openings over the full project lifecycle, from planning and estimation to installation and beyond. Door solution specifications Openings Studio maintains a unified digital thread that connects all project partners to eliminate confusion For these reasons, Openings Studio is deployed all over the world as a specification and ordering tool for building projects. It can deliver detailed door solution specifications directly to popular packages such as Revit® and ARCHICAD®, drawing on a detailed database with colour, size, thickness and certifications for every product; as well as installation and compliance information, Environmental Product Declarations (EPDs) and more. With ongoing use throughout a building’s lifetime, Openings Studio maintains a unified digital thread that connects all project partners to eliminate the confusion that comes with stakeholders having to juggle multiple versions of documents. Management of door hardware “Openings Studio has always been helpful in projects,” explains Gaurav Nirmalkar, Designer at Edifice. “Personally, I have used it in three of the data centres and it never disappoints. The simple and crisp interface is a plus point.” “Recording and management of door hardware is the most important thing in the construction industry. Openings Studio is a good choice for it.”
HID, the worldwide pioneer in trusted identity solutions, announces that the University of Dundee is updating its city campus estate implementing HID® Mobile Access® and signature HID Signo™ readers throughout its buildings to guarantee it has a modern, secure, and reliable access control system to allow staff and students to enter using both RFID cards and smartphones. Mobile-ready HID Signo readers The project will involve buying and installing new mobile-ready HID Signo readers at around 40 buildings – a staged rollout being completed over two years by a specialist security installer, Scottish Communications Group. In addition, the University has purchased 10,000 HID Mobile Access licences to offer its academic community the option to use their Apple and Android smartphones for touchless entry into its facilities. Safe and secure modern system “We wanted a modern system which is safe, secure, and easy for everyone to use,” says Colin Stebbing, the University’s Head of Precinct Services. “Complying with forthcoming legislation was also another important project requirement." "With bills like Martyn’s Law soon to be enacted, ensuring the University is ready for this was important given that we must protect to ensure everyone is safe. The HID solution enables us to not only lock down buildings immediately, but it has built-in functionality which we can leverage over time, meaning we’ve invested in ‘future proof’ equipment which will last us long term.” University of Dundee A thriving institution with ambitious development plans, it is currently building a new £40 million facility The University of Dundee is a public research university in Scotland renowned for its academic excellence in dentistry, medicine, science and engineering, and life sciences. Based in the heart of the city, it is home to over 16,000 students, and 3,300 staff and is ranked 33rd in the Sunday Times Good University Guide 2024. A thriving institution with ambitious development plans, it is currently building a new £40 million facility called the Innovation Hub. This will offer commercial organisations flexible laboratory, meeting, and office space and, over the next 10 years, it is anticipated the Hub will help create up to 280 new high-quality jobs. Touchless smartphone entry The new HID Signo readers integrate with the University’s existing AEOS access control software from Nedap. Supporting both native Bluetooth® and Near Field Communication (NFC) connectivity, they allow touchless smartphone entry and are fast to install as the wiring uses common protocols like OSDP [Open Supervised Device Protocol] and Wiegand. Furthermore, existing access cards already in circulation can be used with the new HID Signo readers thereby speeding up the rollout. University's challenges Historically, the University used to print and issue plastic RFID cards so staff and students could access buildings. This process was laborious and time-consuming, especially during peak times like Freshers Week when some 2,500 – 3,000 undergraduate and postgraduate students enrolled. Issuing cards was logistically complex due to the high demand and the need for thorough identity checks, which could take up to 10 minutes per card. HID Mobile Access Shifting to HID Mobile Access completely changes this and delivers wireless credentialling Shifting to HID Mobile Access – which utilises cloud-based HID Origo management software integrating with the AEOS system – completely changes this and delivers wireless credentialling. This significantly simplifies all the licencing, allocation of credentials, setting of building access rights, and validating or revoking of IDs – all of which are done virtually and remotely. Mobile credential “Once registered by Student Services in AEOS, a student simply gets an email to their phone, they tap on a link, the app automatically uploads and a mobile credential is granted,” says Paul Brady, HID’s End User Business Manager for Physical Access Control Solutions. “Not only does this improve the overall student experience because it’s substantially quicker and more efficient, but it’s far more sustainable as you’re not issuing PVC cards anymore.” Dual system approach While the strategy and aspiration are for the university population to shift wholesale to mobile access, its approach is to operate a dual system. “We recognise that some visitors and staff still want to use a physical pass and not all employees have a university-issued mobile credential,” explains Stebbing. “HID Signo readers allow us to run both credential types in tandem, with HID Mobile Access giving us the option to scale up to include digital wallets from Apple and Google, as well as integrate with digital campus cards should we decide to go down this route in the future.” FARGO DTC4500e printers FARGO range integrates easily with the AEOS software so that Student Services staff can issue physical IDs Given RFID cards are still required, the University of Dundee utilises its reliable FARGO DTC4500e printers to back up this transition to digital transformation. The FARGO range of ID card printers integrates easily with the AEOS software so that Student Services staff can easily issue physical IDs themselves. “HID Signo readers are going in now across the main buildings including the Innovation Hub site,” says Stuart Leslie, Scottish Communications Group’s director. Encryption, communications, and authentication standards “HID’s reputation is built on reliability and security with its solutions supporting the latest encryption, communications, and authentication standards." "Their devices have an open architecture so they’re easy to install and integrate which reduces the cost for the university and makes time to value that much quicker.” Motorola MOTORTRBO Ion smart radios In addition, the Scottish Communication Group is supplying Motorola MOTORTRBO Ion smart radios to the University’s security staff. The radios will be configured to run HID Mobile Access so they can open doors fitted with the new HID Signo readers. Because these smart radios also link to the University’s CCTV, alarm systems, and CriticalArc Safezone® App, security staff need to carry only a single device to fulfill their duties.
When students come to study at the prestigious Les Roches Marbella campus in Spain, they are not just attending one of the world’s major hospitality business schools, they are also enveloped in extraordinary innovation and sophisticated living to mirror the exceptional experiences they are being prepared to facilitate in their future careers. Real-life training site The institution aims to serve up “academic rigor with a twist of innovation and entrepreneurship” to its 1,000+ students from all corners of the planet who collectively represent more than 80 nationalities. This real-life training site for elite hospitality professionals must offer an authentic, hands-on experience to its students — one that reflects the luxurious living and progressive comforts expected from high-end hospitality properties and their employees. Digital badge One particular aspect they sought to enrich was integrating “digital badge” access across the coastal Mediterranean To ensure Les Roches is always ahead of the curve and a model campus when it comes to exemplary learning based on cutting-edge technologies, administrators wanted to evolve its mobile ecosystem. One particular aspect they sought to enrich was integrating “digital badge” access across their coastal Mediterranean property in Spain. Project objective The project’s objective was to migrate to a mobile credentials-based system where a student’s plastic access card is replaced by a digital ID on a smartphone. This would serve as the verification for daily physical access and digital touchpoints (e.g., building access, vending machines, restaurant reservations, etc.). This effort would also allow the school to steer digital transformation and student efficiencies throughout its security and administrative functions. Catering to student experience “Everything here is about the student experience,” said Mano Soler, Director of Student Services and Operations at Les Roches Marbella. “It is our main driver and the reason we embrace and foster innovation because innovation makes our students’ lives easier and supports their well-being through secure technology. The students will eventually leave this campus and, in turn, take that know-how and excellence into the world with them.” Case study challenge The team wanted a mobile solution to fit specific campus requirements such as swift access For 10 years, Les Roches Marbella relied on an RFID (radio frequency identification) card-based system to identify and grant access to students. This was a fundamental tool that nearly 1,000 individuals needed to have with them at all times to validate themselves day in and day out. Supporting their quest for digital transformation, as part of the school’s Spark incubator programme, the leadership team wanted a mobile solution to fit specific campus requirements such as swiftly granting/removing accesses, avoiding disruption when students lose/forget cards, and accommodating a multi-system environment. Need for a mobile credentials-based system Management also wanted to drive improvements through back-office processes and procedures to save time and resources and enhance everyday life on campus through modern technology. One of the most pressing factors for this particular mobile initiative was to achieve higher efficiency around the school’s new student intake registration/check-in process each semester. Loading ID credentials individually onto RFID cards, then printing each of the 1,000+ cards, meant corrections along the way were inevitable. System re-adaptation Yet, the transition to mobile didn’t come without a series of obstacles and serious considerations. Each touchpoint where a card was to be replaced with smartphone technology required deep analysis and complex integration work, specifically involving seven to eight different brands whose products were already deployed throughout the premises (e.g., printers, vending machines, security technologies, door access, laundry facilities, parking garages and more). Les Roches required an access partner with solutions compatible with the many other products already in play within its existing infrastructure, and an ability to successfully address former system re-adaptation. iOS and Android support The mobile technology needed to support both Android and iOS phones, as well as physical card technology In addition, the mobile technology needed to support both Android and iOS phones, as well as physical card technology (the RFID ecosystem would remain intact for non-student purposes and serve as a migration path for other areas not yet mobile). The school wanted a single company to supply both the hardware and software elements. And, as a higher education establishment with upscale expectations and an outstanding reputation, the Les Roches decision-makers required a proven partner of this same ilk. HID solution To transform technologies and reach new degrees of onsite productivity and novel amenities, Les Roches Marbella selected HID for its unmatched mobile access portfolio. As a market pioneer in trusted identification and authentication, and with a network of partnerships that spans the globe, HID’s experts designed a system to meet each requirement from the school resulting in a tremendous collection of 40+ access points featuring mobile identification, app, portal, and reader technologies. Mobile components from HID The integration project was completed within an accelerated time frame to ensure it was in place before students set foot onto campus that fall. HID components that comprise this robust mobile ecosystem include HID OMNIKEY® readers and reader modules (OMNIKEY 5427, OMNIKEY 5127CK Mini, OMNIKEY 5127 Reader Core), HID Signo™ access control readers, HID Seos® mobile credentials, Aperio® locks from ASSA ABLOY and Aero™ X100 door modules. HID access technologies With a slight tap or wave of their smartphone, students interact easily with the mobile ecosystem and via the digital Seos credential to authenticate themselves as they move throughout the property each day. HID access technologies are embedded in: Parking garage systems Building entrances Vending machines Laundry facilities Printers Point-of-sale at restaurants/on-campus eateries Restaurant access control Class attendance tracking Dorm room door locks Mobile-first world “You cannot discount the value of mobile when it comes to today’s student populations,” said Soler. “It is their way of life. They were ‘born digital’ and they have an expectation when it comes to smart living, for them, it’s a mobile-first world. We get it. We embrace it. And, we intend to attract and retain students by offering them an unparalleled educational experience while here in Marbella.” Efficiencies and integration “We not only transformed our campus with epic mobile access technology but also drove important efficiencies and integration into everything we touched." "The value and inventiveness HIDexperts contributed to constructing this complicated mobile ecosystem is completely in line with our ongoing quest to ensure that innovation is at the heart of the Les RochesWay of Life," said Carlos Diez de la LastraGeneral Manager Les Roches Marbella. Results achieved HID credentials available via a smartphone make scaling individual access up and down significantly easier Tying back to one of the original reasons for this mobile initiative, registration check-ins are streamlined, and Les Roches Marbella has gained immediate improvements around this important event that takes place each semester. 100% of students use the mobile access system on campus. Students register digitally with the option to do so in-person, ahead of time, or remotely with no human interaction. HID credentials available via a smartphone make scaling individual access up and down significantly easier for IT, faculty, and students. A unique, homegrown handheld tool On a case-by-case basis, Les Roches Marbella is already finding ways to apply its in-house ingenuity to foster disruptive thinking. The school used 3D printers to design a customised case to house phones/tablets alongside HID access modules creating a unique, homegrown handheld tool that easily allows campus security personnel to check IDs as required. This safety support tool came about when there was no suitable offering available on the market to meet the school’s specific needs for security checkpoints. Automated student attendance tracking The flexibility and power of HID components enabled the team to re-imagine and invent an original Les Roches security product to, as always, improve the student experience. Many new use cases are in the works to fuel future “wins” across the premises. Automated student attendance tracking is already at the beginning of each class period and serves as another way to further support and protect students. Mini computers and readers were installed in each classroom so students could use their mobile ID (via their smartphone) to mark attendance. API-based interfaces, Aero door module When students go back to their dorm rooms any time, each door loc is integrated with the Aero door module All is handled by a web application running on the mini-computer that pushes and pulls data to/from the Les Roches Absences application in real time through API-based interfaces. And, when students go back to their dorm rooms any time, each door loc is integrated with the Aero door module, providing them with a seamless experience across the entire campus. Mobile authentication and verification “Our eyes are wide open to all the possibilities afforded by the marvelous world of mobile authentication and verification, and each week we come up with new ideas for the continued transformation we have in motion on our campus,” said Juan Luis Velasco, IT Manager at Les Roches Marbella. “Our students love this newfound convenience, and our staff members are reaping the benefits of this technology overhaul.” Best-in-class mobile access system Les Roches Marbella has a best-in-class mobile access system that squarely aligns with the school’s wider objective to be an example of innovation and excellence in global hospitality training both within its own brand family, as well as within the broader realm of higher education. Beyond elevating the student experience through the convenience of mobile IDs and strengthening security when it comes to student safety and mobile ID verification, Les Roches Marbella has an extremely efficient, flexible, and scalable solution that can grow with them as technologies evolve and digital trends continue to transform and connect us all to an international degree. Benefits of digital transformation “This is a story about the value of mobile and any size campus in any sector of education can benefit from the digital transformation angles when it comes to campus business,” said Velasco. “But the most rewarding aspect truly is connecting to our students in a way that’s important, convenient, and meaningful to them keeping them connected and secure via a device that’s already an extension of their existence.”
Opened to mark the 100th anniversary of Bauhaus’ founding, the Bauhaus Museum Dessau is a comprehensive public presentation of the Bauhaus Dessau Foundation collection. On show for the very first time, this valuable collection includes around 49,000 catalogued exhibits and is the second-largest Bauhaus collection in the world. Transparency and simplicity Located in the centre of the city, the museum is a building within a building – a suspended concrete structure inside a glass shell. Its architecture is characterised by transparency and simplicity in both concept and aesthetics. The glass façade reflects the surroundings to different degrees or can be transparent, depending on lighting conditions. An intelligent digital key system It should fit unobtrusively within the building's sophisticated architectural concept Requirements for an intelligent digital key system in the museum were set out in advance. The chosen solution must enable the simplest possible management of access authorisations. It should also fit unobtrusively within the building's sophisticated architectural concept. eCLIQ programmable digital key As in the Bauhaus main building and master houses, the Bauhaus Foundation chose a proven system: ASSA ABLOY’s eCLIQ programmable digital key solution. “The building has an increasingly digital future,” says David Moser, SVP and Head of Digital Access Solutions at ASSA ABLOY Opening Solutions EMEIA. “Choosing a digital solution like eCLIQ, rather than mechanical access, can help organisations to work smarter and collaborate better.” Benefits of digital access: security, convenience, reliability An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry “The electromechanical CLIQ master key system has already proven itself extremely well in the Bauhaus main building and the master houses in Dessau,” explains Uwe Becker, Managing Director of Becker Sicherheitstechnik GmbH, the museum’s security partner on the project. The eCLIQ system is a fully digital version of the CLIQ electromechanical key-operated solution. An eCLIQ system can bring digital access to almost any opening, helping filter authorised entry through doors and much more. Convenient and robust solution Robust, durable cylinders and padlocks with eCLIQ technology can protect lifts, server racks, furniture, gates, mailboxes, cabinets, and more with the same level of control as sensitive doors. Every key has an integrated chip, which makes it unique. As a result, keys may be programmed individually to meet specific needs and access permissions. For keyholders, it’s a convenient solution. Versatility and security benefits The versatility and security benefits of eCLIQ are demonstrated whenever a key is lost. Each key’s access authorisations can be removed individually by reprogramming the cylinders. For greater flexibility, eCLIQ also enables access authorisations to be issued on a time-limited basis, which simplifies the management of external service providers such as maintenance contractors and cleaners. “Digitalisation helps all kinds of organisations to boost their site security and makes everyday access more convenient for everyone – employees, visitors, and contractors,” adds David Moser. Aesthetics and the switch to digital All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design All eCLIQ keys and cylinders are compatible with the high demands that Bauhaus places on design. They blend seamlessly with the varied installation situations of different doors and with the overall building concept in Dessau. A standard battery inside each key powers the eCLIQ cylinder and encrypts the data transfer between the lock, key, and system. With eCLIQ, there is no need to wire cylinders or doors, which leaves building designs intact. Digital transition “ASSA ABLOY’s innovative access solutions can help you digitalise and truly future-proof access at almost any kind of site or building,” says David Moser. “Our vast range of reliable, convenient solutions showcase the value of the digital transition and can be tailored to meet any organisation’s needs or goals.”
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the full US Department of Homeland Security SAFETY Act Designation announced that its proactive gun detection and intelligent situational awareness solution is deployed at the University of New Haven. This integration marks the first time a Connecticut university has adopted ZeroEyes, enhancing the safety and security measures across the campus and surrounding areas. University of New Haven The University of New Haven, located on a suburban campus near New Haven, Connecticut, serves a community of over 10,000 students, faculty, and staff. Its comprehensive, multilayered safety and security strategy ensures protection 24/7/365 with features such as electronic card access gates, CCTV cameras, emergency phones, and the LiveSafe app, which facilitates real-time communication with the University Police Department that patrols the entire campus. Threat identify, assess, and respond With the deployment of ZeroEyes, the campus's security infrastructure is even better equipped to identify With the deployment of ZeroEyes, the campus's security infrastructure is even better equipped to identify, assess, and respond to potential gun-related threats. “The security of our campus and the safety of our students, faculty, staff, and visitors are our paramount priority,” said Adam Brown, chief of the University of New Haven Police Department. AI-based gun-detection system “From our first conversations with ZeroEyes, it was clear they could help enrich the safety and security of our community by offering an AI-based gun-detection system that uses the most advanced technology – supported by a specially trained operations center – to identify and analyze the presence of a firearm." "Testing, implementing, and integrating ZeroEyes into our safety and security systems and protocols has been seamless. ZeroEyes’ expertise in this critical area of public safety provides an important tool that enhances the safety and security of our community.” Situational awareness software If a gun is identified, images are instantly shared with the ZOC which is staffed 24/7/365 ZeroEyes’ AI gun detection and intelligent situational awareness software layers onto existing digital security cameras. If a gun is identified, images are instantly shared with the ZeroEyes Operations Centre (ZOC), the industry’s only U.S.-based, fully in-house operation centre, which is staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they dispatch alerts and actionable intelligence including visual description, gun type, and last known location, to local law enforcement and university security as quickly as 3 to 5 seconds from detection. Campus safety “Our collaboration with the University of New Haven underscores their unwavering dedication to campus safety in Connecticut,” said Mike Lahiff, CEO, and co-founder of ZeroEyes. “By integrating our AI gun detection solution, the university is taking a significant step forward in safeguarding its students, faculty, and staff. We are honored to support their mission to create a secure educational environment.”
World Trade Centre (WTC) Amsterdam is home to more than 300 companies. The commitment of its security team to providing a safe working environment in WTC’s fixed and flexible offices goes without saying. However, building managers wanted more from their access solution. More than just an office space, WTC Amsterdam has complementary onsite facilities, including childcare, a gym, physiotherapy clinic, bar/café, dry cleaning service and more. All its facilities must be cleaned and serviced regularly: they sought a more time-efficient way to manage the many contractors and suppliers who come and go every day. Modern digital solution Modern digital solution would provide better oversight of movement around the building They also hoped a modern digital solution would provide better oversight of movement around the building, including usage data to improve maintenance scheduling. For convenience during installation and day-to-day management they targeted a wire-free solution – for simpler, less disruptive switching of 1,000 doors from mechanical locks to digital access – and intuitive management, allowing for easy changing of individual access authorisations, even at the last minute. Digital access system With all these criteria in mind, WTC Amsterdam managers decided on ASSA ABLOY’s smart key digital access system, eCLIQ. They upgraded doors from mechanical to digital access simply by swapping the existing cylinder for an eCLIQ device. Doors are unlocked by battery-powered user smart keys, with a typical battery lifespan of 10 years. “Providing these doors with wired access control would be a huge job and become costly. Instead, we opted for the eCLIQ solution,” explains Sander Borggreve, Facility Manager at WTC Amsterdam. Concrete improvements in operations Scheduling is further simplified by storing keys with a Traka key management system The ROI in terms of workflow benefits has been significant. “Granting temporary controlled access to third parties is very easy with the eCLIQ system. We can set access for a certain period of time, but we can also revoke it at any time,” says Sander. Scheduling is further simplified by storing keys with a Traka key management system. After removing a key from the cabinet, authorised team members enter it into the adjacent eCLIQ Wall Programming Device. In seconds, the key is issued with its fine-grained access rights – covering both door-by-door and time validity. Maintenance and operations With the eCLIQ system, WTC Amsterdam gained not only control but also insights into usage and user flows. This data now informs maintenance and operations, reducing the overall Total Cost of Ownership for the solution. “eCLIQ works very pleasantly in practice. My employees are very satisfied with how the keys work,” says Rutger Barendse of D&B The Facility Group, who provide security staff for WTC Amsterdam. “It is easy as pie!” adds Sander.


Products


Round table discussion
There is no shortage of threats facing security professionals, including some that are new and emerging. Understanding various new threats allows individuals and organisations to take proactive steps to protect themselves, but the first step is to identify what those threats are. Early detection of threats can minimise the impact of a successful attack, whatever the vulnerability at issue. We asked this week’s Expert Panel Roundtable: What new and emerging threats will physical security professionals need to be prepared for in the future?
Technology can be a powerful tool, but it can also be misused. Ethical principles help ensure that technology is used in a way that minimises risks and avoids causing harm to people or society. Issues could include factors such as data privacy and algorithmic bias of certain technologies. As the security industry embraces advanced and evolving technologies, we asked this week’s Expert Panel Roundtable: What are the biggest ethical considerations of using emerging technologies in physical security?
Technological leaps in the last several decades have revolutionised biometrics. The technologies are constantly evolving, spanning facial recognition to iris scanning to fingerprints, to provide new levels of security and convenience. Biometrics are everywhere, from smartphones to border control, constantly evolving to meet the needs of our increasingly digital world. They are also more accurate and easier to use than ever. We asked this week's Expert Panel Roundtable: What’s new with biometrics?
White papers
H.265 High Efficiency Coding: Video compression for security applications
Download
Innovative edge storage solutions for the video surveillance industry
Download
Enhanced Ethernet Technology (ePoE)
Download
Simple Security Solutions for SMBs
Download
Security investments retailers should consider for their 2021 budget
Download
Understanding video management systems
Download
H.265 High Efficiency Coding: Video compression for security applications
Download
Innovative edge storage solutions for the video surveillance industry
Download
Enhanced Ethernet Technology (ePoE)
Download
Simple Security Solutions for SMBs
Download
Security investments retailers should consider for their 2021 budget
Download
Understanding video management systems
Download

Videos
Digital Video Recorders: Manufacturers & Suppliers
- Dahua Technology Digital Video Recorders
- Hikvision Digital Video Recorders
- Vicon Digital Video Recorders
- Honeywell Security Digital Video Recorders
- Hanwha Vision Digital Video Recorders
- Bosch Digital Video Recorders
- eneo Digital Video Recorders
- MobileView Digital Video Recorders
- LILIN Digital Video Recorders
- Dedicated Micros Digital Video Recorders
- DALI Digital Video Recorders
- Genie CCTV Limited Digital Video Recorders
- LTV Europe Digital Video Recorders
- Messoa Digital Video Recorders
- 360 Vision Digital Video Recorders
- Everfocus Digital Video Recorders
- artec Digital Video Recorders
- Visionhitech Digital Video Recorders
- Vanderbilt Digital Video Recorders
- Ganz Digital Video Recorders

Using artificial intelligence (AI) to automate physical security systems
Download
A modern guide to data loss prevention
Download
7 proven solutions for law enforcement key control and asset management
Download
The truth behind 9 mobile access myths
Download
Access control system planning phase 2
Download