Technology & Trends - Mechanical digital locks
The Internet of Things is growing quickly. It has moved far beyond a few smart gadgets at home. Today, connected technology is in homes, factories, hospitals, farms, and cities. Experts expect the global market for IoT devices to rise from about $70 billion in 2024 to more than $181 billion by 2030. This means more devices, more data, and more opportunities for industries everywhere. This growth comes from several advances working together. 5G connections make it possible to send and receive d...
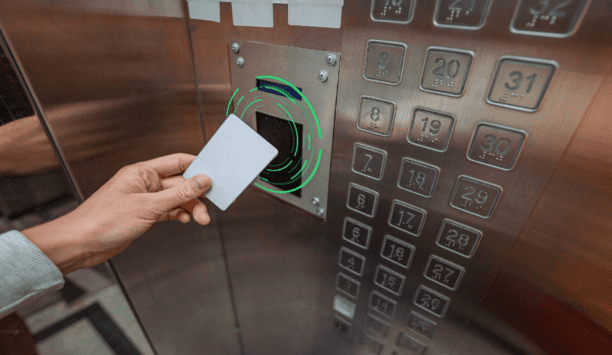
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
With increasing security and public health concerns, contactless credentials are gaining more and more importance. Contactless credentials can be divided into two main categories: soft credentials that include mobile phone applications that tap into their BLE/NFC hardware and transmit the data, and hard credentials that typically include low frequency (125 kHz) and high frequency (13.56MHz) based passive RFID transponders. With the help of these credentials, organisations can tackle safety conc...
Schools were never designed and built with social distancing in mind. So it’s perhaps not surprising that as children returned to schools for the autumn term this year, the prospect of outdoor classes and assemblies was mooted in the media and by the Government. Many in the education sector are making the case that, should there be further COVID-19 outbreaks, in the coming months, it would be better to utilise outside space, rather than resort to closing schools. In the COVID-19 era, head...
Most consumers are enjoying the convenience brought by electronic locks. With the existence of electronic locks, people no longer need to be restricted by keys. There are a variety of unlocking methods and more convenient remote control unlocking options. Suppose, you are going on vacation, and with the presence of an electronic lock, you can easily enter your house with your babysitter, without a spare key. Of course, not only smart homes, but also some infrastructure and commercial buildings...
Access control and management of trusted identities are the building blocks of security, safety, and site management policies for many businesses and organisations. The current pandemic has compounded this with the introduction of new policies and regulations, particularly around social distancing and contact tracing. Most organisations will have some form of legacy access control in place, ranging from the most simplistic options, such as locks and keys, to technology-based systems. The issue...
Q: Mr. Seiter, Mr. Ekerot, you both joined Bosch Building Technologies’ business unit Video Systems & Solutions as Senior Vice Presidents in March 2020, when the Coronavirus pandemic was just beginning. How did your business unit get through 2020? Magnus Ekerot: The crisis was also felt at Bosch. At the same time, demand has risen for solutions that keep businesses open and protect people's health. We offer corresponding video solutions that can make a significant contribution to con...
A defibrillator can save the life of a person suffering from cardiac arrest – but it is most effective when used in the first few minutes of the patient collapsing. Studies have shown that a shock given within the first three minutes provides the best chance of survival and even one minute of further delay can substantially lower the chances of recovering. Public Access Defibrillators (PADs) were created to allow untrained members of the public to deliver life-saving treatment in those pr...
The experience of the COVID-19 pandemic has made us all more conscious of who is coming and going from our property. Whether it is a family home, business premises or public building, property owners want full control over access for protection and peace of mind. As a provider of access control technologies, we are seeing a growing demand for automated gates with a variety of access control systems. There are a number of considerations that buyers need to make when investing. And as an installe...
The safeguarding of premises through the monitoring of entrance and exit points has traditionally been a very manual aspect of security. Human operators have been relied on to make decisions about who to admit and deny based on levels of authorisation and the appropriate credentials. But the access control business, like many industries before it, is undergoing its own digital transformation; one where the protection of premises, assets and people is increasingly delivered by interconnected sys...
If you’re responsible for a medium or large-sized office, it’s more important than ever that you have access to a means of ensuring people’s safety, managing risks and fraud, and protecting property. Any security system that you employ must therefore meet the most demanding commercial requirements of today’s offices, and tomorrow’s. This means thinking beyond a basic intrusion system and specifying a comprehensive solution that integrates smart features like access...
Until recently, the convenience and security of “smart” electronic locks have been exclusively enjoyed by owners of homes, with renters largely being left out in the cold. Locked out by the temporary nature of their living arrangement, and not allowed to make structural changes to their temporary abodes, these renters have been unable to enjoy the many benefits of these connected devices. But today, smart lock capabilities are becoming available to renters and rental property owners...
Throughout the UK there are many examples of smart city transformation, with key industries including transport, energy, water and waste becoming increasingly ‘smart’. A smart city is a one that uses information and communication technologies to increase operational efficiency, share information with the public and improve both the quality of government services and resident welfare. Smart access is an important step forward in providing technologically advanced security manag...
The physical security market continues to experience growth as users look to capitalise on the promises of emerging technologies and because of this, 2017 proved to be a great year for Oncam. In fact, this year was the best year in Oncam's history in terms of sales, as 360-degree fisheye cameras have gone from being a “specialty” camera used only in certain applications to a primary device for enabling total situational awareness. Today, many of our customers leverage 360-degree ca...
During 2017, we’ve enjoyed stable economic growth for a number of years now; we’re not running into as much resistance for security entrances as we did, say, seven to nine years ago. Hardening perimeters against active shooters Compared to other security products such as cameras and card readers, security entrances are a big investment and considered somewhat of a luxury: during downturns we’re among the first to hit the “cutting room floor.” Now, however, fueled...
Securing potentially hazardous sites, which contain gas or oil storage facilities, is becoming increasingly important to UK industry. While other businesses are investing in enhanced access control solutions, such as electronic key-centric access management, many sites containing hazardous materials are left stuck in the dark ages, with basic and impractical mechanical locking systems. This is due to the potential risks associated with using an electronic device, which could cause a spark, in cl...
Customers are increasingly requesting both mechanical and electronic services for their doors In most buildings, security is a hybrid solution of both mechanical and electronic security products. Locksmiths take care of the mechanical door hardware and the integrators focus on the electronic security technology. However, for consumers, this traditional division of labour means they must deal with two different companies for the same door - one to design, install and service a...
Physical access control has been a key component of many organisations’ security strategies for several decades. Like any technology, access control has evolved over the years, and solutions now offer more security and convenience than ever before. From swipe technologies, such as the now antiquated magnetic stripe, to a variety of contactless technologies and mobile access credentials, businesses now have several choices when it comes to access control. Upgrading outd...
At the end of last year, we anticipated that data gathering and analysis would continue to be a strong trend, and that certainly proved to be the case in 2016. More and more organisations are seeing the value of the intelligence provided by diverse systems’ data. The number and variety of networked systems and devices – both security and non-security – continued to grow steadily in the last year, and the data these disparate sources create has proven highly...
Again in 2016, the most well-trafficked articles posted at SourceSecurity.com tended to be those that addressed timely and important issues in the security marketplace. In the world of digital publishing, it’s easy to know what content resonates with the market: Our readers tell us with their actions; i.e., where they click. Let’s look back at the Top 10 articles we posted in 2016 that generated the most page views. They are listed in order here with the author&r...
The shift from wired to wireless access control was expected to gather pace in 2016—and that has happened. This year we at Assa Abloy surveyed a large cross-section of security professionals, seeking their insight into the changing market. Comparing our data with research we did in 2014 showed a clear trend towards wireless access control. Wireless access data Our 2014 survey found 23% of commercial properties using a wireless or hybrid wired/wireless access control s...
The winds of change have swept into the access control market in 2016. The hardware is transitioning away from being solely panel-based, software is rapidly moving to the cloud, and credentials are going mobile. It seems that the security access control world is finally waking up from its technological slumber, and 2017 will be an exciting time. These three major trends are feeding off one another and are driving the growth all around. IP and edge based systemsIn 2016, hardware companies like...
New construction has continued to grow as a result of low interest rates in 2016 and that has positively impacted the security marketplace. Yet the limited availability of skilled labour is becoming a large issue as it leads to higher cost of labour. This also creates a challenge in recruiting, training, and retraining a capable staff in building construction and maintenance activities. As a result, there is a continued desire to improve our efficiency in production, commissioning and the manage...
The technologies behind physical access control are constantly evolving. It’s a fast-changing market that can leave end user organisations struggling to keep up. Smart cards still reign supreme, with good reason, but there are also new options today and on the horizon. Customers want to implement the most secure and up-to-date technologies, but constantly adapting their systems to keep up with the pace of change is impractical. Leveraging access control technologies in a way that both m...
Protecting the world’s critical infrastructure is a complex mission. Managing security for these facilities involves addressing a broad range of possible threats and vulnerabilities, from the intentional contamination of water supplies to the theft of equipment vital to electricity distribution.Vandalism, theft or deliberate sabotage — by terrorists or other criminals — are ever-present threats. The consequences of any security breach can be dire,...
The security industry as a whole is migrating from the historical mechanical lock to the newest technology of electronic locks Mechanical locks and keys date back thousands of years and have undergone many changes, but the industry’s transition to electronic locks might be the most important, lasting, and surprisingly affordable security and safety change of all. The objective behind the creation of locks so long ago remains: to control a value on the other side...
A force of 85,000 police and military will patrol the Olympic grounds and environs to provide security A week before the Rio Olympics were slated to begin, Brazil fired the private security firm assigned to hire personnel to screen people entering the various Olympic venues located around Rio De Janeiro. The security plan called for 3,400 screeners. The security firm had only found 500. What happened? Today, prospective security officers must undergo background checks that do...
Everything about wireless access control makes life easier for those who install and operate it A lot of market data crosses my desk at ASSA ABLOY. Sometimes it can be hard to spot patterns or pick out the trends. But not always. Some recent access control market research we commissioned pointed in one direction. Our conclusion? Slowly but surely, access control is becoming a wireless technology As the global leader in door opening solutions, we are able to survey a large,...
ISE’s research shows that healthcare facilities & hospitals security programmesto ward off determined attackers going after specific targets A well-known security axiom posits that an effective security programme can discourage would-be attackers, causing them to move on in search of softer targets. But it doesn’t always work that way. Take healthcare facilities such as hospitals, for example. Prospective attackers with no particular target in mind may see...
ASSA ABLOY door handles with built in reader, strike, request-to-exit sensorand door contacts help maintain sterile environment of stainless steel rooms Access control technology has been around for a long time, but security professionals still run into weird problems when designing and installing systems. For example, when a hospital discovered that it was losing $4,000 per patient bed annually in medicines and other supplies, it asked ASSA ABLOY for an access control solutio...
Browse expert commentaries
Related videos
Find Lost Wallet with Dahua WizSeek
Dahua Traffic Signal Controller Highlight
CLIQ Connect
- View more Mechanical digital locks
- TESA Mechanical digital locks
- Alpro Mechanical digital locks
- ABLOY Mechanical digital locks
- Codelocks Mechanical digital locks
- Unican Mechanical digital locks
Hikvision AOV 4G Solar Camera Series for Off-Grid Video Security
KentixONE – IoT Access and Monitoring For Data Centres
Climax Technology HSGW-Gen3 Modular Smart Security Gateway
One system, one card
DownloadAligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
Download















![[Download] The Evolution of Cards and Credentials in Physical Access](https://www.sourcesecurity.com/img/news/612/HID-whitepaper-Evolution of Cards and Credentials-920.jpg)


























