Technology & Trends - Access control software
When looking to design, implement, and track a loss prevention and security audit program across a national retail chain, there are two big questions to consider: What are you attempting to resolve, influence, and/or measure? What is the priority? The first point is to understand if there are any specific pressing concerns. If there are procedures not being followed by staff in the stores, then you want to come up with a program that is going to actually influence the way they work...
Are we doing enough to protect our vital infrastructure and commercial properties? This is one of the key issues the sector is currently dealing with. Crime rates have been rising following the pandemic and ensuing lockdowns in 2020–21. The Office for National Statistics reported that between September 2019 and September 2021, crime rates increased by 14%. This illustrates that risks to businesses, public attractions, and public buildings are increasing, and it implies that decision-make...
A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutions. In the world of access control systems, biometric advancements allow for more secure authentication measures and seamless security processes. As more products and services hit the market, learn our predictions for the 2023 biometric trends in this article. Biometric access control systems What are biometric acc...
Dr. Henrik Siegle has been the CTO at Bosch Building Technologies since November 2021. In this interview, he speaks about the megatrends of energy efficiency and sustainability, and about new developments in the building technology sector. Dr. Siegle, the building industry is currently facing major challenges in the form of climate change and energy shortages. How is Bosch Building Technologies dealing with these challenges? Dr. Henrik Siegle: Energy efficiency and sustainability have long...
The UK’s future depends on our children. Within the four walls of classrooms around the country, young minds are inspired, practical skills are learnt, and new passions are established; these will be tapped into by pupils for decades to come. To make sure outmoded security measures are not having an adverse effect on the performance within, we must first examine the limits and physical safeguards around these educational institutions. When planning and building any facility for the educat...
The nuances of data privacy continue to bombard organisations from all angles, and, amid the impending sunset of Universal Analytics (UA), it’s time to stop playing catch-up. Instead, by enacting future-proofing strategies around data as a first port of call, long-term compliance can be achieved as an automatic byproduct. Data privacy At data privacy’s ‘sunrise’, companies’ efforts were largely targeted towards the customer, ensuring that the ever-growing extent o...
Video surveillance has become the king of data—and is known to be the largest producer of data in the world. A single day of video surveillance is estimated to produce more than 500 petabytes of data—for context, a single petabyte is equivalent to 1,000 terabytes – and that number is only expected to grow. Why is it expected to grow? The answer lies with new and emerging technology, and the way that technology operates. For physical security teams, the rapid amount of data the...
With shoplifting up, 21% in 2022, Peter Jackson, managing director of Jacksons Fencing explores how retail businesses can better protect their premises from opportunistic thieves. We think of shoplifting as people walking out of a store, pockets bulging with unpaid-for goods. However, in town centres and retail parks, the rear doors of shops and delivery areas can be an opportunity for theft on a much grander scale. Thefts and break-ins It’s not uncommon for thefts to be perpetrated fr...
Residential burglaries and break-ins are a problem for many homeowners. The FBI estimates there were approximately 1,117,696 burglaries in 2019 in the United States, which accounted for 16.1% of property crimes. Having proper home security can not only protect your home and belongings, but it can also keep your family safe. Even if you’re new to the idea of having and using smart home security devices, it’s easy to get started. This guide will provide the information and actionable...
For both employers and employees, a safe workplace is crucial. But what about the security of those who keep us safe? Worker safety The physical security industry and its personnel are not only valuable but also indispensable assets in workplaces. Most private and public sectors rely on it to keep their respective communities and stakeholders safe. Hence, it is extremely crucial to ensure the safety of physical security workers. The security industry, regardless of size, must prioritise safet...
Managing the technology stack and known vulnerabilities is becoming a key criteria for cyber insurance pay outs. Open source software has once again made the headlines following warnings to organisations about the release of a new version of OpenSSL. Released on 1st November 2022, the new version patched vulnerabilities in version 3.0 and above of the nearly ubiquitously used cryptographic library for encrypting communications on the Internet. Remote code execution The OpenSSL Project team to...
With Black Friday on the horizon and shops and warehouses busier than ever, Elliot Roddy, Operations Director at CDX Security Group has shared some tips on how to keep the must-have gift items safe and secure: Regular monitoring and CCTV, Stock control and audits, and Partner with a trusted security firm. Staying alert with the must-have items Each year, we see certain items gain popularity and become the year's must-haves. This year, social media and the rise of TikTok have accel...
In the past five years, the retail landscape and the relationship between consumers and businesses has shifted drastically. It wasn’t too long ago when shopping at malls was considered a family activity and consumers shopped at local stores where they knew and interacted with sales personnel. Today, however, malls and interactions with employees are relics that accurately portray the way retail used to work. Retail companies have shifted their consumer model to focus on the online market...
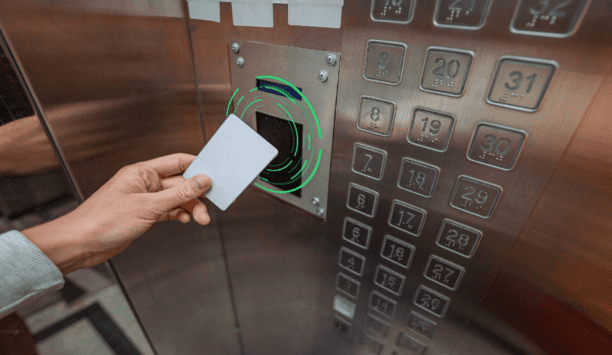
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
You’re no psychic. You probably don’t have the power of clairvoyance. But guess what? When it comes to your security, none of that matters. You can still create future-proof security by properly equipping yourself. Here’s how. Understanding access control Security is changing faster than ever before. With new threats inside the workplace and smaller security teams taking on more tasks, IT and security personnel must automate their processes using new technology. One difficu...
Hybrid cloud computing enables organisations to segregate their resources and workloads on-premise, in a private cloud, or a public cloud. But despite its many benefits, the hybrid environment also creates security concerns. AlgoSec’s co-founder and CTO, Prof. Avishai Wool shares his expert insights on some of these concerns and offers best practices to boost hybrid cloud security. Hybrid cloud computing Hybrid cloud computing combines on-premises infrastructure, private cloud services,...
At the start of the millennium, GRC was still very much in its infancy. Fast forward to 2022 and it is no longer seen as a siloed process. Now it is an organisation-wide concern that permeates every decision from C-suite to the shop floor. And its evolution shows no sign of slowing down as modern solutions are changing the way that GRC processes are delivered and embedded into day-to-day operations within organisations. So, what does the future look like? In an era where risk is accelerating, w...
Although the wider adoption of 5G, together with faster connection speeds and improved bandwidth, opens up new prospects for telecom service providers, it also poses new risks in terms of network security. This article explains how telcos can make their newly-established 5G networks as well as telecom software solutions more impenetrable and secure. Implement robust device authentication protocols 5G is set to spur a wide-scale adoption of connected devices in the business and consumer sphere...
Although inflated fuel prices have somewhat settled since the summer, recent changes in legislation mean construction sites are particularly vulnerable to attempted fuel thefts. Read on to find out what’s changed, and what’s proving effective in mitigating the threat. What are the changes? As of April, this year red diesel can no longer be used in a range of vehicles, including those in construction. That means fuel bowsers are now filled with the same white diesel available to m...
The growing mobile ownership rate, the emergence of more user-friendly banking apps, the tech-native younger generation, and, of late, the pandemic-induced shift to online, all create a fertile ground for mobile banking. Unfortunately, the acceleration of banking app adoption today goes hand in hand with the increase of targeted security threats. In 2022, a month wouldn’t go by without a headline-making mobile banking attack or incident that resulted in stolen funds and sensitive personal...
It’s clear that despite recent layoffs in the tech industry and general unease about the economy, there are still significant gaps in the number of jobs available and the amount of workers available to fill them. According to the Labour Department, there are 5.5 million more job openings than workers available. The physical security industry is not immune to these shortages. Last fall, Allied Universal reported being unable to fill thousands of open roles nationally while other smaller s...
Identity management is an important element of both data security and physical security in an organisation. But all ID management solutions are not the same—especially when it comes to security. There are no uniform security standards for the industry, and many off-the-shelf systems fall short when it comes to data protection. To protect people, property, and data, make sure you select a system that maximises security at every stage. What is identity management? Identity management&mdas...
The smartphone is an integral part of our daily routines. The communication and entertainment device of yesteryear has become a serious player with which we increasingly handle sensitive processes, such as payment transactions. BLE or NFC authentication At the supermarket checkout, more and more customers are pulling out their smartphones instead of their wallets. Apple Pay, Google Pay, or specific banking apps make it possible: to hold the smartphone in front of the reader of the checkout sys...
For the past few years, security professionals have had to change the way that they go about protecting their organisations. From challenging old assumptions around access control through to implementing more access management and authentication policies, security has been at the heart of how companies have responded to the pandemic. The journey to more modern security processes that could support more flexible working was a rapid one. Remote work programmes have bedded in, based on how IT sec...
Cloud-based video surveillance as a service (VSaaS) is in a period of significant growth at present. In fact, the global VSaaS industry was valued at $2.2 billion in 2020 and is expected to reach $4.7 billion by 2025. Part of the reason for this growth is the increased adoption of the technology within shops, restaurants, and other retail settings. A cloud-based video management system can be valuable for businesses of all kinds, but those in the retail or restaurant industries are often able t...
The banking market continues to evolve through the growing use of digital and mobile devices, as more branch operations aim to enhance convenience and service for the customer. These advancements also create more significant opportunities for fraud and loss. Together, these two trends come full circle: Increasingly sophisticated fraud techniques require organisations to pursue new approaches to preventing and detecting such activities. Digital transformation But before we lead down that path,...
One of the biggest security trends in the last two years has been the adoption of cloud-based services, spearheaded mainly by an increasing number of video surveillance-as-a-service (VSaaS) offerings. VSaaS market value According to MarketsandMarkets Research, the global VSaaS market value is expected to reach $6.2 billion by 2026. This growth is propelled by demand for remote access video services, less local hardware to maintain, new internet-enabled devices, and a lower total cost of owners...
In the UK there is a new data reform act working its way through the legislative process. As the law changes, the market changes – so this year will see many companies trying to read the tea leaves and adapt their offerings to take advantage of the emerging changes. The security marketplace is, apparently, constrained by the need for great privacy – it appears to be a zero-sum game – you can have privacy, or you can have security, you can’t have both. In the second half...
Enterprise security directors often count on an integration firm to handle jobs ranging from day-to-day activities to long-term, technology-laden projects. However, before entering a relationship, you must know what's reasonable to expect from an integrator – as not all are created equal. Here are some tips that might make the selection process easier. Completing comprehensive classwork An integrator's experience working in an enterprise environment is an obvious consideration. Ideally...
Organisations have shifted business focus countless times since the onset of the pandemic. While many leaders have been primarily concerned with the immediate health and safety of their customers and employees, 2022 has given rise to a new trend: More than ever, business leaders are seeking security solutions that increase operational efficiency and cost savings as well as improve logistics and business insight. As working environments become more complex, organisations looking to drive higher...
Browse expert commentaries
Related videos
OPTEX REDSCAN mini series protects The Londoner Hotel
Time challenge: installation of battery powered Aperio cylinder
IDIS launches efficient AI-powered security camera range
Verkada Command Connector for Camera Integration & Cloud Management
Hikvision One-Stop SMB Solutions
Dahua X-spans Wizmind Network PTZ Camera
Palm vein recognition
DownloadThe key to unlocking K12 school safety grants
DownloadSelecting the right network video recorder (NVR) for any vertical market
DownloadPhysical access control
DownloadCybersecurity for enterprise: The essential guide to protecting your business
Download