Technology & Trends - Access control system accessories
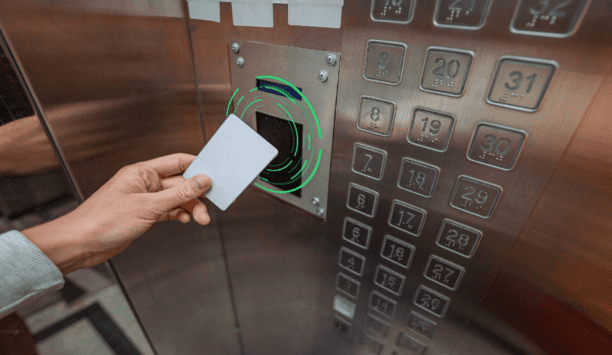
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
As we navigate the new normal, the power of choice and flexibility continues to take centre stage. We’ve grown accustomed to the choice to work from home or virtually anywhere and the flexibility to have everything delivered (sometimes even right into your fridge!). Seamless access control With this, we are seeing heightened demand for seamless access control through smart locks and mobile credentials. This powerful combination creates exciting new opportunities to meet resident demand f...
While the foundation of autonomous retail has been built up over the past few years, it is only now that retailers are beginning to fully experiment with the technology. There were an estimated 350 stores globally in 2018 offering a fully autonomous checkout process, yet this number is forecast to increase dramatically with 10,000 stores anticipated by 2024. This acceleration in the growth of unmanned retail stores has, in part, been boosted by the COVID-19 pandemic and a demand for a more cont...
From analogue to digital, from stand-alone to interlinked, building systems are in a state of transition. Moreover, the rate of change shows no sign of slowing, which can make it difficult to keep up to date with all the latest developments. If asked to pinpoint the single biggest driver of this revolution, one could point out the growing clamour for platform convergence. A security guard in a building doesn’t want to use different systems to check video cameras, fire alarms or if someone...
Ensuring employee health and safety remains a key priority for organisations this year, especially as we see COVID-19 cases continue to rise in different areas of the world. As an ongoing challenge, COVID-19 has shifted the priorities of many organisations. In fact, “improving health and safety for employees” is the top strategic goal this year of manufacturing and logistics organisations in the U.S. and U.K., according to research conducted by Forrester on behalf of STANLEY Securit...
Access control and management of trusted identities are the building blocks of security, safety, and site management policies for many businesses and organisations. The current pandemic has compounded this with the introduction of new policies and regulations, particularly around social distancing and contact tracing. Most organisations will have some form of legacy access control in place, ranging from the most simplistic options, such as locks and keys, to technology-based systems. The issue...
The UK Government has set out an ambitious ten-point plan, known as the green industrial revolution, with an aim “to forge ahead with eradicating its contribution to climate change by 2050.” This makes our government the first major economy to embrace such a legal obligation. Green recovery Acknowledging climate change and meeting net-zero is a demanding challenge especially for those affected by the pandemic. But the UK Government, with the launch of its aspiring strategy, is inve...
Whenever you say the word “security” in today’s world of digitalisation and technology, minds immediately jump to online security. Encryption, passwords, and website security are all common areas of concern for today’s security teams – so much so that we often pass over physical security installations entirely. But we shouldn’t, because contrary to popular belief, security doors aren’t just for banks and safes. High-security doors are deployed and used...
The SolarWinds cyberattack of 2020 was cited by security experts as “one of the potentially largest penetrations of Western governments” since the Cold War. This attack put cybersecurity front and centre on people’s minds again. Hacking communication protocol The attack targeted the US government and reportedly compromised the treasury and commerce departments and Homeland Security. What’s interesting about the SolarWinds attack is that it was caused by the exploitation...
Q: Mr. Seiter, Mr. Ekerot, you both joined Bosch Building Technologies’ business unit Video Systems & Solutions as Senior Vice Presidents in March 2020, when the Coronavirus pandemic was just beginning. How did your business unit get through 2020? Magnus Ekerot: The crisis was also felt at Bosch. At the same time, demand has risen for solutions that keep businesses open and protect people's health. We offer corresponding video solutions that can make a significant contribution to con...
The physical security market continues to experience growth as users look to capitalise on the promises of emerging technologies and because of this, 2017 proved to be a great year for Oncam. In fact, this year was the best year in Oncam's history in terms of sales, as 360-degree fisheye cameras have gone from being a “specialty” camera used only in certain applications to a primary device for enabling total situational awareness. Today, many of our customers leverage 360-degree ca...
2017 was quite an interesting and eventful year for the physical security industry. The economy has been robust and technology has become progressively sophisticated—with interactive services, cloud computing and network-based solutions taking charge to provide new insights to installers and their end-user customers. The Internet of Things is creating increasingly integrated solutions, with a heightened emphasis on total connectivity. Changing security expectations World events have als...
Part 1 in our Intercoms in Security Series Lambert-St. Louis International Airport uses Code Blue intercoms Organisations are demanding a new level of interoperability among mission-critical security systems. Intelligible audio, the ability to hear, be heard and be understood, is critical to communication, which is essential to the core security processes within an organisation, as well as to emergency situations. Intelligible audio provides a platform to optimise various...
The technologies behind physical access control are constantly evolving. It’s a fast-changing market that can leave end user organisations struggling to keep up. Smart cards still reign supreme, with good reason, but there are also new options today and on the horizon. Customers want to implement the most secure and up-to-date technologies, but constantly adapting their systems to keep up with the pace of change is impractical. Leveraging access control technologies in a way that both m...
Facial and body behavior analytics can identify people “without interferingwith the pace of life” Biometrics companies throughout the security marketplace are expanding the functionality of their systems for a variety of uses. This article will take a look at what several companies are up to. SRI International’s identity solutions seek to bring convenience, speed and security to existing workflows. SRI’s Iris on the Move (IOM) biometric systems ca...
Farpointe Data started 2015 in newly relocated offices featuring a larger, more proficient layout that added new manufacturing equipment and increased its production and inventory capabilities. Shortly into the year, Farpointe introduced new WRR-22 and WRR-44 433 MHz receivers that use either 2-button or 4-button transmitters to open two or four different doors from ranges up to 200 feet (61 m). Each button outputs transmitter data over separate Wiegand outputs, yet the receiver installs just...
For the second year in a row, Canon made the biggest M&A move in the security marketplace in 2015. How could Canon top the industry shockwaves it created in 2014 when the Japanese giant acquired VMS company Milestone Systems? That’s easy: They bought Axis Communications for $2.8 billion in 2015. Although the Canon-Axis deal grabbed the most headlines and was easily the most shocking M&A announcement of 2015, it was certainly not the only big news on the mergers...
Just how big is the home automation industry? One way to tell is by looking at the sheer number of companies – large and small—that have rushed to enter this fast-growing space. They include some of the world’s largest corporations – Apple and Google – along with the nation’s biggest cable and telecom companies – Comcast and AT&T. It includes big names in security like Honeywell and ADT. Then there are less known, but fast growing, contenders such as...
A retail banking tipping point is fast approaching with the state-side adoption of EMV technology Banking faces a challenge: to reconcile major security concerns with improving technology in order to reflect modern, mobile technology and the self-service solutions that customers have come to expect from their non-banking retail experiences. This is probably the number one issue I discuss with my bank clients. Banks need to make the technology in their branches more automated,...
Lost or damaged keys cost authorities thousands of dollars to replace Keys are a common element in any transportation department, and an automated key control system is a valuable tool. Key management systems offer multi-site transportation facilities increased security and control to help prevent authorised key access as well as reducing the number of lost or misplaced keys. As an example, road repair is often done at night and requires equipment, vehicles, lights, gene...
Uncoupling software from hardware allows manufacturers to respond faster to changes Nedap Security Management 2014/2015 Review and Forecast:Threats such as Mifare hacking, the European General Data Protection regulation coming in 2016, and the need for security to integrate with other IT-based systems – these are just some of the challenges security manufacturers and system users have to deal with and respond to. External factors such as these do provoke change in physic...
2014 saw more organisations making data-driven decisions with insight or foresight provided by intelligent analysis of the data Morse Watchmans 2014/2015 Review and Forecast: 2014 saw a year of continued change in the security marketplace. A healthier economy triggered growth in new projects and helped loosen the purse strings for capital expenditures. From a technology standpoint, the industry evolution to a more network-centric environment created additional opportunitie...
With a growing threat from home-grown terrorists, there will be a greater need to protect soft targets as well as to use portable barriers Delta Scientific 2014/2015 Review & Forecast:In 2014, hard targets, such as government facilities, airports, refineries and similar installations continued to boost sales for Delta Scientific by protecting themselves from car- and truck bombers using crash-rated vehicle access control equipment including bollards, barriers, barricades a...
Access control systems that leverage proprietary technologies severely limit system flexibility Access control’s ongoing transition from closed systems to more open integration provides benefits for integrators, and especially for end users looking to maximise their system return on investment. End users want greater flexibility, specifically in terms of hardware choice. As a result, more non-proprietary solutions are coming to market. For the integrator, offering more o...
Access Control is the second-fastest growing area in the security market. A major shift from PC-based clients systems to solid state, embedded operating systems, browser-based user interfaces, remote services, and changes in compliance legislation are just a few factors driving access control adoption both across the residential and commercial markets. John LaFond, VP of Integrated Systems at Linear LLC, explains these factors and how they contribute to the future of access control...
In the digital world, people own personal information just like they own physical assets such as cash, keys and clothes in the real world. But because personal information is intangible, its value has been overlooked by many for a very long time. With the increase in cyber crimes on personal data and the infamous Snowden affair, this issue has become more prominent. Fei Liu from Nedap Security Management Research & Development informs that to improve the transparency of data collection and p...
Security officers work diligently to protect people and property and are often first on the scene of an emergency. Working alongside police, paramedics and firefighters, security officers demand our collective respect. The Freedonia Group reports that the demand for security officer and patrol services is forecast to rise at an annual rate of 4.6 percent through 2014 to $25 billion and the number of officers employed by private security firms is expected to increase 2.6 perce...
The power supply is the key driving force for access control systems Power plays a crucial role in the effective functioning of any access control system and the choice of the right power system to suit specific requirements is important. In this article, Ronnie Pennington, National Accounts Manager of Altronix Corporation explains various ways to determine and meet the power requirements for access control systems. Usually, an access control system itself acts as the main so...
An access control system can be an excellent and an invaluable tool for enhancing business efficiency The picture that comes into most people’s minds when thinking about access control systems is someone offering a badge up to a card reader to unlock a door or release a barrier so that they can get into or out of a building. And, of course, this is a primary function for most installations. The capabilities of modern access control systems extend far beyond simply contro...
The intertwining of security and IT is requiring consultants to redefine their role Security consultants have traditionally operated inconspicuously while providing quality, independent advice to customers around their security requirements. However, the relentless intertwining of IT and security in the form of IP technology has required consultants to adapt, and consequently redefine their role within the space. In this article Daniel Wan, Channel Marketing Leader UK at Honey...
Browse expert commentaries
Related videos
Find Lost Wallet with Dahua WizSeek
Dahua Traffic Signal Controller Highlight
CLIQ Connect
Hikvision AOV 4G Solar Camera Series for Off-Grid Video Security
KentixONE – IoT Access and Monitoring For Data Centres
Climax Technology HSGW-Gen3 Modular Smart Security Gateway
One system, one card
DownloadAligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
Download