IP security solutions - Expert commentary
48% of U.S. judges say they are not adequately prepared to deal with the range of “scientific or technical evidence” presented in court Over the last decade, the video surveillance security industry has morphed drastically in attempts to keep pace with both the consumer electronics and enterprise IT markets. This has created a steep learning curve for law enforcement as well as individuals in the judicial system. A 2012 survey titled “A national survey of ju...
CSR applies to the security industry in many different ways and can be practised by small or large businesses What exactly is Corporate Social Responsibility (CSR) and how does it apply to the security industry? Let’s look at how two very different companies – Axis Communications and FGH Security – each put CSR at the heart of their operations. Corporate Social Responsibility means different things to different people, and is often used as a catchall for one...
A perceived benefit of buying direct is to save money as opposed to paying a middleman Security companies have multiple options to purchase security products today – online, manufacturer direct, or from the vast array of security products and electrical supply networks dotting the landscape. Because there are numerous options, and costs may not vary drastically, the final decision on where to purchase ultimately boils down to service and additional support these channels...
Too often we attribute failure of connected devices to the devices themselves when the problem is actually an infrastructure failure Network infrastructures for security devices are complex. It may seem simple to connect an Ethernet cable to a cable modem, but the connection of IP cameras, access control devices and other IP/Power Over Ethernet (PoE) devices is not nearly so simple. Infrastructure is the heart of any system; and too often we attribute failure of connected devi...
Lighting, or the absence of it, is one issue that significantly affects a camera’s video quality Video surveillance has rapidly advanced over the last two decades. Today, integrators can purchase IP cameras offering complete network control, megapixel cameras with HD imaging, and PTZ cameras with remote directional control. Although these features are impressive, they don't solve all the challenges that surveillance solutions face. Importance of lighting for camera per...
Keeping surveillance networks secure can be a daunting task but there are several methods that can greatly reduce risk, especially when used in conjunction with each other. Below are 13 tips security and IT professionals can follow in order to keep an IP video surveillance network secure. 1. The stronger the password the better Strong passwords are the most basic security measure, but unfortunately ignored by many users. Many surveillance systems are deployed in the field with...
What factors should an end user consider when looking for a professional systems solution provider? Andrew Schonzeit, President of IDESCO Corp., New York, knows what it takes to have an award-winning, top-in-its class systems integration company. For more than seven decades, the company has grown, morphed and continued to move into the world of value-add integrated solutions contracting. They’ve received numerous industry and business accolades and increased their statur...
Part 2 of our Security in Healthcare series The future is digital, and analogue systems are a thing of the past – or are they? The fact is, in the healthcare vertical at least, we may still have a way to go before the full potential of IP-based systems is realised. Obstacles include a lack of funding and the challenge of sharing IP bandwidth with other healthcare technologies. Bandwidth competition While many hospitals have invested significantly in IP syst...
Part 1 of our Security in Healthcare series Hospitals have a continuous need for security, to update their systems,and to make repairs The healthcare vertical provides plenty of opportunities for security integrator companies. A single large hospital system can supply a dependable ongoing source of revenue to integrator companies, says David Alessandrini, Vice President, Pasek Corp., an integrator. Hospitals have a continuous need for security, to update their...
The days when Chinese video surveillance products were associated with lower quality are mostly gone now. Certainly, it’s easy enough to test the quality and functionality of any Chinese-made product in a shootout against products made anywhere in the world. In that sense, the quality of Chinese goods is no longer an obstacle for security customers: Their ability to judge quality for themselves eliminates any dependence on previously held opinions. But what about other preconceived ideas...
H.265 compression continued to be a popular topic from exhibitors on the second day of IFSEC Video beyond security, compression, HD over analogue and integration were on the lips of several exhibitors at IFSEC International 2016. Strangely for a security exhibition, there were plenty of exhibitors talking about non-security applications on the second day of IFSEC International in London. For Axis Communications, Atul Rajput, Regional Director for Northern Europe, said th...
IPVideo Corporation, Bay Shore, New York, recently announced a new OEM agreement with Milestone Systems Inc., Beaverton, Oregon, in an effort to provide deeper and wider options in its portfolio of video management solutions. According to Steve Rice, Director of Business Development, the partnership will allow the company to reach a broader number of enterprise customers and provide them with distinct choices – and two completely different video management system (VMS) offerings. On the t...
The growing sales of IP-based solutions in the surveillance market is a well-discussed topic. Security companies are rushing to grab a slice of this lucrative pie. However, at the same time, analogue surveillance systems have continued to retain their appeal for many end users. Aware of this demand, some companies have continued to develop technology for analogue solutions despite the IP trend. One company driving this force is Nextchip, the company behind AHD™. Up until rec...
The integration of H.265 technology may be hindered by the availability of optimised H.264 best encoding for surveillance systems Video compression technology has been a crucial element in surveillance system design since the advent of Internet Protocol (IP) in the 1990s. Since that time, standards for video encoding have been explored in various capacities. Currently, the industry is all abuzz around H.265 High Efficiency Video Coding – the next iteration beyond H.264,...
There are resources to help guide an organisation’s management of cybersecurity risks, most prominently from the National Institute of Standards and Technology (NIST) and the U.S. Department of Homeland Security. NIST defines cybersecurity as "the activity or process, ability or capability, or state whereby information and communications systems and the information contained therein are protected from and/or defended against damage, unauthorised use or modification, or exploitation.&rdquo...
Cloud connectivity can provide a linkage between the mobile users and the facilities and systems they want to interact with From enterprise applications to small businesses, schools, health care facilities and beyond, investments in physical security systems provide valuable resources to help protect people, property and assets – and ultimately the financial security and well-being of the organisation. As need and demand for better security has dramatically increased ove...
Systems may be reliable and performing as originally intended, but can also beoutdated in comparison to current technology offerings Let’s start by defining what a legacy system is in the context of a security control system. Legacy refers to an installed and operating security control system made up of numerous components, both hardware and software, that have been eclipsed by newer technologies. A shortage of parts and pieces may be creeping in, and it’s also li...
It’s the 21st century already. Isn’t it time we all lived in smart homes? For technophiles everywhere, the smart home can’t come soon enough. The same might be said for the security marketplace, which is well positioned to thrive in the coming era of home automation. The wait could be shorter than we think, given some recent trends and events we are seeing in the home automation market. Let’s consider several of them: 1. Home automation is getting attention from Silic...
From a network performance perspective, adding higher megapixel camerasaffects bandwidth utilisation The quest for higher megapixel, high-definition and high-resolution video imaging continues, only now, it has become a marathon of sorts. That’s because the migration will progress decidedly – extending into the foreseeable future and beyond – as technology advances and becomes increasingly affordable. Ultra-high-resolution video is finding its niche, even am...
Many operators don’t know what’s actually transpiring on their OT networkand,even if hacked, have no knowledge of the assault Innovation in the oil and gas, utility, healthcare and transportation industries is heavily reliant on connectivity - between devices and systems, machines and data, people and processes. This connectivity is great for productivity upstream, mid-stream and downstream, but is also exposes these systems to greater cyber threat. Furthermore, as...
The report says almost 50% of the public transport organisations are willingto broaden the type of video analytics used A detailed survey of public transport operators shows a growing demand for networked/IP systems and video analytics to help cope with the requirements of large surveillance systems. The report, Video Surveillance in Public Transport, published by the international public transport association UITP and Axis Communications, is based on 74 respondents across 30...
By adding remote monitoring to service contracts, dealers and end users bothbenefit from substantial cost savings while reducing potential downtime Whether upgrading an existing surveillance and/or access system from analogue to IP, or installing a completely new system using structured cable, the ability to communicate, monitor and control IP devices delivers significant operational and economic benefits. The vast amounts of data these systems generate are useful in many ways...
PIAM solutions ensure that credentials are onboarded to all the right systems The number of credentials people are carrying is on the rise. At any given time, an individual may be carrying badges, cards or other ID devices for their office, the gym, public transit and more, not to mention credit cards and government-issued identification. The more credentials people carry, the greater the challenge of managing and tracking these credentials poses, and the more likely that they...
ISC West has seen manufacturers' efforts to simplify the installation, serviceand deployment of security solutions for systems integrators Efficiencies come in all shapes and forms for systems integrators in the security industry, and ISC West 2016 was a testament to manufacturers' efforts to simplify installation, service, maintenance and deployment of IP video specifications for installers. GURU smartphone app with audit reporting capabilities March Networks, Ottawa, Canad...
IP hardware is enabling customers to break free from proprietary security systems,to embrace the system integration available on open platforms Proprietary, closed systems are the bane of security. Yet they still exist. Robert (Rob) G. Lydic, Global Vice President of Sales for ISONAS, Boulder, Colorado, addresses the importance of open platforms in access control and what it means to systems integration in this exclusive Q&A. Trends in access control technology SourceSec...
The video storage boom shows no signs of slowing down. The talk is not typically how much storage; but where and how to store. Locally-housed (on-premises) storage continues to be the most cost-effective, along with providing the most control over your data. However, prior to considering the storage, it is important to look at the robustness of the network, as it is a key factor in making the right decision for storage architecture. It is necessary to know if there is enough...
The development of PSIM security systems and the move towards smart buildings and cities holds huge potential for environmental performance in the security industry Is the drive to give clients improved CCTV, perimeter protection, intruder alarms and access control making our industry any greener? Is technological innovation consistent with reducing security industry’s carbon footprint? In any case, green operating practices are more a side effect of current developments...
In April of 1775, Paul Revere rode fearlessly through the streets of New England warning the town of Lexington that “The Red Coats are Coming!” It was both a warning and an announcement that a powerful force was upon them. If Paul Revere were alive today and in the security and access control world, he would probably be tweeting, posting, and blogging that “IP access control is coming, and it’s coming faster than you’d expect!” Just as in 1775, it is both a...
As the world faces new threats and challenges at the end of 2015, the security market looks more and more attractive for companies and employees around the world. Digital technology increasingly is replacing a traditional physical security approach, upgrading old-school analogue alarms and CCTV. Attractive security projects From AxxonSoft’s point of view, security projects seem very attractive because they normally can bring up to 30% profit for a standard security system installation....
2015 has been a mixed year. There’s been aggressive competition in the security industry and difficult market conditions in some parts of Europe. The market has slowed down, but at the same time there is still a huge demand for new solutions coming into the market. As a manufacturer, we continue to see strong demand for innovative products. Overall, the industry has matured this year. The full HD market is established now, and more security professionals are now looking beyond that. 4K an...
Top 7 trends to watch in the physical security industry
DownloadTroubleshooting IP video systems
DownloadSimple Security Solutions for SMBs
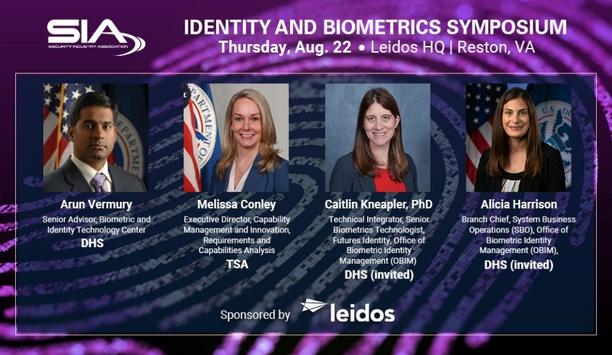
DownloadSIA Identity and Biometrics Symposium
DownloadGunshot detection
Download