Zimbabwe News
From a network performance perspective, adding higher megapixel camerasaffects bandwidth utilisation The quest for higher megapixel, high-definition and high-resolution video imaging continues, only now, it has become a marathon of sorts. That’s because the migration will progress decidedly – extending into the foreseeable future and beyond – as technology advances and becomes increasingly affordable. Ultra-high-resolution video is finding its niche, even am...
Technology solutions enhance and make manned guarding moreeffective and efficient the quickest way Most companies believe manned guards can help mitigate disturbances and neutralise situations, while at the same time reducing the chance of criminal activities and/or accidents occurring. However, people cannot be omnipresent or always be in the right place at the right time. When combining manned guards with the power of today’s technology, the results are unmatched. Dev...
Keith Bloodworth and James Condron will discuss on PSIM for integrators, end users, consultants, and partners The world is changing, what was once deemed to be safe is at risk, and what was once at risk no longer needs securing. People live in an era of new risks, new technology and new ways of staying ahead. CNL Software has been evolving, pushing the boundaries of what is possible in the control room. At IFSEC, discover how CNL Software is leading this new era in security...
The largest global event of 2016 – and the year’s biggest security challenge – will no doubt be the Games of the XXXI Olympiad in Rio de Janeiro, Brazil. Around 15,000 athletes from 206 countries are expected to compete at the Olympic games, August 5-21, 2016, and about 7.5 million tickets will be issued. In our age of terrorism, organisers of any event on the scale of the Rio Olympics must consider the possibility of an attack or other security breach during the more than two...
How mobile telephones have transformed into “smartphones” is one of the great technology stories of our time. What once was a single-function device now can do almost anything – display video, pay for groceries, monitor our health. The smartphones we carry in our pockets today have more computing power than the “super computers” of yesteryear, and that power has found many uses in a seemingly endless array of “apps.” Some of them are directly related to...
Vanderbilt will be hosting a series of ‘Innovation Talks’ with key partners on areas such as closed network systems, integration & automation One year after its launch at the same exhibition, visitors to IFSEC International 2016 are being encouraged to visit stand G1250 and see why Vanderbilt continues to create such a buzz in the security industry. A year on from launch The company’s combination of global reach, independent structure and technical expe...
The stand will also demonstrate protection of sensitive data with Aperio® KS100 Server Cabinet Lock ASSA ABLOY Access Control, a UK division of ASSA ABLOY, the global leader in door opening solutions, is showcasing its revolutionary Aperio® wireless locking technology at IFSEC 2016, at Excel, London, from 21-23 June. Demonstration of Aperio KS100 Visitors to stand E1100 in Hall S7, will have the opportunity to see the new features of the established, leading Aperio&r...
Topics covered ensure there is something for everyone involved within the security sector Tavcom has announced an impressive line-up of expert speakers who will be sharing their knowledge in the Tavcom Training Theatre during this year’s IFSEC International exhibition which takes place 21st -23rd June, 2016 at EXCEL London. Free of charge and free of jargon As in previous years, the variety of the topics covered by the free to attend lectures, ensure there is something...
If anyone tells you that the use of Mass Notification Systems (MNS) is a new trend, it is likely that they do not fully understand it. You have been impacted by mass notification your whole life. Surprised? Every time there is a fire drill at an elementary school, or a bell chimes noon or a blinking light announces a snow-related parking ban, an MNS is being deployed. Ultimately, mass notification is just mass communications. What has changed is the distribution methodology, the granularity and...
Wireless surveillance systems are attractive to customersas they are cost-effective and easy to install Various studies, market statistics and forecasts project growth for the surveillance market from 2016 to 2020. Besides needs ranging from traditional analogue cameras to IP network cameras, more and more consumers also have a high interest in intelligent surveillance systems. Along with safety, these systems provide additional details for users in applications such as p...
Many operators don’t know what’s actually transpiring on their OT networkand,even if hacked, have no knowledge of the assault Innovation in the oil and gas, utility, healthcare and transportation industries is heavily reliant on connectivity - between devices and systems, machines and data, people and processes. This connectivity is great for productivity upstream, mid-stream and downstream, but is also exposes these systems to greater cyber threat. Furthermore, as...
Dotworkz products are available in the Arecont Vision MegaLab as part of the agreement Arecont Vision®, the industry leader in IP-based megapixel camera technology, has announced that Dotworkz, a leading manufacturer of protective camera housings for extreme environments, has joined the Arecont Vision Technology Partner Program. Dotworkz products are available in the Arecont Vision MegaLab™ as part of the agreement. “Integrators and end customers will greatly...
The report says almost 50% of the public transport organisations are willingto broaden the type of video analytics used A detailed survey of public transport operators shows a growing demand for networked/IP systems and video analytics to help cope with the requirements of large surveillance systems. The report, Video Surveillance in Public Transport, published by the international public transport association UITP and Axis Communications, is based on 74 respondents across 30...
Oncam, the leading provider of 360-degree video capture and business intelligence technology, announced recently the addition of two new models to its Evolution 05 camera suite: the EVO-05 Mini Outdoor and the EVO-05 Mini Recessed cameras. Featuring the company’s patented 360-degree dewarping technology, Oncam’s EVO-05 Mini range packs a high-quality 5MP sensor and fisheye lens into an ultra-small and robust form factor with no moving parts. EVO-05 Mini Outdoor The EVO-05 Mini Outd...
By adding remote monitoring to service contracts, dealers and end users bothbenefit from substantial cost savings while reducing potential downtime Whether upgrading an existing surveillance and/or access system from analogue to IP, or installing a completely new system using structured cable, the ability to communicate, monitor and control IP devices delivers significant operational and economic benefits. The vast amounts of data these systems generate are useful in many ways...
As the technology in omnidirectional cameras continues to improve, they are becoming increasingly more affordable to a wider segment of the video surveillance market Just a few years ago, omnidirectional cameras were a novelty. Today, however, this technology has taken the leap to the mainstream. Think about how ubiquitous Google’s Street View is, and you can gain a better idea of the power of omnidirectional cameras. Even consumers are starting to see many forms of omn...
Awareness against fake fingerprints prevent fingerprint from becomingthe choice of biometrics despite their benefits Apple’s refusal to the US government’s request to unlock Syed Rizwan Farook’s iPhone has triggered public interests in personal and information security. Ever since the introduction of Touch ID by Apple, fingerprint technology has been implemented into more and more mobile devices by different manufacturers. It is being adopted as the authentic...
PIAM solutions ensure that credentials are onboarded to all the right systems The number of credentials people are carrying is on the rise. At any given time, an individual may be carrying badges, cards or other ID devices for their office, the gym, public transit and more, not to mention credit cards and government-issued identification. The more credentials people carry, the greater the challenge of managing and tracking these credentials poses, and the more likely that they...
Stringent security policies are necessary in an organisation to prevent incidentsof misplaced trust leading to an attack from intruders Trust is a word closely associated with both physical and logical security, after all, knowing who to trust is a key part of any security policy. However, when trust is wrongly assumed it rapidly becomes a key problem and a significant weakness in the security regime. Often the weak link is human nature itself. This means that to begin...
As more security equipment categories become commoditised, a previously rich source of income for integrators and installers – markup – is becoming harder to come by. Less expensive products with little to no perceptible value differentiation leave integrators with few options, not to mention the growth of pricing transparency that comes courtesy of the Internet. We asked this week’s Expert Panel Roundtable: Given the increase in commoditised hardware (i.e., lower profit margin...
Nationally from 2012 - 2015, there has been a decrease in the money spent on theinstallation, monitoring and maintenance of CCTV compared to the period 2009-2012 The UK has often been referred to as the world’s most watched country in terms of the scale of CCTV surveillance. But a new report claims that UK local authorities have reduced spending on the installation, maintenance and monitoring of public space CCTV systems, while the number of cameras being used is also do...
What effect will the attacks in Brussels have on aviation security? Screenings inpre-security airport areas have been uncommon, but may become standard practice Will the Brussels airport attack herald a new era of aviation security? Like the bombing of Moscow’s Domodedovo Airport in 2011, the Brussels attack took place “landside”, meaning that security precautions would have been low-key and limited to spot checks and the general watchfulness of police office...
Recently at a conference, one of my media colleagues asked an interesting, and basic, question: What exactly is an open system? Many of us think we know what an open system is, but the ensuing discussion provided several different answers, many of them centred on what an open system is NOT (rather than what it is). An open system does not limit a customer’s options. An open system provides maximum flexibility as a system evolves over time. In other words, an open system doesn’t lo...
ISE’s research shows that healthcare facilities & hospitals security programmesto ward off determined attackers going after specific targets A well-known security axiom posits that an effective security programme can discourage would-be attackers, causing them to move on in search of softer targets. But it doesn’t always work that way. Take healthcare facilities such as hospitals, for example. Prospective attackers with no particular target in mind may see...
Access control and visitor management are evolving and becoming more rooted in an organisation’s overall physical security structure Government regulations are driving increased security levels for visitor management. Private industry, where the need to manage and monitor visitors is an equally high security priority, is following suit. As a result, access control and visitor management are evolving and becoming more rooted in an organisation’s overall physical sec...
64 of fire and security industry’s young engineers will head to IFSEC 2016 to put their skills against each other in live installation challenge IFSEC International, organised by UBM EMEA, have recently announced that all places on the prestigious Engineers of Tomorrow annual competition are now filled. 64 of the fire and security industry’s brightest young engineers will head to IFSEC International over the 21-23 June 2016 to put their skills against each other in...
The ARC Village, brought in association with CSL Dualcom, comprises of 8 exhibition booths surrounding a central networking area Europe’s leading security and fire industry events, IFSEC and FIREX International have recently launched the first ever ARC Village at 2016 shows located at London’s ExCeL on 21st to 23rd June. Providing an incisive platform for the UK’s alarm receiving centres to showcase their technical expertise and services, the ARC Village will...
Customer service is a vital part of any vendor’s business approach – from theplanning stages, to installation to maintenance of the access control system In today’s highly competitive and technology-rich security marketplace, an organisation’s customer service is as important as the product solution they offer. Let’s face it, you will always remember if the customer service was terrible – or if it was great. Do they go the extra mile or do t...
Portable crash barriers & traffic access control systems allow security integrators to expand their deployments for municipal surveillance and critical infrastructure The Pope does it. The Democratic and Republican National Conventions do it. Leading universities and police departments do it. Just what does this diverse list of people and organisations have in common? They have all used high-security portable barriers at their events with good success. According to manufa...
ASSA ABLOY door handles with built in reader, strike, request-to-exit sensorand door contacts help maintain sterile environment of stainless steel rooms Access control technology has been around for a long time, but security professionals still run into weird problems when designing and installing systems. For example, when a hospital discovered that it was losing $4,000 per patient bed annually in medicines and other supplies, it asked ASSA ABLOY for an access control solutio...
Browse security news
Featured products
Related videos
OPTEX REDSCAN mini series protects The Londoner Hotel
Hofbräuhaus in Munich relies on eCLIQ
What Alcatel-Lucent OmniVista Network Advisor can do for network infrastructure
The 2024 state of physical access trend report
DownloadThe security challenges of data centers
DownloadSecurity practices for hotels
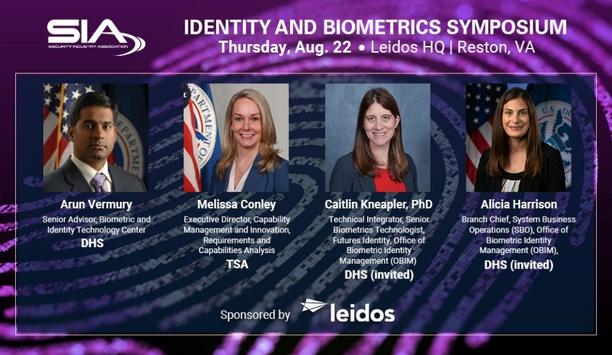
DownloadSIA Identity and Biometrics Symposium
DownloadGunshot detection
Download- Zimbabwe Security companies
- Zimbabwe Manufacturers
- Zimbabwe Distributors
- Zimbabwe Resellers / Dealers / Reps
- Zimbabwe Installers
- Zimbabwe Consultants
- Zimbabwe Systems integrators
- Zimbabwe Events / Training / Services
- Zimbabwe Manned guarding
- Zimbabwe Training organisations
- Zimbabwe Associations / regulatory bodies
- Zimbabwe Event organisers
- Zimbabwe Media
- Zimbabwe Recruitment / personnel
- Zimbabwe Services